Tool 43-Risk And Value Analysis of IT/IS portfolio
1. Introduction
=>Several years of analysis in the IS industry had proven that the development of IS projects can be challenging and time consuming task “Chaos Report” in 1995, or the Robbins-Gioia survey in 2001”,
=>Also a number of studies and surveys have been conducted in recent years that have highlighted problems and failures related to IT projects ”PM world Today, June 2008”.
=>Furthermore, IS/IT project development represents a big investment inside an organization (in 1995, the Standish group reported the average cost of development projects differs according to size). See Appendics(i)
2.What framework should be used ?
A four cycle method created by Salmela and Spil (International Journal of Information Management, 2002) will be used by integrating risk and value analysis .
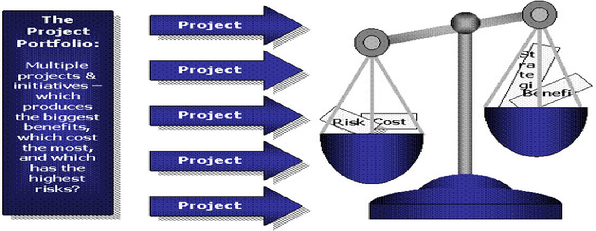
Figure 1. Risk vs value for the project portfolio
3.What are Risk Management, Assessment and analysis?
=>Risk management is the identification, assessment, and prioritization of risks (defined in ISO 31000 as the effect of uncertainty on objectives, whether positive or negative) followed by coordinated and economical application of resources to minimize, monitor, and control the probability and/or impact of unfortunate events[or to maximize the realization of opportunities.
=>Risk assessment is the first process in the risk management methodology.
=>Organizations use risk assessment to determine the extent of the potential threat and the risk associated with an IT system .Risk is a function of the likelihood of a given threat-source’s exercising a particular potential vulnerability, and the resulting impact of that adverse event on the organization.(Risk Management Guide for Information Technology Systems; Gary Stoneburner, Alice Goguen1, and Alexis Feringa ,July 2008)
On the other hand, risk mitigation; the next process in risk management “involves prioritizing, evaluating, and implementing the appropriate risk-reducing controls recommended from the risk assessment process” (Stone burner et al, 2002).
In this model, an authoritative list of common risk factors in information system development was identified and prioritized in a 2x2 matrix according to two different metrics:
* perceived level of control of the risk inside the organization and
*perceived relative importance of the risk
An alternate methodology, described by Stoneburner et al divides risk assessment in 9 steps, where only a few of them play a supportive role in the authorization phase.
Risk analysis could be conducted using several methodologies, such as:
ØFailure Mode and Effect Analysis (FMEA),
ØFault Tree Analysis (FTA) or
ØBenefit Cost Analysis (BCA, Gillen et al. 1999
4.0Values:
IS/IT project development is a big investment =>an inherent return value for the resources spent by the organization such as:
•monetary assets,
• time and personnel.
•performance,
• efficiency and
•saving estimation, which makes the identification and analysis of the desired value features critical for project authorization.
Company size | Average cost | ||
small | $2,322,000 | ||
medium | is $1,331,000 | ||
large | $434,000 |
Appendices: 1.1 average cost of projects
