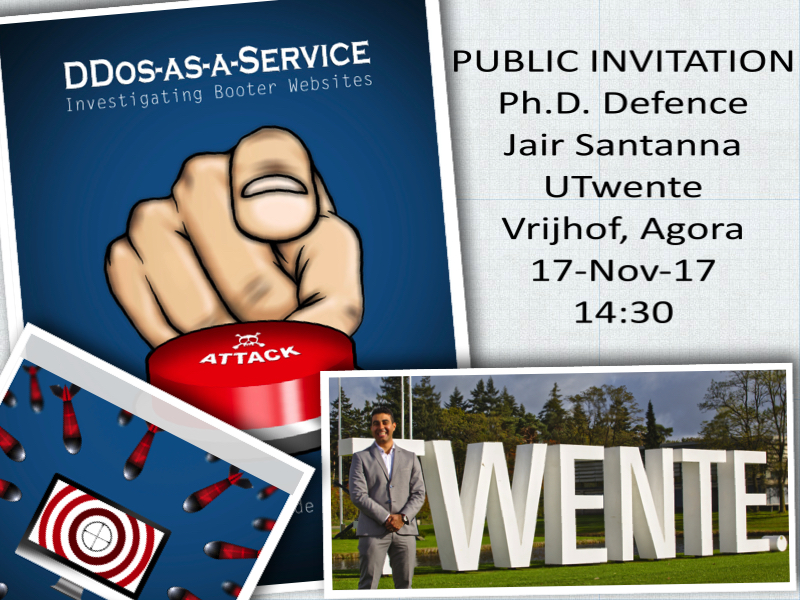
Public Ph.D. Defence
Jair Santanna
Title: DDoS-as-a-Service: Investigating Booter Websites
Local: University of Twente, building Vrijhof, room Agora
Date: 17-Nov-17
Time: 14:30
Abstract:
Why should you care about Distributed Denial of Service (DDoS) attacks? If your Internet home connection would be the target of a DDoS attack, then not only your connectivity is gone, but also your telephone and TV programs. This is because many homes have triple-play-service (a package offered by Internet providers that includes TV programs and telephone service together with the Internet connectivity). Looking from a company perspective, in 2015, small and medium companies reported spending more than $US50,000 recovering from a DDoS attack, while large corporations reported an average $US410,000. This figure increased drastically in 2017: large corporations reported $US2.5M in revenue loss as a consequence of a DDoS attack.
Until 2013, DDoS attacks were something that only a (relatively) skilled hacker could perform, and that required specialist knowledge. In 2013, the hacker community began offering DDoS attacks via Websites easily findable via popular searching engines (Google and Bing). Websites called ``booters'' and ``stressers'' offer, for very affordable prices, for example, starting from less than $US5, to perform as many DDoS attacks as requested for a month period. Between 2014 and 2017 booters were considered by network security companies to be the main responsible for the increase in (DDoS) attack power and frequency.
In this Ph.D. thesis, we investigate booter Websites and (also) third-party people and organizations (in)directly involved with booters. The main contributions of this these are that we show: (1) how to find booters, (2) how to detect their clients accessing and using them, (3) the characteristics of their attacks, (4) what third-party companies are used by them to maintain their operations, (5) which booters are the most dangerous and (6) which ethical arguments can be used to support mitigation actions against them. Finally, while the core of this thesis is based on scientific publications, a number of solutions proposed in this thesis are actively deployed by network operators worldwide. In addition to this, the methodologies in this thesis are used by the Dutch High Tech Crime Unit for collecting evidences for prosecution cases.