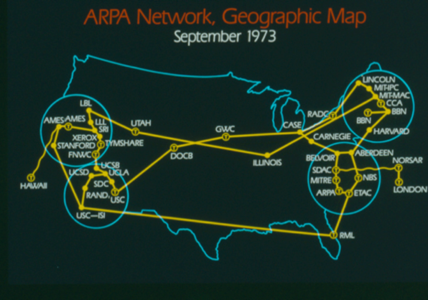
 In the early 70s, the Internet, then still known as the ARPANET, could still be drawn out on a simple map. But since then, once the potential of the technology became clear, it has grown in ways that were hardly predictable. Today, it is a global information system which supports most aspects of our daily life. Think about leisure activities, such as enjoying your favourite TV show or, as recent times have taught us, also remote working, access to services, online education and, last but not least, staying in touch.
In the early 70s, the Internet, then still known as the ARPANET, could still be drawn out on a simple map. But since then, once the potential of the technology became clear, it has grown in ways that were hardly predictable. Today, it is a global information system which supports most aspects of our daily life. Think about leisure activities, such as enjoying your favourite TV show or, as recent times have taught us, also remote working, access to services, online education and, last but not least, staying in touch.
In a way you can almost compare the Internet to a living organism, organically growing, at times in unexpected directions. But what do we really know about it? Are the detailed descriptions of protocols and communication technologies enough to describe it and understand it? And let’s not forget about ourselves: how do we - as human beings - use and manage the Internet? How do our actions affect the functioning of our networks?
We are looking for students that, like us, care about the Internet, have the curiosity to understand it, and share a drive to shape its future. We work with large large-scale network measurements to study the evolution of the Internet. We are interested in topics like:
- Network measurement: How do we design and implement novel methods for global-scale measurement?
- Deployment: How are new technologies deployed? What mistakes are made, and what are the factors that determine a technology’s success or failure?
- Security: Can we characterize vulnerable deployments or predict malicious behaviour in networks and services?
- Resilience: What are the weak points in the Internet's infrastructure?
- The Internet and the Public Good: What societal impact does a new Internet technology have, and how does society shape the Internet? How can network measurements be used to further the interests of society or counter threats?
If you are looking for a BSc or MSc assignment and these topics resonate with you, wait no longer and contact us! We regularly have open assignments and we are happy to discuss topics that may pique your interest!
For information, please contact any or all of us:
Anna Sperotto
Ralph Holz
Mattijs Jonker
Roland van Rijswijk-Deij
