Researchers from the Complex Photonic Systems (COPS) group used two layers of random materials to encrypt and decrypt a message sent via light communication. With that, they hid the sender and receiver simultaneously, and only when the light passed through both layers was the message received. The research team published their findings in the journal Optics Express, and believes this proof of concept has applications in visible light communication systems, light fidelity (LiFi), and optical fibre communications.
In an era where digital information is the lifeblood of our interconnected world, ensuring its security is paramount. Encryption plays a vital role in safeguarding our data, turning a simple message into a complex pattern and then converting it back, rendering it indecipherable if the message is intercepted in the middle. As technology advances at an unprecedented pace, the future of communication lies in the realm of visible light. But how can we guarantee the security of this cutting-edge form of communication?
Random objects
Surprisingly, the solution may be found in everyday objects that surround us. Researchers from the University of Twente, in collaboration with experts from the Technical University of Eindhoven and the innovative Signify company (formerly known as Philips Lighting), have shown that random materials – such as a layer of paint, a piece of paper, or a glass diffuser - enhance the secrecy of light communication by scrambling the message. When light traverses through these random materials, it scatters in multiple directions, creating an intricate pattern known as a speckle pattern. This very pattern becomes the foundation for encryption.
This encryption follows the concept of physical unclonable function (PUF). A PUF is an object so complex that it cannot be copied with current technologies. If a PUF is used as an encryption key, only the correct key – which is unclonable – can access the information. In this case, the key is the random object, and the information is the speckle pattern.
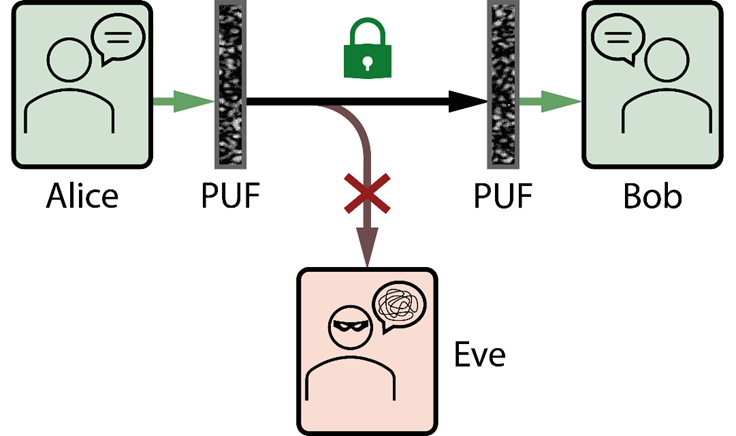
Figure 1: Diagram of the scheme. Alice sends a message to Bob while Eve tries to retrieve the message. In this scheme, the original message is only retrieved after passing through both PUFs, meaning Eve can't get the message.
Two layers
Researchers from the Complex Photonic Systems (COPS) group took this concept even further. Instead of using a single key to encrypt the message, they use two layers of random media as dual keys. With that, they hide the sender and receiver simultaneously, and only when the light passes through both keys is the message received. Any malicious eavesdropper attempting to intercept the message in transit would be confronted with a meaningless mixture of random patterns, utterly unrelated to the original message.
Furthermore, the secrecy is enhanced by the redundancy of the system. The proposed system is based on modulating the incident light using a device similar to a screen projector (or beamer) at the sender. Because the random materials are so complex, there are thousands of different ways to modulate the light, resulting in the same message, while changing the random pattern between the two keys. If the sender is constantly switching between the different modulations, an attacker in the middle is overwhelmed with random patterns, while the receiver is unaffected by it.
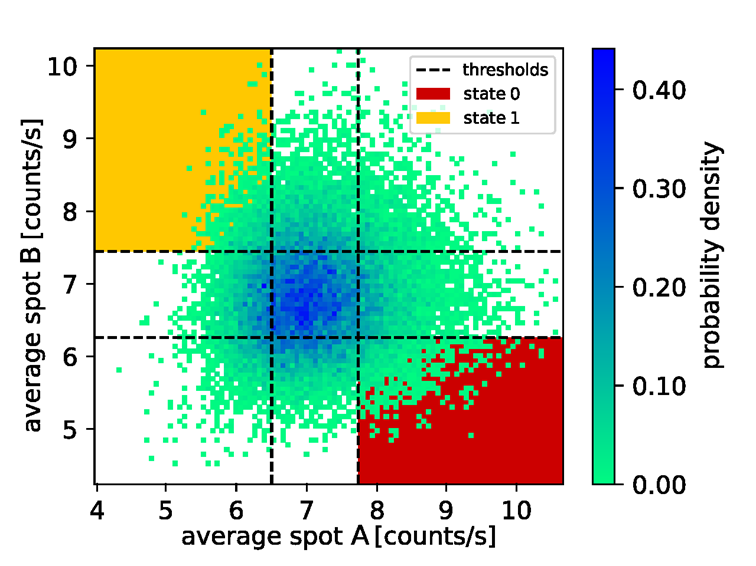
Figure 2. Distribution of 50,000 random patterns at the receiver (Bob). With this distribution, Alice and Bob agree on which patterns are a binary 0 or a binary 1. Bob just needs to measure spots A and B to receive the message.
The paper ‘Enhanced secrecy in optical communication using speckle from multiple scattering layers, by Alfredo Rates, Joris Vrehen, Bert Mulder, Wilbert L. Ijzerman, and Willem L. Vos, appears in Optics Express. COPS is also proud to announce that the data used for the publication is available in the Zenodo database with DOI: 10.5281/zenodo.6397330. The researchers thank the NWO programme Free-Form Scattering Optics, the MESA+ institute, and all their colleagues at COPS chair.
DOI: 10.1364/OE.493479





