Fifty ways to Change your IS Strategy
Ton AM Spil
Chapter 1 -page 4 - Prescribing the ICT Future
Chapter 2 -page 27 - First and last cycle – Agreement
Chapter 3 -page 71 - Next and previous cycle – Alignment
Chapter 4 -page 101 - Previous and next cycle – Analysis
Chapter 5 -page 149 - Last and First Cycle – Authorization
Chapter 6 –page 186 - Dynamic and Flexible SISP
Chapter 7 -page 209 - Inter organizational SISP in Networks
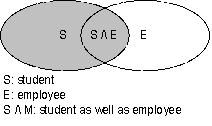
Insurance case & Innovation Care in
Twente case
Chapter 8 -page 236 - University case
Preface
It is not easy to say that information technology did not progress much if you are writing a preface in your swimming trousers in the shade of an apple tree, waiting for the “Newton effect”. Let me then start with stating that the impact of information technology in organizations has been progressing slowly in the last decade. The use of new information systems is often bad and wrong decisions are made on all levels of the organizations causing an immense waste of money and time concerning information, information systems and information technology.
This second draft of the syllabus e-strategizing shows 52 ways of improving decision making on information strategy. The book can be labelled as a “from teacher and student to teacher and student” learning experience. I thank all e-strategizing students of 2004 and 2005 for their contributions. My apologies for not correcting the bad English yet since it took me quite some time to “only” assemble the abundance of material.
This syllabus has to be handled together with the book “Strategic Planning for Information Systems” written by John Ward and Joe Peppard. Please take caution that the examination of the book (excluding chapter 8, 10 & 11) will take place in week 39 just three weeks after the start of the course. It will determine one third of the final grade. The second part of the lectures will follow this syllabus, constantly comparing it to the tools and techniques delivered by Ward an Peppard. The second part (one third) of the course will ask you to to give a short presentation about one of the 52 ways. Finally, within a group, the third part of the final grade is the result of an assignment given later on teletop.
I hope you will enjoy taking this master course as much as I enjoyed preparing it.
Ton AM Spil
Enschede, 18th of July 2006
Please referr to as:
Salmela, H & Spil, T A M(2002) " Dynamic and emerging Information Systems Strategy formulation and implementation ", International journal of Information Management , 22, 6, pp 441-460.
Dynamic and emergent Information Systems Strategy
formulation and implementation
Hannu Salmela
Turku School of Economics and Business Administration
Department of Administration / Info. Systems Science
PO BOX 110
20521 Turku FINLAND
phone: +358-2-338311, fax +358-2-3383451
e-mail: hannu.salmela@tukkk.fi
Ton A.M. Spil
(corresponding author)
University of Twente
Department of Technology and Management
PO BOX 217
7500 AE Enschede THE NETHERLANDS
phone: +31 –53-4893497, fax. + 31 53 4892159
e-mail: a.a.m.spil@sms.utwente.nl
Keywords:
Information Systems Strategy, Corporate Strategy, E-Business strategy, Strategic thinking
Abstract
Early attempts to formulate information systems (IS) strategies concentrated on the analytical task of deriving IS strategies from business plans. The limitations of the static plans that often resulted from these formal studies were, however, soon discovered. The critics suggested informal and incremental planning to ensure flexibility, creativity and strategic thinking to comprise emergent strategies as well as planned strategies.
In previous IS planning research, there appears to be a contradiction between the published planning methods and the generally held views about effective implementation of IS planning process. The explicit methods described in IS literature predominantly assume a comprehensive IS planning process. Despite the fact that many researchers consider incremental approaches to be more effective, methods that can be used to facilitate incremental IS planning are few, not detailed enough and not comprehensive.
The four cycles method (A method) introduced in this paper attempts to combine the strengths of both the comprehensive and incremental planning to be able to recognise emerging and make an e-business strategy. The method provides a basic schedule for organising planning activities. IS planning is seen as a continuous process that is periodically adjusted to the expectations of the participating managers. Practising managers can use the method to facilitate implementation of an incremental and continuous IS planning process. For e-business strategy research, the paper provides a theoretically based method that can be tested in future action research projects.
The first results of conducted action research show that the A-method should not be used as a checklist but as a choice list. Each period had a constant focus on external developments and the fit with internal possibilities. The method provided a flexible and dynamic basis for actions. Restrictions were the emergent nature of the changes and the difficulty of formalising creativity and innovation. We learned that a thematic approach by giving each cycle a creative subject helped to “open up” the users in the organisation. Future research should focus on the inter-organisational nature of e-business strategy. If it is difficult to get top management participation, it will be more difficult with more organisations involved.
Introduction
The challenge of aligning information systems (IS) decisions with business needs was discovered already in the early 1980's. For almost a decade, strategic IS planning was ranked on the top of the listings of critical issues in IS management (Niederman, Brancheau and Wetherbe, 1991). Chan (et al, 1997) and Segars and Grover (1998) show that it has not been out of the agenda since. Teo and Ang (2001) studied 138 firms and concluded that there are still many problems to be solved. The problems in launching and developing the IS strategy can be partly solved by using a comprehensive method, the problems in using the strategic plan have to be solved incrementally and that is why we propose a combined strategy.
Most of the formal methods for formulating strategic IS plans were published in late 1980's and early 1990's. While these methods provide clear steps for planning a new IS strategy, the risks associated with large special studies were also soon discovered. Thus, researchers started investigating more dynamic and incremental approaches to IS strategy formulation (Earl, 1993; Ciborra, 1994). In these approaches, explicit planning methods are seen as having only a minor role. The process is informal and rests very much on the ability of key managers to include the right people and conduct the right analyses.
With the advent of new technologies, such as Internet, the challenge of aligning IS with business is perhaps more significant and more difficult than ever. Even if the new strategies are now named e-business strategies (Hooft & Stegwee, 2001, Hackbarth & Kettinger, 2000), the basic tasks in planning are still the same: developing strategic vision, governing the projects, allocating resources, planning the infrastructure and ensuring management commitment (Earl, 2000; Venkatraman, 2000).
This paper is based on a view that the early strategic IS planning methods are too static for formulating IS strategies in the new age. On the other hand, given the complexity of issues in the planning agenda and the broad (inter) organisational implications that the new web-based systems often have, relying on a totally informal and incremental planning process involves risks as well. The objective of the four cycles method is to promote continuous planning that involves sufficient degree of formalism to ensure that all critical areas of IS planning are addressed periodically.
The paper begins with an introduction to IS strategy planning and its objectives and describes both formal and informal ways of carrying it out. It then continues to describe the four cycles method to IS strategy planning. For each cycle, relevant prescriptions, tools and outcomes are drawn from e-business planning, strategic IS planning and strategic management literature. At the end of the paper, the contributions for research and practice are discussed.
Objectives for information systems strategy planning
A key outcome of IS strategy planning is a portfolio of information systems that will assist an organisation in executing its business plans and realising its business goals (Lederer and Sethi, 1988). Organisations thus conduct IS planning to identify the most valuable IS projects. They seek applications that provide higher payback (Galliers, 1987), strategic significance (Choe et al., 1998) and congruence with the organisation's competitive needs (Galliers, 1987; Segars and Grover, 1998). Uncertainty has become a way of life. Companies are finding it ever more difficult to predict changes in their environments (Luftman, 1996), which also increases the risk of IS investment failure (Salmela, Lederer and Reponen, 1996; 2000).
IS planning is also concerned with the implementation of these information systems (Sambamurthy et al., 1993; Gottschalk, 1999). An important objective in IS planning is to ensure senior management commitment for implementing the selected projects and to create a partnership between IS and user groups for successful implementation efforts (McLean and Soden, 1977; Segars and Grover, 1998, Teo and Ang, 2001). In addition, IS planning forecasts resource and skill requirements and defines improvements in the IT infrastructure and IS organisation to support both existing and future information systems (McLean and Soden, 1977).
In a turbulent environment, ensuring organisational IS capabilities and IT infrastructure may, in fact, be more significant than the simple selection of a prioritised portfolio of IS applications (Ciborra, 1994).
A more long-term view of IS planning emphasises that planning should also lead to improved managerial capabilities needed in the IS planning itself (Ruohonen, 1991; Raghunathan and Raghunathan, 1991). The planning process should be consciously evaluated and improved (King, 1988; Baker, 1995).
By thus improving the "taken for granted" routines and complex relations between the IS function and other business functions in a firm, IS planning could, in the long run, become a unique capability and a source of sustainable competitive advantage (Mata, Fuerst, and Barney, 1995). E-business planning should therefore not be a one time planning process but a dynamic process that is continuously reviewed and improved.
Learning from comprehensive and incremental approaches for IS strategy planning
Although the objectives of IS planning are generally accepted, this does not apply to the views expressed about the appropriate IS planning process. Some researchers recommend a comprehensive process, while others have suggested that an incremental and informal process best ensures the achievement of IS planning objectives. In a similar vein, planning practices used in different organisations differ as well.
In comprehensive planning, managers attempt to be exhaustive in making and integrating strategic decisions (Sambamurthy et al., 1993). They involve large group of people from different organisational levels in the decision making process (Earl, 1988). The organisation forms committees of users and IS specialists and carries out a procedure of several steps and the study usually takes several weeks or months (Lederer and Sethi, 1992). As part of this procedure they do extensive analyses (Raghunathan and Raghunathan, 1991; Bergeron et al., 1991). To manage the large planning group and diverse analyses, at least some degree of formality is needed in the planning process. Because of the large visibility of decisions, they use documented criteria in making the decisions (Ein-Dor and Segev, 1978). Table 1 summarises practices that are typically used in comprehensive planning.
Planning Characte-ristics | Comprehensive Practices | Incremental Practices | |
1 | Plan comprehen-siveness | Plans are complicated and highly integrated with overall strategy (King, 1978; Premkumar and King, 1994; Raghunathan and King, 1988). | Plans are simple and loosely integrated with overall strategy (Sambamurthy et al., 1994; Ciborra, 1994). |
2 | Approach to analysis | Formal, multiple analyses are used to derive plans (Earl, 1988; Raghunathan and Raghunathan, 1991; Bergeron et al., 1991). | Personal experiences and judgement are used to derive plans (Sambamurthy et al., 1993; Vitale et al., 1986). |
3 | Planning Organi-sation | Planning is based on formal representation from many different organisational groups (Galliers, 1987; Earl, 1988). | Planning is based on an informal network of a few key individuals (Pyburn, 1983; Vitale et al., 1986; Earl, 1993). |
4 | Basis for Decisions | Formal methods and criteria are the basis for decisions (Ein-Dor and Segev, 1978). | Shared group understanding of a few key individuals is the basis for decisions (Sambamurthy et al., 1994; Ciborra, 1994) |
5 | Plan control | IS plans are periodically reviewed to adapt to changed circumstances (Galliers, 1987). | IS plans are continuously reviewed to adapt to changed circumstances (Earl, 1993; Vitale et al., 1986; Sambamurthy et al., 1993). |
Table 1: Comprehensive and incremental views about the IS planning process
A large number of planning methods exist that define almost a step-by-step procedure for a comprehensive formulation of an IS strategy. Instructions for conducting IS planning are provided in Critical Success Factors method (Shank et al, 1985), IBM's Business Systems Planning (Zachman, 1982), and Andersen Consulting's Method/1 (Lederer and Gardiner, 1992), to mention only a few.
The comprehensive approach is grounded in the comprehensive approach to strategy formulation (Faludi, 1976) and in the traditional strategic management theory (Ansoff, 1965; Steiner, 1972; Ansoff and Sullivan, 1993; Rowe et al, 1996).
The critics of comprehensive IS planning have suggested that the need to rely on formal planning methodologies and predefined criteria can trivialise planning so much that it becomes merely a simple top-down exercise (Vitale et al., 1986; Sambamurthy et al., 1993). They have noted that formal planning has also been shown to replace, rather than support informal communication (Pyburn, 1983). A short process does not necessarily provide an environment for learning and for deriving a strategic vision (Reponen, 1994). The critics have also pointed out that users and managers consider comprehensive and formal analyses as costly and remote (Earl, 1993).
The critics warn that in a changing business environment comprehensive planning simply may not provide the necessary flexibility to be effective (Pyburn, 1983; Vitale et al., Ciborra, 1994).
In contrast to comprehensive planning, some organisations practice a more incremental approach. For them, planning focuses on a few or perhaps just one theme and IS decisions are made on a one-by-one basis (Earl, 1993). This focused agenda keeps the planning team small and enables planning to be based on informal contacts among team members (Pyburn, 1983). It also allows the use of personal experiences and experimentation with new and innovative ideas, sometimes at the relatively low levels in the organisation (Ciborra, 1994). Table 1 summarises practices that are typically used in incremental planning.
In incremental approach, explicit planning methods are seen as having only a minor role. While methods can be used, they are seen more as process enablers (Earl, 1993) to be used in an ad-hoc manner (Ciborra, 1994). Consequently, the incremental approach doesn't provide similar explicit step-by-step methods for IS planning, as was the case with comprehensive approaches. The process is informal and rests very much on the ability of key managers to include the right people and conduct the right analyses.
What might be considered as closest to an incremental method is the Continuous Strategic Alignment method described by researchers from the MIT-school in the early 1990s. In essence, the method identifies five different alignment mechanisms (Venkatraman et al., 1993, p. 144):
1. governance process, which specifies the allocation of decision rights
2. technological capability process, which specifies and modifies the IT products and services needed to support and shape business strategy
3. human capability process, which specifies and modifies the various human skills to support and shape business strategy
4. value management process, which allocates the required resources and ensures maximal benefits from IT investments
5. strategic control, which attempts to maintain internal consistency among the four mechanisms
Hence, the method acknowledges the need for a dynamic administrative process to ensure continuous strategic alignment between the business and IT domains.
Incremental planning is based on the theory that organisations learn and benefit by adapting based on their learning (Argyris and Schon, 1978;). It draws many of its principles from the behavioural theories of business strategy making (Quinn, 1980; Minzberg, 1994).
Some reported difficulties illustrate why incremental planning might fail. In particular, senior managers have expressed concern that incremental planning fails to address critical needs (Earl, 1993). For example, from their perspective developing new systems locally can mean that potentially strategic applications can be dismissed as "just end user hacking" and never get sufficient resources to become organisation-wide innovations (Ciborra, 1994). Some IS managers have warned about poor definition of IS requirements and infrastructures (Pyburn, 1983; Earl, 1993). Others have worried about how future planning themes would be generated. A new CEO, management team, or management style could erode the incremental planning process (Earl, 1993). Rapid responses to changing needs have also been seen as increasing the risk of incomplete projects (Pyburn, 1983).
The alleged limitations of incremental approach are concordant with the views stated in strategic management literature that, at the moment, there is limited formal support for the “strategic thinking” aspect.
In other words, a combined method would be needed to support the synthesising of qualitative and quantitative data into visions of the appropriate direction to pursue (Wilson, 1994; Mentzas, 1997; Heracleous, 1998).
The need for a new planning method
Comprehensive planning methods provide clear steps for planning a new IS strategy. Such methods make it easy for a practising IS manager to make a step-by-step plan for a comprehensive IS planning study. The risks associated with large special studies are, however, well documented in the IS planning literature.
Incremental planning literature doesn't provide similar methods to guide an incremental IS planning process. Even the continuous strategic alignment model by Venkatraman et al. (1993) is fairly general. While it identifies five different administrative processes, it doesn't provide detailed instructions for their implementation.
There are, however, reasons why explicit formal planning methods might be useful, even in incremental planning.
Although managers are likely to accept the principles of incremental planning, they may find it difficult to apply them in practice. Particularly in organisations, where managerial knowledge and experience about IS planning is low, methods can help in setting up a planning system. One recent case study (Cerpa and Verner, 1998) reported that methodologies such as CSF provided the means to set up a planning framework and to aid in evaluating the IS strategy.
Also, if the general planning style in the organisation is formal, an IS manager may find it difficult to rely on a very informal IS planning process (Pyburn, 1983; Earl, 1993). Hence, a formal IS planning structure may be needed simply because the senior and business managers are accustomed to such planning.
For instance, Quinn (Quinn, 1980) reported that even if total enterprise strategy is formulated informally and incrementally, top executives still required periodic updates and reviews from different subsystems. Lower level planning also relied on the use of formal methods and techniques. Hence, a formal IS planning structure can make it easier for senior management to integrate IS/IT projects with the events and plans in other subsystems and vice versa.
Finally, explicit methods are also needed in IS planning research, particularly if action research is used. One of the principal guidelines for conducting action research is that researchers should make their reasoning explicit and organise it in such a way that it is testable (Susman and
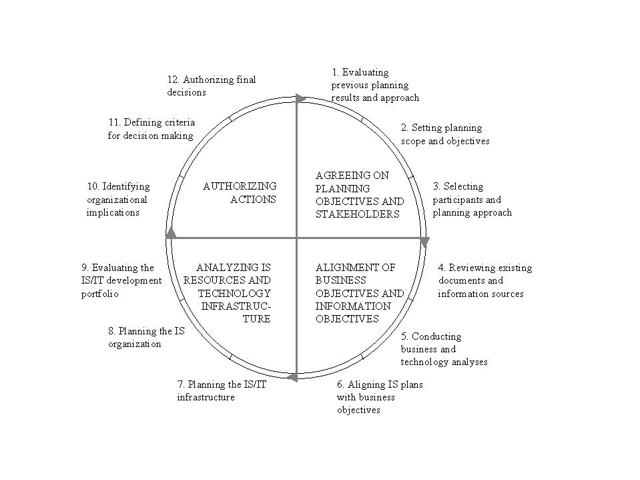
Figure 1 – The Four Cycle method
Evered, 1978). Thus, explicit methods can make it easier for researchers to apply, test and improve the methods in a convincing manner.
The four cycles method
The development of the four cycles method is based on a research program on IS planning. During the years 1985 to 2000, altogether 18 action research projects on IS planning have been conducted, both in the public sector and in private organisations both in Finland and the Netherlands.
In the Netherlands 6 large action studies were conducted at a consultancy firm (85-86), a production organisation of energy systems (86-87) and a bank (88-89)(Wassenaar, 1995). These organisations were evaluated from a transactional perspective. From 1989 till now a longitudinal action study was conducted in a large hospital (Wassenaar, 1995, Spil, 1996, Sikkel et al, 1999). From 1987 till 1996, a university information systems strategy was evaluated and influenced (Spil, 1996) and from 1999 until now we study a facility management organisation (not yet described). All these studies have led to the notion that a “new” method was necessary.
The research program in Finland comprised altogether 12 action research projects during the years 1985 to 2000. (Mills, Reponen and McFarlan, 1988; Ruohonen, 1991; Reponen, 1994; Salmela, Lederer and Reponen, 1996; 2000). The client organisations represented a wide variety of different industries(paper industry, electronics, furniture, finance, wholesale, construction) and public services (labour protection, education, defence). In majority of the cases, planning followed a comprehensive approach, with special emphasis on organisational commitment and learning (Ruohonen, 1991; Reponen, 1993). While many of these planning studies were clearly successful, there were also cases that suffered from lack of involvement and poor implementation of plans (Reponen, 1994). The cases where incremental planning was used were not without problems either. In one case, for instance, planning assisted in identifying a strategic application but failed to provide sufficient resources for its prompt implementation(Salmela, Lederer and Reponen, 2000). Overall, the experiences gained led to the idea that a combined approach might work better than either extremely comprehensive or extremely incremental approach.
The four cycles method divides a chosen period of time into four different planning cycles: 1) agreeing on planning objectives, 2) aligning business objectives and information objectives, 3) analysing IS resources and IT infrastructure, and 4) authorising actions.
The main difference to comprehensive methods is in the process but also typical informal outputs like mind mapping (#18 table 2) are added. The four basic cycles are repeated each period. Analyses that in the traditional comprehensive methods are carried out within a few weeks or months can now be distributed over the whole period. Because the same cycles are repeated periodically, some analyses can be distributed over several years. In addition, the repeating cycles ensure the monitoring and updating of strategies on an annual or even quarterly basis.
The planning cycles and associated planning tasks are summarised in figure 1 and are now elucidated. Because the contents of each cycle are similar to well established comprehensive and incremental methods, repeating all tools and prescriptions was not considered necessary but we want to give more detail than just give an overview. The objective is to illustrate the contents of planning in each cycle by identifying some relevant pieces of research.
First cycle: Agreeing on planning objectives and stakeholders
"There’s nothing more practical than a good theory"
The first cycle begins with an assessment of progress in implementing IS decisions and plans. Also new issues requiring immediate attention can be brought into the planning agenda. If they require immediate action, a special task force can be assigned to start investigating the issues. As each cycle begins with a short update session, implementation of plans can be monitored on a quarterly basis.
The primary planning objective in the first cycle is, however, the evaluation of the selected planning approach. If no problems are evident, an informal situation appraisal of the planning process at the beginning of a new planning year can be adequate (Dyson and Foster, 1980; Baker, 1995). Problems in the planning process, such as inadequate participation or failure to implement plans (Lederer and Sethi, 1988; Premkumar and King, 1994; Mentzas, 1997), suggest that a more thorough analysis may be needed.
The cycle comprises the following three planning tasks:
1.Evaluation of previous planning results
2.Setting the scope of planning and selecting objectives
3.Selecting participants and adjusting the planning approach
In essence, managers are asked to critically assess the results that have been achieved with the organisation's current approach to IS planning. Based on this assessment, they evaluate whether more, or less, of their time should be devoted to IS planning. The managers therefore choose which of the listed activities (table 2-4)they want to perform in the next period. Outcome can be that this year they only produce a thorough list of current and planned projects (#3) but also that all 45 activities are conducted. Also the way planning is approached (degree of formality, comprehensiveness) is discussed. The objective is to choose an approach that best fits the planning environment, planning tasks and expectations of participating managers. In practical terms, the main task in this cycle is to agree on the planning objectives and accept a schedule for the coming period.
Previous IS literature provides many useful analyses that can be used to support these tasks. Some of them are listed below. Furthermore, table 2 lists documents that can be developed, updated and/or used within this cycle.
Evaluation of previous planning results | ||
#1 | Information year report | Contains an assessment of all running projects on the aspects time, money and quality in comparison with the project descriptions as decided upon. A good example is the financial year report. |
#2 | Information management control range | Summarises the claims on budgets and decisions on projects that already have been made. Together with the total budget it shows the range of (financial) planning for information management. |
#3 | List of current and planned projects | Provides a complete overview of all running and planned projects with risks, benefits and participants. |
Setting the scope of planning and selecting objectives | ||
#4 | Set of critical planning objectives | Contains an a set of information objectives that give direction to the content of the outcomes of this planning process. These can be drawn from branche information (benchmarking), from trends analysis and from corporate strategy. |
#5 | List of targeted planning outcomes | Contains a list of the results that senior management and information management wants to reach during the coming year. Results are selected from all outcomes in Tables 1 to 4. In the simple end, outcomes can consist of a list of running and planned projects. In the complex end, a complete set of strategic information systems planning outcomes can be selected. |
#6 | Scope for the IS planning process | This outcome elaborates the objectives and outcomes. It is based on an agreement on the ambition level of the planning process. This ambition can be defined for each outcome as characteristics (focus), time (long middle and short) and description level (global, detail). |
Table 2: Potential outcomes of the first planning cycle
Selecting participants and adjusting the planning approach | ||
#7 | A matrix with objectives, participants and phases | Assigns responsibility for achieving planning objectives to key managers. Schedules the planning process and assigns people to each planning task (when should a task be done, what should be done, and by whom). |
#8 | Educational plan | Defines an overview of knowledge and experience that is needed and available in the planning process. Builds a training program for each participant in the planning process. Each outcome can be connected with a special training program. |
#9 | An informal network of people to be involved | Defines roles for each participant (decide, inform, ask or train). By performing a network analysis, groups of people can be identified that like to work together. |
#10 | Communication plan | Defines communication mechanisms to be used to communicate plans and to keep the process alive. |
#11 | Analysis of contingencies | Describes the IT heritage (existing IT structure and the past successes and failures in IT), technology assimilation (the stage of adoption and management of the technologies in use), and the strategic impact of IS (positioning of the organisation in the strategic grid, assessing past and future strategic dependence on IS). |
#12 | Planning approach and methods | Defines the approach selected to IS planning and explicitly explains how it fits with organisation characteristics described in the analysis of contingencies (#11). |
Table 2: Potential outcomes of the first planning cycle (continued)
Evaluation of previous planning results is a natural starting point for the evaluation of the selected approach. The managers should monitor the implementation of plans, not only to revise the plans, but also to evaluate whether the goals, resources, analyses, processes, outputs and outcomes of the IS planning itself are appropriate (King, 1988; Raghunathan and Raghunathan, 1991). In essence, there should be sufficient feedback mechanisms to allow managers to improve their IS planning effort (McLean and Soden, 1977; Baker, 1995).
Because IS planning can have multiple objectives and it can serve many different interests (Galliers, 1991; Ciborra, 1994), it is important that the emphasis of different objectives is clearly stated. Planners should ensure that senior managers perceive the issues in the planning agenda as important for the strategic goals of the organisation (Ein-Dor and Segev, 1978; Goodhue et al., 1992). Also, short-term opportunities and problems with direct implications to users should not be forgotten (Boynton and Zmud, 1987).
The importance of selecting skilled people from various parts and different levels of the organisation is also well documented (Galliers, 1987; Boynton and Zmud, 1987; Sääksjärvi, 1988; Premkumar and King, 1994; Ruohonen,1991; Spil, 1996). It is also important to define the groups that need to be interviewed, informed or trained (Boynton and Zmud, 1987).
Furthermore, a contingency analysis (Feeny, Edwards and Earl, 1987; Earl, 1989) can be used to evaluate the degree to which the planning approach fits with the contextual variables. Planning approach should not differ too much from the organisation’s general planning style and control structure and it should also reflect the complexity and significance of the organisation’s IS and the consensus about the mission of organisation’s IS department. (Earl, 1989; Doukidis, Mylonopoulos and Lybereas, 1994).
While many researchers have pointed out the significance of critically evaluating the planning approach, existing E-business planning does not incorporate it in the planning process. The four cycles method does not provide a ready made solution. Instead, managers are asked to decide how planning should be approached and whether they find a formal, or informal, approach to be more natural. Such discussions are expected to promote continuity and learning of key participants. Time as a valuable asset in e-business strategy planning should be used as effectively possible.
The second cycle: alignment of business objectives and information objectives
"Information is not a goal, it is a support for the organisation."
Also the second cycle begins with a review of current issues and progress in implementing IS decisions and plans. Thus, if new issues have occurred after the beginning of the first cycle, they can now be addressed.
The main task in the second cycle is to promote strategic thinking, creativity and innovation in the planning process but also to ensure sufficient integration of IS plans with business plans. The emphasis is on identifying future IS projects that provide business value and support both business strategy and business processes.
The second planning cycle comprises three planning tasks:
1.Reviewing existing plans, documents and information sources
2.Conducting business and technology analyses
3.Aligning IS plans with business objectives
In essence, the participating managers are asked to re-examine the assumptions about the business needs and technology opportunities used in previous plans. This new information is then used update IS priorities for the future.
Previous IS literature provides many useful analyses that can be used to support these tasks. Some of them are listed below. Furthermore, table 3 describes documents that can be developed, updated and/or used within this cycle.
Reviewing existing plans, documents and information sources | ||
#13 | List of existing useful documents | Past projects have created a large amount of documentation which, if properly documented, can be reused in the planning process including, for example, workflow diagrams and management control models. |
#14 | Internal information sources | Sources for information about the current IS/IT perspective in the business, its maturity, business coverage and contribution, skills, resources and the technological infrastructure. Current strategy, objectives, resources, and activities and the culture and values of the business. |
#15 | External information sources | Sources for information about technology trends and opportunities and the use made of IS/IT by external bodies. The economic, industrial, and competitive climate in which the organisation operates. |
Conducting business and technology analyses | ||
#16 | Implications of corporate strategy for IS objectives | Identifies business goals and plans and deduces IS requirements via a formal method for translating them. |
#17 | Implications of other business analyses for IS (CSF, SWOT) | Identifies critical processes in the organisation (core competencies) to be supported by information systems. Combines and groups the critical success factors with the strengths, weaknesses, opportunities and threats to derive information objectives. |
#18 | List of new future acts or events | Indicates for the coming three years how markets and clients can change, what opportunities for data retrieval there will be, which technical progression is suspected, which organisational changes are planned and possible, which new methods are in theory available. What is the budget prognosis for the coming years and which new activities can we develop and which activity we should drop. |
#19 | Classification of certainty of acts and events | For each act or event found in outcome #18 a certainty and time scope is given to evaluate which act or event needs attention |
Aligning IS plans with business objectives | ||
#20 | List of new project ideas with priorities | Lists initial project ideas and opinions of the participants about their priorities costs and risks. For high priority ideas the risks and benefits of the ideas are worked out in detail and according to those results a new priority scheme is made. |
#21 | Aligned IS plan and project priorities | Documents the shared vision between senior managers of the organisation in which direction information systems should go. Clear priority decisions are made by senior management and information management on which objectives and which ideas priority is given. |
#22 | Senior management participation | Describes how senior management will control that the agreed priorities are taken into consideration in the rest of the planning process. |
Table 3: Potential outcomes of the second planning cycle
Even if the objective in the second cycle is to create new plans, existing IS plans can be used as a flexible framework within which the implications of changing circumstances/ strategies can be identified and managed (Galliers, 1991). Information sources analysis can also be used to evaluate current planning documents and existing information sources (Ward and Griffith, 1996).
The corporate business strategy (if such exists) can be carefully studied each year and all impacts for information management listed. Other business analyses can embody the analysis of current and future business environments, critical success factors, strengths and weaknesses, and programs of the organisation (King, 1988; Raghunathan and Raghunathan, 1991).
The relationship between strategic business plans and information systems plans should be seen as an iterative (Henderson and Sifonis, 1988). Hence, the process should also incorporate the tracking of key developments in technology to enable the managers to spot opportunities, which can give them a competitive advantage (Boynton and Zmud, 1987; Earl, 1988). Also, the likelihood of events can be evaluated (Mintzberg, 1994).
Brainstorming sessions can be used to discuss new ideas for using information systems. Buzan (1995) has developed an instrument to make quick associations with a specific subject. A voting system can be used to decrease the number of ideas (Stevens, 1997). In any case, the process should reduce conflict that revolves around uncertain assumptions (Henderson and Sifonis, 1988) and it should also enhance communication of the objectives between senior management, IS management, and user management (Ruohonen, 1991).
Given the amount of interest in aligning IS with business, it is no surprise that the analyses in the second cycle are quite "traditional".
In comprehensive methods (and in the planning practice in many companies) innovation of new opportunities and making of organisational decisions about IS priorities are scheduled very close to one another. Since many stakeholders also need to protect their own interests and needs, such process does not promote "creativity and strategic thinking". In the four cycles method, the second cycle is devoted to analysis and innovation. Final decisions can be made later. There must be room for new ideas. Restrictions are the emergent nature of the changes and the difficulty of formalising creativity and innovation.
The third cycle: Analysing IS resources and IT infrastructure
"A new information system is rarely build upon a green field site."
Again, the cycle begins with a review of current issues and progress in implementing IS decisions and plans. Thus, if new issues have occurred after the beginning of the second cycle, they can now be addressed.
The planning during the third cycle concentrates on assessing current information and communication technology (ICT) architecture and IS skills, and in preparing for the future. The cycle can be seen as comprising the following three planning tasks:
1. Planning the ICT infrastructure
2. Planning the ICT organisation
3. Development of a preliminary project portfolio
The third cycle adds realism to planning by bringing in resource capacities and constraints under which the information systems function operates. A concrete objective is to develop a preliminary project portfolio that includes both IS development projects and projects for improving the ICT infrastructure.
Previous IS literature provides many useful analyses that can be used to support managers in these tasks. Some of them are listed below. Furthermore, table 4 describes documents that can be developed, updated and/or used within this cycle.
Planning the IS/IT infrastructure | ||
#23 | Identification of core business areas | The identification of the core business areas elaborates earlier analysis of core business processes (outcome #17) with the analysis of the degree to which a competence is significant in terms of access to wider markets, customer significance, and risk of imitation. |
#24 | IS support for core business areas | Describes for each core area why it is important and how each area are composed (results of the noun/verb analysis). Illustrates supportive IS functions (results of the functional analysis systems technique diagrams). |
#25 | IS needs | Describes the information needs, conceptual information systems, the business conclusions and recommendations, the application portfolio and the business information models. |
#26 | Information technology developments | Identifies most relevant IT developments from the business perspective. Reviews the latest publications in IT and describes shortly a reference list to access more information (most likely hyperlinks). |
#27 | Technology assimilation plan | Defines a timetable for adopting the most promising technologies, given the current technology and IT heritage of the organisation. |
#28 | Future | Management and control description of the future data, application, computing and communication infrastructure. |
Planning the IS organisation | ||
#29 | Strategy and structure of the IT function | Contains a decision on the location of the responsibility, authority and activities of information management either centralised, distributed or decentralised. |
#30 | Rules and regulations for the IT function | Describes general rules as well as quality and service levels for all services provided by the information management function. These agreements can be matched with financial agreements between the IT function and users. |
Evaluating the IS/IT development portfolio | ||
#31 | Current investments and costs | Provides a clear picture of the current financial situation of all IS cost centers with given budget and used budget. Provides a long term prognosis of project budgets in major on-going IS/IT projects. |
#32 | Future investment possibilities | Describes the future capabilities of the IS function to initiate new projects and to maintain high quality in the provided services. |
#33 | IS future benefits | Defines the overall quantitative and qualitative benefits that the IS/IT project portfolio can leverage. |
#34 | Proposed IS/IT project portfolio | Describes the proposal for the IS/IT portfolio and documents other important outcomes the scenario analysis process. |
Table 4: Potential outcomes of the third planning cycle (continued)
Weill and Broadbent (1998) provide a large selection of tools and concepts for developing an ICT infrastructure. Such tools enable development of IT infrastructure that supports strategic applications and integration of multiple businesses or functional groups. They also assist in demonstrating the value of IT investments to senior management.
Mentzas (1997) and Ward and Griffith (1996) provide a comprehensive list of tasks for making IS/IT infrastructure decisions: diagnose current state and describe functional descriptions for each process, identify functional inefficiencies, create new business process models and analyse both organisational processes and interdepartmental relations (Ward and Griffith, 1996).
Functional analysis techniques from strategic management can also be helpful in analyses (Stevens, 1997). For each core business area two questions can be asked: why is this area so important and how is it composed (noun/verb analysis). With Functional analysis diagrams a group can identify supportive IS functions (Stevens, 1997).
IS organisation and the development of human resources is an important category in the ICT infrastructure (Earl, 1989; Ward and Griffith, 1996; Galliers and Baker, 1994). A functional centralisation-decentralisation model can be used to describe the structure of the IS organisation (Robson, 1997). The rules, policies and regulations for ensuring integrity of infrastructure and information can now be evaluated and updated (Earl, 1989). Also, questions related to outsourcing of IS services can be addressed (DeLooff, 1997).
Scenario analysis can be used to formulate a preliminary IS/IT project portfolio (Schoemaker, 1995). A comprehensive analysis can involve 10 steps, starting from identification of scenario themes, stakeholders and technology trends and ending up in constructing initial scenario themes, checking for consistency and plausibility, identifying research needs and evolving towards decisions.
The infrastructure is increasingly seen as a fundamental resource that differentiates the competitive performance of firms (McKenney et al, 1995; Weill and Broadbent, 1998). Making right decisions about ICT infrastructure is a challenging task. In principle, the decisions would require multiple analyses from both technical and business perspectives. It is also obvious that the decisions have to be made incrementally, as both business needs and technology options evolve over time.
Making long-term decisions about ICT infrastructure within one comprehensive study is difficult. The advantage of the four cycles method is that the plans for ICT infrastructure and IS organisation are updated periodically. New infrastructural challenges can be emerging and taken into account.
The fourth cycle: authorising actions
"No statements but actions"
If new issues have occurred after the beginning of the third cycle, they should be addressed before seeking approval for the major IS projects.
The fourth cycle concentrates on preparing clear proposals for action. The objective is to ensure firm commitment of resources to implement the IS projects and to acquire the IT resources and IS capabilities. This cycle comprises the following three planning tasks:
1. Identifying organisational implications
2. Defining criteria for decision making
3. Authorising final decisions
The emphasis in the fourth planning cycle is to identify major organisational and business changes associated with the projects and to seek line management acceptance for them. The primary objective is to reduce potential for conflict that might jeopardise the implementation of plans (Segars and Grover, 1998).
Previous IS literature provides many useful analyses that can be used to support managers in these tasks. Some of them are listed below. Furthermore, table 5 describes documents that can be developed, updated and/or used within this cycle.
Identifying organisational implications | ||
#35 | Impact on organisation | Lists organisational implications (both positive and negative) for each proposed project, as seen by users and specialists. |
#36 | Contingency plan | Identifies changes that can happen in the near future and identifies actions that can/should be taken in individual projects if changes occur. |
#37 | Human resource plan | Assigns human resources to projects and defines an education plan associated with each. |
#38 | First drafts of project proposals | For each IS/IT project, a draft project proposal is formulated which describes the business reasons for initiating the project. |
Defining criteria for decision making | ||
#39 | A uniform set of selection criteria | Lists the criteria to be used in selecting IS/IT projects, e.g. fit with the organisational objectives and information needs, availability of resources (expertise, time and money) for execution, project costs and benefits. |
#40 | Weighing of the criteria | If level and importance of criteria differs too much then a weighing of the criteria can be defined. |
Authorising final decisions | ||
#41 | The concept of IS/IT portfolio | Describes the IS/IT portfolio with the highest score. Provides a tentative choice that can be communicated to relevant stakeholder groups. |
#42 | Stakeholder views on IS/IT portfolio | Documents the views expressed by different groups during a group (or bilateral) selection process. Summarises commonly accepted choices as well as controversial issues. |
#43 | Risk and value analysis | Summarises the risks and benefits of tentative IS/IT portfolio(s) as a whole and lists the projects in terms if risks and benefits/value. |
#44 | Final IS/IT portfolio | Describes the IS/IT portfolio that has been formally approved by top management. |
#45 | IS management coordination structure | Assigns responsibility of implementing the different projects and defines how the progress in implementing the plans will be monitored. |
Table 5: Potential outcomes of the fourth planning cycle
Organisational implications of implementing the IS plan should now be carefully included in the plan (Galliers, 1987). An organisation plan in Andersen Consulting's Method/1 comprises issues such as assignment of personnel to tasks, development of change management approach, and identification of issues that can prevent, or facilitate, adoption (Lederer and Gardiner, 1992).
Defining criteria for decision making constitutes an important task in the authorisation cycle. Even the most carefully prepared action plan can stumble, if there is no method for setting prioritising between alternative options (Hopstaken and Kranendonk, 1991).
Value management (Stevens, 1997) can be used to increase commitment to decisions. In this approach, the formal authorisation starts with a concept of final IS/IT project portfolio. A group process or bilateral processes can be used to create a common perspective and clearly note all exceptions of the common perspective. In any case, the decision process should allow ample opportunity for debate and airing of different views (Checkland, 1991; Galliers, 1987).
The actual authorisation process in the four cycles method does not differ remarkably from the prescriptions in comprehensive methods. IS decisions are approved as one integrated plan. However, it is important to note that in the four cycles method, the implementation of decisions is monitored on a quarterly basis. Periodic review of plan implementation in the beginning of each cycle should ensure that important projects are not delayed because of lack of resources or organisational politics.
Also, modifications can be made on a quarterly basis to adapt to changes in technology or business environment. In a volatile business environment, using a whole calendar year to generate new plans can be too slow. In such environment, a planning period can be reduced to six or even four months. Such planning would allow plans to be recreated even within a very short time.
Contributions and conclusion for practice and research
Much of the strategic IS planning methods popularised in the late 1980s and early 1990s have gone out of favour. Managers still remember the problems in implementing the detailed plans that resulted from the IS strategy studies. They are also painfully aware that the real business challenge is not to achieve strategic alignment when planning is carried out, but the ability to continuously refresh and adapt the strategic vision that aligns IS with business.
The objective of the four cycles method is to facilitate managers in implementing a continuous planning process. It provides a periodic planning schedule and identifies issues (Each period had a constant focus on external developments and the fit with internal possibilities) that should be addressed periodically. Hence, the method should be useful in organisations that prefer to have some degree of formalism in their IS planning process.
It is important to note, however, that the process allows considerable flexibility in choosing an appropriate planning process. Hence, planning can be adapted to the significance of the issues (or themes) in the planning agenda. It can also reflect the expectations of "good management practice" in the organisation as a whole.
If managers consider informal IS planning as most appropriate and natural, the process can be designed to meet only the minimal requirements. The managers can decide to have periodically only two meetings: analysis of planning results and monitoring of current and planned implementations. Every second period they can make an IT developments inventory and discuss future IT infrastructure. Once in every three periods, a special session for the alignment of information domain and the business domain can take place.
For those organisations that prefer to have a more comprehensive process, more extensive analyses can be conducted in different planning cycles. For this purpose, the method provides a selection of relevant prescriptions and tools from previous IS planning literature. These can be used to ensure that the time used in planning meetings is effective. By making clear priority decisions, scarce time and resources can be spared and used elsewhere.
In general, the objective is to establish a continuous e-business planning process and to ensure that all critical aspects of IS planning addressed periodically. Thus, managers can use the method to reduce the gap that often exists between the planning prescriptions and the way planning is practised.
If the four cycles method is compared with previous comprehensive methods, the key difference is that the planning process is continuous and repetitive. The continuous and repetitive nature of the process permits periodic evaluation of the selected planning approach. It should also promote innovation and creativity, as the idea generation does not have to be closely associated with the making of decisions over IS projects. Also, the complex analyses and decisions about ICT infrastructure can be made incrementally, over several years. In essence, it should avoid many of the problems typically associated with the comprehensive approaches.
The four cycles method adopts many features from the incremental IS planning literature. Most importantly, the process is seen as continuous and it allows reformulation of plans throughout the period. The key difference comes from the role of formal methods. While acknowledging that formal methods can only be one building block, it is assumed that even incremental IS planning could benefit from a formal planning structure and schedule.
The use of a formal method is presented as one means for an organisation to avoid some of the alleged problems of the incremental approaches, such as poor definition of infrastructures, high proportion of incomplete projects or discontinuity in planning due to changes in the management team.
The four cycles method is well grounded to existing literature and to a series of action research projects conducted in several organisations. Nevertheless, it has not been tested in practice. The rationale for describing the four cycles method prior to testing it is that the description provides a basis for future action research projects. The objective is to explicate the reasoning behind the four cycles method and to make it publicly testable. Future research is needed, however, to demonstrate the methods strengths and weaknesses, to establish under what circumstances it is more applicable and also under what circumstances it is less applicable.
Thus, perhaps most importantly, this paper argues that the use of appropriate IS planning methods is still relevant for recognising and making of E-business strategy, both for research and for practice. Future research should focus on the inter-organisational nature of e-business strategy. If it is difficult to get top management participation, it will be more difficult with more organisations involved.
References
Ansoff, H.I. (1965) Corporate Strategy, McGraw Hill, 1965.
Ansoff, H.I. and Sullivan, P.A. (1993) Optimizing Profitability in Turbulent Environments: A formula for Strategic Success, Long Range Planning, 1993, vol. 26, no. 5, pp. 11-23, 1993.
Argyris, C. and Schon D. (1978) Organizational Learning: A Theory of Action Perspective, Addison Wesley, Reading MA, 1978.
Baker, B. (1995) The role of feedback in assessing IS planning effectiveness. Journal of Strategic Information Systems, 4(1) 61-80.
Bergeron F., Buteau C., Raymond L., (1991), Identification of strategic information systems opportunities: Applying and comparing two methodologies, MIS Quarterly, March 1991, vol. 15, no. 1, pp. 89-101.
Boynton, A.C. and Zmud, R.W. (1987) Information Technology Planning in the 1990’s: Directions for Practice and Research. MIS Quarterly, 11(1) March 59-71.
Buzan, T. (1995) The mind mapping book, BBC books, London, 1995.
Cerpa, N. and Verner J.M.(1998), Case study: The effect of IS maturity on information systems strategic planning, Information & Management, vol. 34(4) pp. 199-208.
Chan, Y E, Huff, S L, Barclay, D W, & Copeland, D G (1997)Business strategic orientation, information systems strategic orientations and strategic alignment, Information Systems Research, 8, 2 pp 125-150.
Checkland P. (1991) From framework through experience to learning: the essential nature of action research, In: Nissen H-E. Klein H.K., Hirschheim R., (eds.), Information Systems Research: Contemporary Approaches & Emergent Traditions, North Holland, 1991.
Choe, J-M. Lee, Y-H. and Park, K-C. (1998) The relationship model between the influence factors and the strategic applications of information systems. European Journal of Information Systems 7(2), 137-149.
Ciborra, C. (1994) The grassroots of IT and Strategy. In Ciborra C and Jelassi T, Strategic Information Systems: a European perspective. John Wiley and Sons, Chisester.
DeLooff, (1997) Information Systems Outsourcing Decision Making: A Managerial Approach, Idea Group Publishing, London.
Doukidis, G.I. Mylonopoulos, N.A. and Lybereas, P. (1994) Information Systems Planning within Medium Environments: a Critique of Information Systems Growth Models, International Transactions in Operational Research, 1(3) 293-303.
Dyson, R.G. and Foster, M.J. (1980) Effectiveness in strategic planning, European Journal of Operational Research, 5(3) September 163-170.
Earl, M.J. (1988) Formulation of Information Systems Strategies: Emerging Lessons and Frameworks. In Earl M, (ed), Information management: the strategic dimension, Claredon Press, Oxford.
Earl, M.J. (1989) Management strategies for information technologies. Prentice Hall, New York.
Earl, M.J.(1993) Experiences in Strategic Information Systems Planning, MIS Quarterly, March 1-24.
Earl, M.J., (2000) Evolving the e-business, Business Strategy Review, 11(2), 33-38.
Ein-Dor, P. and Segev, E. (1978) Organisational context and the success of management information systems, Management Science, 24(10) 1064-1077.
Faludi, A. (1976) Planning Theory, Pergamon Press, Oxford.
Feeny, D.F. Edwards, B. and Earl, M.J. (1987) Complex organisations and the information systems function-a research study. Oxford Institute of Information Management research and discussion paper (RDP 87/7). Templeton College. Oxford.
Galliers, R.D. (1987) Information systems planning in the United Kingdom and Australia - a comparison of current practice. Oxford Surveys in Information Technology,4 223-255.
Galliers R.D. (1991) Strategic information systems planning: myths, reality and guidelines for successful implementation. European Journal of Information Systems, 1(1), 55-63.
Galliers, R.D. and Baker, B. (1994) Strategic Information Management. Butterworth-Heineman.
Gottschalk, P. (1999) Strategic information systems planning: the IT strategy implementation matrix, European Journal of Information Systems, 8, 107-118.
Goodhue, D.L. Quillard, J.A. and Rockart, J.F. (1992) Managing the data resource: a contingency perspective, MIS Quarterly, September 373-191.
Hackbarth, G. & Kettinger, W.J.(2000)Building an E-business strategy, Information Systems Management, 17, 3, Summer, p78.
Henderson, J.C. and Sifonis, J.G. (1988) The value of strategic IS planning: understanding consistency, validity and IS markets, MIS Quarterly, June 187-200.
Heracleous, L. (1998) Strategic Thinking or Strategic Planning? Long Range Planning, 31(3) 481-487.
Hooft, F.P.C. van & Stegwee, R.A.(2001)E-Business Strategy: How to benefit from a Hype, Logistics Information Management,14, ½, pp 44-54.
Hopstaken, B. and Kranendonk, A. (1991) Informatieplanning; puzzelen met beleid en plan (in Dutch), Kluwer, Deventer.
King, W.R. (1988) How effective is your information systems planning? Long Range Planning, 21(5) October 103-112.
Lederer A.L., Gardiner V. (1992) The process of strategic information planning, Journal of Strategic Information Systems, March, 1992, 1(2), 76-83.
Lederer, A. and Salmela, H. (1996) Toward a theory of strategic IS planning , Journal of Strategic Information Systems, 5(3) 237-253.
Lederer, A. and Sethi, V. (1988) The implementation of Strategic Information Systems Planning methodologies, MIS Quarterly, 12(3) September 445-462.
Lederer, A. and Sethi, V. (1992) Meeting the Challenges of Information Systems Planning, Long Range Planning, 25(2) April 69-80.
Luftman, J.N. (1996) Competing in the information age, Oxford University Press.
Mata, F.J. Fuerst, W.L. and Barney, J.B. (1995) Information Technology and Sustained Competitive Advantage: A Resource-Based Analysis. MIS Quarterly 19(4) 488-505, 1996.
McKenney, J.L. Copeland, D.C. Mason, R.O. (1995) Waves of Change: Business Evolution through Information Technology, Harvard Business School, Boston.
McLean, E.R. and Soden J.V. (1977) Strategic Planning for MIS. John Wiley and Sons.
Mentzas, G. (1997) Implementing an IS Strategy – A Team Approach, Long Range Planning, 30(1) 84-95.
Mills, R.G., Reponen T., McFarlan F.W., (1988) Finnpap/Finnboard, Harvard Business School teaching case nr. 9-188-103.
Mintzberg, H. (1994) The fall and rise of strategic planning, Harvard Business Review, January-February 107-114.
Niederman, F. Brancheau J.C. and Wetherbe J.C. (1991) Information Systems Management Issues for the 1990s, MIS Quarterly, December 1991, 475-495.
Porter, M. and Millar, V. (1985) How information gives you competitive advantage, Harvard Business Review, July-August 149-160.
Premkumar, G. and King, W.R. (1994) The evaluation of SISP, Information & Management, 26 327-340.
Pyburn, P.J. (1983) Linking the MIS plan with corporate strategy: an exploratory study, MIS Quarterly, 7(2) 1-14.
Quinn, J.B. (1980) Strategies for change, logical incrementalism, Homewood, Il.
Raghunathan, T.S. and King, W.R. (1988) The Impact of Information Systems Planning on the Organization, OMEGA, 16(2) 85-93.
Raghunathan, B. and Raghunathan, T.S. (1991) Information Systems Planning and Effectiveness: An Empirical Analysis, OMEGA, 2/3 125-135.
Reponen, T. (1993) Strategic information systems - a conceptual analysis, The Journal of Strategic Information Systems, 2(2) June 100-104.
Reponen, T. (1994) Organizational information management strategies, Journal of Information Systems, 1994, vol. 4, 27-44.
Robson, W. (1997) Strategic Management and Information Systems. Pitman. London.
Rowe, A.J. Mason, R.O. Dickel, K.E. Mann, R.B. and Mockler, R.J. (1996), Strategic Management: A methodological Approach, Addison Wesley Publishing Company, Reading, MA.
Ruohonen, M. (1991) Stakeholders of strategic information systems planning: theoretical concepts and empirical examples, Journal of Strategic Information Systems, 1(1) 15-28.
Sääksjärvi, M. (1988) Information Systems Planning: What makes it successful? Australian Computer Conference proceedings, 523-542.
Salmela, H. Lederer, A.L. and Reponen, T. (1996) Prescriptions for IS planning in a turbulent environment, proceedings of the ICIS conference, Cleveland, pp. 356-368.
Salmela, H. Lederer, A.L. and Reponen, T. (2000) Information Systems Planning in a Turbulent Environment, European Journal of Information Systems, 9(1) 3-15.
Sambamurthy, V. Venkatraman, S. and DeScantis, G. (1993) The design of information technology planning systems for varying organizational contexts, European Journal of Information Systems, 2(1) 23-35.
Schoemaker, P.J.H. (1995) Scenario Planning: a tool for strategic thinking, Sloan Management Review, Winter 36(2) pp. 25-40.
Segars, A.H. and Grover,V. (1998) Strategic information systems planning success: An investigation of the construct and its measurement, MIS Quarterly, June 139-162.
Shank, M.E. Boynton, A.C. and Zmud R.W. (1985) Critical Success Factor Analysis as a methodology for MIS planning, MIS Quarterly, 9(2), 121-129.
Sikkel, K, Spil, T A M & Weg, R L W van de (1999)A real-case study in information technology for undergraduate students, Journal of Systems and Software, 49, pp117-123.
Spil, T.A.M. (1996) The effectiveness of SISP in professional organizations, PhD thesis. University of Twente. ISBN 90-9009588-8. Enschede.
Steiner, G.A. (1972) Comprehensive Managerial Planning, The planning executives institute, Oxford, Ohio, 1972.
Stevens, D. (1997) Strategic Thinking. McGraw Hill, Australia.
Susman, G.I. and Evered, R.D. (1978) An assessment of the scientific merits of action research, Administrative Science Quarterly, December 1978, vol. 23, pp. 582-603.
Teo, T.S.H. & Ang, J.S.K.(2001)An examination of major IS planning problems, Internation journal of Information Management, 21, pp457-470.
Venkatraman, N. Henderson, J.C. and Oldach S. (1993) Continuous Strategic Alignment: Exploiting Information Technology Capabilities for Competitive Success, European Management Journal, 11(2), 139-149.
Venkatraman, N. (2000) Five steps to a dot-com strategy: How to find your footing on the web, Sloan Management Review, Cambridge, 41(3) 15-28.
Vitale, M.R. Ives, B. and Beath, C.M. (1986) Linking information technology and corporate strategy: An organizational view, In: Proceedings of the Seventh International Conference on Information Systems, 15-17.
Ward, J. and Griffith, P. (1996) Strategic Planning for Information Systems, 2nd edition, John Wiley and Sons, Chichester.
Wassenaar, D A (1995)Informatieplanning in transactioneel perspectief, PhD Thesis, Free University, Amsterdam.
Weill, P. and Broadbent, M. (1998) Leveraging the new infrastructure: How market leaders capitalize on information technology, Harvard Business School Press.
Wilson, I (1994) Strategic Planning isn’t dead – it changed, Long Range Planning, 27(4) 12-24.
Zachman, J.A. (1982) Business Systems Planning and Business Information Control Study: A Comparison, IBM Systems Journal, 21(1), 31-53.
 Chapter 2 – Agreement of the IS Strategy Agenda
Chapter 2 – Agreement of the IS Strategy Agenda
Evaluation of previous planning results | ||
#1 P29 | Information year report | Contains an assessment of all running projects on the aspects time, money and quality in comparison with the project descriptions as decided upon. A good example is the financial year report. |
#2 P31 | Information management control range | Summarises the claims on budgets and decisions on projects that already have been made. Together with the total budget it shows the range of (financial) planning for information management. |
#3 P34 | List of current and planned projects | Provides a complete overview of all running and planned projects with risks, benefits and participants. |
Setting the scope of planning and selecting objectives | ||
#4 P36 | Set of critical planning objectives | Contains an a set of information objectives that give direction to the content of the outcomes of this planning process. These can be drawn from branche information (benchmarking), from trends analysis and from corporate strategy. |
#5 P40 | List of targeted planning outcomes | Contains a list of the results that senior management and information management wants to reach during the coming year. Results are selected from all outcomes in Tables 1 to 4. In the simple end, outcomes can consist of a list of running and planned projects. In the complex end, a complete set of strategic information systems planning outcomes can be selected. |
#6 P44 | Scope for the IS planning process | This outcome elaborates the objectives and outcomes. It is based on an agreement on the ambition level of the planning process. This ambition can be defined for each outcome as characteristics (focus), time (long middle and short) and description level (global, detail). |
Selecting participants and adjusting the planning approach | ||
#7 P50 | A matrix with objectives, participants and phases | Assigns responsibility for achieving planning objectives to key managers. Schedules the planning process and assigns people to each planning task (when should a task be done, what should be done, and by whom). |
#8 P52 | Educational plan | Defines an overview of knowledge and experience that is needed and available in the planning process. Builds a training program for each participant in the planning process. Each outcome can be connected with a special training program. |
#9 P59 | An informal network of people to be involved | Defines roles for each participant (decide, inform, ask or train). By performing a network analysis, groups of people can be identified that like to work together. |
#10 P62 | Communication plan | Defines communication mechanisms to be used to communicate plans and to keep the process alive. |
#11 P64 | Analysis of contingencies | Describes the IT heritage (existing IT structure and the past successes and failures in IT), technology assimilation (the stage of adoption and management of the technologies in use), and the strategic impact of IS (positioning of the organisation in the strategic grid, assessing past and future strategic dependence on IS). |
#12 P65 | Planning approach and methods | Defines the approach selected to IS planning and explicitly explains how it fits with organisation characteristics described in the analysis of contingencies (#11). |
Way 1 – Information Year Report
By Gerben de Haan
Introduction
The goal of the information year report is to give an overview of all running projects on
the aspects time, money and quality in comparison with the project descriptions
[SALM02]. This will give an insight in the ability of an organization to complete IS/IT
planning and implementation projects successfully and may form a base for improvement
processes throughout the organization.
Not only the outcomes of an implementation project should be evaluated, but also the
process that led to the outcomes should be incorporated in the evaluation. This places the
actual outcomes in perspective. The process should be assessed by, amongst others,
matters of staffing and skills, project organization, risk assessment and project
communication [DEPF97] [SALM02].
Why?
Before starting a new cycle of strategy definition, of whatever kind, it is important to
evaluate previous cycles [SALM02]. Based on these previous planning experiences and
the effectuation of this planning, organizations can learn and improve their planning and
project methodologies. Dymoke-Bradshaw and Cox refer to evaluation of IS/IT processes
as a “coupling mechanism between use and design” and as a “tool for continuous learning
and improvement” [DYM01].
As presented by the empirical study of Kumar on post-implementation evaluation of IS
implementation processes [KUM90] IS executives do not need additional evaluation
methodologies, but determining what criteria to evaluate is much more important. At the
time of Kumar’s study, the lack of agreement upon evaluation criteria was likely to
hinder the evaluation process [KUM90]. The information year report-tool specifies these
criteria and can thereby contribute to the evaluation process significantly.
What?
The information year report should assess IS implementation projects on both process
and product. The criteria to assess product on are: time, money and quality. Whereas the
criteria to asses the process on are: people involved, communication plans, progress
evaluation.
An information year report should consist of an analysis, and maybe summarization, of
all individual project assessment reports. These reports provide an historical record of the
planned and actual budget and schedule of IS/IT projects [DEPF97]. Depending on the
number of projects running, the report contains an extensive description of each
individual project or presents an aggregated general “lessons learned” document. With
this document, management can redefine planning and project methodologies [DYM01].
As Kumar found, the criteria money and quality form a major part of the least assessed
criteria in post implementation evaluation processes. [KUM90] According to Kumar
most evaluation processes focus on technical criteria as availability, accuracy of
information and user satisfaction. The process evaluation criteria as defined above are
only assessed partially. Most post-implementation evaluations do asses the project
schedule, but lack an evaluation of perception of the process according to people
involved.
When?
The process of analyzing the IS/IT projects and writing the information year report
should be a periodically repeated activity of every organization that is conscious of the
importance of IS/IT within their organization. Obviously, all organizations should be
conscious of this. The information report analyses should be started either at the end of a
planning project or at the beginning. [SALM02] According to Kumar, evaluations are
mainly conducted at the end of a project, marking the official end. He states that this
finalization of a project is an important reason to plan evaluations. It is one of the few
methods to mark the end a project. [KUM90]
Many articles refer to Post-Implementation Evaluation when assessment on criteria as
defined above is described. [DEPF97] This seems the most logical moment, everyone
involved is still into the project, and probably has a clear view on issues encountered.
Who?
Question rises who should be involved in the assessment that ultimately leads to the
information year report. According to many articles on evaluating, (representatives of) all
groups of stakeholders should be involved [DEPF97] [DYM01]. Since different groups of
stakeholders have different roles, interests and concerns there should be a difference in
approaching the different groups.
In a IS/IT evaluation the population to be involved should ideally consists of: [DEPF97]
•The project team
•Stakeholder representatives, including external project oversight
•Executive management
•Maintenance and operation staff
Best result is achieved when the evaluation is initiated by IT project planning managers
or the IT department responsible for the roll-out of the projects [KUM90] [DEPF97].
How?
To assess IS/IT projects, subsequently followed by aggregating “lessons learned” for the
information year report, several questions need to be agreed upon by the stakeholders.
As discussed in the previous section, the project (planning) manager should be
responsible for the assessment. This employee should consult representatives of all
groups of stakeholders as listed above. Depending on the group, different questions
should be asked. The same questions may be asked to multiple stakeholder groups.
An example list of questions per stakeholder group is listed in table 1.
Stakeholder group Questions
Project team
•Did the delivered product meet the specific requirements and goals of the project?
•Was the project schedule met?
•Were risks identified and mitigated?
•Did the project management methodology work?
End-users
•Are you satisfied with the end product?
•Are all benefits as proposed when starting the project covered in the end product?
•Were you involved well enough during design phase?
•Were you educated well enough?
Management
•Were cost budgets met?
•Was the progress adequately communicated?
Maintenance and operation staff
•Did the delivered product meet the specific requirements and goals of the project?
•Do the operational conditions of the endcproduct meet the situation as specified in the
design documents?
•Does the system conform to the operational needs of the company?
Table 1 – Example evaluation questions per stakeholder group [NSW03][DEPF97]
This list of questions needs to be specified and extended extensively in a specific
situation. This table just gives in idea of which questions to ask. Something to focus on
when developing evaluation questions is to keep them as sharp and clear as possible.
Vague or ambiguous questions will not contribute anything to the evaluation [DEPF97].
The result
After the assessment of the currently running, or lately finished project, there should be
some form of aggregation. This aggregation analyses the different project evaluations and
leads to an overview of general issues in IS/IT planning and implementation for the
organization subject of the evaluations. These general issues can be reacted upon and
methodologies, protocols and processes can be adjusted accordingly.
Way 2: Information management control range
“determining the reach an range of the IS-planning process”
By Henk van den Hazel
Introduction
When an IS-planning process is started, management must know what reach and range of their systems is required. Which services must be shared and to whom must the organization be able to connect. In the past already investments have been made and this projects have impact on determining the direction for future projects. This tool gives management an opportunity to determine the business functionalities needed to align reach and range of their systems.
What
The reach and range tool is a model developed by Keen[Keen91]. It determines the degree in which an organization wants there IS/IT to function as an integrated part or as separated islands.
Keen’s model has two dimensions:
•Reach:
This is the degree in which the IT-infrastructure is supposed to be able to connect with other systems in- and outside the organisation. IT infrastructure is a important business resource and is now seen as a key source for attaining sustainablecompetitive advantage
•Range:
The range is the variety of services and information that will be shared among internal and external users of the organization
These two criteria are combined in a matrix . The outcome of this matrix is a useful planning tool for management. By knowing where you are and knowing where you want to go, it is quite simple to make a plan to get to the desired situation.
Reach and range must be in balance. A good IT-infrastructure without services to share isn’t very useful. A variety of services without an infrastructure to make it work, isn’t very useful either. The direction of the planning process must therefore be towards restoring the balance. Otherwise the much money and time will be spoiled.
What an organization does with the outcomes of this tools depends on strategy they are following. Most organization prefer moving to open systems.
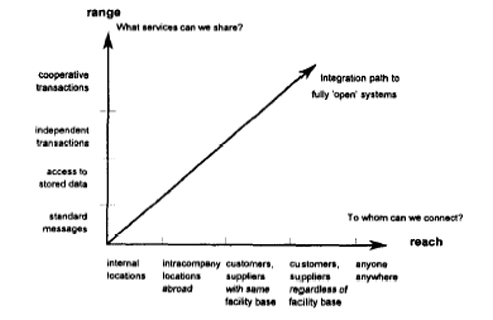
Why
Using this tool is important because research points out, that organizations who are using an integrated approach are more efficient an do have more opportunities to cooperate with other organizations.[Broadbent99] Therefore an organization must consider which level of connectivity and which breadth of services is suitable in their environment.
When
Determining the information management control range is part of the evaluation of previous planning results and should therefore be used in the same phase as the information year report and the list of current and planned projects. Because the output of this tool is an important input for the next cycle it is important that this tool is used when the IS planning process just has started.
How
First IS-management can score their organization on reach and range. After that all relevant stakeholders have an informal meeting. In this meeting the IS-manager can lead an brainstorm in which the management orients itself in which direction it want to develop their IS/IT. Often this will be quite simple, because most organizations wants to move to open systems. The third step is to determine how to reach the desired position. Usually there are already defined projects. This projects can be scaled on their fit. In this meeting also other tools from the four cycle method can be used. The outcome of this tool are the following:
•Reach and range in the current situation;
•Reach and range in the desired situation;
•List of projects to reach the desired situation.
Where
This is a tool that has impact on the strategy of the organization. It can best be carried out in an informal environment. In this way thinking will be more creative en be less bounded to borders that exists in the mind of the team.
Who
IS-managers can usually fill in the matrix for the current situation themselves. For the question where the organization wants to go it’s advisable to involve general management and other relevant stakeholders. This question has as mentioned before a high impact on the e-strategy of the organization.
Way 3. List of current and planned projects
By Peter Chiv
The outcome no. 3 in the first part of cycle 1 entitled “Evaluation of previous planning results“ provides a complete overview of all running and planned projects with risks, benefits and participants.
Why is it important to involve running and planned projects at all? The answer in short is that we can learn from previous, running and already planned projects to improve our planning. Risk analysis of actions or events of other (previous, running, planned) projects can indicate how to assess similar or the same ones in our new project. The same reason applies to the enumeration of benefits of other projects, too. With the knowledge about already occurred benefits we can make assumptions about the benefit-level of one action or event in our new project. Information about people involved in the different projects and fields, respectively, helps us to find the right - already known - participants and partners for our new project. To sum up, we can say that new projects can benefit from experiences of other projects. There is no need to re-invent the wheel entirely. This will hopefully save us from failures, decrease manpower and thus save much money.
Therefore such considerations are most useful in the beginning of a project, i.e. the planning or even pre-planning phase, when a project is most changeable. Such information about current and planned projects can be very precious information to influence the project planning and beware it from failures.
Since this outcome should be a result of the pre-planning or the planning phase, particularly the management is addressed. Hopefully previous, running and planned projects have been subject to a risk and benefit evaluation and these evaluations resulted in documents created with and by people involved; so that these documents can be used in a new project. Otherwise the risk management staff and the one in charge of assigning people to different tasks have to create this list of current and planned projects.
Let’s take a look at what this outcome can look like in practice. As mentioned above people of the risk management are qualified to realize such overview of all running and planned projects with their risks and benefits. There are many different methods how to do this and I am going to present one, maybe the most popular one.
Risks can be analysed and evaluated according to the likelihood they will be realised and the level of seriousness/impact they will have if they do occur. That is, risks are classified whether there is a low, medium or high likelihood they will occur, and according to whether their level of seriousness/impact will be low, medium or high if they happen. The result can be illustrated as a table (see below) or as a 2-dimensional diagram.
Risk | Likelihood | Seriousness/Impact | ||||
Low | Medium | High | Low | Medium | High | |
Event 1 | ● | ● | ||||
Event 2 | ● | ● | ||||
Event 3 | ● | ● | ||||
Table 1 - Risk table for project xyz
With the help of a risk table it is possible to assess the likelihood and seriousness/impact of the new project. The risk table serves as a indication and enables us to compare and weigh the risks of the new project.
The list of the benefits should include all benefits in a ranking. After identifying all benefits or even damage, the benefits are evaluated according to their level of benefit for the performing company. Beginning with the primary benefits the list enables the reader to have a better overview. All other levels give a more detailed benefit description.
Benefit level | Benefit |
Primary | Benefit description |
Benefit description | |
Secondary | Benefit description |
Benefit description |
Table 2 - List of evaluated benefits
The enumeration and evaluation of the benefits of other projects show us how to assess our benefits. They give us an overview which aims are possible and which are rather unrealistic. Thus it can give hints about the feasibility of the project.
The list of the participants involved in a project should include “internal” as well as “external” people, departments and organisations. Each participant entry in the list should refer to his/her task and reasons why the participant is/was involved in that project. Something like following could be the result.
Participant | Reason | Task |
Mr. John Smith | Project manager | Task description |
Organisation ABC | External consultant | Task description |
Table 3 - List of participants for project xyz
The benefit from such a list is obvious. Participants for the new project regarding their task can be easily found. Enumeration of external participants may give a hint who is best suitable for the new project with respect to good co-operation in the past. In other words, the list indicates which external partners have already gained knowledge about our company.
Conclusion
With the three lists and tables, respectively, it is easy to find previous or planned projects that might have similarities or even overlapping. Information about these projects can serve as a reference for the further planning of the new project. Moreover previous projects help to indicate the level of feasibility. Particularly the risk table and the list of evaluated benefits serve as a comparison scale.
Besides the benefits already mentioned above this outcome in general supports decision-making, identifies possibilities for performance improvements and helps to assess the efforts for the new project.
Purpose and evaluation
The aim of this article is to provide a tool for the use of critical planning objectives in the context of information strategy planning. This tool fits in with the “four cycles method” way of IS planning as described by Salmela and Spil [SALM02]. The “set of critical planning objectives” tool was originally designed by Wilco Menge in [SPIL05]. In this article the tool will be evaluated in terms of usability and validity and be revised to enhance its utility. The article will have the same structure as the original, answering the six basic questions of what, why, when, how, where and who.
The existing tool description gives an adequate definition of the set of critical planning objectives. It also provides some ideas on how to implement it – the how question. However, the usability could be enhanced by not focusing exclusively on objectives from the corporate strategy, but also on objectives derived from external sources.
To further improve the usability of the tool, this article will also clarify how it fits within the four cycles method and how it relates to some other tools that are used within this method.
Finally, the questions of where to use critical planning objectives and who should do this could be expanded and made more clear. This article will attempt to improve those points by using additional literature.
What is a set of critical planning objectives?
To answer this question, a short summary of the four cycles method mentioned before is in order. It is an IS planning method facilitating the implementation of an IS planning process. The four cycles are:
1.Agreeing on planning objectives and stakeholders
2.Alignment of business objectives and information objectives
3.Analyzing resources and technology infrastructure
4.Authorizing actions
Defining a set of critical planning objectives falls within the first cycle, agreeing on planning objectives and stakeholders. Within this cycle there are three planning tasks:
1.Evaluation of previous planning results
2.Setting the scope of planning and selecting objectives
3.Selecting participants and adjusting the planning approach.
The set of critical planning objectives tool is part of the second task. Salmela and Spil state the following:
“[The set of critical planning objectives] contains a set of information objectives that give direction to the content of the outcomes of this planning process. These can be drawn from branch information (benchmarking), from trends analysis and from corporate strategy.” [SALM02]
The tool thus contains a list of strategic objectives that are used in the planning process to formulate the actual outcomes that management wants to realize in the coming year.
Why are critical planning objectives necessary?
In order to give direction to the planning process, there needs to be some ‘point of departure’ on which further decisions in the process are based. A set of critical planning objectives can provide such a ‘point of departure.’ By formulating the most important objectives that have to be met by the planning process, managers can use these as a framework to formulate the outcomes they want to realise on the short term. By keeping the critical planning objectives in mind, a list of targeted outcomes can be compiled from the evaluation of previous planning results.
Therefore, defining the critical planning objectives is necessary to provide a link between the first and second planning task of the four cycle model. It enables management to make the most of the evaluation of previous planning results, since it gives direction to the rest of the planning process.
How should critical planning objectives be developed?
There are two ways to approach the development of critical planning objectives: from an internal point of view and from an external point of view. The internal point of view means drawing on objectives from the organizational strategy. Looking outside the organisation, i.e. the external point of view, managers can use benchmarking or trend analysis to formulate planning objectives. These two viewpoints will now be discussed further.
The internal viewpoint
Daft acknowledges two kinds of objectives, or goals, within companies: official objectives and operative objectives [DAFT01]. They both serve an important role. The official objectives can be either a mission statement or a formal definition of the scope and objectives the organisation is trying to achieve. These give the organisation legitimacy and a basis for existence. Operative objectives are derived from these official objectives. They are the more specific, measurable goals that the organisation wants to achieve on the short term.
Keeping the purpose of the tool in mind, it is clear that official objectives should be the first looked at when formulating a set of critical planning objectives. These are overarching, strategic objectives that should be built upon. However, this does not mean that the operative objectives should be entirely disregarded. Depending on the information needs and the direction the organisation wants to go in, some of these can be used as critical planning objectives to ‘point’ the planning process in a certain direction.
The external viewpoint
Looking outside the organisation can give managers a fresh insight in what they want to achieve. What are the competitors doing? How well is our organisation doing, relative to competitors and to our stated objectives? Benchmarking is a good method to analyse these questions and formulate critical objectives for areas that need to be improved. Ward and Peppard [WARD02] provide an importance-performance matrix which can be used to do this. It is reproduced below in figure 1.
Concentrate here? | Maintain performance? |
Not important? | Possible overkill? |
High
IMPORTANCE
Low
Low PERFORMANCE High
Figure 1 The importance-performance matrix
The most important sector of the matrix is the top-left one. Here is where the organisation should focus it efforts in developing new objectives. The bottom two sectors are interesting, because there is room to drop or change existing objectives there. As for the top-right sector, any objectives which fit in there are on the right track, and should not be changed.
When should critical planning objectives be developed?
The fit of the critical planning objectives tool within the four cycles method has been discussed before, it should take place during the second planning task of the first cycle generally.
However, it will not be necessary to adjust all critical planning objectives during each iteration of the cycle. The official objectives or mission statement represent a long term commitment for the organisation. Critical planning objectives derived from these thus need not, and indeed should not change drastically every cycle. Doing so would cause the organisation to lose its orientation. Operative goals on the other hand are more prone to change, and any planning objectives related to these should be carefully assessed every pass of the cycle. Some may have to change, or be dropped completely. There will be some overlap with the first planning task here, evaluation of the previous planning results. This isn’t particularly bad, since the first task will be more concerned with the content of the objectives – have they been met – while the second task shall focus on questions of whether they are still realistic or even needed. That way objectives can be reformulated, dropped, or new ones created.
Benchmarking can be time-consuming, as information on competitors’ activities is required. Therefore it may not be feasible to run a full benchmark analysis during each iteration. However, with the speed markets change and organisations have to react, it is advisable to at least keep an eye on important changes in the equilibrium. As with the official objectives though, critical planning objectives formulated through benchmarking shouldn’t change drastically every cycle. Sometimes a shift may necessitate adjustments, but it is better to stick to a certain course then to take two steps forward, three back, and end up not going anywhere in particular at all!
Where should critical planning objectives be developed?
The formulation of critical planning objectives requires sensitive information about the organisation and a firm understanding of its workings. Therefore, it should be done by managers within the organisation. Only if this consistently fails to lead to a satisfying planning process should the organisation consider bringing in an external consultant, but this is a costly and risky venture for the reasons mentioned above.
Who should develop critical planning objectives?
This depends on the approach the organisation takes to planning. Salmela and Spil point out that it is important to select well-qualified personnel from all levels of the organisation and involve them in the planning process [SALM02].
In order to achieve such involvement, it is possible to approach the planning through Management by objectives (MBO), as described by Daft [DAFT00]. This can be applied within the four cycles method.
In essence, MBO is a planning method where managers and employees set goals on various levels – departmental, personal, etc. and monitor these. It consists of four steps:
1.Set goals
2.Develop action plans
3.Review progress
4.Appraise overall performance
Steps 2 through 4 are also done within the four cycles method. Most important is thus to put the focus on the first step, setting goals. By doing this through the MBO method, agreement between employees and managers can be reach, which creates the strongest commitment to later achieving the formulated goals.
Way 5. List of targeted planning outcomes
Diederik Rothengatter
Introduction
In this document the 5th tool of the Salmela & Spil method will be described. This tool is located in the first quarter of the IS strategizing cycle. In this part of the method the emphasis lies on “agreeing on planning objectives and stakeholders.” The description of this tool is:
“List of targeted planning outcomes: Contains a list of the results that senior management wants to reach during the coming year. […] In the simple end, outcomes can consist of a list of running and planned projects. In the complex end, a complete set of strategic information systems planning outcomes can be selected.” [SALM03]
This is a very compact explanation of the objectives intended with this way. The exact outline of this tool is worked out in this report by using the analysis of ‘what, why, when, how, where and who’ (considered in different order).
When
Following the Salmela & Spil IS strateging cycle, this tool is located in the first quarter. This quarter is focused on agreeing on planning objectives and stakeholders, and this specific tool is positioned under the ‘setting planning scope and objectives’ part. This tool is used at the very start-up of every planning iteration, just after the evaluation of the previous planning cycle.
What
The objective of this tool is to decide on what contribution are to be made to the IS during the next planned period. By proceeding in accordance with effective SISP methodologies, corporations can establish the basis for IS that would assist management to improve and aid in the corporation in proposing, prioritizing proposed IS for short- and long-term development in direct association with the business plan. [KARA94] It is of most importance of align the SISP method to the business planning. As described by Grover and Segars, businesses can vary from written-formal systems to personal-informal systems. Furthermore depends the effectiveness of the IS Planning on the evolutionary stage of the business planning, the more mature a business planning is the more effective a strategic IS planning will be. [GROV05] Another aspect to consider is the size and the expertise existing in a corporation, for the smaller a company is, the fewer the financial resources and technical expertise are available and the poorer the management skills are. [JOUI04] This will have impact to what extend the demand on strategic IS planning can be.
Why
The information input form business plans and planning resources is found to significantly influence the quality of the planning process. The quality of the planning process in turn, significantly influences the contributions of IS to an organization’s performance. The role of IS in the organization is also found to significantly influence the planning practices in organizations. [PREM91] It is important to explicitly emphasize and state the desired outcomes of the planning process. Because IS planning can have multiple objectives and it can sever many different interests, it is important that the emphasis of different objectives is clearly stated. [SALM03] Successful SISP should help achieve alignment between IS and business strategies, analyze and understand the business and its associated technologies, foster cooperation and partnership among functional managers and user groups, anticipate relevant events and issues within the competitive environment, and adapt to unexpected organizational and environmental change. [GROV05]
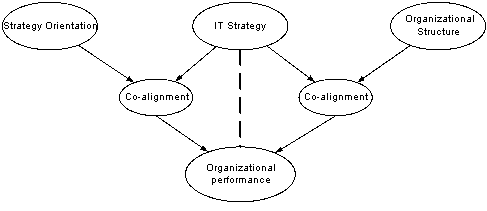
This figure shows that, if a firm wants to generate best performance levels, it should align its IT strategy with its strategy and organizational structure. In other words, firms can achieve best performance levels by aligning IT strategy with corporate strategy and structure [JOUI04]
How
While there have been studies that examine the ‘what’ question of SISP, particularly concerning the issue of IS-Business alignment, there has been little on the ‘how’ questions. [GROV05]
Grover and Segars argue that that the concepts of adaptation and learning are invariant across phenomena, and therefore that it is possible to observe stages of evolution is the SISP. The model above shows these stages. [GROV05] A company has to realize it position in this model and adjust its SISP according to it. The management and planning department can conclude that the more iterations of the Salmela & Spil cycle are conducted, the more effective SISP will be. The list of targeted planning outcomes must be adjust in accordance to the stage of organizational planning. In conducting the SISP process there are several problems to encounter. One of those problems is the duration of SISP. Considering the fast evolution of IT, the duration is too long. In planning the next iteration of the cycle the list of targeted planning outcomes should be adjusted to a short cycle. Furthermore, the fact business process reengineering is being accomplished separately from SISP causes substantial problems since IS is an enable of business process reengineering for improving efficiency and effectiveness in business processes. [SMIN99] Business process reengineering may change the functional structure of the corporation and may require IS to incorporate certain features. If SISP is achieved without considering such changes and needed features, the IS is likely to become incapable of supporting altered processes.
Min et al. [SMIN99] developed a framework to model the IT opportunities. Using Key Performance Indicators (KPI) to measure the current IS/IT in the company and looking at Critical Success Factors (CFS), a analysis can be made on opportunities can be used in the list of targeted planning outcomes. The next figure shows this model.
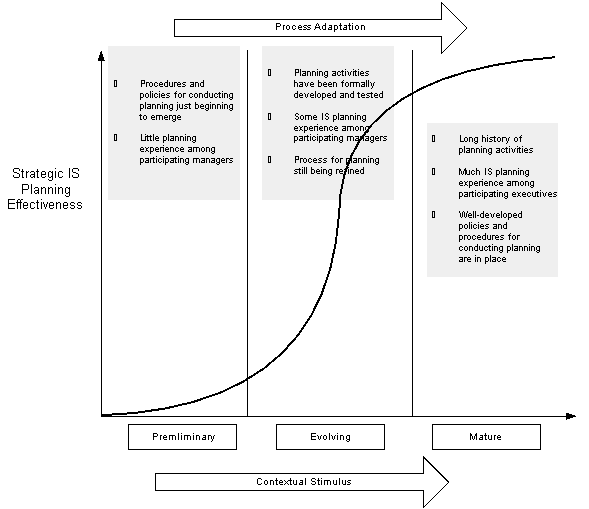
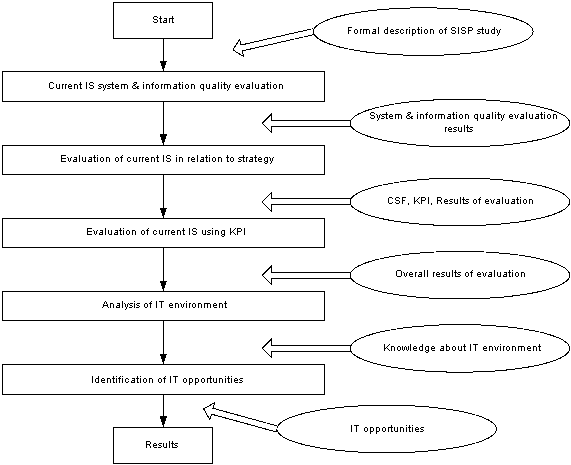
Where / Who
An SISP process should not be initiated unless a top executive sponsor and some executives are committed to being involved in it. Furthermore, for each application, the business manager responsible should be identified. [WARD02] This can be done during the composition of the list of targeted planning outcomes.
Introduction
This document is part of the four cycle method presented by Salmela and Spil [SAL02]. It is the 6th tool out of 45 and part of the 2nd task (Setting the Scope of planning and selecting objectives) in the 1st cycle (Agreeing on planning, objectives and stakeholders).
In the vast amount of IT and business literature the scope of a project is mostly very ill defined. Literature about, for example, the Rational Unified Process confirms this – the author simply states that the scope is something that needs to be done “so that you can derive acceptance criteria for the end product.” [KRU00]. Most authors describe the scope as an informal process which has to be done, but they do not describe how this scope should be constructed nor managed during the project life cycle after its construction.
The definition of scope varies wildly among books and articles, but in general one can speak of 3 definitions; the project scope, the product scope and the scope of work [HEE02, ZHU04]. This paper will focus on the project scope since this provides a view of a project’s mission, goals and objectives – the planned results and constraints of the IS planning process. Project Scope Management involves methods to ensure that the project includes all work required, and only the work required, it’s main focus is defining and controlling what is included in the project [PMI00].
A project scope is a tricky thing, usually underestimated by developers and management, informally specified and left alone and forgotten after it has been defined [KRU00]. A fairy large (92 organisations) survey showed that an unclear scope definition is a big factor in project failures; it can lead to confusion, misinterpretation and delay [YEO02, TUR88]. Scope changes continuously during different project phases as more details become clearer, these changes should, and can, be managed [TUR05, KER01]. The Project Scope Management (PSM) approach deals not only with the scope definition, but also with continuous scope change control throughout the project [PMI00].
In the following chapter the Scope of the PSM is explained; the constraints and level of detail that should be used in the PSM approach. After this the Project Scope Management Process will be briefly described in such a way that it is applicable to the IS planning process. The 5 elements of this process will be discussed and related to the IS planning process. Next to the “normal” scope identification, extra attention will be given to Scope Change Management – a continuous process during the entire project and a method to avoid risks [KER01, PMI00]. Project risk analysis documents should pay attention to project scope definition, scope agreement and scope change management since, as previously stated, it is critical to ensure the project remains “on the right track” [KER01].
Scope of the PSM Process
This chapter focuses on the time scope, abstraction level, focus and stakeholders of the PSM process. The scope management process, as described in detail in the next chapter, is a fairy large undertaking and contains a continuous change control element. Time spent on the scope management process is relative to, but not limited to, the size, abstraction, complexity and stakeholders of the project. It is therefore vital to specify these before the scope management process is started. Described below are the definition of the abstraction level, the focus and the stakeholders.
A problem in scope management in every form is defining the abstraction level – the amount of detail that the document should contain for it to be useful while staying ‘high enough’ to keep an overview of the project. It is best to look to the IS project on a business level and not look “inside” the various IT systems it will contain. Descriptions of proposed system functionality should be in the scope documents – how the systems implement this functionality should be described in product scope documents, which are not included in the project scope documents [HEE02].
The second constraint of the PSM process are the focus areas included in the scope documents – the IS system will reside within an organisation and is thusly influenced by different external and internal factors which should be taken into consideration. First the focus should be on the IS project at hand. Based on the IS project some of the following external and internal factors can be taken under consideration if their influence may have effect on the outcome of the IS project: technological, political, economic, social, pressure groups and stakeholders [WAR02]. If one of these groups has direct and noticeable influence on the outcome of the IS project it is important not to ignore this – it could result in serious problems, ranging from employees who are not willing to use the system to government regulations which prevent the use of the system, at the end of the IS project implementation.
Last but not least are the stakeholders. The scope document has to be sponsored, created, managed and executed [PMI00, DAF00] – end users are mentioned before (PSM focus, above) and will not be discussed here. In the first element of the PSM a scope manager is selected. This person leads the scope creation and is responsible for the scope management and execution after the scope documents have been created. A sponsor needs to be available which has enough power within the organisation to make decisions regarding the IS project and remove organisational barriers [DAF00].
Time spent on the scope management process is relative to, but not limited to, the size, abstraction, complexity and stakeholders of the project. Time is money and should therefore be managed correctly. The amount of effort placed in each of the objects that influence the time spent on scope management should be relative to the project size – the more complex the problem or impact the project has on the organisation, the more time should be spent on scope management and scope change management to increase the change on successful project completion.
Project Scope Management Process
As introduced before, the project scope management methodology is part of the Guide to the Project Management Body of Knowledge (PMBOK). This guide is a reference and the de factor standard for project managers around the world [PMI00]. Many books and articles use or (indirectly) reference to this guide, since it is constructed based on many years of best practices. Several other ‘methods’ have been reviewed – however these offer only a subset of solutions, which always can be linked to an element in the Project Scope Management (PCM) theory (including but not limited to [HEE02, KER01, HEL03]) or have a completely other definition of scope unusable in tool 6 (this) of the four cycle model.
The works in this chapter are mainly derived from the PMBOK and adapted to the context of IS planning [PMI00]. References to other sources are given where needed. This document assumes that the previous tools/tasks defined in the four cycle method presented by Salmela and Spil, have been completed [SAL02]. This means that the critical planning objectives and the targeted planning outcomes are already known. Also there has been an evaluation of previous planning results which can be used as guidance in defining the IS planning scope.
This chapter will discuss the 5 elements in the PSM theory, namely; Scope Initiation, Scope Planning, Scope Definition, Scope Verification and Scope Change Control. Each of these elements has an input, output, and a tools and techniques explanation. Together these elements form the PSM as depicted in figure 1.
Figure 1 describes a methodically ideal process scope management process where each of the scope management elements follow each other chronologically. The scope change control is modelled as a “loop” – it should be a continuous process during the entire IS project. Changes in the projects internal and external environment could change the scope of the project and should therefore be monitored closely. In reality this model is used less chronological and links to various other planning processes within the IS planning process, some of the elements might overlap and interact in different ways then stated below. This paper however, focuses on a somewhat higher level view on scope management which can be applied to different IS planning incentives. This way the reasoning behind the different elements becomes clearer and more applicable to a more broad scope of IS planning projects; every project is different.
In the following paragraphs the 5 elements will be discussed. First the element will be introduced, then the element’s inputs will be reviewed, then the tools used and finally the outputs.
Scope Initiation
The scope initiation process links the project to the organisation. In the Salmela and Spil [SAL02] model this process will be used to 1) formalize the earlier prepared planning objectives and outcomes, 2) link the project to a project manager and 3) create constraints and ‘assumptions’
This process requires multiple inputs:
•The planning objectives and outcomes.
•Project selection criteria, the planning objectives and outcomes should be matched against a rule set of management concerns (financial, market share, etc)
•The organisational strategic plan. The IS project should be aligned with the organisational goals.
•Historical information, this information is ‘gathered’ in the first cycle of the four cycle model.
Based on these inputs the objectives and outcomes can be evaluated based on the strategic plan, the rule set and the historical information. Expert judgement could be used in combination with project selection methods which measure the value or attractiveness to the project owner. Finally a project manager should be chosen who is able to contribute the most to the project. This project manager is usually defined as a “Champion” [DAF00]. Also a “Sponsor” needs to be found, a person that has enough authority to make decisions regarding the project and who is able to remove organisational barriers [DAF00].
This element leads to 4 outputs:
•The Project Charter, a document that authorises the objectives and outcomes
•Project Manager, described above
•Constraints, a preliminary global set of rules which the project has to follow. These usually involve financial constraints for the whole project.
•Assumptions. A set of preconditions which have to be met before and during the project for the project to be sustainable and reach the intended goals of the project.
Scope Planning
This is the process that is usually defined as “creating the scope”. It involves various analyses for the purpose of documenting the work that is required to produce the Information System. It requires the inputs from the previous ‘phase’ (3.1).
These inputs (objectives and outcomes, the project charter, constraints and assumptions) are then analysed using:
•product analysis, to create a better insight of the planned Information System
•benefit/cost analysis
•alternate identification, to search for different approaches to attain the goals of the IS
•expert judgement
These analysis result in a scope statement. This statement is the foundation for the IS project and can be used to communicate with stakeholders and everyone involved to create a common understanding of the goals of the project. This document describes the justification of the project, a description of the product (the objectives and outcomes), the deliverables and the objectives that the project should obtain.
Besides this important document there are 2 more important outputs from this process, namely a document which contains the assumptions and constraints (supporting detail document) and a document describing how the scope and scope changes should be managed.
Scope Definition
This phase breaks down the scope statement into smaller more manageable objects. These smaller objects are easier to understand and manage – they are (more) measurable, controllable and easier to schedule. To be able to break the statement down into smaller objects, we need the following input documents:
•The scope statement
•Assumptions
•Constraints
•Historical information, to avoid previously made errors made when implementing the smaller objects
The statement can be broken down using different techniques which are not included here due to the document size limit, [PMI01] is a good example of a fairly large (85 page) explanation about the work breakdown structure approach. Though it can be made theoretical and complex, it comes down to decomposition. An IS project is broken down into major objects, usually departments, business units, which are then broken down again into smaller objects until the scope is small enough to ‘grasp’ and manage within the greater context.
This process results in 1 or more documents containing the small objects with their scope, constraints and assumptions and, if applicable, an updated scope statement with findings that were made within this process.
Scope Verification
This process is small compared to the previous one; it consist of getting formal acceptance from the involved stakeholders and verifying that all the documents made before are correct and complete. These documents should be thoroughly inspected after which formal acceptance can be granted.
Scope Change Control
One of the most overlooked aspects of Scope management is Scope Change Control or Scope Change Management. This involves the a) continuous monitoring of scope changes, b) managing change if it occurs and c) making sure that the scope changes that occur are agreed upon
As described before, one of the bigger risks in the executing an IS project is scope deviation. Scope changes, planned or agreed upon, have to be managed carefully so that actions can be taken in time to adjust the scope or get the project back on track. While this aspect is a big part of risk management, which is discussed in the last cycle of the Salmela and Spil model, it is worth mentioning it here.
During the monitoring process, one should look at:
•The current scope documents; the scope statement and the decomposed scope statement, to see if and where the current process is deviating.
•Performance reports; to see if the IS planning process is being preformed on time and within constraints, under the assumptions made.
•Change requests; based on various external and internal occurrences, there might arise a need for change within the scope. These requests must be carefully managed with regard to the current scope and processes within the IS planning process.
The main activity within this process is the scope change control; changing the scope based on change request and environmental change. These changes might occur based on, including but not limited to, new details, outside information or performance measurements.
A “side” process to this change control is additional planning. Plans should be made to accommodate expected and unexpected changes to the project scope. These plans can be utilised when these changes occur and should be designed to limit the impact of the change.
Conclusion
Above we described a theoretical approach to form a complete set of scope documents and manage them correctly. We described constraints of the scope management process (time, size, abstraction, complexity and stakeholders) which should be defined before the scope documents are created.
After these constraints have been set one can start the project scope management process and follow the 5 elements (Scope Initiation, Scope Planning, Scope Definition, Scope Verification and Scope Change Control) to create a set of scope documents. The last element in this (Scope Change Control) process provides a way to continuously manage and adapt the scope based on external and internal changes to keep the project “on track”.
Following the above one can create a scope management process to facilitate an IS project and give the project a much bigger chance on successful completion.
Definition
The method described in this document is part of the first cycle of the four cycles method for IS strategy. The main goal of this first cycle is to agree on planning objectives and stakeholders. This first cycle can be divided into three main tasks:
•Evaluation of planning results;
•Setting the scope of planning and selecting objectives;
•Selecting participants and adjusting the planning approach.
The method I will describe can be used to accomplish the third task. First, I will give a brief description of what this method exactly is and how it can be used. The method can be described as a matrix with objectives, participants and phases which assigns responsibility for achieving planning objectives to key managers. It also schedules the planning process and assigns people to each planning task. This is a very broad definition. Therefore I will give a more detailed description now by explaining the functions of the matrix.
Functions
The first function of the method description is assigning responsibility for achieving planning objectives to key managers. This is important, because there must be a person (in this case a key manager) which is responsible for a certain objective. The top management can communicate with this person about the progress of the particular objective. This person is also responsible for failure or success. This will have a positive effect on the progress of the objective, because the responsible person will do his best to achieve the objective. If there is no responsible person, it is more likely that the objective will not be achieved.
The second function of this method is to schedule the planning process and assign people to each planning task. In other words: when should a task be done, what should be done, and by whom. This is important to give some basic structure to the planning process. If it is not clear who should do a task of the planning process, it is more likely that this task will not be done good enough. The assigning of people to tasks can be used as guidance for the planning process. During the planning process, this guidance can be adjusted, but it gives a good overview of all the tasks and people assigned to these. The matrix should not be to much detailed, then it could become unreadable. The matrix should give a broad overview of the tasks of the planning process. During the process, broad tasks can described more detailed in other documents. The matrix is just a basic start document.
Because this method is part of the first cycle, it is clear that this method should be used in an early phase of the planning process. It is obvious that you first assign people to different tasks before executing these tasks. Also giving responsibility for objectives to people should be done before actually beginning with the planning process.
Constructing the matrix
The information will be presented in a matrix; this can be done in various ways. A good way to construct the matrix is to place the participants on the horizontal axis and the phases, tasks and objectives on the vertical axis. On the left side of the matrix, there is now a clear overview of the different phases, tasks and objectives. It is wise to set the phases and tasks in chronological order here. On the horizontal axis, the participants are placed. In the example (see figure 2) there are placed some stakeholders groups (top management, IS management, middle management, end users) and some persons who are responsible for several objectives. Additionally it is possible to set some deadlines for each phase, or even for each task. However, the matrix should not become unreadable, so it is preferable that not every small task is represented in the matrix with a deadline. It is more practical to give some major tasks or complete phases a deadline.
The assigning of tasks and responsibilities to several stakeholders and persons can be considered as an important part of the planning process. Therefore, it is preferable that each stakeholder can give his or her opinion about the construction of the matrix. For example, this can be done by organizing a brainstorm session where one or two people represent each stakeholder group. Also the persons that can be pointed as responsible person for an objective should take in this brainstorm session. During this session, the construction of the matrix should be discussed extensively. By following this procedure, the matrix will satisfy as much as possible all the stakeholders.
Participants Phases, tasks objectives | Top management | IS management | Middle management | End users | Person A | Person B | Person C | Person D |
Phase 1 | x | x | x | |||||
Objective 1 responsibility | x | |||||||
Objective 2 responsibility | x | |||||||
Task 1 | x | x | ||||||
Task 2 | x | x | ||||||
Task 3 | x | x | x | |||||
Phase 2 | x | x | ||||||
Objective 1 responsibility | x | |||||||
Objective 2 responsibility | x | |||||||
Task 1 | x | |||||||
Task 2 | x | x | ||||||
Task 3 | x | |||||||
Phase 3 | x | x | x | |||||
Objective 1 responsibility | x | |||||||
Objective 2 responsibility | x | |||||||
Task 1 | x | x | x | |||||
Task 2 | x | x | ||||||
Task 3 | x | |||||||
Agreeing on planning objectives and stakeholders
A new method for formulating a Information Strategy planning is designed. The method is designed on the base of several action studies on IS planning in the public as well as in private sector in Finland and the Netherlands. This model is novel, because it combines the incremental and the comprehensive approach to IS strategy. The method consists of four cycles dividing a period into four different planning cycles:
1.agreeing on planning objectives;
2.aligning business objectives and information objectives;
3.analysing IS resources and IT infrastructure;
4.authorising actions.
Each period the four cycles can be repeated, so the strategy is continuously changing and adapting to the new needs. Every cycle has different planning tasks for reaching its objective.
One of the planning tasks of the first cycle is to select participations and adjust the planning approach. To reach this objective, different activities (tools) are described. One tool is defining an educational plan. In this report this tool is worked out in more detail by using the analysis of ‘what, why, when, how, where and who’ (in a different order).
What
The objective of an educational plan is to develop a plan that defines an overview of knowledge and experience that is needed and available in the planning process. Two kinds of knowledge are in this case defined: scientific knowledge and knowledge of information. Scientific knowledge is the understanding gained through experience or study. Knowledge of information is the specific information about something.
First, the knowledge and experience needed for the planning process has to be defined. Specific knowledge and experience about handling the different stages of the four cycle method is needed. For example, how to evaluate, how to define criteria etcetera. These are examples of scientific knowledge.
Beside this, information about the strategic position of the organization is needed. It is very likely that the participants need to have information about the competitive forces of Porter and the PEST. This means knowledge of the new entrants, buyers, substitutes and suppliers. PEST analysis consists of analysing the political, economic, social and technological environment of the organization. This is an example of knowledge of information.
Brainstorming about the knowledge and experiences that participants need to have:
Level of IS management:
§being able to analyse the environment, knowing the strategic position of the organization and be aware of partners and competitors;
§having knowledge of trends in the sector;
§knowing where most benefits in strategy can be gained;
§knowing the strategic position of the organization: environment, strategic capabilities and opportunities.
Level of Functional Management:
§knowing the innovative capacity of the organization;
§implementing strategy in the organization;
§understanding the pitfalls of strategic planning;
§knowing where most benefits in strategy can be gained;
§knowing the strategic position of the organization: environment, strategic capabilities and opportunities.
These are only some examples. This list has to be structured by an educationalist and an expert in IS strategy planning for its specific situation.
After the needed knowledge and experiences is defined, an inventory has to be made up from the present knowledge of the participants. This can be done by letting the participants analyse themselves by answering questionnaires. Though, the functional management has to be able to judge whether or what kind of knowledge and experience is present at the participants.
Why
When the needed knowledge and experience is defined as well as the available knowledge is known. A gap between those two is probably notice. This gap can be declined by making use of a training program.
Deficiency![]()
![]()
![]()
![]()
Training program
Figure 1 - Gap of knowledge
All required knowledge and experience has to be present in the organization (by the participants) to be able to have a successful information system strategy. However, as is quoted in the lectures, Wang and Tai said that ‘most intended strategies are not realized due to application difficulties and environmental changes that are not under the control of the organization’. This is a good example of not being able to have everything under control. Therefore, it is good to point that the gap mentioned in figure 3 will never be dissolved totally.
When
As said before the educational plan is designed in the first planning cycle, within the activity of selecting participants and adjusting the planning approach. Before the educational plan can be designed, the objectives, the participants and the different phases need to be set. This should be done in the activity prior to the educational plan.
It is important to have the educational plan designed in the first stages of the planning cycle, because in this stage there is the possibility to gain knowledge to the organization that can be used in the planning process. In this stage it is also still possible to gain experts from outside when the participants do not have enough qualifications (knowledge and experience).
How
Knowledge and Experience or Competencies
The difference between knowledge and experience on one hand and competencies on the other is that competencies are more comprehensive, they e.g. describe personal attributes as well. Thiadens defines it as follow: “…the professional skill and/or the personal skill an employee has and that is needed for performing a task at a proper level. Competencies consist of four parts, being capacities, character traits, knowledge and the styles of behaviour...” [THIA04]. In this article I will refer to competencies instead of knowledge and experience because competencies have a broader reach to measure.
Framework
The proposed framework illustrated in Figure 2, could be used to develop an educational plan as described in the four cycle method [SALM02].
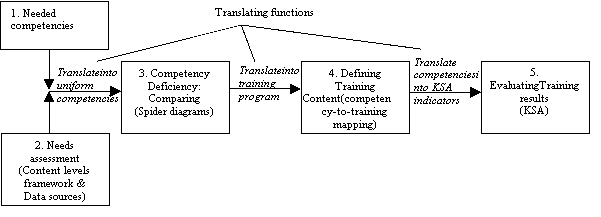
Figure 2: Proposed framework for developing an educational plan.
It suggests that the output of a needs assessment (2) is confronted with the needed competencies(1) and will result in a competency deficiency(3). This deficiency in
turn, should evolve into a proper training program(4). The final step is to evaluate the training results (5) to judge if the trainees gained the right competencies during the program.
Needs assessments: content levels framework & Data sources
Needs assessments is a systematic exploration of the way things are and the way they should be [ROUD95]. We could do a needs assessment on how an individual should perform in an organization or how this individual should perform in relation to a certain task. From another viewpoint we could do a needs assessment in a specific business unit in relation to their corporate task. Of how about a needs assessment about if organizational goals or objectives are met? These examples stress that there are different views from where one could start a needs assessment.
Ostroff and Ford (1989) designed a content levels framework in a 3x3 matrix with nine cells from where a needs assessment could start. Figure 3 shows how this is done in a dual perspective way which focuses on content (person, task, organizational) and their appropriate levels (individual, subunit and organizational).
Level | Content | ||
Person | Task | Organizational | |
Individual | Cell 1.1 What knowledge and skills do specific individuals need to learn for effective performance? | Cell 1.2 What are the knowledge and skill requirements necessary for the accomplishment of specific tasks by an individual? | Cell 1.3 How do the goals of an individual affect or constrain performance, motivation to learn, or training effectiveness? |
Subunit | Cell 2.1 What skill mix is needed for successful job performance within a given work group, e.g., interpersonal skills, teamwork skills? | Cell 2.2 What activities, technologies, and behaviors should be trained for effective task performance within a given subunit? | Cell 2.3 How do work group goals and culture affect or constrain performance or training effectiveness? |
organizational | Cell 3.1 How does the organization tie human resource planning (i.e., HR analysis, skills inventories, forecasting of work force demand and supply, and forecasting of skill mix) to strategic planning? | Cell 3.2 What are the core work processes and technologies of the organization? | Cell 3.3 How do organizational goals, objectives, and resources affect whether and where training is needed? |
Figure 3: Ostroff & Ford - The content levels framework for training needs assessment
Each cell (i.e. the intersection of each content factor with each level), will provide a clear direction from where to approach a needs assessment. It suggest questions or issues that functional management should address, and build forth upon, when doing a needs assessment on a particular content base with the associated level.
Measuring present competencies
When examining organizational deficiencies, it is important to get a complete picture from many sources each in respect to their level and content. Of course, the desire for quality information needs to be balanced against the constraints of time and resources.
We give some example data sources (Figure 4), adopted from the research of R. Ryan Nelson et al [NELS95], which could be used to measure the present competencies with respect their specific content level. A data source gives some more direction by means of specific techniques or tools that could be used when doing a measurement in this content level. At the personal content level (cell 1.1 through 1.3) we could do e.g. interviews or use observation techniques to measure competencies. At the organizational content level (cell 3.1 through 3.3) we look e.g. in what detail the organization knows it’s personal inventory, and if the organization has a proper overview of the missed deadlines.
Content | Data Source |
Personal | 1. Observation 4. Tests a. Job knowledge b. Skills c. Achievements 5. Attitude surveys 6. Devised situations (Role play, Case studies) |
Task | 1. Job specification or task analysis 3. Review literature concerning job |
Organizational | 1. Organizational goals and objectives 3. Skills inventory 4. Analysis of efficiency indices a. Costs of labor b. Missed deadlines c. Downtime |
Figure 4: Some questionnaire examples each on a different content level
In Summary, the Ostroff & Ford matrix should be used to give the direction of a needs assessment, while the data sources are techniques and tools used within a chosen direction. In planning the assessment, it is important to identify which of these data sources are available and what are their importance of using them.
Competency Deficiency: Comparing
Until now we had described two tools for supporting the needs assessments of present competencies. According to our proposed framework (Figure1) the needs assessment should be confronted with the needed competencies and emerge into a proper training program. One important aspect to point out here is that the output of the needs assessments must be feasible enough for comparison against the needed competencies. Take for example the needed competencies for an IS/IT manager described by Feeny and Willcock [WARD01] in Figure4 (left). From the output of the needs assessment one should determine in what degree the assessment results, which are pronounced in terms of competency, are part of these competencies. This process is subject of the “translate into uniform competencies” function, showed in Figure 2. From this translation an estimation could be made to pronounce the results of the needs assessments in terms of competency. This estimation compared against the needed competencies could then be displayed in a spider diagram which shows the gaps. Figure 5 (left) shows the output of a needs assessments on an organizational level and content basis (area 3.3 in the Ostroff & Ford framework) . Figure 5 (right) shows the difference after the comparison on an individual level and task content basis (area 1.2)
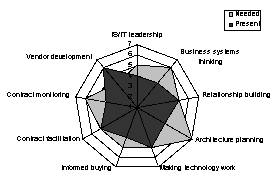
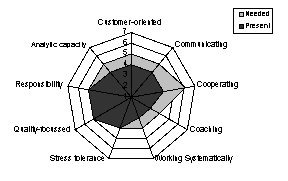
Figure 5: Spider diagram: Gaps in needed and present competencies (Left: IS/IT manager gaps at organizational level; Right IS/IT manager gaps at personal level in relation to a certain task
The lighter gray surface should, when there is no gap, been totally covered by the darker gray surface. In this way functional management has a proper overview of their current and present competencies.
Defining training content: competency-to-training mapping
While it is the task of the senior management to provide the training programs, a mapping to a right training program could still be difficult. Like the translation into uniform competencies, its also a manner of time and experience to see which training program gives the right competencies to the trainees. Deficiencies in competencies (gained from the spider diagrams) should directly be translated into a proper training program for a certain function (e.g. IS/IT manager). Figure 6 shows an example of a competency-to-training mapping for the role of IS/IT mangers. If we take the deficiencies of Figure 5 (left), this trainee should have training programs A,B and D which cover all the deficiencies.
IS/IT Leadership | Business systems thinking | Relationship building | Architecture planning | Making the chronology work | Informed buying | Contact facilitation | Contract monitoring | Vendor development | |
Training A |
|
| |||||||
Training B |
|
|
| ||||||
Training C |
|
|
| ||||||
Training D |
|
|
| ||||||
Training E |
|
| |||||||
Training F |
|
|
Figure 6: A possible map of training programs, where one attains different competencies in each training
Evaluating Training results: KSA
Competencies reflect a combination of knowledge, skill and ability (KSA) elements. Individual KSA elements are sometimes referred to as indicators. Because competency can only really be evaluated in practice, we rely on “indicators” to let us know if trainees have acquired the KSAs that support development of the competency. If a trainee has not demonstrated the ability to perform the indicator, it is unlikely that they will be able to perform the competency in practice. While we also could use the needs assessments (framework and data sources) again to measure, every organization however is in someway bounded to certain time constraints. Although KSA indicators are less precise, they provide a faster mechanism to see if the training has had the proper effect. A similar table of that from Figure 6 could be used to map attained competencies against KSA indicators which i.e. which indicators are sufficient to see that a competency is gained. This mapping is the last translation that should be made and has to be done by the translation function: “Translate competencies into KSA indicators” as showed in
Figure 1.
Conclusions
Most applications and investigations of needs assessment, focused on end-user training, emphasize only the person component while ignoring the critical roles of the organizational and task components. With the model of Ostroff & Ford we have shown that these dimensions are important as well, and should be used to give needs assessments more structure, and therefore senior management more direction.
The toughest parts of the proposed framework are the translating functions as shown in Figure 2. These translating functions become more efficient and effective while the organization is experiencing with the educational plan over time.
Where
The educational plan can be designed within the organization, but it is also possible to outsource the design of this plan. The same applies for the training program. When the knowledge of designing these plans is not present within the organization or when the designing of these plans cost too much time, it is better to outsource this activity. However, the cost of outsourcing has to be taken in account.
The execution of these plans will take place within the organization at the level of IS & BS operational users and the level of IS Management.
Who
The Functional management has the responsibility that the educational plan is formulated. However, the plan can be designed by an educationalist in collaboration with an IS strategy expert. The educational plan and the training program will concern all participants in the IS strategic planning cycle.
Introduction
As part of the course E-Strategizing at the University of Twente, a paper on one of the tools of the Four Cycles Method has to be written. This document describes the ninth tool from this ICT planning and management technique. The ninth tool is part of the first cycle of the Four Cycles Method as described by H. Salmela and T.A.M. Spil in their paper [SALM02]. The goal of this document is to answer several basic questions concerning this tool by means of the following basic questions: what, why, when, where, who and how. The rest of this document is structured according to these questions.
Tool description
The original document by Salmela and Spil contains a rather minimal description of the tool.
An informal network of people to be involved: Defines roles for each participant (decide, inform, ask or train). By performing a network analysis, groups of people can be identified that like to work together.
This chapter will try to outline the tool in more detail by answering the questions mentioned in the introduction.
What
As can be derived from the description of the ninth tool (from now on simply referred to as the tool) it is about identifying the role for each participant of an e-strategy. The roles that should be assigned are: decide, inform, ask and train. Since the paper by Salmela and Spill does not provide a context for these roles, the table below contains an intuitive overview about what each of them means.
decide : | Participant decides about specific Information Technology (IT) related issues. |
inform : | Participant needs to be informed about specific IT related issues. |
ask : | Participant can be asked to explain (can train) specific IT related issues. |
Train : | Participant needs training for specific IT related issues. |
Table 4 - Meaning of each of the definable roles
If the roles are to be interpreted as formulated in table 4 this can be useful during the implementation of an e-strategy. The next paragraph will outline in more detail why this is so.
Based on van Bommel's description of the roles and my feedback in the previous sections, I propose the following definitions of the roles. Again I would like to stress that without a more detailed description from the original authors, this can only be an interpretation, which doesn't necessarily cover the intended definitions.
decide make decisions
inform inform the rest of the participants (and the rest of the organization) of decisions and
their implications
ask play the role of critic (keep an open mind, challenge leaders' opinions and prevent
group-think)
train Participant (with expert knowledge) on some subject should train others who lack that
knowledge but need it in order to fulfill their role
The role of “ask” needs a little more explanation since it's not trivial and not already (partly)
described by van Bommel.
All participants form a group that is (usually) isolated from the rest of the organization, which can
bring up some negative side effects.
First of all, Group Think [JANI72] might occur. Group Think happens in groups that have high
cohesion, are isolated and lack procedures to systematically solve problems (besides other factors,
which aren't relevant in this case). The effects of Group Think are extensive and can lead to a lot oflarge problems. Secondly, Muntslag and Katsma [MUKA05] state that project groups (made up of managers as well as technical staff) often face difficulties. While the context of their research is that of groups implementing Enterprise Systems, the conclusions can be transferred to groups developing an estrategy. The bottom line is that non-management staff should behave differently in these groups than in their regular organization function. For example, they should dare criticize managers' ideas in the e-strategy group, which they usually don't do because it doesn't fit their habit from their regular function in the line organization.
We can conclude that it is prudent to have one or more group members play the role of critic, who
don't shy back from criticizing managers' ideas, and who play the role of devil's advocate. This is
the role called “ask”. Ideally, this role should be assigned to someone who has experience with
working in groups and maybe some minor background in psychology.
Selecting participants
Van Bommel correctly points out how to select participants for the e-strategy group, but based on
his description, only people from within the organization can be selected. Ward and Peppard [WARD02] explain why considering the external value chain for strategic information systems planning is important. It intuitively follows participants for the e-strategy development group should also be selected from outside the organization (e.g. business partners, suppliers, customers and other members of the external value chain). It might also be useful to select IT consultants, business consultants or enterprise system vendors.
Assigning roles
Contrary to what van Bommels description implies, I think participants can fulfill more than one
role at the same time. Some roles even go well together whereas others don't.
For example, the roles “decide” and “inform” can be easily combined, making the “inform” role
more effective since the person that makes decisions also informs others about them and can always explain the rationale behind that decision.
On the contrary, it should be obvious that the roles “decide” and “ask” are likely to interfere with
each other.
Why
The paper written by Salmela and Spill does not provide us with a clear answer to why the definition of roles is important. Therefore, we take a look at a paper written by Boynton and Zmud [BOYN87]. Boynton and Zmud outline in their paper a corporate function, which is characterized by efforts to integrate core business functions with information technology. This corporate function is called the IS function of an organization [BOYN87, page 60]. This paper also indicates there is an increase in dispersion of activities to subunits throughout organizations. As IT resources are perceived by subunit managers as becoming less expensive and less difficult to use, subunits are likely to bypass the IS function [BOYN87, page 61]. The dispersion of activities among subunits means that knowledge and resources are spread across these subunits. Since the business professionals who are working in these subunits are increasingly able to apply IT resources and provide the necessary technical support [BOYN87, page 61] it is interesting to keep track of each role a professional could perform during an e-strategy. If this kind of information is available to the entire organization, every subunit can benefit from a participants role.
When
To ensure optimal use of the tool it is best used at an early stage of a project. Since it is useless to know, whom can help with specific issues after an e-strategy has been implemented it is best to determine each of the participants’ roles during the initial phases of an e-strategy. The first cycle of the Four Cycle Method therefore seems like a logical place for such activity to take place.
Since each of the four cycles of the Four Cycles Method is repeated several times, it is possible to maintain an up-to-date indexation of each of the participants’ roles.
Where
To ensure maximum results from the effort invested into determining and assigning roles, it is best to keep track of each participant’s role in a central place. For this the centralized IS function can be used. Boyton and Zmud point out that there is need for a balanced approach to IT management, where IT management stays responsible for certain activities yet relinquishes control over other activities [BOYN87, page 61]. Maintaining an overview of each participant including the defined role for this participant could be one of the responsibilities for IS management.
Who
Since a role has to be defined for each participant of the e-strategy it is best to let subunit managers (or perhaps project leaders from a subunit) determine the role for each of the participants from their own subunit. Assigning roles can be done according to the results of other tools (for instance results from tool numbers 7, 8 and 11). With help of these tools, subunit managers should be able to define roles for each of their professionals. In cases where it is unclear which role a participant could fulfil the subunit manager and the participant should discuss which role would best fit the participant.
How
The most important question of all is how one could assign a role to each of the participants. For this it should firstly be decided how to deduce for every participant the role that best fits him or her. This obviously depends on numerous factors and as was pointed out in the previous paragraph can best be established by the person’s manager.
Determining what each of the participants capabilities are can be done by looking at the previous work that has been performed. For each given field of expertise, the specialist could be assigned the role of ”ask”. People that lack specific expertise could be assigned the role of “train”. Both these groups can help each other. Most likely group and project leaders as well as managers will be assigned to the role of “inform” or “decide”. Although this does not seem obvious, it is not unthinkable that a regular participant could be assigned to one of these two roles as well.
Traditional planning and management literature found on the Internet (see [BECT] & [MEMP]) often assumes agreements are reached between stakeholders and participants. These agreements are then used to define roles for the participants. These are not the kind of roles needed for the Four Cycles Method. No agreements are drawn up in the first cycle and therefore this method is not preferred to assign roles.
As pointed out in the previous paragraph the most obvious person to assign roles are project leaders as well as managers. It is best if the overview created by the manager is kept simple. Following information should at least be recorded for each participant: name, location, expertise (or subject of matter) and role.
Tool 10 – Communication plan
By Sefan Linders
The communication plan is part of the first cycle “agreeing on planning objectives and stakeholders”. Within the first cycle this tool is part of the theme “selecting participants and planning approach”.
The goal of this document is to answer several basic questions concerning this tool by means of the following basic questions: what, why, when, how, where, who as described by Kipling [KIPL98]. The document is structured according to these questions.
What
As the organization of IT is part of a larger organization, communication with the other parts of an organization is important for good functioning. Also within the IT organization, communication is important. A communication plan defines communication mechanisms to be used to communicate plans and to keep the process alive [SALM02]. A communication plan identifies people with an interest in the project (stakeholders), communication needs, and methods of communication. For example, the communication plan can describe basic reports that will be produced and meetings that will be held [BCB03], a description of the communication objectives, policy issues and communication within the organization and outside of the organization. [FER99]
Why
Effective communication will assist in the current direction of organisations into self-directed or self managed work teams. Executives hope that these teams will help push accountability down, to focus decision making at the grass roots of the operation. [FLE99]
Good internal communication ensures a better morale within the group. It is demoralizing to hear about what is happening in the group from someone outside the group.
[NSBA96]
When
The communication plan is part of the first cycle of the four cycles method [SALM02], and therefore can be written each time this cycle is done. Otherwise, a communication plan can be written yearly, i.e. at the beginning of the annual year [FLE99].
How
This plan uses the objectives and perspective of the business or functional unit as a starting point. Write the plan from the perspective of the larger organization. The person should be familiar with the operations and procedures of the larger organization, and aware of its strengths and weaknesses. Most communication planners have this flexibility and awareness because they work on an ongoing basis with people throughout the organization.
In terms of length, the strategic communication plan should be relatively brief, concise, focused, and readable. The average reader of a communication plan will be an expert in the business of the company or government department. Therefore, detailed explanations may be unnecessary. A communication plan should not exceed 10 pages if the creators want others to read and use the plan on a daily basis.
A communication plan can contain as many as 13 sections: a background statement, corporate or business/functional objectives, policy issues, external environment, internal environment, windows of opportunity, communication objectives, themes and messages, communication priorities, strategic considerations, requirements for consultation, partnership, negotiation
performance indicators and financial resources [FER99]. Of course the treatment of these subjects in the plan depends on the size of the IT organization. The background statement, policy issues, external and internal environment are described in more detail below.
Background statement. Positioning of the business unit in the larger environment. Not necessary if the communication plan is part of a greater business plan.
Policy issues. An increasing number of organizations have accepted the principle that every strategic plan must have a communication component that addresses management of the organization’s critical and emerging issues. Thus, the communicator searches for evidence of policy decisions or strategies that could have a significant impact on the communication planning activities of the organization.
External environment. The role of the strategic planner is to provide management with an analysis of stakeholder views and activities that could affect the operations of the organization. The term external environment, in this context, refers to the climate of opinion and knowledge outside the boundaries of the organization, which can be the IT organization.
Internal environment. This part of the plan outlines positive and negative factors in the internal environment. Much of the information incorporated into this section of the plan pertains to employee perception, drawn from the results of communication audits. How employees feel about their organization has a potentially huge effect on their performance. Thus, this section of the plan includes references to practices with a positive or, alternatively, a negative effect on employees. [FER99]
Who
Ideally, the head of communication oversees the process of generating this plan. As a member of the executive team, this individual comprehends the larger vision of the organization, including the corporate priorities. Moreover, the credibility of a communication plan depends, in no small measure, on the credibility of the chief communication executive. [FER99] Of course, within an IT organization, the head of communication within that organization will be the head of this department. In this case, the CIO will be the one who writes this plan. [WAPE02] Within a project, the project manager will responsible for identifying communication needs and deciding whether a formal communication plan is needed. [WAS02]
Way 11. Analysis of contingencies
By Wouter Driezen
The analysis of contingencies [FEEN87]; [EARL89] is one of the possible outcomes of the first planning cycle as noted in the four cycles method for formulating dynamic IS strategy [SALM02]. In this writing, I will first shortly explain what such an analysis consists of, and then I will give insight in why it could be used. I will then follow with some words on when the analysis of contingencies can be used, how the analysis can be performed, and where this all can take place. Last, I will give an example of a possible conductor of the analysis and possible participants.
What
As said, the analysis of contingencies is one of the possible outcomes of the first planning cycle of the four cycles method. This analysis gives a description of the present IT structure as well as the past successes and failures of this IT structure. It also describes the stage of adoption and management of the existing IT. Furthermore, it describes the strategic impact of IS, that is the positioning of the organisation in the strategic grid and the assessment of past and future dependence on IS [SALM02].
Why
The analysis of contingencies is used to get insight in the degree to which the planning approach, that is about to be chosen, fits with the so-called contextual variables. The insight obtained from such an analysis is very useful, because a planning approach on IS strategy should not be significantly different than the planning approach that is generally used in the organisation at hand, nor should it differ too much from the organisational control structure. Thereby, the planning approach should reflect the complexity and significance of the organisations IS and the consensus about the mission of the organisation’s IS department [EARL89]; [DOUK94].
When
Being a possible outcome of the first planning cycle, it is clear that the analysis of contingencies should be performed during that first cycle. Yet, the first planning cycle can be divided in three planning tasks. These are (1) the evaluation of previous planning results, (2) setting the scope of planning and selecting objectives, and (3) selecting participants and adjusting the planning approach. The analysis should be performed as part of the third planning task. The value of performing the analysis when first implementing the four cycles method, I guess, everyone will agree on. However, I think, the value of the analysis does not decline when going through the cycle at a later point in time. This because with every cycle the context changes. Therefore, it is not unlikely that the planning approach chosen in the previous period is inadequate in the present situation. So, even though one may conclude in the first planning task that the previously used approach was indeed the right one, that does not imply its fit today.
How
A way of performing an analysis of contingencies is by documenting all IT structure and interviewing the head of the IS department as well as end-users on the successes and failures of the IT. If done thoroughly once, it only has to be updated with every new period. Interviewing and monitoring management can clarify to what extent current technologies are adopted and how they are managed. To uncover the strategic impact of IS in the organisation; one can interview top-management and read past IS-strategies. To supplement these, one can use the Information Intensity Matrix [PORT85].
Where
The analysis of contingencies is performed inside the organisation. This is a logical consequence of what the analysis comprises. Additionally, the analysis is used to determine an appropriate planning for use inside the organisation.
Who
In my opinion, an independent individual can best conduct the analysis of contingencies. This can be someone from outside the organisation or someone from inside who is granted enough independence to be able to speak and freely. One can imagine, for example, the head of the IS department is unwilling to admit past failures of IT. They independent individual should be given enough competences to be able to address employees of all layers in an organisation and of all departments in order to get a well founded insight in the contingencies as mentioned above.
Way 12. Planning approach and methods
By Ingmar Eeftink
As primary goal of the first cycle of the “four cycles method” shown in [SALM02], defining the approach selected for the Information Strategy planning is an important task of this method. It is evident that without a proper definition one could create an IS strategy which is not properly aligned with the organization and would therefore probably fail.
Before one can define a correct approach, which fits a selected organization, it is critical that the current situation has been studied, proper objectives have been set, targeted outcomes have been defined and that the scope of the project is known. This is, as mentioned by [SALM02], a natural starting point as the evaluation of previous planning results must be used for the evaluation of the selected approach.
In general one can say that the planning approach should not differ too much from the organization’s general planning style and control structure and it should also reflect the complexity and significance of the organization’s IS and the consensus about the mission of organization’s IS department [SALM02].
Five phase model
In this document a “five phase model” will be used to define the proper IS planning approach. According to [SMIT96] there are five phases, or stages, in which an organization can be, which will be defined later on. In order to determine in which phase an organization is located, there is a description in terms of four aspects of Information Strategy, also mentioned as “situational influences”. These four aspects are the following:
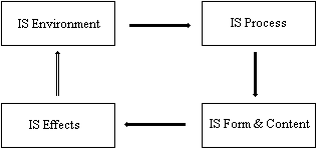
Figure 7 - The four aspects of IS
1.Environment. Defined as all facts and conditions that do not form part of de Information Strategy process, but can or should influence it. The environment can be divided in “internal”, typology of the organization, general strategy, and IT competencies and IS strategy awareness, or attitude and an “external” environment, entailing customers, products and markets of the organization, relevant external technology developments, legislation and society.
2.Process. This incorporates the actual dominant view of the process as either mechanistic, problem driven or political. Other important items are the methods and tools that are used, the participants and their roles and linkages with corporate strategy.
3.Form and content. The form denotes the degree of formality and regularity of the documentation (degree of simplicity, number of pages). The content falls into the following categories: objectives for the information function, architectures, rules and plans.
4.Effects. These are the intended and unintended effects of the IS. Items of interest are results and outcomes of previous Information Strategies. As shown in figure 1, effects influences the Internal Environment as effects include the changes in IT and IS architectures.
Using these four influences, we can now determine in which of the following stages the selected organization is located at this moment. The five organizational phases are hereby declared as:
1. Turbulence: A specific event (for example a merger, a new manager or an external disturbance) arouses strategic interests in IT. There is uncertainty and experimentation with entirely new approaches here.
2. Orientation: A new analysis of the environment has been made here, new goals are formulated, the IS is rewritten and new methods of strategizing are tried.
3. Consolidation: Senior management decides formally to apply the new uses of IT. Structures for the application of new IT are adjusted, successful applications and methods are extended and duplicated.
4. Exploration: The organization gets used to the new structures, procedures and technologies. Efficiency comes into focus; reduction of costs becomes part of the business and Information Strategy. Detailed procedures exist and responsibilities have been decentralized.
5. Tension: Shortcomings and missed opportunities become acute and the existing structures seem to obstruct organizational development. Stakeholders are actively looking for and experimenting with change.
The five phases are linked to the four previously mentioned influences: the environment, the process, form and content and effects. In table 5 there is an overview of the approaches to Information Strategy in each organizational phase. In this table a “-“ means that the item is not defined in that phase.
Organizational phase | |||||
Information Strategy | Turbulence | Orientation | Consolidation | Exploitation | Tension |
Environment Shock IT competencies IT awareness Process Process Type Methods/tools Top management Form and content Objectives Architectures Plans Effects Project level Bottom line | Current Seeking Very High Political / Problem driven No Very active Focus - Tentative Yes No | Recent Expanding High Political / Mechanistic Yes Active Established Experimental Flexible Yes No | - Expanding High Mechanistic Yes Supportive - Focus Firm Yes - | - Stable Low Mechanistic Customized Low - Stable Firm - Possibly | Imminent - - Problem driven No Growing - Outdated - - - |
Table 5 - Overview of the approaches to Information Strategy in each organizational phase
Using this table, one should be able to define in which category the organization is located and with that align the approach for Information Strategy planning with the correct phase.
References Chapter 2
[BCB03] The Complete Idiot's Guide to Project Management
door Sunny Baker, G Michael Campbell, Kim Baker
Alpha Books, 2003
[BECT] http://www.becta.org.uk/tsas/index.cfm?refsect=ntss&bcsect=ntss1% C2%A7=fits§=fits&id=tt5120
[BOYN87] Boynton, A. C., & Zmud,R. W. (1987). “Information technology planning in the 1990s: Directions for practice and research”. MIS Quarterly, 11(1), 59–71.
[Broadbent99] M. Broadbent, P. Weill and B.S. Ned, Strategic context and patterns of IT infrastructure capability’, Journal of Strategic Information Systems, Vol. 8, 1999 157-187
[CSUM00] CSU Monterey Bay (2000). “CSUMB Campus Strategic Planning: Communication Plan”.
http://csumb.edu/strategicplan/commplan.html
[DAFT00] Daft, R.L. (2000), Management, The Dryden Press, p410-411.
[DAFT02] Daft R.L. (2000), “Organisatietheorie en –Ontwerp”, ISBN 90 395 1982 X
[DANC70] Dance, Frank (1970). “The 'concept' of communication”. Journal of Communication, 20, 201-210
[DEPF97] Post Implementation Report & Lessons Learned, Department of Finance,
http://www.dof.ca.gov/HTML/IT/PMM/OPTIMIZED/PM6.3%20Project
%20Closeout%20PIER.pdf
[DOUK94] Doukidis, G.I., Mylonolopoulos, N.A., & Lybereas, P. (1994). “Information systems planning within medium environments: A critique of information systems growth models”. International Transactions in Operational Research, 1(3), 293-303.
[DYM01] Dymoke-Bradshaw, C., Cox., B, Developing organization-technology fit: the role
of evaluation in IS innovation projects, Electronic Journal of Information System
Evaluation, 2, 1, 2001 http://www.ejise.com/volume-4/volume4-issue1/issue1-
art2.htm
[EARL89] Earl, M.J. (1989). “Management strategies for information technologies”. New York: Prentice Hall.
[FER99] Sherry Devereaux Ferguson (1999), “Communication Planning: An Integrated
Approach”, Sage Publications Inc.
[GALL01] Galliers, R.D. (2001), Reflections on Information Systems Strategising
[GROV05] V. Grover, A.H. Segars, An emprirical evaluation of stages of strategic information systems planning: patterns of process design and effectiveness, Information & Management 42 pp. 761 to 779, 2005.
[HEE02] G. R. Heerkens, “Project Management”, McGraw-Hill,, 2002
[HEL03] K. Heldman, “Project Management JumpStart”, Sybex, 2003
[JANI72] Janis, J.L., Victims of group think: A psychological study of foreign policy
decisions and fiascoes. Boston, MA: Houghton Mifflin (1972)
[JOUI04] Jouirou et al., Strategic alignment: a performance tool, Proceedings of the Tenth Americas Conference on Information Systems, 2004.
[KARA94] S. Karababas, H.Cather, Developing strategic information systems, Integrated Manufacturing Systems 5, No. 2, pp. 445 to 461, 1994
[Keen91] Keen,P (1991) Shaping the future, Harvard Business School Press,
Boston, 1991
[KER01] H. Kerzner, “Strategic Planning for Project Management Using a Project Management Maturity Model”, John Wiley & Sons inc, 2001
[KIPL98] Kipling, R.(1998), “The Elephant's Child”, Event Flow Diagrams, Flynn & Jazi, IS Journal, July, no. 8, pag. 53-83.
[KUM90] Kumar, K., Post Implementation Evaluation of Computer-Based Information Systems: Current Practices, Communications of the ACM, 33, 2, 1990
[KRU00] P. Kruchten, “The Rational Unified Process An Introduction, Second Edition”, Addison Wesley, March 14, 2000
[MEMP] http://is.memphis.edu/depts/vpcio/unzoped/itsp2003/itsp2003
[MINA99] Mina S. K., Suhb E. H. and Kim S. Y. (1999), “An integrated approach toward Strategic information systems planning”, The Journal of Strategic Information Systems Volume 8, Issue 4, December 1999, Pages 373-394
[MUKA05] Muntslag, D.R. and Katsma, C.P., The art of Implementation, In Reader IITO
(2005), chapters 3,4
[NSBA96] National School Boards Association (1996). “The Communication Plan”. http://www.nsba.org/sbot/toolkit/tcp.html
[NSW03] Government of New South Wales, Strategies for documenting government business: Step H: Planning the post implementation review, 2003
[PALA01] Palanisamy,R (2001). “User involvement in information systems planning leads to strategic success: an empirical study”. Journal of Services Research, Volume1, Number 2 (October, 2001)
[PEFF04] Peffers, K.,& Tuunane, T.(2004), “Planning for IS applications: a practical, information theoretical method and case study in mobile financial services”, Information & Management
[PMI00] Project Management Institute, “A Guide to the Project Management Body of Knowledge (PMBOK Guide) 2000 Edition”, Project Management Institute, USA, 2000
[PMI01] Project Management Institute, “Practice Standard for Work Breakdown Structures”, Project Management Institute, USA, 2001
[PORT85] Porter, M. E. & Millar, V. E. (1985). “How Information Gives You Competitive Advantage”. Harvard Business Review, 62(4), July-August: 149-160.
[PREM91] G. Premkumar and William R. King. Assessing Strategic Information Systems Planning, Long Range Planning, Vol. 24, No. 5, pp. 41 to 58, 1991.
[SALM02] Salmela, H. & Spil, T.A.M. (2002). “Dynamic and emergent information systems strategy formulation and implementation”. International Journal of Information Management 22, 441-460.
[SALM03] H. Salmela, A.M. Spil, Dynamic and emergent information systems strategic formulation and implementation, IT Management Select, vol. 9, No. 3, 2003.
[SMIN99] S.K. Min, E.H. Suh, S.Y. Kim, An integrated approach toward strategic information systems planning, Journal of Strategic Information Systems 8, pp. 373 to 394, 1999.
[SMIT96] Smits, M.T. & Poel, K.G van der (1996). “The practice of information strategy in six information intensive organizations in The Netherlands”; Journal of Strategic Information Systems 5; 1996; pages 93-110.
[TUR05] N. Turbit, “Defining the Scope of a Project”, The Project Perfect White Paper Collection, 26-06-2005
[TUR88] E. K. Turner, “Scope definition for bidding project-control services”, Butterworth & Co (Publishers) Ltd, Vol 6, No 1, Feb 1988
[VEDA01] Vedabrata, B., E. Hartono, A.L. Lederer & V. Sethi (2001). “The impact of organizational commitment, senior management involvement, and team Involvement on strategic information systems planning”. Information & Management 39, pp. 513-524.
[WARD02] Ward, J., Peppard, J. Strategic Planning for Information Systems, 3rd edition, John Wiley & Sons Ltd., 2002.
[WAS02] Communication Plan, University of Washington, 2002
http://www.washington.edu/computing/pm/plan/communication.html
[YEO02] K. T. Yeo, “Critical failure factors in information system projects”,
International Journal of Project Management, no. 20, pp 241-246, 2002
[ZHU04] Y. Zhu, S. Chen, “SCOPE: A Conceptual Framework of Ontology-based ProgramProject Scope Control”, LACCET2004, 2004
Chapter 3 – Alignment
Reviewing existing plans, documents and information sources | ||
#13 P73 | List of existing useful documents | Past projects have created a large amount of documentation which, if properly documented, can be reused in the planning process including, for example, workflow diagrams and management control models. |
#14 P76 | Internal information sources | Sources for information about the current IS/IT perspective in the business, its maturity, business coverage and contribution, skills, resources and the technological infrastructure. Current strategy, objectives, resources, and activities and the culture and values of the business. |
#15 P79 | External information sources | Sources for information about technology trends and opportunities and the use made of IS/IT by external bodies. The economic, industrial, and competitive climate in which the organisation operates. |
Conducting business and technology analyses | ||
#16 P83 | Implications of corporate strategy for IS objectives | Identifies business goals and plans and deduces IS requirements via a formal method for translating them. |
#17 P85 | Implications of other business analyses for IS (CSF, SWOT) | Identifies critical processes in the organisation (core competencies) to be supported by information systems. Combines and groups the critical success factors with the strengths, weaknesses, opportunities and threats to derive information objectives. |
#18 P89 | List of new future acts or events | Indicates for the coming three years how markets and clients can change, what opportunities for data retrieval there will be, which technical progression is suspected, which organisational changes are planned and possible, which new methods are in theory available. What is the budget prognosis for the coming years and which new activities can we develop and which activity we should drop. |
#19 P91 | Classification of certainty of acts and events | For each act or event found in outcome #18 a certainty and time scope is given to evaluate which act or event needs attention |
Aligning IS plans with business objectives | ||
#20 P93 | List of new project ideas with priorities | Lists initial project ideas and opinions of the participants about their priorities costs and risks. For high priority ideas the risks and benefits of the ideas are worked out in detail and according to those results a new priority scheme is made. |
#21 P95 | Aligned IS plan and project priorities | Documents the shared vision between senior managers of the organisation in which direction information systems should go. Clear priority decisions are made by senior management and information management on which objectives and which ideas priority is given. |
#22 P97 | Senior management participation | Describes how senior management will control that the agreed priorities are taken into consideration in the rest of the planning process. |
Why?
Past projects have created a large amount of documentation, which, if documented well, can be reused in the planning process [SALM02]. But, in what way can previously established documents be useful in the Strategic Information Systems Planning (SISP) process? According to Ward & Griffith [WARD96, p135] the purpose of existing documents is to develop an extensive understanding of the business in its environment, and to interpret its current, planned and future potential needs. In addition, Hoffer, George & Valacich [HOFF02] identify the usefulness of existing documentation. They argue that during SISP in order to develop strategies and (IS) project plans to migrate to the desired future state it is, amongst other things, needed that an organization should model its current situation. Existing documentation such as a written corporate strategy document can contribute to this.
What
As concluded earlier in order to gain an (in-depth) understanding of an organization’s current business and IT/IS situation it is necessary to dig into existing documents that describe or model certain parts of it. Among other information-seeking activities in this way, it is possible to establish blueprints of the organization’s situation. These blueprints can also be used for other purposes (e.g. analyses, determining future needs and alignment business/IT). However, what kind of existing documents are used? The list gives some examples. After the summing up they will be shortly outlined. In order to maintain readability we have distinguished three different categories in which the documents can be placed. These three categories are based on the ‘3 lagenmodel’ [DOOL02].
Business
•Business/Corporate Strategy
•Vision
•Critical Succes Factors (CSF’s)
•Organizational architecture
•Organizational structure
•Functions, roles and responsibilities
•Process architecture
•Business processes diagrams
•CSF’s
•roles
Business-IS
•Information architecture
•Information needs
•Application portfolio
•Human resources
IS/IT
•System architecture
•Data-architecture
•Network architecture
Business environment
The documents in this section should provide for some blueprints of the vision, strategy, organizational structures and processes of the organization. The corporate strategy of an organization can be found in an official document. The corporate strategy often contains elements such as the mission, vision and Critical Success Factors (CSF’s) [WARD96, p164-165].
The organizational architecture describes aspects such as the organizational (formal, static) structure, functions, roles and responsibilities. The different documents should give insight in aspects such as how the organization is currently organized and is being controlled. This comprises questions such as the division of responsibilities among organizational parts (divisions, functions). Also, it should give insight in how the three levels (strategic, tactical and operational) fit into this picture. In large organizations, the formal organizational structure can often be found on paper. Also, the functions, roles and responsibilities can be documented well (e.g. function descriptions).
The process architecture describes which business process there are within the organization and how they are organized. The process architecture should give insight in aspects such as how activities are linked together (across inter- and intra-organizational boundaries) and where/how they provide outputs to internal (e.g. divisions, management staff) or external customers (e.g. suppliers, clients) [WARD96]. Also, it should be clear which roles (within certain)/functional departments are involved in which activities. Also, CSF’s or process indicators can be documented. These indicators can be used to analyse and improve the current business processes.
Business-IS/IT
The documents in this section should provide for some blueprints of how the IS/IT environment supports the business environment (e.g. business goals, business processes). The blueprints in this section should model how an organization currently attains her Business/ICT alignment.
The information needs should describe aspects such as how certain information systems support certain business process and activities within these processes. With ‘how’ is, for example, meant which information system (e.g. Enterprise Resource Planning System, Workflow Management System) and what data items are used. Another document might be a description of the current application and/or IS portfolio. The applications and/or IS are categorized in terms of their role in current (and future) business needs (strategic, high potential, key operational and support) (WARD96, p142). In modelling current IS-needs and application portfolio’s an organization can, for example, identify new IS that support current or future improved business processes and/or business goals.
Not only IS/IT supports the business environment, but also people within the organization. It is therefore important to have an inventory of the available knowledge and IS skills of the employees within the organization. These skills reside mostly at the IS-management group. However, it is also necessary to make an inventory of the knowledge that resides at non IS-levels (e.g. management, BS users). There might be a lot of tacit knowledge. This way it can be determined if there is a lack of knowledge and further training is needed in order to attain the desired situation.
IS/IT environment
These documents are about the technical infrastructure of the IS/IT environment [DOOL02].
Documents describing the system-architecture are, for example, about the physical (hardware) and logical systems (middleware) and their structure . Physical systems are things like clients (e.g. workstations, terminals) and servers. Example of middleware components are application- and database servers (software-based).
Documents describing the data-architecture are, for example about the technical representation of the (corporate and application) data. With ‘representation’ is meant a representation of how the data is stored and what the storage-structures are (e.g. relational databases, object-oriented databases). Documents describing the network-architecture are, for example, about how communication (e.g. messages between applications and/or systems), both physical (e.g. routers, bridges) and software-based (message protocols and object protocols).
How
How are these documents established? All the documents listed above should be established by means of analytical approaches rather than creative approaches. This is because the former takes a structured analysis route from the upper (organizational) levels to lower levels, systematically decomposing each level according to its characteristics (WARD96, p136).
The analytical approach can be supported by means of several (formal) business and information modelling methods, tools and techniques. These means can both be on paper as ‘computer-supported’. The latter may also allow for various interactive analyses.
For modelling the ‘Business domain’ one could use a technique such as the ‘Dynamic Enterprise Modelling Development Method’ developed by the Baan Company [ESPO96 cited in: LIMB02]. For the Business-IS domain one could use a tool such as ‘Bizzdesigner’ [BIZZ03] or Affinity Clustering [HOFF02]. For IS/IT modelling one could use UML-techniques such as component-diagrams and deployment diagrams [LETH01]. It is also possible that an organization has developed its own in-house standards for the three different categories (Business, Business-IS and IS/IT) Because it is argued that an analytical approach is preferred, it is advisable to do this top-down from an organizational point of view. In business modelling, top and functional management should have the most input because they have the most knowledge concerning the business domain (e.g. structure, processes). For the business-IS domain it would be the IS and functional management. For the IS/IT it would be mainly the IS management.
Because it is possible to use formal tools, it is advisable to determine in advance if the organization has the necessary (in-house) knowledge and experience. If not, it is wise to consult an external expert. Hiring an external consultant has also the advantage of dealing with negative side effects such as ‘context-tunnelling’. An external expert has a fresh and (presumed) unbiased look on your organization. Also, often he can tap into other resources.
Preface
The second planning cycle of the four cycle method[SALM 03] for e-strategizing is all about alignment of business objectives and information objectives. The main goal for the cycle is to create innovative and strategic new plans. Before you know where you want to go, it’s useful to know where you are now so a path can be determined. Therefore a starting point for those new plans is a thorough investigation of existing plans, documents and information sources. Besides the information on paper it’s important to capture tactic information that’s only inside the heads of employees. This tool will help in analyse the internal information sources and create a ‘management summary’ view of IS demand, to support the e-strategy.
What
To support the e-strategy team in proposing new plans, a high level view of the current internal information is needed. The output should be will be limited to a maximum number of pages to force a selection of essential information (i.e. max 10 A4). This high level view should cover:
-Current use of IS/IT in the business, it’s coverage, it’s maturity of use and who uses it and what is it’s contribution.
-What skills do we have in what areas and how do these skills contribute to our business mission (from end users to IT staff).
-What resources and the technological infrastructure do we have, what is the current strategy and what are our objectives, what are our primary and supporting processes
-Mission, objectives, culture and values of the business.
[SALM 03], [GAKK 91]
Why
The reasons for doing this analysis are:
•Getting a clear view of the current strategic use of IS/IT in the organisation
•Clear view of existing resources (people, technology, skills)
•Not making the same mistakes again. It’s common knowledge a lot of IT projects fail, it’s important the top management takes these lessons into account.
When
This analysis should be done at the very beginning of the second planning cycle of the four cycle method [SALM 03] for e-strategizing . The total time spent should be balanced with the other tasks in this cycle, like external information, that is equally important. It’s important to spend enough time in discussion with employees to get the information that’s only in their heads onto paper.
How
The most important input is discussion time with all levels of management and end users. Much of the key information required is often in the heads of employees at all levels in the organization and needs to be elicited through discussion. However, discussions and workshops will be wasted effort and frustration for business people if used to establish facts that can be obtained from available documentation[WARD 02].Therefore it’s best to start with creating the summary document before having workshops to validate and extend this document. The first part of the analysis is document research of the company in a top-down analysis. The following information needs to be gathered:
•The top of the iceberg is the business strategy
oMission/vision
oObjectives
oCritical success factors
•The business processes actually execute the strategy
oActivities, actors
oInformation flows
•The organizational environment (internal environment) is the layer on which the processes depend to operate.
oStructure, relationships
oAssets
oSkills, knowledge
oValues, style, culture
[WARD 02], [EARL 89]
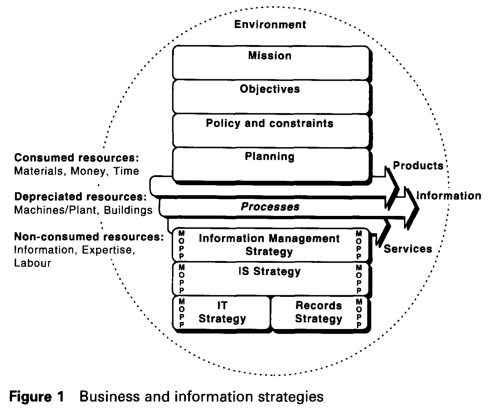
Figure 1 gives a abstract picture of the relationships of the elements from our top town analysis described above. [BUCH 98]
The result of the above analysis is a foundation, but not yet IS/IT specific, and also doesn’t go very deep on detail. To get a clear view of the actual IS demand Ward [WARD 02, page 205] suggests over 30 tools in 11 categories. In the following table the 15 tools are selected, most relevant for this analysis.
Critical success factor analysis | Areas of business where things must go right Performance measures |
Balanced scorecard analysis | Business objectives and key information requirements |
Business portfolio | Options for long term IS investment to strengthen competitive position |
Process analysis | Identification of core business processes Effectiveness of processes in meeting drivers Process improvement options Process (re)design blueprints Resultant IS/IT options |
Technical business modelling | Conceptual architecture |
Current application portfolio | Profile of current applications |
IT technology infrastructure | Inventory of current hardware and software. Analysis/test of skills of employees per department |
Table 1: Areas and tools for second level analysis of IS demand
The results from these tools should give a clear view of current use of IS/IT, the skills of people, the available resources and the objectives and values of the business. This view can be used for discussion with management and employees to clarify and append it. Finally this result can be used for a presentation to top management and the e-strategy team.
Where
Since this tool is about gathering of information from internal information sources, it’s most logical to be inside company. Direct access to all information documents, systems and people is of the essence.
Who
This analysis it selves is best preformed by a small team (i.e. 4 people) led by an external consultant. The role of the consultant is to prevent context tunnelling and to prevent implicit information not getting written down. The remainder of the team needs to be able understand and summarize the gathered information and place the collected information into coherent context. As described before discussion with management and employees also plays a key role, this strongly increases the number of people indirectly involved.
Preface
This document will give a description of tool no. 15: External Information Sources. This will be done by the methodology of the ‘six honest men’, as stated in the assignment.
What?
The tool External Information Sources is a tool that can be used in the alignment cycle. Its aim is therefore to gather information that can be useful to the formulation of a company’s e-strategy. Since the second cycle is about innovation and analysis [SALM02], reviewing existing plans, document and information sources are important in order to obtain alignment between business strategy and IS-strategy. Tool no. 15 focuses on the analysis of external information sources, like on trends and opportunity in IS/IT and on the economic, industrial and competitive climate. Important is that these information sources are not created within the company, but externally. The main task of the 2nd cycle is to promote strategic thinking, creativity and innovation and external information can offer surprising and new insights to the company and can give information on developments that are not controllable for the firm (e.g. technological development, economic climate).
Why?
According to Earl [EARL98] the tracking of key technological developments enables managers to identify opportunities, which might lead to a competitive advantage. This, and the already mentioned aspect that external information promotes creativity and develops new insights, makes it very useful for companies to keep track of developments.
When?
Henderson & Sifonis [HEND98] state that the relationship between strategic business plans and IS plans should be seen as an iterative process. Therefore, it is useful for a company to keep track of external information at any time. The keener a company is on new developments in the environment; the faster it is able to respond to these and to obtain a competitive advantage. However, according to the four cycles method of Salmela & Spil, external information is most useful for a project after the scope and objectives have been set. This slight difference is most likely due to the fact that external information sources are not specifically meant for the company and its problems/opportunities. Therefore, information on developments is only applicable for the company after it has formulated its scope and objectives. It is not impossible however, that external information is the actual driver of new scope and objectives.
How?
External sources contain information on the company’s environment. There are several methods to analyse the environment, in fact, there is so much information available that one might loose track of what kind of information is important and what is less relevant. A company should try to collect information on the environment and translate it to useful knowledge and insights. Frameworks can prove to be extremely helpful for this. I therefore suggest that a company should make a distinction between several layers of the environment (see figure). For each layer, there is a specific tool to analyse it.
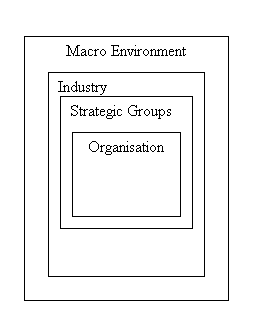
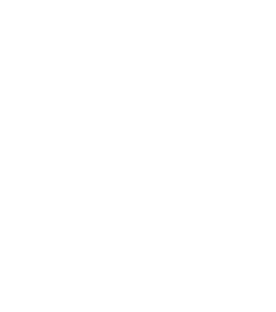
Figure 8 - Organisational environment (Source: Johnson & Scholes, 2002)
Macro Environment
A tool to analyse the macro environment is the PESTEL framework. This framework identifies six environmental factors, political, sociocultural, economic, environmental, technological and legal. The advantage of this distinction is that the macro environment becomes somewhat less complicated. All six factors are relevant, but for the formulation of the IS-strategy, some factors are more (technology, legal) or less (political, environmental) important for the company. Information on PESTEL factors are relatively easy to determine and the framework itself can assist. For a company, the PESTEL framework is relevant, because it gives insights on the environment. Because the environment is dynamic, it should be updated once every few years.
Industry
For analysing the environment on the industrial level, a good tool is Porters Five Forces Framework [PORT80a]. This framework identifies five different forces on an industrial level that can influence the company. The five forces are: Potential entrants, Buyers, Suppliers, Substitutes and Competitive Rivalry. Each force can have its own impact on the competitive position of the company. The Five Forces Framework identifies several kinds of impacts for each force. The environment can be more dynamic on the industrial level, so it is important to keep a keen eye on changes. Information should be updated at least annually.
The P5F framework only gives an overall or helicopter view, it therefore is needed to get more specific tools that gives an in debt look on the five forces.
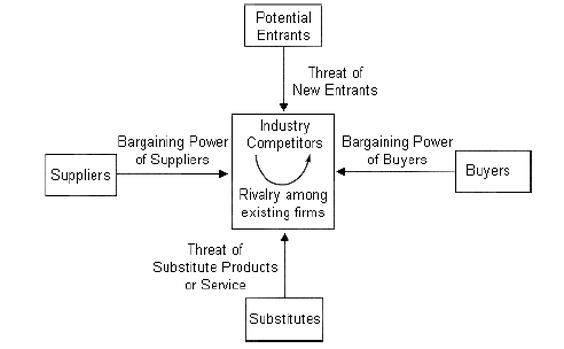
Figure 1 - Porters Five Forces Framework [PORT80]
The Ansoff Matrix is a marketing tool that was first published in the Harvard Business
Review in an article called ‘Strategies for Diversification’ (1957). This tool is related to two forces of the P5F framework, namely rivalry and threat from entrants. The tool can be used for getting more in dept external information of the industry.
The matrix (shown in figure 2) consists of four quadrants as follows:
1. Market Penetration
Here existing products are marketed more effectively to existing customers.
2. Market Development
Here the existing product range is launched in a new market.
3. Product Development
This is where new products are marketed to existing customers.
4. Diversification
This is where completely new products are marketed to new customers.
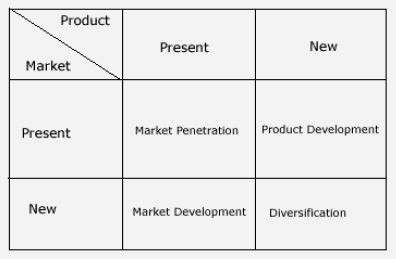
Figure 2 - The Ansoff Matrix [WARD05]
Strategic groups
Strategic groups are organisations within an industry with similar strategic characteristics, following similar strategies or competing on similar bases [JOHN02]. Insights in strategic groups is very useful for the company, because the company can better understand its most direct competitors and it can try to obtain competitive advantage over them by making use of this information. Porter (PORT80b) and McGee & Thomas [MCGE86] identify several characteristics for the analysis of strategic groups. The environmental level of strategic groups can be highly dynamic and information should be updated regularly.
Determining who competes with whom in the industry and the dimensions along which competition and differentiation occur, requires that the characteristics of the industry's dynamics be understood and that individual firms be grouped in some way. This can be done at looking at the following characteristics:
oGeographical coverage
oQuality of service levels
oMarketing spend
oProduct range
oFinancial and economic
oMental models of the industry structure
oNetworks of relationships
Which of these characteristics are most relevant in an industry needs to be understood in terms of the history and development of that industry and the forces at work in the environment.
This concept is useful in several ways. It helps understand who are the most direct competitors of any given organisation, on what basis competitive rivalry is likely to take place within each strategic group and how this is different from one group to another. Also it can be used to plan a change to another strategic group.[JOHN02] [THOM99]
Where?
The gathering of external information is not tied to a physical location, so it can be done everywhere, but a location with near access to (governmental) archives is recommended.
Who?
The gathering of external information is a process that can be done by virtually everyone. It is therefore not unlikely that a company chooses outsourcing for this activity. However, the translation of environmental information to information that could be useful for strategy formulation should be done by at least a stakeholder in the process, but preferably by someone of the middle or top management.
Way 16. Implications of corporate strategy for IS objectives
By Claartje van der Linden
In this paper, a description will be given of a tool that is part of the second planning cycle in the Four cycles method [SALM02] for formulating an information systems (IS) strategy. This second planning cycle is focused on alignment of business objectives and information objectives. The tool that will be described is an element of the business and technology analyses, which are an important part of the cycle.
The main goal of the tool is: Identifying business goals and plans and deducing IS requirements via a formal method for translating them.
The tool will be described by making a ‘what, why, when, how, where, who and what else’ analysis.
What?
With this tool, the implications of corporate strategy are translated into IS objectives and requirements. A corporate strategy is ‘the plan of action that prescribes resource allocation and other activities for dealing with the environment and helping the organization attain its goals’ [DAFT00]. This strategy has impact on both the business-level strategies and the functional-level strategies, or, seen the other way round, both forms of strategies are realizations of the corporate strategy. IS strategy can be perceived as a functional-level strategy, because it answers the ‘How do we support the business level strategy to compete?’ question [DAFT00]. It can also be seen as more than just a functional-level strategy, because nowadays IT and IS can have major impacts on the competitive position of a company.
By making the translation formal, the tool can be applied to different kind of business strategies in different companies.
Why?
By making sure the business plans and goals of the corporate strategy are translated to the IS strategy, corporate strategy and IS strategy can be aligned. This alignment is important to make sure that IS strategy supports corporate strategy. In addition, it is important to keep the objectives of the different departments integrated; corporate strategy should represent all these objectives. A good alignment means a good (IT-) realization of business goals, which can help a company to compete in a competitive environment (or at least keep up with competitors). IS can, for example realize efficiency and integration, which can help to cut costs. The ways in which IS strategy can support and realize corporate strategy have to be well formulated in the IS strategy.
When?
Time is an important factor in translating the corporate strategy to an IS strategy. To make sure corporate strategy does not demand too much or too little from IS strategy, it is a good thing to keep the IS and IT possibilities in mind when formulating the corporate strategy. On the other hand, with this tool IS strategy is deducted from corporate strategy, so IS objectives can only be formulated after the corporate strategy is clear. Because nowadays IS and IT can realize competitive advantages (or at least make sure a company can keep up with competition) and therefore is very important within a company, it would probably be a good thing to formulate corporate strategy and IS strategy at the same moment. However, in reality, this can be difficult; because it implies that a change in corporate strategy immediately has to be translated to changes in IS requirements. Anyway, it is important to keep the mutual influence in mind, especially when considering the factor ‘time’.
How?
There has to be a formal tool to link corporate strategy with IS strategy and to translate corporate strategy to implications for IS objectives and requirements. This tool could, for example have the form of a chart with an input (corporate strategy)/ output (IS objectives) format. To realize such a chart a lot of common corporate strategies and their impact on IS objectives should be investigated and written down. When using such a chart, you should be aware that everybody can use it. It can guide you, but it will be difficult to use it for creating a competitive advantage.
Another more creative way of realizing this tool, would be by involving the main stakeholders (see ‘who’), making a list of strategic aspects in which IT and IS could play a role and then brainstorm about ways in which these aspects could be translated to IS objectives (black box approach).
Where?
This tool can be useful in every company that wants to create good integration of corporate strategy at all the different departments, including the IS department. Because almost every company nowadays uses IT and IS and because in almost every company IS plays a strategic role, you can say every company has to use a tool to create integration and translation. Even though the company is not very large, it is a good way to make clear what the relation between corporate strategy and IS strategy is in your company.
More concrete, the tool can be used within the top management and the IS department (main stakeholders, see ‘who’). In implementing the IS objectives probably many other departments and perhaps even people from outside the company will be involved.
Who?
The translation and linking has to be done by corporate and IS management. Corporate management is up-to-date about the ins and outs of the corporate strategy, IS management knows all about IS objectives. Also people from the IT department (well aware of the technical possibilities) and people from the financial department (who know how much money is available to realize translation and implementation of corporate strategy into IS strategy) have to be present.
What else?
Although many aspects concerning the translation tool have been described, some things need special attention:
•Corporate strategy can be incremental or comprehensive. This has to be taken into account when translating corporate strategy to IS strategy. An incremental corporate strategy will most likely be difficult to align with a comprehensive IS strategy.
•It should be kept in mind that IS objectives and IS strategy depend not only on corporate strategy, but also on a lot of other factors. Technological (IT) possibilities, changes in demands from users within the company and from outside the company and changes in IS used by other involved companies (for example in the value chain) are examples of other influencing factors. Most probably, these other factors are more dynamic and change more often than the corporate strategy.
•In translating the corporate strategy to IS objectives, it is important to be clear about the practical restrictions to this translation. Technical possibilities, costs and time are some of these restrictions.
•When using a formal tool for translating corporate strategy to IS strategy, it is important to keep in mind that such a tool is not sanctifying; also, the creativity, ideas and inspiration of the different stakeholders are important!
Way 17. Implications of other business analyses for IS
By Niels Bakker
With some additions by Corneel Hindriks
The main task within de second planning cycle is to promote strategic thinking, creativity and innovation in the planning process but also to ensure sufficient integration of IS plans with business plans. The emphasis is on identifying future IS projects that provide business value and support both business strategy and business processes.
The second planning cycle comprises three planning tasks:
•Reviewing existing plans, document and information sources
•Conducting business and technology analysis
•Aligning of IS plans with business objectives
De second task, conducting business and technology analyses, can have several outcomes. Examples of potential outcomes are:
•Implications of corporate strategy for IS objectives
•Implications of other business analyses for IS (CSF, SWOT)
•List of new future acts or events
•Classification of certainty of acts and events
In this paper, I will discuss the second outcome. This outcome identifies critical processes in the organization to be supported by information systems. It also combines the critical success factors (CFSs) with the strengths, weaknesses, opportunities and threats (SWOT) to derive information objectives.
Each year the top management produces a strategy for the entire organization. Its goal is to set a guideline for all employees to strive the same goal. In this way, the top management is trying to be more competitive.
The business strategy has implications for all departments within an organization. All departments have to make their own strategy in line with the business strategy and they must set measurable goals in order to keep control. The relationship between the IS plans and the business strategic plans should be iterative [HEND88]. The Business Strategic and IS Planning have to be valid (external) and consistent (internal). In order to create a consistent Business Strategic Planning, the critical success factor (CSFs) methodology is being used. The underlying concept of the CSF is that the whole is the sum of the individual parts: the success of the organization is the sum of the successes of individual business units.
The strategic IS planning process uses the goals established in the strategic business planning process. The critical success factor method is used to transform the strategic goals into areas that are critical to the IS planning process. In general, the CSF method comprises three steps: (1) interview with relevant managers, (2) focus group sessions to evaluate and characterize the relevant CSFs and (3) feedback, critique and adoption of the CSFs to provide a final CSF statement. The CSF approach is being used within the different business units in the organization and is time dependent; the criticality of the factors can change over time.
Another way to analyse what important issues are for an organization is to execute a SWOT analysis. SWOT stands for strengths, weaknesses, opportunities and threats. The SWOT analysis will show the managers the current situation of the organization and could be used as input for the IS planning process.
The strengths and weaknesses are internal. This means that internal characteristics of the organization will be analyzed in order to get more. The strengths are the positive characteristics that the organization can exploit to achieve its strategic performance goals. Weaknesses are characteristics that may restrict the organizations performance. The information sought typically pertains to specific functions such as marketing, finance, production and R&D. Internal analysis also examines overall organization structure, management competence and quality, and human resource characteristics.
Opportunities and threats are external. Opportunities are characteristics of the external environment that have potential to help the organization achieve or exceed its strategic goals. Threats are characteristics of the external environment that may prevent the organization from achieving its strategic goals. The competitors, customers and the suppliers are the most relevant to strategic behaviour.
During the strategic planning processes on different levels within the organization, SWOT analysis will be useful to obtain knowledge about the current situation and which characteristics should be exploited or neglected.
After discussing the critical success factors and the SWOT analysis, it is now possible to make clear why they are important for the IS planning process. IS department has to develop and maintain systems that are important to support work in other departments. This department is also up-to-date about innovations and new technologies within the field of IT and therefore should be able to choose the best technology available (bottom-up). The latter is not always possible when a new technology or system does not fit into the business strategy. The other way around is also possible. When the top management is trying to implement a system that is infeasible or old fashioned, the desired outcome is not possible and is frustrating the IS department (top down).
This proves that it is important for the IS department to give input to the business strategy. The critical success factors methodology makes this possible. SWOT analyses are important to derive the critical success factors. The opportunities and the strengths should be used during the determination of the success factors.
At this stage the SWOT-analysis and the critical success factor method can be applied to the theme: unification of Universities. The information planning process has to start by executing a SWOT-analysis. After identifying the strengths, weaknesses, opportunities and threats, it will be possible to identify the critical success factors. Questions that can be asked during the SWOT analysis can be found on the next page. The critical success factors are an important part of the IS strategy and can be send to the top management, so they can process these CSFs in the business strategy.
Important issues at this theme are the initiators of the IS planning process, because there is not one department of all Universities. Persons that are responsible for the IS department at the individual Universities should form a project group and create the documentation concerning SWOT en CSF.
Useful questions for a SWOT-analysis:
STRENGTHS:
•Define areas you excel in, such as the company's core competency and resource analysis
•What does your company do well?
•How strong is your company in the market?
•Does your company have a clear strategic direction?
•Does your company's culture produce a positive work environment?
WEAKNESS:
•Evaluate your liabilities
•What could be improved at your company?
•What does your company do poorly?
•What should be avoided?
•Is your company unable to finance needed technology?
•Do you have poor debt or cash flow?
OPPORTUNITIES:
•Analyze your customers and market attractiveness?
•What favourable circumstances are you facing?
•What are the interesting trends? Is your company positioned to take on those trends?
•Is your company entering new markets?
•Is your company advanced in technology?
THREATS:
•Check out what your competitors are doing and assess other potential challenges
•What obstacles do you face?
•What is your competition doing?
•Are the required specifications for your products or services changing?
•Is changing technology threatening your position?
•What policies are local and federal lawmakers backing? Do they affect your industry?
The consultant who uses this tool must take care of the interpretation. Intention and Synthesis is captured by the CSFs technique. After identifying the strengths, weaknesses, opportunities and threats, it is possible to identify the CSFs. The Business Objectives of the organization are also an important input for the CSFs. [WARD02] These could be found in the annual report of the organization.
Integration is done through transforming the CSFs into Information Objectives. The last stage of the model of Avison et al., Implementation, is not covered in our tool. But this is not necessary because the meaning of this tool is to create an IS-strategy and not to implement it.
The process of our tool is graphically shown in figure 2.
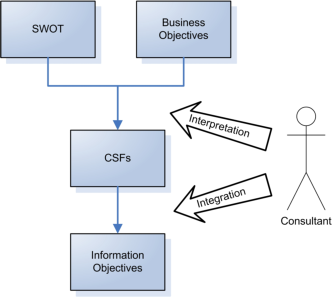
Figure 9: The process of this tool
Introduction
This report describes the outcome “List of new future acts or events”. This outcome is part of the second planning task “Alignment of business objectives and information objectives” of the second planning cycle of the Four Cycle Method by Salmela & Spil [SALM02]. In this report the theory of the six honest men is used [KIPL42], answers six questions; What and Why and When And How, Where and Who.
First to give an insight in the topic a description by Salmela & Spil is given: A list of new future acts or events:
Indicates for the coming three years how markets and clients can change, what opportunities for data retrieval there will be, which technical progression is suspected, which organisational changes are planned and possible, which new methods are in theory available. What is the budget prognosis for the coming years and which new activities can we develop and which activity we should drop [SALM02].
What
is a list of new future acts or events?
The outcome is part of the second cycle of the Four Cycle Method designed by Spil & Salmela [SALM02]. This cycle has the main task to promote strategic thinking, creativity and innovation in the planning process but also to ensure sufficient integration of IS plans with business plans (business goals). This outcome gives a long-term (3 years) indication of how markets/clients can change and what (technical) opportunities there can be. The key element in this outcome is to ensure (to encourage) creativity and innovating thinking among them who are involved in the project. New ideas can evolve here.
Why
is a list of new future acts or events necessary?
The main reason why this outcome should be used is to be able to spot opportunities (technology), which can lead to competitive advantage [SALM02]. It can be used to create and discuss new plans without the pressure of choosing and planning. In addition, a broad variety of people within an organization can contribute to this outcome.
Teo & Ang conclude that neglecting to adjust the IS plan to reflect major environmental changes is a major problem current IS managers have to deal with. Most IS planner did little technological forecasting [TEOA01]. They depend on their vendors to keep “fill in the list” with new technological information systems.
When
is a list of new future acts or events created?
A list is created in the beginning of a IS planning project. Later in the project, these “items” on the list are evaluated en some will make it to the end to be implemented after further analysis.
How
can a list of new future acts or events be created?
Analyses have to be made about future (coming three years) technical opportunities. This is a very difficult thing to do because not al upcoming technologies are known at the beginning of the analysis. New technologies may arise during the IS planning project. Technological advances cannot be predicted with confidence [TEOA01].
Several “traditional” analyses/methods can be used. The overall idea is to combine traditional methods with creativity and innovation. Strategic thinking, creativity and innovation can be explored by using brainstorm sessions to discuss new ideas [SALM02]. Brainstorm sessions have an informal character where all participant can express there ideas.
IS vendors can supply new technologies for all kind of business processes. However, most of the time vendors have a vested interest to hype up their product lines [TEOA01]. So IS managers should be cautious when dealing with IS vendors.
Existing IS plans/results can also be used in this part. The results of the previous outcome can be used; the SWOT analysis for example can be used (for both the market and technology) to identify opportunities and to get rid of the weaknesses, and to anticipate to upcoming threats.
It is important for IS planners (and participants) in this outcome to have sufficient knowledge about business processes and goals so that they can more effectively evaluate technical solutions proposed by vendors [TEOA01]. Because a major problem in failing IS plans is ignoring business goals as stated by Teo & Ang.
Where
in an organization should a list of new future acts or events be created?
To identify new technologies IS managers should look outside the company. A given example is to ask vendors about upcoming technological breakthroughs. Inside the company through brainstorm sessions new ideas can be discussed and answers like “What do we need?” and “What do we want?” can be answered (before going to vendors for example).
Who
should create a list of new future acts or events?
The IS manager is the main person to identify new technologies. Other participant through brainstorming should be able to identify the needs and compare them with the founded new technology. Participants are Senior management, IS management and user management.
Conclusion
Innovation, creative thinking without boundaries is very important in this outcome (final decisions can be made later [SALM02]). To identify new IS technology traditional methods/analyses can be used. It is also important to realize that not all new technologies are known/available at the beginning of the three years. Results of analysis should be adaptable to anticipate new technologies yet to come.
Way 19. Classification of certainty of future acts and events
By Wesley Oosting
In this report, I will describe the nineteenth outcome mentioned in the four cycles method – The Classification of certainty of future acts and events [SALM02]. This description will be structured following the tale of the six honest serving-men.
I keep six honest serving-men
They taught me all I knew
Their names are What and Why and When
And How, Where and Who.
( Rudyard Kipling, The Elephant's Child)
(Event Flow Diagrams, Flynn & Jazi, IS Journal, 8,53-83)
What
After the creation of new ideas for future acts and events and putting them on a list (for example with the use of a brainstorm session or a SWOT analysis), the next step is to classify the items on this list. This classification is done based on the (un)certainty and the time scope. This time scope can be divided as is done in goal planning: short-term [0-1 year] (operational goals), intermediate-term [1-2 years] (tactical goals) and long-term [2 years and further] (strategic goals). [DAFT00] The result of this method will be an ordered list of future acts and events with an approximated (un)certainty and time scope.
Why
“Uncertainty means that decision makers do not have sufficient information about environmental factors, and they have difficult time predicting external changes. Uncertainty increases the risk of failures for organizational responses and makes it difficult to compute costs and probabilities associated with decision alternatives.” [DAFT01]
With the indication of this uncertainty, the organization is able to respond better to these uncertainties by changing the need for and creation of the information in the direction needed. “The basic generalization is that only uncertainties about constraints on success matter, and so only information about those constraints on success is crucial to the operation.” [STIN90] The organization is thus able to focus her information strategy in a better way.
By giving the acts and events a time scope, one is able to indicate immediate needs. It is also possible to make a good mix of short-term and long-term projects.
When
“Because the constraints (as mentioned in the previous paragraph) are likely to change over time, the uncertainties that are relevant and the news that resolves those uncertainties are likely to change.” [STIN90]
It is therefore good to update the classification of certainty when new information (news) is conducted. The collection of the new information can be done on a regular based manner with meetings. It is of course also necessary to update the classification when new acts and/or events arise during a new creation-cycle of the list of acts and events.
Within the four cycles method the classification of certainty of future acts and events is placed in the second planning cycle – Alignment of business objectives and information objectives. [SALM02]
How
To make a classification of the (un)certainty of the future acts and events one can use a grading tool. By giving points to indicate the (un)certainty) one can create an order in the list. (For example from 1 [uncertain] to 5 [certain]). This can also be done with the time scopes, which can be categorized in the three scopes.
The classification can be ordered by certainty and by the time scope. The latter is able to present a better quick view of what needs to be attended to next. However, this has the disadvantage of leading to a too much ad hoc view of the acts and events.
Ordering by (un)certainty gives a better view of which events and/or acts need the most attention. This view however, may lead to ‘overlooking’ short-term ‘inferior’ acts or events.
My suggestion is therefore to present the classification in three different categories based on the three time scopes. This gives a better overview of the acts and events that need the most attention. It also enables a better support for a better mix of planning goals.
To come up with uncertainty factors one can use some management literature guidance. Stinchcombe for example identifies four uncertainty sources in the market: (1) unstable markets, (2) unstable specifications of the product, (3) unstable technology and (4) variable raw materials, parts, or environments [Stinchcombe, 1990]. An other source mentioned is cost uncertainty.
Where
The classification of the acts and events has to take place at all management levels. This is mainly because the acts and events vary in goal hierarchy, ranging from operational to strategic goals. It is easy to embed the classification process in the existing meeting structure schedule.
The classification is especially useful in organizations within a complex environment. They need the overview and building-of-knowledge provided with this method to cope with the uncertainties, which are more the case with complexity. The strategic management can be adjusted to the complexity of the environment by for example “Scenario planning” (simple, dynamic) or “Experience and Learning” (complex, dynamic). [JOHN02] [DAFT01]
Who
A group of stakeholders can do the grading process mentioned in the How-paragraph. This gives a good overview and a broader mean of classification. Stakeholders are for instance middle and lower-level managers and project members with ‘inside’-experience and knowledge. This group can join in a meeting with delegates of the information researchers.
The participating stakeholders can all use the method to further specify and qualify the list made with the method of outcome 18 – List of new future acts or events.
Tool 20. List of new project ideas with priorities
By Joost Diepenmaat
This tool describes how a list of new project ideas with priorities should be achieved.
The first step is to derive the relevant questions from the concept of the “six honest men”:
•What is a list of project ideas with priorities?
•Why is this necessary in developing an E-strategy?
•When is a list of new project ideas created?
•How should a list of project ideas be created?
•Where in an organization should this list be created?
•Who should create this list?
The main goal of the tool is: Identifying a strategy to come up with prioritized project ideas efficiently, which present a sophisticated and comprehensive overview to its end users.
The next paragraphs will answer the six questions above in order to fulfill the goal.
What
is a list of project ideas with priorities?
A list of project ideas provides an overview of comparable project properties. It should give enough crucial information to decide why a certain project should be executed or not. Therefore priorities within each project are defined to estimate a possible success factor.
For each project idea the following properties should be covered:
•Description / overview & objectives
•Expected outcome & implications for existing systems
•Involved parties
•Location
•Financials & time (planning) [HUMP97]
•Risks & integration.
Priorities can be defined for each of the properties described, but also on top of the project (e.g. “Project B can only be done when A is finished.”).
Historical information, if available, should not be forgotten in the overview. Project failures or successes from the past bring grounded information [HUMP01].
Why
is this necessary in developing an E-strategy?
People make decisions based on what they know. Therefore it is important to make decisions on the right moment using reliable resources. An overview of project ideas is a very important piece of paper to discuss the future activities of a company.
When
is a list of project ideas created?
A list of project ideas should be created as soon as possible. A modern company should be able to change its company goals quickly. Together with this, a list of project ideas should be kept up to date continuously.
You would rather have too many ideas than having none of them. Therefore getting “brilliant ideas” from your employees is also an important continuous process.
Where
in an organization should this list be created?
The most important issue is to gather enough information through the whole organization. Hence, visions from all involved parties (including employees and customers, etc.) should be formalized into the document.
How
should a list of project ideas be created?
It is important to collect all project ideas from internal and external resources and finally come up with a prioritized list of ideas to discuss and take decisions. Therefore a number of actions should be taken:
1.Collect as many project ideas as you can via different channels and define them.
2.For each defined project analyze the following properties:
a.Description / overview & objectives
b.Expected outcome & implications for existing systems
c.Involved parties
d.Location
e.Financials & time (planning)
f.Risks & integration.
Give measurable scores to each of these properties
3.Make project decisions.
Who
should create this list?
Any non-independent party should create this list after he gathered sufficient information. From a business perspective the decision takers should only deliver proposals which are analyzed by the party formulating the idea list. By doing interviews it should be clear.
What?
This tool documents the shared vision between senior managers of the organisation in which direction information systems should go. Clear priority decisions are made by senior management and information management on which objectives and which ideas priority is given. [SALM02]
Given the description above, two consecutive steps can be deducted. The first one is to document the shared vision of the senior management.The second step is that, from this shared vision, senior management has to determine which objectives and which ideas are the most important for the realization of the shared vision.
Why?
There are several reason why the IS plan and the project priorities should be aligned. For example, the determination of the shared vision supporting objectives, allows the decision makers to identify and invest in projects which actually support these objectives. Furthermore, by doing this, resources can be allocated more efficiently, where it matters for the organization.
Another reason is that documenting the shared vision aids in getting senior management on the same page. This increases the chance of a project being completed successfully. In [HOFF02] it is stated, that one of the possible fail factors for a project is lack of support from senior management, for example because they themselves do not believe in the project. But if senior management understands that a certain project complements the shared vision of the company, they’ll probably want it to succeed and therefore support it.
When?
In [SALM02] it is discussed, that the alignment of IS plan and the project priorities should be performed at the end of the second cycle of the Four cycles method. This is a good point, as there are several pieces of information (such as the business strategy) which have to be gathered first, before any sensible alignment and prioritizing can take place.
How?
As stated in the first section of this tool description, two steps have to be performed in order to align the IS plan and determine the objectives and ideas which need to be given priority. The first one is to document the shared vision of the senior managers.
Documenting the shared vision
In [COLL96] it is stated that the shared vision consists of three basic elements:
1.an organization's fundamental reason for existence beyond just making money (often called its mission or purpose),
2.its timeless unchanging core values,
3.huge and audacious -but ultimately achievable- aspirations for its own future.
According to [WARD02], the Information Strategy should support the Business Strategy. As such the information systems used in the organisation should support the fulfilment of the shared vision by the senior management.
Thus the elements from [COLL96] are to be defined with regard to the information systems need. It should be made clear in which way the information systems should go, in order to support the Business Strategy, as stated in [WARD02].
Several techniques exist in order to define the three elements from [COLL96], such as mind mapping. The senior management note down their ideas about the three elements and rate each idea. The best ideas for each element are then collected and form the shared vision.
Setting priorities
The second step is the determination of the priorities. Thus senior management has to decide which objectives and ideas will aid the most in realizing the shared vision.
Objectives and ideas are defined throughout the first and second cycle of the Four Cycle method from [SALM02]. Several tools are mentioned in [SALM02] that can help in defining the objectives and ideas, for example tool 20 “List of new project ideas with priorities” or 18 “List of new future acts or events”.
By using these tools to generate several possible objectives and ideas, senior management can decide on basis of the previous step, which objectives and ideas will aid most in achieving the goals of the information strategy.
This way the projects, that will achieve the desired objectives and ideas, can be given priority.
Where?
The location where the alignment process takes place is not of importance. On the other hand, the room where this process takes place is. As such the atmosphere should be relaxed and inspiring to work in.
Since the shared vision is something which might need to be kept a secret for the outside world, it might be advisable to perform this tool within the organisation.
Who?
The people who should be involved in the alignment process consist of the senior management, but also a secretary to write down the results of this tool as well as documenting the process.
Alternatively, senior management might opt for a fresh view on the shared vision and have other people, like middle/lower management, discuss about the results of this tool.
In [LAUD00] it is discussed that employees in different layers of the organisations hierarchy have different needs of information. For example Executive Support Systems vs Transaction Processing Systems.
Thus by involving other employees, new insights might be detected which might aid in a better Information Strategy plan. It also has the benefit of improving the overall employee understanding and support of the shared vision, as they are more involved. [HOFF02]
Way 22. Senior Management Participation
By Niels Höfte
The first step in this assignment is to derive the relevant questions from the concept of the “six honest men”, the questions I derived from the concept are summarized, in non-sequential order, below.
•What does “Senior Management Participation” mean?
•Why is this necessary in developing an E-Strategy?
•When do we use it or when is it relevant to use it?
•How can we implement the principle “Senior Management Participation”?
•Where do we use the principle, in which context?
•Who are involved in “Senior Management Participation”?
Each of the questions mentioned above, except the “Where” question, form a separate part of this assignment and is divided in separate paragraphs. The question “Where do we use the principle, in which context” will be explained in a general sense in the whole assignment.
What does “Senior Management Participation” mean?
Senior Management Participation is an outcome of the second cycle of the “four cycle method”. The emphasis in this second cycle is on identifying future IS projects that provide business value and support both business strategy and business processes [SALM02]. Participation of the senior management means that the relevant managers for the specific case (University) are actively involved in aligning the business objectives and the information objectives. It also means that the senior management supports the project unconditionally. This support from the senior management initiates trust in the rest of the organization.
Why is this necessary in developing an E-Strategy?
In “The impact of organizational commitment, senior management involvement, and team involvement on strategic information systems planning” Basu et al. describe how they conducted a postal survey that produced usable data from 105 corporate information systems [BAS02]. In their article they describe their research and that it supports their hypothesis that senior management involvement predicts the achievement of SISP (Strategic Information Systems Planning) objectives. Before and during the development of an E-strategy, the senior management creates the margins for the project. They set boundaries in which E-strategy can be developed. Senior management can provide feedback and guidance throughout the project.
When do we use it or when is it relevant to use it?
Senior management participation is a very important issue in developing an E-strategy. Because senior managers are very busy people, senior management participation should only be used when there are no other layers of management that have the same responsibilities and authorisations as the senior management. It is very hard to get senior management involved in the development of an E-strategy because it is an unknown territory for them.
How can we implement the principle of “Senior Management Participation”?
To implement the principle of senior management participation we have to commit the management to the development process of the e-strategy. This commitment can be realized trough several concepts. I derived these concepts from an article by Prof. Dr. Ir. D.R. Muntslag; “The Art of Implementation” [MUNT01]. I believe that the concepts described in this article can also be applied in the case of developing an E-strategy. Each of the concepts is clarified below.
Structured meetings
Frequent evaluation sessions of the development process will sharpen the participation of the senior management. Especially when, during these meetings, some serious decisions concerning the senior management are being addressed.
Provoke confrontations
During evaluation meetings, each stakeholder present might have a different opinion about a certain proposal [MCC81}. Provoking the senior management forces them to get into a discussion with you about the proposal, which in turn reinforces the participation of the senior management.
Retain informal contact
Informal contacts such as personal phone calls, diner parties or “corridor meetings” can play an important role in getting the senior management to participate.
Communication about the development process
A real efficient way to get the participation of senior management is to confront them directly with the results of the development process. When the developer illustrates a new E-strategy he can intensify the concepts of the new strategy with concrete examples.
Who are involved in “Senior Management Participation”?
In his article “Stakeholders in Strategic Information Systems Planning” Ruohonen defines three main groups of stakeholders involved with strategic information systems planning (SISP) [RUO92]. These groups will also be involved in the concept of Senior Management Participation:
•Top Management groups
•IT/IS Management Groups
•User Management Groups
Top Management is the senior management that is responsible for business management and top-level decision making. Their experience in IS is usually limited.
IT/IS Management is the management responsible for the information processing and information services departments.
User Management is the management that is responsible for separate business units. They must report to higher level management (i.e. Top Management).
Management education is needed to integrate the different views of managers concerning the use of IT. Successful SISP requires clear communication and interpretation of these views.
References
[AVIS98] Avison, D.E., Eardley, W.A. & Powell, P. (1998). “Suggestions for capturing corporate vision in strategic information systems”. Omega, 26, 443-459
[BARN03] Barnes, D. et all (2003), “Integrating Operations and Information Strategy in e-Business”. European Management Journal Vol. 21, No. 5, pp. 626–634, 2003.
[BIZZ03] Bizzdesign (2003), Bizzdesigner,
http://www.bizzdesign.nl/bizzdesigner/bizzdesigner.html
[BUCH 98] Buchanan, S. & Gibb, F. (1998). The information audit: An integrated
approach. International Journal of Information Management, 18(1): 29-47.
[COLL96] Collins, J. (1996) “Aligning Actions and Values”; Leader to Leader / The Drucker Foundation; Summer (no. 1).
[COLL99] Collet, S. (1999). “SWOT Analysis”. Computerworld, 33(29), 58
[DAFT00] Daft, R.L. (2000). “New Leadership for Learning Organization” Management. Fifth Edition. The Dryden Press, Hartcourt College Publishers, Orlando.
[DAFT01] Daft, R.L. (2001). Organization Theory and Design. Seventh Edition. South-Western College Publishing, Thomson Learning.
[DOLA01] Dolak, D. (2001); “Creating and Communicating Vision: The Business Leader's Primary Responsibility”; PCM.
[DOOL02] Dool, F. van den, Keller, W.J., Wagenaar, R., & Hinfelaar, J.A.F. (2002). “Architectuur elektronische overheid, Samenhang en Samenwerking”. Verdonck Klooster & Assciates ICT consultants.
[EARL88] Earl,M. J. (1988). “Formulation of information systems strategies: Emerging lessons and frameworks”. In M. Earl (Ed.), “Information management: The strategic dimension”. Oxford: Clarendon Press.
[EARL 89] Earl, M.J., Management Strategies for Information Technology. Prentice-Hall, London, 1989.
[GALL 91] Galliers, R.D., 1991, Strategic information systems planning: myths reality and guidelines for successful implementation. European Journal of Information Systems, 1, 55-64
[HEND88] Henderson J.C., & Sifonis, J.G. (1988). „The value of strategic IS Planning: understanding consistency, validity and IS markets”. MIS Quarterly, 12(2), 187-200
[HOFF02] Hoffer, Jeffrey A., George, Joey F., & Valacich Joseph S. (2002). “Modern Systems Analysis and Design” (3rd ed). Prentice Hall.
[JOHN02] Johnson, G. & Scholes, K. (2002). “Exploring Corporate Strategy”. Sixth Edition. Prentice Hall, Pearson Education, Edinburgh Gate, Harlow, England.
[KIPL42] Kipling R. (1942), “The Elephant's child”, Garden City, N.Y,.
[LETH01] Lethbridge, T.C., & Laganière, R. (2001). “Object Oriented Software Engineering”, McGraw-Hill
[LIMB02] Limburg, D. O., & Goslinga, H. P. (2002) “Dictaat ‘Bedrijfsprocessen laboratorium’”. Universiteit Twente. 11-34
[MCC81] J. McCann, J.R. Galbraith; Interdepartmental relations; in: Handbook of
Organizational Design, P.C. Nystrom, W.H. Starbuck; vol. 2, Oxford
University Press, New York, 1981.
[MCGE89] J. McGee & H. Thomas, (1986), “Strategic groups: theory, research and taxonomy”, Strategic Management Journal, vol. 7, no. 2
[MUNT01] Muntslag, D.R. (2001). “The Art of implementation”. Inaugural lecture. Chair in ERP Implementation and Organizational Change at the UIniversity of Twente
[OZ01] Oz, E. (2001). “Management Information Systems”, 3rd edition. Thomson Learning
[PORT80a] M.E. Porter, 1980 a, “Competitive Strategy: Techniques for Analyzing Industries and Competitors”, Free Press
[PORT80b] M.E.Porter, 1980 b, “Competitive Strategy”, Free Press
[RUOH91] Ruohonen, M. (1991). “Stakeholders of strategic information systems planning: theoretical concepts and empirical examples”. Journal of Strategic Information Systems, 1 (1), pp. 15-28.
[SALM02] Samela, H., & Spil, T.A.M. (2002). “Dynamic and emergent information systems strategy formulation and implementation”. International Journal of Information Management 22(6), 441-460.
[STIN90] Stinchcombe, A.L. (1990). “Information and Organizations”. University of California Press, Oxford England.
[TEOA01] Teo R. Ang J (2003), “An examination of major IS planning problems”, IT management (select), ISSN 1383-9667, vol. 9 (2003), afl. 3, pag. 58-69 (12), 2003
[WALT03] Walters, Bruce A. et all (2003), “Strategic information and strategic decision making: the EIS/CEO interface in smaller manufacturing companies”. Information & Management Vol. 40, pp. 487–495.
[WARD96] Ward, J., & Griffith, P. (1996). “Strategic planning for information systems” (2nd ed). Chichester: Wiley.
[WARD05] Ward, D. and Rivani, E. An Overview of Strategy Development Models
and the Ward-Rivani Model. 2005
[WEIS04] Weiss, J.W. Anderson, D. (2004); “Aligning Technology and Business Strategy: Issues & Frameworks”, A Field Study of 15 Companies.
Planning the IS/IT infrastructure | ||
#23 p 103 | Identification of core business areas | The identification of the core business areas elaborates earlier analysis of core business processes (outcome #17) with the analysis of the degree to which a competence is significant in terms of access to wider markets, customer significance, and risk of imitation. |
#24 P 104 | IS support for core business areas | Describes for each core area why it is important and how each area are composed (results of the noun/verb analysis). Illustrates supportive IS functions (results of the functional analysis systems technique diagrams). |
#25 P 106 | IS needs | Describes the information needs, conceptual information systems, the business conclusions and recommendations, the application portfolio and the business information models. |
#26 P 114 | Information technology developments | Identifies most relevant IT developments from the business perspective. Reviews the latest publications in IT and describes shortly a reference list to access more information (most likely hyperlinks). |
#27 118 | Technology assimilation plan | Defines a timetable for adopting the most promising technologies, given the current technology and IT heritage of the organisation. |
#28 121 | Future | Management and control description of the future data, application, computing and communication infrastructure. |
Planning the IS organisation | ||
#29 P 123 | Strategy and structure of the IT function | Contains a decision on the location of the responsibility, authority and activities of information management either centralised, distributed or decentralised. |
#30 P 129 | Rules and regulations for the IT function | Describes general rules as well as quality and service levels for all services provided by the information management function. These agreements can be matched with financial agreements between the IT function and users. |
Evaluating the IS/IT development portfolio | ||
#31 P 133 | Current investments and costs | Provides a clear picture of the current financial situation of all IS cost centers with given budget and used budget. Provides a long term prognosis of project budgets in major on-going IS/IT projects. |
#32 138 | Future investment possibilities | Describes the future capabilities of the IS function to initiate new projects and to maintain high quality in the provided services. |
#33 142 | IS future benefits | Defines the overall quantitative and qualitative benefits that the IS/IT project portfolio can leverage. |
#34 144 | Proposed IS/IT project portfolio | Describes the proposal for the IS/IT portfolio and documents other important outcomes the scenario analysis process. |
Way 23. Identification of core business areas
The four cycles method [Salmela & Spil] aims to prevent the disadvantages that rise from using the comprehensive and incremental planning methods. The method combines elements of both comprehensive as well as incremental methods in order to reach a combined approach. The method consists of four cycles that are repeated periodically. The following cycles are defined:
1.Agreeing on planning objectives.
2.Aligning business objectives and information objectives
3.Analysing IS resources and IT infrastructure
4.Authorising actions.
As part of carrying out these cycles several outcomes may be created. In this document outcome 23, “identification of core business areas”, that is part of the third cycle, “Analysing IS resources and IT infrastructure”, will be explained closer.
In the third cycle a plan for the ICT infrastructure and organisation is made as is a preliminary project portfolio of projects that are intended to support the business processes of the organisation. These plans are based on information gathered from previous phases. Outcome 23 is described as follows:
Identification of core business areas
“The identification of the core business areas elaborates earlier analysis of core business processes (outcome 17) with the analysis of the degree to which a competence is significant in terms of access to wider markets, customer significance, and risk of imitation.” (Salmela & Spil, 2002)”
This outcome builds upon results from outcome 17 which is described as follows:
Implications of other business analyses for IS
Identifies critical processes in the organisation (core competencies) to be supported by information systems. Combines and groups the critical success factors with the strengths, weaknesses, opportunities and threats to derive information objectives.” (Salmela & Spil, 2002)
The intention of outcome 17 is to map what processes are the most important in the organisation. A situation analysis is performed to identify SWOT (Strengths, Weaknesses, Opportunities, Threats) and CSF (Critical Success Factors) so that new strategy may be developed. [Daft, p. 245]
Outcome 23 is a logical continuation on outcome 17 and builds upon the analyses from outcome 17 to determine which business areas are suitable for expansion and for creating a competitive advantage.
Based on the analysis in outcome 23 it can be determined in outcomes 24 up to and including 28 what the information systems and future infrastructure needs will be. Later in the third cycle this will lead to a portfolio of new IS project plans.
In order to identify the core business areas a competitive forces analysis can be carried out. [Daft, 249] This analysis might be combined with a PEST analysis for more complete results.
Strategy can be divided in three layers: Corporate-level, business-level and functional-level (see also figure 1). It is off course of utmost importance that top management and information management agree on the results of the business analyses carried out in outcome 23. Ideally the people working on the business-level strategy cooperate with the people working on the information (functional level) strategy to carry out the business analyses so that congruence between the levels is achieved.
One might say that the analysis of core business areas in itself is not really related to the IS/IT infrastructure as it is more related to the charting of the business side of things. This outcome connects closely to the outcomes and objectives – namely the conducting of business analyses – of the second cycle. Therefore one might say that this outcome might take place in the second cycle instead of the third cycle.
Either way this analysis of core business areas forms a bridge between the second and the third cycle so that business analyses can be converted into plans.
Introduction
This paper describes the outcome IS Support for core business areas as mentioned in the four cycles method (Salmela and Spil, 2002). This outcome is part of the third cycle, analysing, and concerns the planning the IS/IT infrastructure part. The definition of this outcome (nr. 24) is as stated as follows: “describes for each core area why it is important and how each area is composed (result of the noun/verb analysis). Illustrates supportive IS functions (results of the functional analysis system technique diagrams).” From this definition the outcome can be decomposed in two major parts:
1.Relevance and composition of the core business areas.
2.Supportive IS functions.
These two issues will be covered in this paper in relation to Strategic Information Systems Planning (SISP). For both issues the six honest man (Kipling, 1998) will be used to provide a complete overview. These include: what, why, when, how, where and who.
Relevance and composition of the core business areas
This issue relies on previous steps in the four cycles method. Outcome 17 provides an elaboration of core competencies that need to be supported by the IS. Based on this outcome 23 identifies the core business processes. This issue tries to add the relevance of these business areas, followed by their composition.
In a recent study Peppard (2004) has developed a framework consisting of six domains of core competencies. The second domain is relevant for this issue:
Define the IS contribution (IS strategy):
•Prioritization | Ensure that the portfolio of investment in applications and technology produce the maximum return from resources available. |
•IS strategy alignment | Ensure that IS development plans are integrated with organisational and functional strategic plans. |
•Business process design | Determine how IS can deliver ‘best practice’ in operational processes and organisational activities. |
•Business performance improvement | Identify the knowledge and information needed to deliver strategic objectives through improved. |
•Systems and process innovation | Carry out relevant R&D into how IS/IT can be used to create new ways of conducting business and new products and/or services. |
The creation of a business model is a difficult task, because everybody has a different viewpoint. Business processes and functions can be modelled by using static data modelling (e.g. DFD, SADT, ERD, IDREF-0, etc.) and dynamic behavioural modelling (e.g. STD, Petri nets, RAD, Activity Diagram, QFD, ARIS, etc.) (Mentzas, 1999).
Supportive IS functions
Based on the previous information it is necessary to identify the IS functions that supports the core business processes. There are numerous techniques available to do the functional analysis that is necessary to match the IS functions with the business processes. The techniques mentioned in the prior issue can also be applied for this. The relationship between software process modeling (IT) and business process modeling (IS) has been examined by Warboys (1994).
Information technology itself as no inherent value and it can not be a source of sustainable competitive advantage. The business value derived from IT investments only emerges through business innovation, new business models, or process change. Thus, IS/IT itself do not create value, but value is created by the organisation’s ability (core competences) to utilize and mobilize the IS/IT (Peppard, 2004). To continue the framework of Peppard (2004) the third domain concerns:
Define the IT capability (IT strategy):
•Infrastructure development | Define and design information, application and technology architectures and organisation structures and processes to manage the resources. |
•Technology analysis | Understand technology trends and make appropriate recommendations for organisational acquisition of technology and associated resources. |
•Sourcing strategies | Establish criteria and processes to evaluate supply options and contracts with suppliers |
Peppard has also proposed the so called fourth era, which he defined as: “the organisation’s performance will be significantly dependent on its IS capability”. The previous era is focussing on developing an IS strategy, which identified the most beneficial set of IS/IT investments in order to support business objectives and take advantage of new IT opportunities. The fourth expands this view by adding the idea that with a strong IS capability, IT opportunities will be incorporated in the business strategy.
Conclusion
After these descriptions about the outcome IS Support for core business areas as, I will try to provide an overview by using the six honest men, as mentioned in the introduction.
Relevance and composition of core business areas | Supportive IS functions | |
What | Business processes | IS functions |
Why | Align the IS/IT with the business processes (fourth era) | |
When | After core competencies and core business processes are defined | |
How | IS strategy | IT strategy |
Where | Internal | |
Who | (Middle) managers | IT managers |
I will conclude this paper with the following statement of Ciborra (1994): “successful applications of IT are often due more to serendipity rather than to any formal planning process.”
What?
The third planning cycle from the four cycles method is the part of analysing IS resources and IT infrastructure. The third cycle adds realism to planning by bringing in resource capacities and constraints under which the IS function operates. A concrete objective is to develop a preliminary project portfolio that includes both IS development project and projects for improving the ICT infrastructure. I will describe outcome 25 witch include IS needs.
The output of this is to describe the information needs, conceptual information systems, the business conclusions and recommendations, the application portfolio and the business information models. I will focus on the search of information needs because I think this is de most important outcome. The other outcome depend on the result you get from identify the information needs.
Why?
A careful identification, analysis and classification of information needs of users (including all potential users and non users as well) are an essential basis for the planning, implementation and operation of information systems. In fact, any lapse in proper identification of information needs will affect the efficiency and effectiveness of information systems and services. The turbulent and changing information environment calls for continual research to ensure that the needs of the information users are satisfactorily met and that the information professionals acquire the required expertise to cope with the operational management of the information resources and plan for the future.
How?
It has been found to be a difficult task as it is almost an investigative or detective work. Information need is a subjective, relative concept only in the mind of the experiencing individual1. It has been defined as the ''recognition of the existence of uncertainty'' 2. In order to identify information needs one should adopt various methods to gather information on the various factors that influence the information needs. No single method or tool will serve entirely. A careful selection and blending of several techniques depending on the user whose need is being studied is necessary3. In day to day work, lack of self sufficiency constitutes information needs. These information needs represent gaps in the current knowledge of the user. Apart from the expressed or articulated needs, there are unexpressed needs which the user is aware of but does not like to express. The third category of need is the delitescent or dormant need which the user is unaware of. A need is specific and generally time bound either immediate or deferred. The information provided for a need will be used. In the case of interest, the information provided may be used or may not be used. According to Crawford4, information needs depend on: Work activity, discipline/ field / area of interest, availability of facilities, hierarchical position of individuals, motivation factors for information needs, need to take decision, need to seek new ideas, need to validate the correct ones, need to make professional contributions, need to establish priority for discovery etc. Also information needs are affected by a variety of factors such as the range of information sources available and the uses to which the information will be put.Information needs identification is a complex process. Some of the factors adding to the complexity are:
•Same information is perceived by different users differently as their information need. (Value system of users differ due to the nature of work and it affects factors such as the information products and services).
•Researchers need original documents whereas planners need digests of `point of view ' / opinions);
•Information is put to different uses (R & D personnel, Application developers and Technicians all put information to different uses);
•Need is satisfied by having access to the identified information in a particular package and form, and at a suitable time;
•The flow of information and channels of communication are complex and add to the complexity; and
•Individual preferences and behavioural aspects add a further dimension.
The major steps in the process of identifying information needs:
1.Study of subject(s) of interest to the organisation/ User(s
2.Study of the organisation and its environment
3.Study of the immediate environment of the User(s)
4.Study of the User(s)
5.Formal interview
6.Identification and recording of information needs
7.Analysis and refinement of the identified information needs.
The picture on the next page is from F.J. Devadason, it is a method that consist of several studies (see reference section) that made on this subject. The outcome must provide information about the organization IS-needs, but also the organization itself must be clear, so you can get the right relevant information from the different stakeholders. So you can get a clear picture of the organizations information needs and so the IS needs.
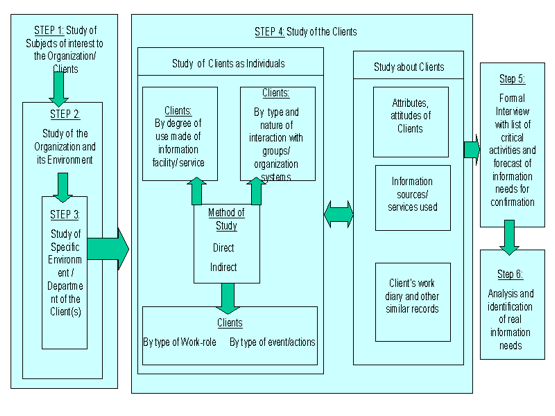
When?
According the four-cycle method is it after the first two cycles, thus after agreeing on planning objectives and stakeholders and the alignment of business objectives and information objectives. The third planning cycle forms three main tasks, planning the IS/IT infrastructure includes the tool information needs. The four-cycle method is an iterative process. The information needs will shift, because of the rapid changing environment. Thus it is important to use this tool several repeatedly, so you get a realistic up to date view of the information needs.
Who?
I think this is a good job for the information managers; they have a good insight in the organization. They know a lot of the information processes within the organization. The managers must interview the important stakeholders so they can get a clear picture of the organization information needs. An important stakeholder is for example the end-user.
Where?
The information needed for this tool you can find it mostly in the organization herself. The interviews with the stakeholder can also take place in the building of the company. But is not strictly, in principles you can get this information from every physical place.
Addition IS Needs
Brief introduction
The missing tool we’d like to introduce into the ‘four cycles method’ is called BSP (Business System Planning). This methodology, is developed by IBM and has a very unique feature: it combines top down planning with bottom up implementation. The methodology focuses on business processes which are derived from an organizations business mission, objectives and goals. The business processes are analyzed to determine data needs and then data classes. Data classes that are similar are combined to develop databases. The final result describes an overall information systems architecture as well as an installation schedule of individual systems ([Pan95]).
Placement in four cycles method
The BSP method is a complete methodology, so it cannot be placed as a whole in a stage of the four cycles method. We suggest using BSP in stage 25 (‘IS Needs’).
BSP can derive business processes from the organizations mission, but as that is already done in the four cycles method in stage 17 and 23, this part of BSP will not be added to the four cycles method. The determination of data needs and data classes from the business processes is, in our opinion, a useful addition to stage 25, IS Needs, of the four cycles method.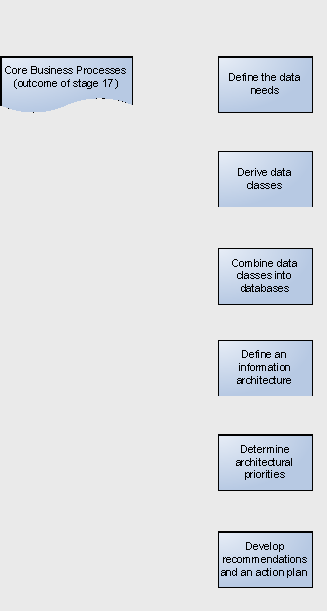
Adapted BSP
The part of BSP we suggest in addition to stage 25 of the four cycles method will be called aBSP (adapted BSP). The steps in the process of aBSP are depicted in figure 1, which has been edited from [Pan95]. The process starts with defining the data needs, the results of stage 17 are used as input. From the data needs, data classes are derived, which can be combined into databases. From that a information architecture is created, including priorities. The process results in a list of recommendations and an action plan.
Strength and weaknesses of aBSP
According to [Pan95] BSP has the following strength and weaknesses:![]()
“Strengths: Because BSP combines a top down business analysis approach with a bottom up implementation strategy, it represents an integrated methodology. In its top down strategy, BSP is similar to CSF method in that it develops an overall understanding of business plans and supporting IS needs through joint discussions. IBM being the vendor of this methodology, it has the advantage of being better known to the top management than other methodologies.
Weaknesses:
(a) BSP requires a firm commitment from the top management and their substantial involvement.
(b) it requires a high degree of IT experience within the BSP planning team.
(c) it does not incorporate a software design methodology.
(d) major weakness of BSP is the considerable time and effort required for its successful implementation.“ [Pan95]
Most of the strength and weaknesses are valid for aBSP too. Of course, IBM isn’t the vendor of aBSP, so aBSP hasn’t got the advantage of being better known to the top management than other methodologies like BSP has.
One could argue that the other important strength of BSP (combining top down business analysis approach with a bottom up implementation strategy) isn’t valid for aBSP. That’s true for aBSP alone, but that’s because aBSP is meant for implementation in the four cycles method. The combination of aBSP and the four cycles method creates a extended four cycles method which combines top down business analyses (from the four cycles method) with a bottom up view (from aBSP). One of the weaknesses of aBSP is not valid in this situation; namely weakness (c). When aBSP is used in the four cycles method it doesn’t matter aBSP doesn’t incorporate a software design methodology.
What does aBSP add?
Adding aBSP to the four cycles method has a big advantage. In general a bottom up input is added to the four cycles method. This added view of the organization ensures more complete information on the processes in the organization and thereby ensures that the IS which, in the long run, is the result of the planning process executed fits the processes better. In other words, the resulting IS will be more adopted to the real information needs in the business processes, because of the bottom up input, which sometimes conflicts with the top down view of the process.
Conclusions
We suggest adding aBSP to stage 25 of the four cycles method, so a bottom up input is added to the four cycles method. This ensures a better adaptation of the resulting IS to the business processes.
Testing the Usability
Testing the usability of this model will happen according to a case which suits the charasteristics to test this tool. I found a suitable case about a CRM system to be reconfigured at a technologically advanced company, called i-flex.
Case study.
i-flex solutions is a company specialized in IT solutions for the banking sector. Due to the shift within i-flex to a more marketing oriented organization and the changes in the global market, i-flex needs to have a stronger Sales support Information System.
i-flex solutions has already implemented a PeopleSoft CRM system to support Sales and Project Delivery, but this system is not configured optimally. The system needs to be updated with more analyzing and reporting tools and it needs a more complete database content to give true added value to the users.
The information requirements were never mentioned or questioned before, which caused a gap between the actual possibilities and the required functionality.
Next to these information requirements, the system had to fit other requirements as well. Although these requirements were not explicitly mentioned, they were restrictions which the system had to be adjusted to. Examples are the technical possibilities, the authorization levels of different users and the fact that PeopleSoft could not be replaced.
The IS team of i-flex was updated with the new information concerning the requirements of the users and have taken this further as the system is in a continuous process of learning.
Applying Tool on Case study.
Step 1: Study of subjects of interest to the Organization / Clients.
By nature of the physical and organizational distance between the end-users and the IT support team of the CRM system, this may well seem a very useful.
Tier 1 banks, which are very big and complex banks, are very interesting for the organization and the users. The users of the system will be discussed later, but we may assume that they are Sales representatives.
Furthermore, Pipeline Analysis, Customer Analysis, Instant Product Information and Leads and Opportunity Management are all very interesting subjects in the daily Sales processes.
Step 2: Study of the Organization and its Environment.
i-flex solutions is a software developing organization, but is shifting to a more marketing oriented organization. It has about 3500 employees and is therefore relatively big in its market. It has a few other big competitor and a lot of much smaller competitors. In this sector, alliances with other companies are not only very common, but also an essential issue to survive. Alliances are for example Oracle and Real Software.
i-flex services primarily banks, but also large insurance institutions, governmental instutions and financial ministries. Most of the customers are large and have also large budgets.
Step 3: Study of specific Environment / Department of the Clients.
The market, which typically consists of companies with larger budgets, are extremely suitable for a Sales strategy called hybrid marketing. This strategy contain the cross-selling and upselling strategies. Cross selling is selling more different products to a customer whereas upselling means selling more of the same product at a customer. The users of the PeopleSoft CRM system are one of the few Sales representatives in Europe. The organization is for the greater part an Indian organization. In Europe, we see a growth of Banks in the Eastern part since most of the Eastern European countries join the EU and face a rapid growth in income.
Step 4: Study of the Clients.
Attributes / attitudes: The users of PeopleSoft are all very high educated persons and have a successful career until now. They are contented with working for an Indian company. In the European office, they generally state that European people can work more independent than Indian people. This is many times countered by the upper management, which is also from Indian origine. Sometimes this conflicts.
Sales has regular contact with high management of their customers, because the amounts of money involved in such projects are very large. Therefore, the Sales employees are well equipped and can afford to make appointments on the behalf of i-flex.
Information sources / services: The users do not have a single source for information. The information sources even change over time and this can change very quickly. Most information is retrieved from internet. This can be sites of the customers, dedicated leads exchaning sites, financial company databases etc. Other necessary information is product information. This information comes from Marketing, Development and the management.
Work diary / other records: The diary is very busy and contains a lot of appointments with customers and prospects. Employees are working outside the office and office hours a lot. The diary is placed on computer and online, which makes it possible for others to exchange appointments easier. Other records are not relevant for so far.
As individuals, by degree of use made of information facility / service: As individuals has been done already. Also, the degree of use made of informaiton facility / service is mentioned earlier.
By type and nature of interaction with groups / organization systems: The nature of interaction from the Sales users with groups has also been mentioned before. Groups of interaction are project delivery, upper management, customers, other sales teams, etc.
Method of study: The study of the users which made it possible to retrieve the above mentioned information is mainly from interviews. Another part is retrieved from business documents.
Step 5: Formal interview with list of critical activities / forecast information needs for confirmation.
This step needs not te be done anymore. The list of critical activities has been set up with the help of interviews. Interviewing the users again to confirm the information may be good to assure the correctness, but this takes time which most users commonly do not have. A confirmation from upper management would be useful, but the question arises how much knowledge they have of the business of Sales.
Step 6: Analysis and identification of real information needs.
The Sales users want to have faster access to critical information. This information is currently not placed together which makes searching for it unnecessary long. Further, much information is present, but can not be analyzed. Searching for example for all customers which have bought Flexcube is not possible or very complex. Reporting tools are also desired, because reports strongly support the statements of Sales employees. Of course, we should not forget the general information needs. These are customer address, telephone, e-mail, but also budget, decision makers and influencers as well as operating platform, present competitor software etc. Also, information about competitor and alliance software is required.
Conclusion about Usability.
In general, the tool is very useful. Step 4 however, is unnecessary confusing while not being an important step. Step 5 is not very clear. Why should there be a formal interview to confirm the list of critical activities? Of course you can say it is good to check or to get this list, but the information is already obtained during the predecessing steps. How the information is obtained is not fixed, but this leaves some room for creativity.
There is a somewhat greater doubt about this tool for translation from IS needs to system functionality. It is not easy and there is no standard procedure for translating business functions and - processes into system functionality and - tools. The tool leaves the gap open and makes itself vulnerable to questions on the translation.
For some processes, we can translate business activities 1 to 1 in system activities. For a Sales department, as we have taken into account, or for Customer Relationship Management, this is not true. We can see several reasons. The first and most important is Sales not being a predefined task. Its processes are different every time a new event occurs and each problem should be tackled differently.
Other reasons are Sales department needing to work with outside parties, which activities can not be predicted. Therefore, and I think this is a very important conclusion here, is that tools in a system for analysis can have much more added value to a Sales department than a tool which has a translation of the ‘standard’ processes.
I believe the tool can work perfectly to get to IS needs. Although I tested it on a Sales environment, where it is very difficult to come up with the exact needs, it still delivered a very good output. The tool summarizes the whole process of finding the information requirements.
Introduction
In the document of Salmela & Spil [SALSPI] the tool description of tool number 26 (Information technology developments) is:
“Identifies most relevant IT developments from the business perspective. Reviews publications in IT and describes a reference list to access more information (most likely hyperlinks).”
This description is very short and only tells what the outcome is. In this article I will try to outline the tool in more detail. This will be done with answering the questions what, why, when, where, who and how.
What should be identified as possible and usable IT developments and trends?
This tool tries to identify new developments en trends in the IT fields that could be used. It is important to look at IT developments and trends that are usable from the business perspective, so it should have a big, strategic value for the organization (for example a new enterprise system). With this IT development or trend the organization should achieve a strategic goal (and probably use it to gain more profit).
Why should we need IT developments and trends?
New IT development and trends are in important for five reasons:
•It is a trend
Companies are very sensible for trends and so are its employees. When something is done in allot of other organizations (it doesn’t matter with one), all organizations need to have or use it (for example wireless LAN is very hot at the moment).
•The competition has or uses it
When competitors are using the new IT developments and gain advantage, other organizations can’t stay behind. Not using the new development could result in losing market share and ultimately going bankrupt.
•Stay ahead of the competition
Another reason could be to use the new IT developments to gain more market share by introducing this new IT development before the competitors can. Competitors need to react on this IT development or they lose market share.
•Streamlining the organization
Sometimes IT developments (like Enterprise systems) could optimize the organization. This could result in cost reductions or more efficient working methods.
•Beginning a new business form
The last reason is to step into a new market or expanding the current one (like some bookstores did with the introduction of online stores).
When should be looked at IT developments and Trends?
The process of scanning for IT developments and trends isn’t a one time action. It should be continuously progress. IT developments and trends appear and disappear sometimes in a short time (example the millennium bug was a hot business, but short one). So it is imperative that there is a constant monitor on IT developments and trends. But when an strategy is made it needs to know what IT developments and trends are active so at that moment there should be a scan in all resources to find these IT developments and trends.
Where could these IT developments and trends be found?
There are three important sources to get information about IT developments and trends:
•The internet;
At this moment there is the internet the biggest information resource available. On the internet there are newsgroups and websites where new IT developments and trends are discussed or ‘sold’.
•Magazines;
Other important resources are magazines witch are still important information medium. The advantage of magazines is that there is already a selection made of the usable information so the search is much easier. The problem is that the competition also see this information quit easily.
•Congresses and conventions
The last important resource is conventions and congresses, where companies show their new IT developments and trends.
Who should gather this information about IT developments and trends?
Most of the time the IT department knows a lot of IT developments and trends, because it is in their work field. It is also their job to report these things to their supervisor or management. Although the IT department knows about new IT developments and trends, they are not really scanning all resources (like visiting congresses), so the IT manager, or another person of the IT department need to do this. It wouldn’t be a full time job that’s why there is no need for a fully dedicated person, but he needs to know a lot of the field of business the organization is in and tends to go to.
How are most relevant IT developments identified? (changed question)
The first step is to change the culture of the company to make all the people conscious about the importance of new IT developments. This is of course easier said than done. The focus of everyone is better than only a focus of the higher management. The culture could be changed by giving presentations and by introducing a point system, so people are (financially) rewarded when their input turns out to be valuable for the company.
Maybe a web based system, which is accessible for every employee, is a great solution to collect the IT developments throughout the organization. The point system is also more centrally manageable that way.
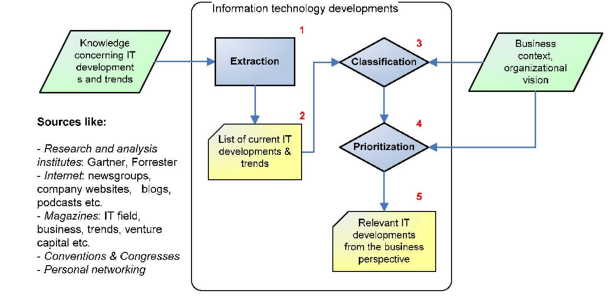
The overall process and context of this tool is explained by the diagram above. The tool fits into its context by, on the left hand side, the knowledge sources and, on the right hand side, the business context and organizational vision. This business context and vision comes from the people (especially the business people, board member) in the “IT development steering group” explained earlier. Extraction As mentioned earlier, the extraction phase (1) could be done by the whole organization, from board of directors to far down in the hierarchy. The creation of the list of current IT development & trends (2) could be automated with the web-based solution explained earlier. This process should be continuous.
Classification & prioritization When it is time for the company to plan the IS strategy (alignment cycle), it should form the steering group. This group should then classify (3) and prioritize (4) the list of IT developments it receives as input.
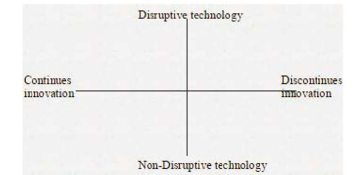
The classification of a development could be done several ways. The steering group should decide on what kind of classification method is used. One way is to use the following technology quadrant [ENT-05].
By placing each development in the quadrant (classification), and by keeping in mind the organizational vision, the steering group can discover the value of an IT development from the list. For example:
•A development from the list is classified as disruptive [DISR] (so other technologies become obsolete); (dev 1)
•Another development (dev 2) from the list is closely related to the field of the disruptive development (dev 1); Than the value of the first development could be higher than the second.
Of course the (business) experience and “gut feeling” of the members of the steering group play an important role in this classification process.
A question checklist could assist the steering group even more by discussing each question. This way the chance of forgetting an important factor is kept to a minimum. By using this question list the group can prioritize the list of IT developments. Questions, like the following, could be used for this (taken from [ENT-05]):
Does this innovation lead to a sustainable competitive advantage?
Can you use this innovation worldwide or are there important local issues? (e.g
culture, laws)
Can you identify a new user segment to offer this innovation to?
Can you organize a reliable delivery of this service to your clients?
What is the functional place of this new development in the client’s processes?
What is the extra value for the client?
Affects the value chain?
Which competencies and capabilities of the company are there that you could
use?
Finally, the steering group should come up with a list of relevant IT developments and trends from a business perspective (5).
Way 27. Technology assimilation plan
By Tim van Eijndhoven
Revised by Y Bosman
A technology assimilation plan provides management an indication of the effort that will go into assimilating new technologies in the company. The question to answer to provide this document is threefold. First we have to determine which factors affect the time it takes to assimilate a new technology. Secondly we have to determine how much the organization profile is positive for these factors. Finally we have to determine how to come to a planning for the assimilation process. The plan will probably be highly situation specific.
What is a technology assimilation plan?
Every business would like to have a competitive advantage over its competitors. One way of doing this is keeping up with technology. Having the latest technology will most likely have a positive impact on sustaining the competitive edge of your business. According to [RAH87] the ability of organizations to apply and assimilate new information technology lags far behind the available opportunities. Assimilation refers to the process within organizations stretching from initial awareness of the innovation, to potentially, formal adoption and full-scale deployment [FIC99] This is something which we can see perfectly in the model of Cooper and Zmud [COO90]. The stages in their model of adaptation and implementation are defined as follows:
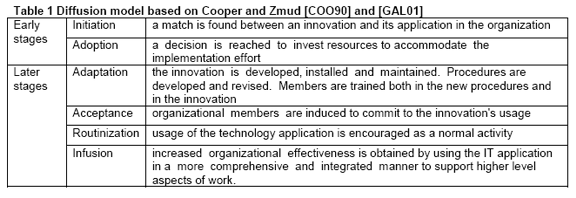
A technology assimilation plan approaches these steps from a strategic viewpoint. The plan should assess the time needed to flow through these stages. In essence assimilating a new information technology is actually stimulating a widespread diffusion of the technology throughout the organizational structure. Therefore planning for technology assimilation incorporates planning for the diffusion process. [AGA92]
Factors affecting technology assimilation
These factors suggest that a top-down approach in a formal organization would improve the chance of success for assimilation of new technologies. Analogue to this we could say that these organizational characteristics would reduce the time for assimilation of new technologies because the organization has less to do in a change phase. This change phase is a part of the Organizational development steps mentioned by Daft [DAF01], these steps are
1.unfreezing – participants are made aware of problems in order to increase their willingness to change their behaviour
2.(change agent) – change facilitator
3.changing – individuals experiment with new workplace behaviour
4.refreezing – individuals acquire a desired new skill or attitude
High levels of resources help the change process. When an organization already is strongly IT oriented it will most probably make a higher level of resources available for the assimilation of new technologies.
In general the assimilation time will be influenced by the relation the technology has with already existing technologies in an organization. In this relation it can be said that if an organization has a larger IT heritage (or IT nature) the new technology is more likely to have a close relation with one of the existing technologies in the organization and therefore the assimilation time will be less.
All these things considered the time it takes to adopt to a new technology will be comprised of the time to unfreeze, change and refreeze the organization personnel.
The time the assimilation process would take for the types of organizations can be illustrated in the following graph:
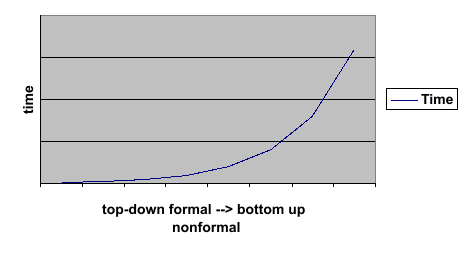
Planning the assimilation process
As said before the assimilation process will consist of the change phases given by Daft. Firstly the organization has to be profiled by the methods given in “measuring influential factors” This profile should then be matched to the success profile, the differences in these themes will have to be overcome by initiating an organizational change process towards the success factors. The bigger the difference the larger the amount of time that should be spent will be. There is no fixed formula to express the differences between the current profile and the success profile nor is there a formula to calculate the amount of time to spend on each of the necessary change processes. However the describing of the differences between the success profile and current profile will give an idea of how big the change should be, then a time estimation can be based on this idea.
The extent to which a particular path works for an organization depends on a large number of factors, not the least of which being the characteristics of the technology and where the organization is currently situated. [AGA92]. [GAL01] identified a set of themes which influence the assimilation of new technology. I decided to give my own interpretation of the table and conclusions of the paper presented by [GAL01]. As mentioned in the What question earlier, when planning for technology assimilation we actually plan for the diffusion process. Table 2 gives an overview of the themes which may have a positive and or negative influence on the different stages of adoption and diffusion.
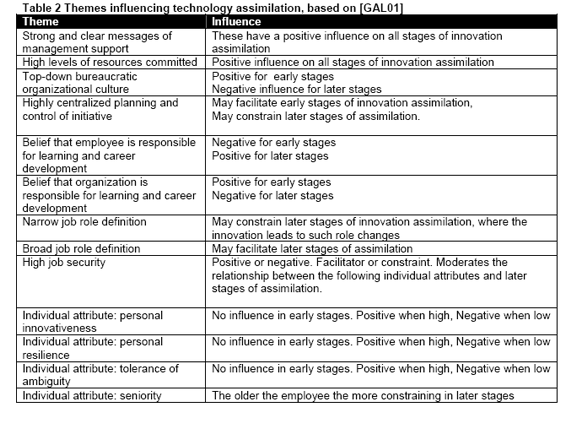
[RAM05] talks about adoption planning and when looking at his paper it becomes clear an integrated approach to technology adoption enables firms to effectively leverage emerging technologies for competitive advantage. According to him the key elements of adoption planning must include the following:
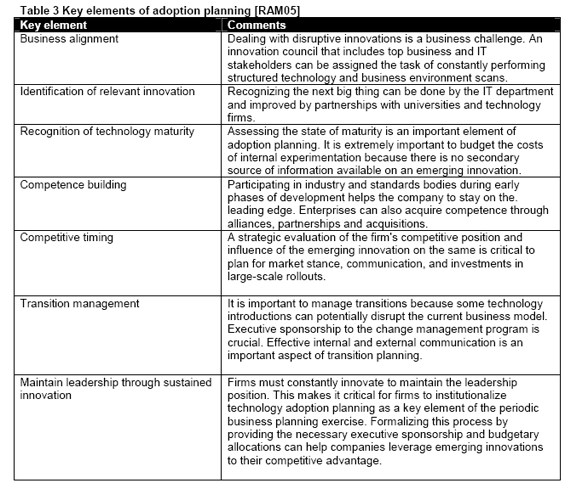
Way 28. Future Infrastructure
By Christian Bercz
The tool of future infrastructure is part of the third cycle ‘Analysing IS resources and technology infrastructure’, of the four cycles method1 for IS planning. To be more specific, the tool is part of the ‘planning the IS/IT infrastructure’ task. Its potential outcome is the “Management and control description of the future data, application, computing and communication infrastructure”.
Why
The purpose behind overall management of the technology infrastructure is to provide an appropriate set of technology, resources processes and services to meet the needs of the organization.2 In planning the IS/IT infrastructure the idea is to make a plan that will meet this purpose successfully in the future. As this tool, ‘Future Infrastructure’, is the finishing tool of this planning task, its purpose is to present a concrete result of the IT infrastructure planning process. IT specialist can use it to make a detailed technical description of it. It is crucial input for later IS organization planning and evaluation of the development portfolio.
What
Its potential outcome is the “Management and control description of the future data, application, computing and communication infrastructure”. This output should describe the means by which the results of the tool ‘IS needs’ should be fulfilled in the future. It is a concrete description of how in the future the IT infrastructure looks like. Infrastructure comprises four parts; physical infrastructure, architectures, policies and standards, and Management processes.2
The physical infrastructure consists of a range of network, hardware and base software products and services, deployed to enable applications and the general purpose use of technology to function successfully. A component is considered as being part of the infrastructure if it is used by more then one application or more then one person. The architecture describes the physical infrastructure and its configurations. It is a representation of a set of hardware and software components, and how they support the application and information requirement. Policies and standards cover the management of the infrastructure in terms of its acquisition, deployment and support. The last part of the infrastructure consists of Management processes to plan and justify the investment.
How
The description of the future infrastructure should be based on three inputs; IS needs, current infrastructure, information technology developments and its assimilation plan.
The first and most important input is the result of the other tool “IS needs”. This tool describes all the information needs, conceptual information systems, the business conclusions and recommendations, the application portfolio and the business information models. This makes the organisation needs clear in concrete terms and is therefore the ‘raison d’etre’ of the future IT infrastructure. The second input is the current IT infrastructure, which is important because it is the starting point for the future infrastructure, since “an information system is rarely build on a green field site”1. It can be useful to provide a future infrastructure to sustain or enhance current applications which are critical to business needs. Or it might be wise and profitable to maximize the use of current information and facilities available in the existing infrastructure.2 The current IT infrastructure is analysed in the second cycle.
The third input is the result of the two preceding tools: Information technology developments and Technology assimilation plan. The results show possibilities and opportunities to use and adopt in the future infrastructure in order to meet objectives.
By combinating these three information inputs one should be able to develop a description of the future infrastructure. To summarize this a lists of steps is provided to go through:
Step 1: get results “IS needs”.
Step 2: get analyses and understanding of current IT infrastructure
Step 3: define shortcomings of current IT infrastructure
Step 4: choose suitable technology possibilities and opportunities
Step 5: describe future IT infrastructure
Who
IT Managers and specialist with the ability to translate IS needs in IT solutions using the latest technology and the knowledge of the current IT infrastructure.
When
This tool is part of the third cycle. Since the four basic cycles are repeated each predefined period, this tool will be repeatedly used. Since it relies heavily on inputs from other tools, it should only be used when these inputs have changed. So this tool can be skipped when nothing has changed in tool number 25, 26 or 27 or when the current IT infrastructure or the analysis and understanding of it has not been changed.
But since it produces an important output with practical value that summarizes and makes a lot of other tools effective it should not be skipped when some of its inputs have crucially changed.
Way 29– Strategy And Structure Of The IT Function
Naam: Reinier Kernkamp
Introduction
This document describes tool 28 “Strategy And Structure Of The IT Function” and this tool is part of the third cycle named “analyzing IS resources and IT infrastructure” [SPI05]. The focus of this third cycle is on the practical application of these tools. As stated in the assignment I will use the comprehensive system for understanding, what Rudyard Kipling called his “six honest serving men”. Their names are what, why, when, how, where and who.
What?
The tool Strategy And Structure Of The IT Function is a tool that can be used in the analyze cycle. This tool contains a decision on the location of the responsibility, authority and activities of information management either centralized, distributed or decentralized [SPI05]. Information technology function has to do with everything around the topics maintenance and support of information systems, telecommunication and computers. We can think of system-, network-, database-, and website maintenance. Also development of programs and administrative applications is done here. We have to analyze how a centralized, distributed(federal) or decentralized structure relates to the responsibility, authority and activities of information management. If this is clear we know which way is best for the organization in order to have a good IT function, and the strategic goal of the IT strategy will comply with the corporate strategy. The relation between the Corporate and IT Strategy and Structure and the environment
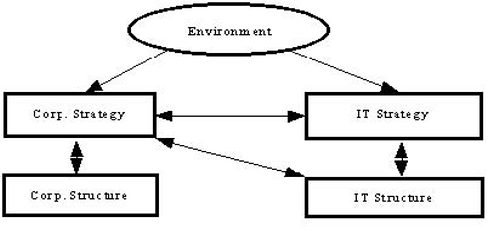
Why?
From the start of ‘computing’ it has been difficult to position the main IT resource of the organization in the organization structure. A lot is not clear about the positioning, structuring and organization of the IT function. Some things are better centralized and others devolved.[WP02] The quality of information delivery is a critical factor in the ability of firms to compete in today's dynamic environment. Companies have introduced new and innovative organizational structures to deal with the rapidity of change, the globalization of markets, and increasing expectations for quality and customer service. In the process, many have discovered that the interaction of the information technology function with the organization's business units is a key determinant of success or failure. Yet, organizations differ in the nature and outcomes of this interaction. [GG98] The organizational structure of functional support groups such as information technology has seen less attention in the literature. However, in many ways, the design issues associated with these functions are more complex and interesting because they are affected by the strategy and structure of the firm as a whole. Figure 1 illustrates the dynamics of this situation for IT. A large body of academic and trade literature supports the importance of aligning and business strategies. The implications for structure, however, are less clear. [GG98]
When?
According to four cycles of Salmela and Spil [SPI05] the “Strategy And Structure Of The IT Function” tool is used during the analyzing IS resources and IT infrastructure cycle. The third cycle can be seen as comprising the following three planning tasks:
•Planning the ICT infrastructure
•Planning the ICT organization
•Development of a preliminary project portfolio.
This tool is used in the second planning task; planning the ICT organization. It contains a decision on the location of the responsibility, authority and activities of information management, either centralized, distributed(federal) or decentralized. Today we are living in a dynamic environment and companies have to deal with the rapidity of change, the globalization of markets, and increasing expectations for quality and customer service. If the company doesn’t properly react to all these changes by adjusting the information technology function with the organization's business units, the company is bound to fail [WP03]. A good structure of the IT function is a key determinant of success or failure.
How?
First it is important to decide how the IT function should fit in the current organisation structure. ’Should it be a separate department?’ or ‘should every division have its own IT department?’ are questions that must be answered. This depends also on the size of the organisation.
After that, a decision on the structure inside the IT department should be made. Who has the authority to make decisions and who is responsible for what? It is important to balance authority and responsibility. It won’t work if someone has to make sure something is deliverer before a deadline when he cannot influence the delivering process.
Together with authority the matter of centralisation and decentralisation should also be discussed. In a centralised organisation decisions are made near the top of the organisation and in a decentralised organisation the authority lays on a lower level (Daft, 2001, p.18).
Both centralisation and decentralisation have advantages. According to Daft (2000, p.311-312) the advantages of decentralisation are that decentralisation is believed to relieve the burden on top managers, make greater use of workers’ skills and abilities, ensure that decisions are made close to the action by well-informed people, and permit more rapid response to external changes. Decentralisation is often used in an uncertain environment. On the other hand in times of crisis and risk decisions are made centralised.
To determine which aspects of IS/IT are best managed centrally and which are better devolved we have to know what we really mean with the terms centralized, decentralized and federal(distributed). We have to look at the advantages and critical management issues for each three types. First we will look at networking and processing of data for the centralized, decentralized and distributed structures. Next we will discuss the federal IT organization and finally a summary of the advantages and critical management issues shall be given for each of the three types. A functional centralization-decentralization model can be used to describe the structure of the IS organization. Under the context of networking and processing of data, these centralized, distributed or decentralized structures can be defined as[SCH00]:
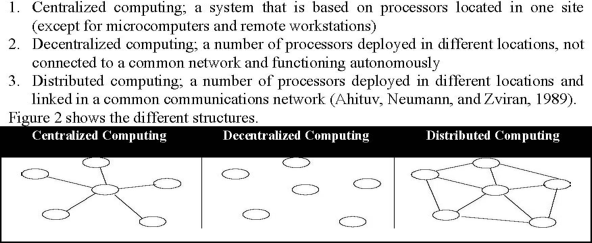
Figure 2 - Three Typologies of IT Structures [SCH00]
According to Von Simson [SIM90] the IS functional design with IS/IT roles should be played by both a central IS function and the business units and prescribes a “centrally decentralized” IS function. In his opinion clear structures, distinct roles and responsibilities must be defined with a mix of centralized and decentralized resources. If this isn’t done properly confusion, conflict, duplication of effort and or inadequate systems integrity will occur. Here we also bring up the federal structure, which is often seen as capturing the benefits of both centralized and decentralized structures. A federal structure makes it possible business units receive a responsive service from decentralized IS functions and at the same time a corporate IS function provides group wide IT services as well as some degree of central leadership and control of IT activities. To understand what we mean with IT activities we will use the definition of Sambamurthy and Zmud [SAM99]. They explain 3 general IT activities as:
1IT infrastructure management: "decisions that address the nature of hardware and software platforms, annual enhancement to these platforms, the nature of network and data architectures, and the corporate standards for procurement and deployment of IT assets"
2IT use management: "decisions that address applications prioritization and (short term and long-term) planning, budgeting, and the day-to-day delivery of operations and services"
3Project management: "blending knowledge of IT infrastructure capabilities and capacities with knowledge associated for the conceptualization, acquisition, development, and deployment of information systems applications"
The federal IT organization with the decentralized and centralized benefits can be seen in figure 3.
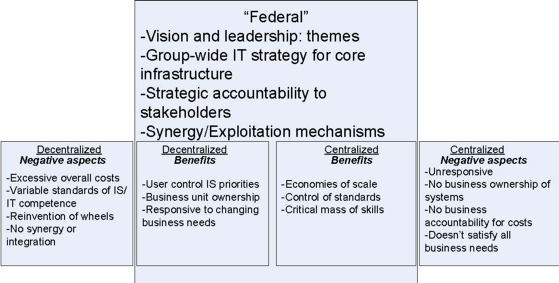
Figure 3 - The 'federal IT organisation' (source: after Hodgkinson)
Now we will discuss the dominant structural arrangements for IS activities, highlighting the advantages and identifies the critical management issues of each type, so we can make a good choice how to structure the IT function. The book Strategic Planning for IS[WP02] mentions four structural arrangements for the IS function. This tool only uses the centralized, decentralized and federal structural arrangement as depicted in table 1.
Table 1 -Summary of structural arrangements for IS/IT function in multiple business units
Structural arrangements for the IS Function | Strategies for managing IS/IT activities | Advantages | Critical management issues |
Decentralized IS/IT activities in business units | - Business units pursue independent system initiatives | - Business units have ownership - Users control IS/IT priorities - Responsive to business unit’s needs | - Integration - Lack of quality control of data - Variable standards of IS/IT competency - “Reinvention of wheels” and duplication of effort - Little synergy across business units - Managing cost |
Centrally-driven IS/IT activities | - Corporate wide IS/IT solutions imposed on business units | - Scale economies - Control of standards - Critical mass of skill | - Politics - Unresponsive - Does not meet every business unit’s needs -Effect on customer |
Federalism(integra ted IS/IT) | - Balancing central control and business unit autonomy without losing the advantage of global coordination and integration | - Group wide IS/IT strategy and architecture with devotion where appropriate | - Complexity - Execution - Timing - Defining “where appropriate” |
Where?
Figure 1 shows the relation between corporate strategy and structure and IT strategy and structure. It shows decisions on strategy and structure of the IT function should be made when an organization has the idea the IT function strategy doesn’t fit the corporate strategy. The strategy and structure of the IT-function has to be changed over time in any organization, because it depends on changes in the environment, structure of the organization and the corporate strategy.
Who?
Generally there is someone in the organization who has overall authority for IS/IT. In the end, someone at board level, even the chief executive officer by default is accountable for IS and/or IT [WP02]. Reality shows many board member are actually responsible for IS. The implication of locating responsibility for IT with the IT director(or chief information officer), finance director, business unit heads and the board has been researched by Griffiths[GRI94]. She has identified the benefits and deficiencies for each of these four manager types of IS/IT as shown in table 2.
Table 2 - Consequences of locating overall authority for IS/IT
Plusses | Minuses | |
IT directors | Technical expertise Accurate systems Sound technology Systems integration | IT not aligned Education omitted Information overload Technical solutions |
Finance directors | Tight cost control Department coordination Training costs integrated Strict authorization | Not always the best value for money Insufficient time to devote to IT Opportunities missed Short-term approach |
Business-unit head | IT investments linked to business direction Locally-focused systems Continuous development Shorter reporting structure | Systems not coordinated Incompatibility across business units Duplication of data Unnecessary costs incurred |
Board of directors | Strategic direction Appreciation of broader impact of decisions Major problems tackled Funding allocated | Logistical details omitted IS/IT underexploited Infrastructure weak Slow to exploit technology |
As IS/IT becomes more critical to organizations, the more senior(higher-ranking) will become the executives with specific IS or IT responsibility, both in corporate and business unit terms [WP02]. The success of such a senior role in ensuring that strategies are developed and achieved will depend much on the individual as his or her position on the organization chart [WP02].
Way 30. Rules and regulations for the IT function
By Sijmen Schoeman
Visualization by Rogier Bennebroek
Introduction
The third cycle of the four cycles method is about analysing IS resources and the IT infrastructure. The planning during the third cycle concentrates on assessing the current ICT architecture and IS skills, and in preparing for the future. The cycle can be seen as compromising the following three planning tasks [SA2002]:
1.Planning the ICT infrastructure;
2.Planning the ICT organization;
3.Development of a preliminary project portfolio.
This essay focuses on planning of the ICT organization, and especially on the rules and regulations for the IT function. It covers two important for techniques for specifying service levels and financial agreements, respectively service level agreement and charge-back methods.
Legal issues
The discussion on the legal field will be quite general because legal issues can be quite different and depend on the situation. For example the location (country) or the product under consideration can change the legal implications.
Legislation has its impact on every field of our lives and forms the minimum that everybody has to obey. Not obeying the law has consequences for the trespassers of the law. This is also the case for businesses [Brack, 2000] and therefore is also applicable for the IT function. Therefore, legislation should be taken into account in this tool.
To make the term of legislation less vague, every country has legislation that has to be fulfilled. For example, the protection of privacy sensitive information is a hot topic at the moment in the Netherlands. So, it is prescribed by law that personal information of employees is secured in a safe manner.
But legislation is also present when two companies are willing to work together [Brack, 2000], e.g. when an external IT function is hired. When agreements are made, these are considered as binding on both parties. This is also the case for agreements that are verbally. When these agreements aren’t fulfilled, legislation foresees in sanctions for the parties that doesn’t live up to the agreements [Brack, 2000]. This can result, for example, in penalties and therefore, legislation has a close link with financial agreements.
Quality levels
Although everybody knows the word quality, defining quality and make the term workable is very difficult. The reason for this is, according to van der Bij, Broekhuis & Gieskens [2001], the fact that it is ‘difficult to speak concrete about quality, without coupling quality to an object’.
The object in this case is the service or product that should be delivered by the IT function. The definition of product quality of van der Bij et al. [2001] might be useful. Their definition of product quality is: ‘the quality of the good or service that is delivered’. Although this definitions appears to be concrete, it is still difficult to specify the good or service that is under consideration. Therefore, the attributes of the service under consideration should be specified, so that there all know what quality is expected. We come back to this topic later on in this paper.
Also, the product or service under consideration has a certain price. But the actual value of the product or service depends on the quality of the delivered good. Therefore, value and indirectly price are also an attribute of the good delivered.
Service level agreements
A Service Level Agreement (SLA) is a contract between a service provider and the end uses, which stipulates and commits the service provider to required level of service. A SLA should contain the following:
•a specified level of service
•service options
•enforcement or penalty provisions for services not provided
•a guaranteed level of system performance (e.g. downtime)
•a specified level of customer support
•the software and hardware provided and
•the payments for these services.
The goal of a SLA is to bridge the gap between service provider (the supplier) and the users (customers) [Trienekens et al., 2004].
According to Trienekens et al. [2004], a SLA should more or less contain the following topics:
Basic specifications | Specifications of product/service |
General •Introduction and principles •Type and size of the agreement •Definitions and abbreviations Parties •Identification of parties •Ownership and risks •Responsibility, liability and penalty clausule •Communication structures, contact persons Scope •Description of the service •Scope •Disagreements •Restrictions, excluded events •Confidentialy •Modifications Currency of the SLA •Revision of the SLA •Duration and ending of the SLA | •Description of product/service •Service level of product/service •Support •Maintenance •Security •Disasters and continuity •Reporting •Documentation •Costs and payment |
Schematic visualization of tool 30
In order to have a workable result, this tool will be visualized so that the coherence of the different fields (Legal, Quality, Finance and SLA’s) becomes visible. As can be noted, issues about legislation, quality and financing also turn up in Service Level Agreements. Therefore, SLA’s can be seen as the umbrella which consists of other factors like legal, quality and financial issues. This can be visualized in the following picture:
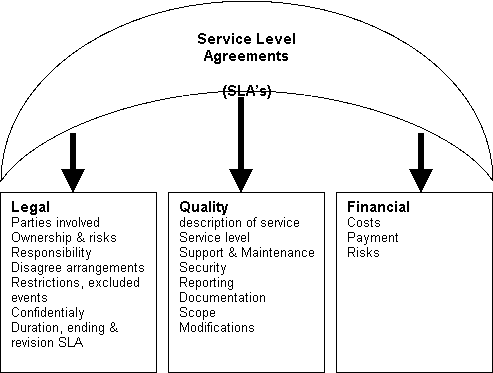
Figure 1: visualization of tool 30: rules and regulations of the IT function
This visualization describes general rules as well as quality and service levels for all services that are provided by the information management function. This visualization can be used when users are planning the IS organization and therefore contributes to the third cycle ‘analyzing IS resources and technology infrastructure’. Therefore, this tool is a useful addition to the other forty-nine tools that are available in the four cycles method, as described by Samela and Spil [2003].
Charge-back methods
Some companies treat the cost of the IS function as a part of overhead cost, a general expense carried by all departments that is considered essential to running the company. The downside of this system is that IS services can be easily abused, mostly because departments are tempted to order many extra services because no cost is directly associated with them. To mitigate this problem, many organizations have established charge-back systems. A charge-back system is a method by which organizational units pay for the services they receive, often referred as service charges [OZ2001].
What is chargeable?
The items for which a business unit may be charged fall into the following categories [OZ2001]:
•Personnel hours: usually, IS staff time is the largest part of the charge for systems development or systems maintenance. The IS unit charges either a fixed hourly rate of hourly rates that differ according to the level of expertise being provided.
•Computer time: this charge is normally billed to departments for the use of mainframe computers or computers on loan.
•External storage space: IS departments charge for storing data according to the amount stored. The charge is so many euros per megabyte per month.
•Number of I/O operations: some IS departments charge business departments for each log-on involving a shared computer.
•Paper output: some IS departments charge business departments per page of paper printout.
Costs that cannot be definitely attributed to specific business units are generally not charged back.
Charge-back features
Charge-back systems must have the following features [OZ2001]:
•Accountability: every element of the IS service must be accounted for and attributed to the manager who ordered it. If the cost of some services cannot be precisely allocated to individual units, they are not charged to individual units. Such costs are considered overhead and are absorbed by divisional or corporate headquarters.
•Controllability: managers who order services should be able to control what they purchase. The charge-back system should be designed so that business managers can determine the type and amount of service to purchase to best fit their specific needs.
•Timeliness: the IS unit must bill managers periodically, with reasonable intervals between billings, so that the managers can track the IS costs the incur and change their requests if they so wish.
•Congruence with organizational goals: charge-back rates should be established to encourage business units to use resources that are in the interest of the corporation and to discourage business units from using services that are not in the corporation’s overall interest.
Introduction
This section will cover how an organization can evaluate its current investments in IT. This forms a fundamental part of the third part in the planning cycle: analysis.
What is evaluated?
This tool provides insight in the cost centres of IT in an organization. All current and developing projects are evaluated on financial criteria. Both investment volumes as maintenance costs have to be considered. These financial figures are related to the performance of the project. Determining performance is a difficult issue in IT projects; therefore a model will be introduced using both measurable indicators as perceived performance by end users. The resulting evaluation will give an overview of how successful different projects are. Based on that, decisions can be made on stopping, continuing or changing a project.
This model is the real options evaluation, based on the system of options in the stock markets. Shareholders can buy a call option, allowing an investor to buy shares at a specific price at a specific time. The put option allows an investor to sell for a specific price at a specific time [BRE03]. By using the same model for IT investments, risk is also incorporated into the value of an investment. This will give a more reliable outcome and should improve decision making.
Real options have been used for choosing a new investment from alternatives. However, this can be applied for current investments as well. An investment can be seen as an asset that can be changed by expansion or abandonment. [KAM93]
When should current investments be evaluated?
Each project needs to have its own evaluation points, determined by the status of the project. Besides project investment evaluation, the evaluation of current investments needs to be done when preparing an IT strategy. When using the four cycles method, the best moment is the analysis phase, where IS/IT development portfolio is evaluated. The current investments need to be determined in order to know which new projects can be started, or how current investments can be expanded.
Why is an investment evaluation necessary?
Investment evaluation is critical because of two important reasons. First, the performance of a project needs to be monitored. Is the project carried out efficiently and are the costs justifiable in relation to the benefits? Secondly, the environment changes all the time. This leads to new opportunities as well as threats.
Systematic evaluation pushes management to consider opportunities, but also to define the risk of these projects. IT must contribute to the organization and must therefore generate profit. In the past, projects where initiated by the availability of technology. However, new technology is only relevant for an organization when the benefits it delivers (now or in the future) exceed its costs.
How can IT investments be evaluated?
The main advantage of the real options approach is that it allows opportunities to be calculated in the project value. An IT investment is often not limited to a single go or no-go decision. A first investment is made, that is evaluated after a certain period. The next decision is to expand or decrease the investment made. Valuating these options is the basis of the real options approach.
Benaroch [BEN02] has defined an approach to manage IT investment risks. He concludes that it is important to identify options, but searching for embedded options will provide even more valuable information. Option A may sound profitable, but it may have a very risky factor embedded in it, reducing its value. A consequence of this approach is that investments with options for change later on are more profitable. When the investment turns out to fail, there is a “safe way out”.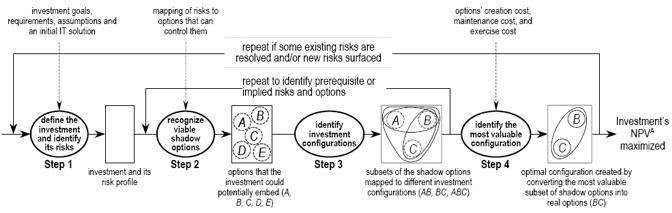
Step 1: Define the investment and its risks
First, the investment goals and requirements have to be defined. Investment assumptions (economical, technical and organizational) should show the investments risk. Payoff and costs should be linked to investments and decisions.
Step 2: Recognize viable shadow options
The project should be analyzed for shadow options. These options are embedded
in the first decisions that can be made. A project can have several consecutive
decision points, where an extra investment or disinvestment can be placed. This is
translated by an expansion or abandonment option.
A good way of showing this step is a decision tree [BRE03]. This shows all possible decisions with their shadow options. Benaroch [BEN02] defines 9 possible real options for IT investments, all connected to possible investment decisions, such as outsourcing and leasing. When calculating a value however, it is only important what the risk, costs and expected outcome of a decision is.
Step 3: Design alternative investment configurations
Using the viable shadow options from the previous step, investments can be configured. An investment configuration should provide an ideal risk trade-off and a maximal number of shadow options. These configurations can be seen as paths through the decision tree made in the previous step.
Step 4: Evaluate options and investment configurations
This step calculates the option values for all the investment configurations. Given all the previously found information, an option value can be calculated.
Kambil & Henderson have used a slightly different approach for determining option values for IT investments [KAM93]. Their focus is more financially based and they leave out the part of investment configurations. The approach from Benaroch was adapted later on by author authors (Chatterjee & Ramesh [CHAT99], Balasubramanian et al [BAL00]). However, Kambil & Henderson have a good financial explanation for option value calculation.
Example
To illustrate the practical use of this tool, a simplified example will be given. This example is meant to show an option calculation in a brief form. The number of options is very limited; a real-life situation would consist of more options and risks. More elaborate calculations have been made by Kambil [KAM93] and Benaroch [BEN02].
Step 1: Define investment and risks:
A company uses a HRM system for personnel management. This system requires a lot of maintenance, so the IT manager wants to know the money spent relates to the benefits of it.
Risk: New laws require more information to be captured, thus leading to changes in the system. This information can be imported through XML from a government agency. Otherwise, it has to be entered manually.
Opportunity: Currently the personnel data is copied manually to the payroll system. It might be possible to automate this using XML transfers
Step 2: Recognize shadow options
The first option is to leave the system as it is, and add the needed information manually. The costs of this operation are estimated on € 5.000 annually.
It is also possible to add XML support to the system, which will incur a € 40.000 investment and € 4000 maintenance costs. However, with this extra investment personnel data can be copied to the payroll system. It is not sure whether this is going to work. If it works, € 10.000 will be saved each year on top of the € 5.000 of the legally required information.
The steps are shown in the following decision tree analysis (DTA).
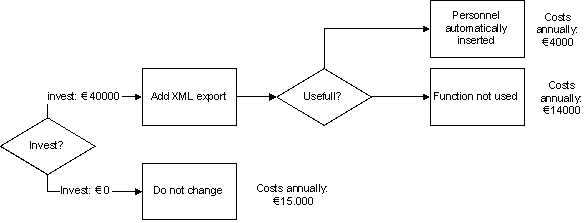
Figure 11: Decision Tree Analysis (DTA) for example case
Step 3: Design investment configurations
In this simplified example there is only 1 investment decision: to invest in the XML functionality or not.
Step 4: Evaluate options
To evaluate an option, some values need to be estimated:
Riskless rate of return: estimated at 4%
The project is now valued at € 1.200.000. However, adding the costs of manually transferring information will lower this. In this simplified case, a perpetuity is used to calculate this value. In real situations, a shorter lifetime will be more appropriate.
€ 5.000
Value = € 1.200.000 - 4% = € 1.075.000
So in fact the initial value of the project is € 1.075.000.
Investing in the XML function will:
-Save € 5000 each year, because data is automatically inserted
-Leads to € 4.000 extra costs each year.
-Gives a chance on € 10.000 of savings per year, because of the automatic payroll interface.
So this leads to two alternatives, one where the costs of payroll are saved (a), and one where these costs were not saved (b).
€ 4000 € 10000
Scenario A: € 1.200.000 - 4% + 4% = € 1.350.000
€ 4000
Scenario B: € 1.200.000 - 4% = € 1.100.000
The value of an option can be determined by the Cox-Rubenstein formula [RUB79]
(r-b) (r-a)
C = Ca (a-b) + Cb (a-b)
r![]()
Where C is the value of call option, and:
-a and b the returns on the different scenarios
-r the riskless rate of return
-Ca the value of a call option on scenario A
-Cb the value of a call option on scenario B
The return on Scenario A is:
a = € 1.350.000 / € 1.075.000 = 1,26
b = € 1.100.000 / € 1.075.000 = 1,02
Ca = max[0, aS-I] = 1,26 * 1.075.000 – 40.000 = € 1.310.000
Cb = max[0, bS-I] = 1,02 * 1.075.000 – 40.000 = € 1.060.000
So a call option would cost:
(r-b) (r-a)
C = Ca (a-b) + Cb (a-b)
r![]()
(1,04-1,02) (1,04-1,26)
C = € 1.310.000 * (1,26-1,02) + (1,26-1,02)
1,04
C = € 1.078.000
So in this scenario a call option on the investment on XML delivers a (slightly) higher value than the current value. According to this formula, the investment needs to be done. However, the risk of the opportunity in this project was not quantified. Therefore it has been weighted equally to the chance of not succeeding in using an automatic payroll interface.
Who should participate in IT investment evaluation?
The evaluation of IT investments should be done in the IT department, usually by the manager responsible for the IT investment planning. Because of the financial character of this tool, it is advisable to cooperate with the finance department. They probably have more insight on how to appreciate risks and how to calculate options.
Conclusion
This paper has given an introduction to the use of real options for calculating investment values. This topic is handled more in-depth by other authors, including the references from this article. There are a lot of extensions possible in this model, suitable for more complex cases.
Real options are found to be a good way of making decisions on IT investments. In contrary to the usual Net Present Value (NPV) calculation, it accounts for risks and appreciates control over the project. Current investments are usually valuated by their current benefits and costs, with the real options approach they are seen as continually active projects, where a decision can be made at any given time. Of course non-financial criteria can be as or even more important, but an IS planning should always provide reliable figures to justify a decision. Real options are a real step forward when it comes to investment calculation.
Introduction
This paper focuses on the “way”; Future Investment Possibilities. Which is an aspect of the the 4-cycle method described by Salmela and Spil. The goal of this paper is to work this aspect further out and provide a clear description and explanation of future investment possibilities. This is necessary to extend the 4-cycle method to a 4-cycle methodology, with a match between theoretical foundations and practical experiences.
The approach used is twofold. On the one hand Ton Spil assigns students to individual aspects of the 4-cycle method for a description and explanation through a paper. His focus is on creating an integrated overview of all aspects of the 4-cycle method. On the other hand individual student take on with the assigned aspects and work these out by starting from scratch or revising paper of prior e-strategizing courses. This is done by means of literature research and integrating the different literature. Also an attempt is done to provide it with hand and feet by providing an overview of stages relevant fro future investment possibilities.
This paper is set up as follows; First a short explanation of the 4-cycle method will be given, this explanation will go into more detail into the analyzing quartile of the 4-cycle method. Especially the other ways Salmela and Spil defined for the 3rd quartile will be discussed briefly, including their context with future investment possibilities. Secondly future investment possibilities itself will be discussed into more detail; definition, goal and context. Relevant theory will be discussed to provide the subject with more foundation and depth. An attempt at detailing different aspects of future investment possibilities is undertaken.
Finally in a conclusion a short overview will be given of this paper, pointing towards the most important aspects introduced and discussed in this paper. Also will an indication be given what aspects discussed in this paper need further refining or research for verification.
Future investment possibilities are an aspect of the “Evaluating the IS/IT development portfolio” which is a part of the analyzing cycle of the 4-cycle-method. Other parts of this cycle are “planning of the IS organization” and “Planning the IS/IT infrastructure” [SA, 448]. These other ways create a planning that can be used to generate a list future investment possibilities.
Points of attention
Three points are important to realize when considering the 4-cycle method [ZA, slide 24]:
1. All the tasks and sub-tasks are interrelated and inter-influential. The previous outcomes, along with the external changes, provide the dynamic basis for the flexible strategic adjustments for IS-planning.
2. The whole planning process is continuous and repetitive
3. The 4-cycle method gives us the choice-list but not the check-list
Future investment possibilities
Future investment possibilities are defined as “describing the future capabilities of the IS-function to initiate new projects and to maintain high quality in the provided services” [SA, p451].
Context
Exploring future investment possibilities is not only an incremental analyzing process, but because it is a part of strategy formulation also an iterative process. This analyzing process should be constantly adapted to internal and external changes and the dynamic interaction between the two. Thereby creating a reinforcement and sharper focus of future investment possibilities, taking into account the progress made so far [JO, p62-463].
Theory
Having a good focus of investments, and n overall agreement about this focus, over the long run is important. Not only because of the actual sums involved, but also due to the irreversibility of certain investments [NA, p111]. Certain investments will commit an organization to more investments, because the level of adoption (users choosing to use a product [NA, p65]) does not meet the expectations. The benefits of IS-technology investments accrue over time [WA 2, p222], this shows in successive and supplementary investments in the IS/IT-systems. Without an iterative review of investment possibilities, in coordination with users, this can result in pouring money and efforts down the drain. The IS-function should therefore not choose it’s investment possibilities alone. But on the other hand a good review is necessary of the opportunities in the IS/IT-field, often this is now not the case [MI, p377].
Planning can be developed top-down and bottom-up [JO, p434]. At the top-level future investment possibilities will be more formulated as a concept, while at the bottom-level formulations will probably be more specific; a function or application. Both should be incorporated in a final list of possibilities.
When working toward a list of future investment possibilities it is important to take into account the maturity of the current IS/IT-operations and capabilities. The Process maturity model of the Software Engineering Institute provides a concept that takes into account how ell developed and understood an organizations processes (business as well as IS/IT) are [FE, p88-89]. The level of maturity will place limitations on the immediately achievable goals; e.g. when a process is not well understood yet it is very difficult to develop very advanced IS/IT-solutions.
It is difficult to catch all justifications into financial figures. Especially IS/IT investments cannot always be justified (only) financially. A tool described by Ward is the investment justification; this shows what indicators for investments might be applicable for what kind of IS/IT-applications [WA 1, p427]
Different parts
Future investment possibilities are an important issue that fills in the planning for future occasions for the IS/IT-capabilities. The key elements of planning are the setting of objectives and priorities [LE, p319]. Setting objectives is about generating alternatives and choosing one, in the 4-cycle method choosing an alternative is done at a later stage.
Therefore to find the best way to deploy the limited resources the process of future investment possibilities can be divided into three parts; I) collecting information, II) seeking alternatives III) Prioritization of possibilities.
Information collection
The 4-cycle method is an interrelated and continuous process, so the participants can acquire the information they need from the results of previous processes (e.g. internal and external resources, CSF and SWOT analysis, list possible future events, etc.). Basically, the information necessary includes 2 categories; the business situation and structure and the current IS/IT-capabilities. This information can be come by from the prior cycles (agreement on planning objectives & stakeholders and Alignment of business objectives and information objectives).
Goal; find the information that helps functional management and IS management deeply understand the current situation and potential future challenges of the business and IS. This part provides the basis for seeking potential projects.
Methods; Integration and collection of information of the prior cycles of the 4-cycle method. Different rationales can be used (Business-led, Method-driven, Technological, Administrative and Organizational [WA 1, p123]), each rationale requires involvement of different disciplines and ranks. Each with different methods of their own, it is out of place and impossible to discuss here all possible methods.
Participants; Functional business management, IS managements [OZ, p410-411] and of course users. But in certain case also senior management and consultants.
Result; Gathering of internal information and external information. This information provides insight in the strength, weakness, opportunities threats of current IS/IT- and Business-resources, capabilities and visions and analysis on the trends in the industry and more specifically competitors. This information can partly be retrieved of prior cycles of the 4-cycle method.
Seeking alternatives
The main task in the second cycle is to promote strategic thinking, creativity and innovation in the planning process but also to ensure sufficient integration of IS plans with business plans [SA, p452]. Therefore a great deal of this work might already have been carried out and the outcomes only need to be collected. But in the 3rd cycle additional analysis might have to be carried out because the IS-organization and IS/IT-infrastructure are analyzed too. This might result in new insights/outcomes.
Goal; find reasonable potential alternatives which can improve the effectiveness and performance of IS/IT and help the business to gain competitive advantage in the future.
Methods; questionnaire for the IS/IT users, creative workshops using informal brainstorming techniques and several formal meetings to agree on the final outcomes. Innovation and creativity is greatly encouraged during this process.
Participants; Functional business management, IS managements [OZ, p410-411] and of course users
Result; proposals of IS projects that can solve the existing needs and contribute to the sustaining development of the business. These proposals are the potential projects that could be approved in the future.
Prioritization of possibilities
It is important to use prioritization of investment possibilities because it forces to consider these with a certain rationale. Therefore three factors should be included in the assessment; Benefits (what is most important to do?), Resources (what is possible to do?) and risks (what is likely to succeed?) [WA 2, p228]
Goal; to distinguish priorities in the alternatives generated based on an analysis of benefits, resources and risks.
Methods; Lederer and Mendelow describe a number of possibilities to establish and maintain priorities. These issues are about the complete management of the process f setting priorities and involving people (Use of a steering committee, control IS-resources, dedicate teams to functional areas, prepare a good plan, promulgate priorities and reasons for them act dictatatorially, apply new technology, reward completed projects, obtain excess resources, encourage teamwork, live with it[LE, p324-325]).
A possible tool is the value-risk grid presented during the lectures [ZB, slide 4]. A final list of priorities can be formulated in a similar form like the MoSCoW-tool (Must haves, Should-haves, Could-haves, Would-haves) of DSDM [DS, moscow]. This tool makes clear to everybody involved, what will be the main priorities (Must-haves) which will be dealt with first, and what topics next.
Participants; Functional business management, IS managements [OZ, p410-411] and of course users. But in certain case also senior management and consultants.
Result; a list of prioritized proposals, these proposals are generated while seeking alternatives.
Conclusion
In this paper a theoretical foundation is provided for future investment possibilities. Although it is an honest attempt, and to the personal opinion of the author a good one, it might still be possible to find additional relevant literature that can be added.
The most important addition of this paper, when comparing it with the prior version is the addition of setting priorities when creating an overview of future investment possibilities. The three different parts now described for future investment possibilities might need practical testing when the 4-cycle method is applied.
Way 33: IS future benefits
Menno Berens
The tool described in this way can be used to define the overall quantitative and qualitative benefits that the IS/IT project portfolio can leverage. Quantitative benefits are those that can be measured and expressed in figures, while qualitative benefits are often hard to measure and normally not expressed in figures, but are more often described in words.
What this tool tries to do is to nevertheless combine these two types of measures in one model, by using a so called Multi Criteria Analysis (MCA).
The MCA is normally used to select the best of multiple alternatives, but in this tool the MCA is used to determine the future benefits of a project portfolio. The fact that we use the MCA differently does not change the application of it though.
In this tool we combine financial and non-financial values in a MCA. The financial values are calculated through the commonly used NPV (Net Present Value) technique, also explained in “Financial Assessment of the IS/IT portfolio” on page 144 of the E-Strategizing Syllabus. Non-financial criteria have to be formulated according to the current project.
Financial values
Because in the IS/IT branch the uncertainty is quite high, chances are that some projects fail. This does not mean that risky projects should not be undertaken, because a high potential return might easily make up for the risk of losing an investment. To include the risk of failure, the NPV from the Syllabus has to be complemented by a risk factor. For every likely scenario of a project, the chance of this scenario should be multiplied with the NPV of that scenario, to get an average NPV, as in the next formula.
![]()
The time-span of the NPV-analysis is quite important and difficult to determine. Truth is that in the e-strategy environment projects and investments follow each other up more quickly than in most other braches, so time-span should be chosen low.
The NPV can be positive as well as negative. If for example most of the costs are financial, and the benefits are indirect or non-financial, the NPV is likely to be negative.
Non-financial values
To determine the non-financial values, a decision has to be made on how to compare different projects’ contribution to meeting the objectives. This requires the selection of criteria to reflect performance in meeting the objectives. Each criterion must be measurable, in the sense that it must be possible to assess, at least in a qualitative sense, how well a particular option is expected to perform in relation to the criterion. In order to finally compare this qualitative assessment to the quantitative financial values, it is necessary to translate all the qualitative assessments to a numerical score on a common scale, for example between zero and hundred. After this translation the different comparable values have to be weighted, important criteria get a high value and less important criteria get a lower value.
Combining them
The total value of all projects can then be presented as the sum of all financial measures, and the sum of all non-financial, quantitative figures. This encompassing figure can then be compared to other project portfolio alternatives, or with portfolios from the past.
Also, the individual projects from the project portfolio can be compared to each other by drawing them in a graph, with on one axis the financial value, and on the other axis the non-financial value and drawing each project in this graph.
An example
Projects | ||||
Criteria | Weight | Portal | Newsletter | Integrator |
communication | 15 | 50 | 50 | 80 |
unification | 20 | 30 | 40 | 80 |
knowledge creation | 10 | 10 | 10 | 40 |
preparation for the future | 15 | 10 | 10 | 40 |
students opinion | 20 | 30 | 20 | 40 |
employees opinion | 20 | 10 | 10 | 40 |
Total | 100 | 24 | 24 | 54 |
NPV | -100 | -50 | -300 | |
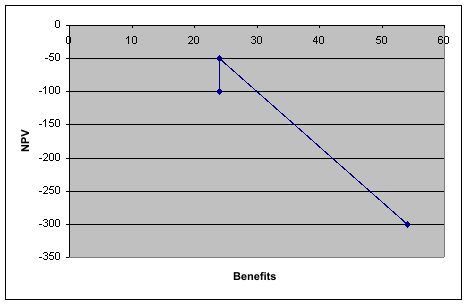
From the graph, it shows that the Portal- and Newsletter-project have the same benefits, but different costs, and that the integrator has much more benefits, and much more costs. When the project portfolio is larger, as is to be expected, the graph becomes more interesting because it gives a quick overview, the projects on the right and upper border have the highest benefits/costs(NPV)-ratio, while the projects on the left and bottom have less benefits and/or more costs.
Way 34. Proposed IS/IT project portfolio
By T. van den Brink
The concept of the IS/IT portfolio can be a useful way to organize the IT efforts within an organization. In its most simple form the IS project portfolio consists of all the projects that have been started in a organization. Companies that have adopted more mature IS/IT portfolio management, however, use portfolio management to find a balanced set of projects that are aligned with the company’s strategy and returns an optimal value. The problem is which projects to start, and which ones to decline.
What
The concept of Modern Portfolio Theory (MPT) was introduced in 1952 when H. Markowitz published an article with the same title. The basic idea of MPT is that managers should focus on selecting portfolio’s of investments based on risk-reward expectations. F.W. McFarlan first suggested that MPT could be applied to IS/IT investments in his article: ‘Portfolio approach to information systems’ [McF89]. His idea was that managers should use a risk-based approach to find the best IS/IT projects.
This approach was later extended to use a portfolio approach to select, control and evaluate IT projects. This tool description will focus on the first part, the selection of the right projects, in order to get an optimal IT/IS portfolio that delivers high value to the company at the lowest possible risk.
Why
The reason why it is important to select the right projects to undertake, is that there is a lot of money and time concerned with IS/IT projects and it is essential to determine what projects to start and which ones to decline in an early stage, before to much money and time has been wasted on a particular project.
It is however needed that managers look at the overall IS/IT portfolio instead of just at the value/risk of individual projects. By using the method that will be discussed later in this tool description it is possible to select an optimal set of projects from a wide variety projects that can be undertaken. And by doing so the value can me maximized at minimum risk.
When
IS/IT Portfolio management is an ongoing process, since project end and start on different moments in time. The selection if a projects will be accepted will always take place before the start of a project at a time when not all information might be known, therefore the calculation of the risk is important.
How
Since it is impossible to calculate all different IS/IT portfolio’s that can be created from a set of projects automated methods provide a helpful tool for making these kinds of calculations possible. The most frequently used method for risk analysis is the Monte Carlo Simulation[Mck05].
The results of these simulations is a graph which shows all IS/IT portfolio’s, it clearly shows which portfolios present high value/low risk and which present low value/high risk and everything in between. Portfolios that have a relative high risk for their value should be avoided.
The figure below shows a possible outcome from a simulation[Mck05]. The graph shows a ‘efficient frontier’, the closer a IS/IT portfolio is to this line, the more efficient it is. By selecting the IS/IT portfolios that are on the efficient frontier one is certain that there is no other portfolio with the same risk and a higher value or a portfolio with the same value and a lower risk.
Figure 1: Portfolio optimization for oil and gas investments. Source: Don Merritt, Merak Projects
Where and Who
Portfolio management can be a useful tool for all organization that have to make decisions about the projects they are going to start. It should be performed by high level management, this is because they can make decisions about the overall project portfolio and can determine what money is spend.
References
AGA92] Ritu Agarwal, Mohan Tanniru, "Assimilation a new information technology: a strategy and its assessment", ACM, 1992
[ARM99] Curtis P. Armstrong, V. Sambamurthy, "Information Technology Assimilation in Firms: The Influence of Senior Leadership and IT Infrastructures", Information Systems Research, © 1999 Informs Vol. 10, No. 4, December 1999, pp. 304-327
[BAL02] P. Balasubramanian et al., Journal of Strategic Information Systems, volume 9 , 2000, pp 39-62
[BEN02] Benaroch, Managing Information Technology Investment Risk: A Real Options Perspective, Journal of management information systems, Volume 19, Number 2, pp 43-84
BHATTACHARYYA, G. (1975). Project on study of subjects. (Library Science with a slant to Documentation. 12; 1975; Paper G
Bij, J.D., van der, Broekhuis, H. & Gieskens, J.F.B. (2001). Kwaliteitsmanagement in Beweging, Deventer: Kluwer
Brack, A., (2000). Bedrijfsrecht op een bedrijfskundige manier, Groningen: Martinus Nijhoff
[BLOGS] The use of Blogs in the 2004 presidential election http://www.campaignsonline.org/reports/blog.pdf
[BRE03] Brealey & Myers, Principles of corporate finance, McGraw Hill, New York, 2003
[CHAT99] Chatterjee & Ramesh, Real Options for Risk Management in Information Technology Projects, Proceedings of the 32nd Hawaii International Conference on System Sciences, 1999
Ciborra, C. (1994). The grassroots of IT and strategy. In: Ciborra et al, Strategic Information Systems: A European Perspective. Wiley, Chichester, pp3–24.
[COO90] Cooper, R.B. and Zmud, R.W. "Information Technology Implementation Research: ATechnological Diffusion Approach," Management Science (36:2), 1990, pp. 123-139.
[CRI02] Rick Crider "Secrets of Technology Adoption", Constructware, www.constructware.com
CRAWFORD, Susan. Information needs and uses. (Annual Review of Information Science and Technology. 13; 1978; pp 61 - 81).
CRONIN, Blaise. (1981). Assessing information needs. (Aslib Proceedings. 33(2); 1981; pp 40).
[Daft] Daft, R. L., Management, 5th Edition, Harcourt 2000
DERVIN, B and NILAN, M. (1986). Information needs and uses. (Annual Review of Information Science and Technology. 21; 1986; pp 3 - 33).
DEVADASON, F.J. (1989). Identifying information needs: Discussion Paper at the Regional Consultation on Provision of Information Services to End Users, UN/ESCAP Fertiliser Advisory, Development and Information Network for Asia and the Pacific - Network of Fertiliser Information Systems (FADINAP/NFIS). Bangkok, 20 - 24 Nov, 1989.
[DISR] Wikipedia on disruptive technologies
http://en.wikipedia.org/wiki/Disruptive_technology
DOCUMENTATION RESEARCH AND TRAINING CENTRE, INDIAN STATISTICAL INSTITUTE. (1971). Seminar on reference service : Working papers and proceedings. Bangalore, DRTC. 1971. pp 68.
ELLIS, David; COX, Deborah and HALL, Katherine. (1993). A comparison of the information seeking patterns of researchers in the physical and social sciences. (Journal of Documentation. 49(4); 1993; pp 356 - 369).
[ENT-05] Slides from the UT course ntrepreneuring
[EIJ04] Tim van Eijndhoven, "Technology Assimilation Plan", 2004
[FIC99] Robert G. Fichman, "The Diffusion and Assimilation of Information TechnologyInnovations", September, 1999 to Appear in: R.W. Zmud (Ed.) Framing the Domains of IT Management: Projecting the Futur…Through the Past, Cincinnati, OH: Pinnaflex Educational Resources, Inc.
[FIE96] Fiedler K., Grover V., Teng, J., An Empirically Derived Taxonomy of Information Technology Structure and Is Relationship to Organizational Structure, in Journal of Management Information Systems, volume 13, number 1, pages 9-34, 1996.
[GAL01] Michael J. Gallivan, "organizational adoption and assimilation of complex technological innovations: development and application of a new framework"
The database for advances in information systems - Summer 2001 (vol 32. no3)
[GG98] Judith R. Gordon, Steven Gordon, Structuring the Interaction Between Information Technology and Business Units: Prototypes For Service Delivery, 1998
[GRI94] Griffiths, C., responsibility for IT: A grey area of management, in L. Willcocks, ed., Information Management: The Evaluation of Information System Investments, London,1994
HEWINS, E.T. Information need and use studies. (1990). (Annual Review of Information Science and Technology. 25; 1990; pp 145 - 172).
HOMER, J.H. (1981). Patterns in the use of information : The right to be different. (Journal of American Society for Information Science. 1981; March; pp 103 - 112).
ITOGA, Masaru. (1992). Seeking understanding beneath the unspecifiable : An alternative framework for mapping information needs in communication. (Libri. 42(4); 1992; pp 330 - 344).
[KAM93] Kambil, Henderson & Mohsenzadeh, Strategic management of information technology investments: an options perspective, pp 161-178, Idea Group Strategic Information Technology Management Series, 1993
KATZ, D. and KAHN. R.L. (1978). The social psychology of organisations. Ed 2. New York, John Wiley. 1978.
KUHLTHAU, Carol C. (1993). A principle of uncertainty for information seeking. (Journal of Documentation. 49(4); 1993; pp 339 - 355).
Kipling, R. (1998). The Elephant’s Child.
KUNZ, Werner; RITTEL, Horst W.J. and SCHWUCHOW, Werner. (1977). Methods of analysis and evaluation of information needs : A critical review. Munchen, Verlag Dokumentation. 1977. pp 16.
MINTZBERG, H. (1977). The nature of managerial work. New York, Harper. 1973. Quoted in WILSON, T.D., and STREATFIELD, D.R. Information needs in local authority social service departments : An interim report on project INISS. (Journal of Documentation. 33 (4) ; 1977; pp 290).
[Mck05] P. McKenna, Modern Portfolio Theory: Driving project portfolio management with investment techniques, 15 Aug 2005
[McF89] FW McFarlan, Portfolio Approach to Information Systems, Software risk management table of contents, 1989
Mentzas, G.N. (1999). Coupling Object-Oriented and Workflow Modelling in Business and Information Process Reengineering. University of Athens, IOS Press, pp63-87.
Multi-criteria analysis manual, paragraph 2.5 27 November 2005
http://www.odpm.gov.uk/stellent/groups/odpm_researchandstats/documents/page/odpm_research_608524-03.hcsp#P179_17882
Chapter 15 Dealing with Multiattributed Decisions, presented at the course Business Case Development.
NEELAMEGHAN, A. (1975). Modern business environment and environmental scanning. (Library Science with a slant to Documentation. 12(1); 1975; pp 5).
NEELAMEGHAN, A. (1992). Information for small enterprises. Bangalore, Sarada Ranganathan Endowment for Library Science. 1992. pp 50.
NEUBAUER, K.W. (1977). Information sangebot und informationsverhalten in bibliotek und dokumentation. Quoted in above cited ref. 13, pp 9.
[OZ2001] Oz, E. (2001). Management Information Systems (3rd ed). Course Technology, p413-414.
Pant, S and Cheng Hsu (1995). Strategic Information Systems Planning: A Review.
1995 Information Resources Management Association International
Conference, May 21-24, Atlanta, Georgia.
http://viu.eng.rpi.edu/publications/strpaper.pdf
Peppard, J. et al (2004). Beyond strategic information systems: towards an IS capability. Journal of Strategic Information Systems 13, pp167-194.
PAISLEY, W.J. (1968). Information needs and uses. (Annual Review of Information Science and Technology. 1968; pp 1 - 30).
PRATAP LINGAM, P. (1987). Manpower planning for sectoral information and documentation system in India with an illustrative case study of textile industry. (IASLIC Bulletin. 32(1). 1987; pp 24 - 26).
PRATAP LINGAM, P. (1980). Methodology for identifying and recording information needs of users in an industrial enterprise: A case study. (Library Science with a slant to Documentation. 17(2); 1980; pp 27).
PRATAP LINGAM, P. (1985). Some selected extra-curricular components in information science. (Library Science with a slant to Documentation. 22(4); 1985; pp 196).
PRATAP LINGAM, P. (1986). Towards a methodology for developing a mechanism for business environmental scanning. (IASLIC Bulletin. 31(3); 1986; pp 84, 92 - 96).
PRATAP LINGAM, P. (1983). Design engineer : His information requirements. (International Forum on Information and Documentation. 8(2); 1983; pp 29 - 35).
[RAH87] Lois E. Raho, James A. belohlav, Kirk D. Fiedler,
"Assimilating new technology into the origanization: an assessment of McFarlan and
McKenney's model" MIS Quarterly, Vol. 11, no. 1 (Mar. 1987) 47-57
[RAM05] Girish Ramachandra, "Learning from RFID: strategies for new technology adoption", SETLabs briefings no 3, 2005
RHODE, N.F. (1986). Information needs. (Advances in Librarianship. 14; 1986; pp 49 - 50). New York, Academic Press.
[RUB79] Cox & Rubenstein, Option pricing: a simplified approach, Journal of financial economics, 1979
Salmela, H., Spil, T. (2002). Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22, pp441-460.
[SAM99] Sambamurthy V., Zmud, R.W., Arrangements for Information Technology Governance: A Theory of Multiple Contingencies, in MIS Quarterly, volume 23, number 2, pages 261-290, 1999.
Schoeman, S., (2004). Rules and regulations for the IT function. Syllabus E-strategizing p98
Salmela, H. & Spil, A.A.M., (2003). Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22, p453
[SCH00] Schwarz A., Taylor D.S., under the supervision of Dr. Wynne Chin The Governance and Structure of the IT Organization, 2000
SLATER, M. (1989). Information needs of social scientists : A study by desk research and interview. Boston Spa, BLRDD. 1989. (British Library Research Paper No. 60).
[SIM90] von Simson, E.M., The centrally decentralized IS organization, Harvard Business Review, 1990
[TH1999] Thiadens, T. (1999). Beheer van IT-voorzieningen. Schoonhoven: Academic Service, p203-217.
[TR2004] Trienekens, J.M. et al. (2004). Specification of Service Level Agreements: Problems, Principles and Practices. Software Quality Journal 12, p43.
Warboys, B.C. (1994). Reflections on the relationship between BPR and Software Process Modelling. University of Manchester, Informatics Process Group, pp1–9.
[WP02] Ward, J. & Peppard, J.: Strategic Planning for IS, 3rd ed., 2002
WILSON, T.D. (1981). On user studies and information needs. (Journal of Documentation. 37; 1981; pp 3 - 15).
WILSON, T.D., and STREATFIELD, D.R. (1977). Information needs in local authority social services departments : An interim report on project INISS. (Journal of Documentation. 33 (4) ; 1977; pp 290).
Chapter 5 - Authorization

Chapter Four - Authorizing
Identifying organisational implications | ||
#35 P 151 | Impact on organisation | Lists organisational implications (both positive and negative) for each proposed project, as seen by users and specialists. |
#36 P 153 | Contingency plan | Identifies changes that can happen in the near future and identifies actions that can/should be taken in individual projects if changes occur. |
#37 155 | Human resource plan | Assigns human resources to projects and defines an education plan associated with each. |
#38 160 | First drafts of project proposals | For each IS/IT project, a draft project proposal is formulated which describes the business reasons for initiating the project. |
Defining criteria for decision making | ||
#39 P 163 | A uniform set of selection criteria | Lists the criteria to be used in selecting IS/IT projects, e.g. fit with the organisational objectives and information needs, availability of resources (expertise, time and money) for execution, project costs and benefits. |
#40 165 | Weighing of the criteria | If level and importance of criteria differs too much then a weighing of the criteria can be defined. |
Authorising final decisions | ||
#41 P 167 | The concept of IS/IT portfolio | Describes the IS/IT portfolio with the highest score. Provides a tentative choice that can be communicated to relevant stakeholder groups. |
#42 P 170 | Stakeholder views on IS/IT portfolio | Documents the views expressed by different groups during a group (or bilateral) selection process. Summarises commonly accepted choices as well as controversial issues. |
#43 174 | Risk and value analysis | Summarises the risks and benefits of tentative IS/IT portfolio(s) as a whole and lists the projects in terms if risks and benefits/value. |
#44 179 | Final IS/IT portfolio | Describes the IS/IT portfolio that has been formally approved by top management. |
#45 P 182 | IS management coordination structure | Assigns responsibility of implementing the different projects and defines how the progress in implementing the plans will be monitored. |
Introduction
The “four cycle” method is a result of a research program on Information Strategy (IS) planning. The overall conclusion of this program was that a combined approach might work better than the use of either comprehensive or incremental methods for planning IS. The “four cycle” method divides a chosen period of time into four different planning cycles: Agree, Align, Analyze and Authorize and for each cycle the activities that could be executed in the next period are described.
This paper will discuss an activity of the fourth cycle namely: Impact on organisation and give an answer to some basic questions: what, why, when, who, and how.
What is “impact on organisation”
The fourth cycle concentrates on preparing clear proposals for action. The objective is to ensure firm commitment of resources to implement the IS project and to acquire the Information Technology (IT) resources and IS capabilities [Salmela]. One of the sub steps of this cycle is an analysis of the impact of the proposed projects on the organisation and the result of this analysis is described as:
“A list of implications (both positive and negative) for each proposed project, as seen by users and specialists [Salmela].”
In short you can say that the impact of a project on the organisation is the possible consequences of the project for the organisation and these can be positive or negative.
Why is an impact on the organisation analysis useful
An impact on the organisation analysis is import too make sure that no IT resources or IS capabilities are spilt with the implementation of a project. A prediction of the possible impact of the project on the organisation is necessary to make sure that no mistakes are made and knowing the possible consequences of the project for the organisation is of great importance for the decision to make. This prediction will not only protect the organisation against mistakes but can also bring up new insights for further research towards the possible use of IT in the organisation.
People should be involved because an IS projects concerns often different
groups of people like for instance management, users and designers. All parties have different
objectives and therefore their interests should be aligned to come to a success of the project. Planning
is also an important activity in which people are important. Before the project starts one should know
which persons are assigned to certain project tasks. These people resources can not be assigned to
different projects in the same period. If the IS project is executed for a customer and the project fails
completely or partly this may cause damage to the company’s reputation. [HOF02]
When?
The definition of impact on organisation says the impact should be performed for each proposed
project. This should happen in the first phase of the Systems Development Life Cycle (SDLC): project
identification and selection. The IS project should be classified and ranked in comparison with other
projects. An important method that can be used for this measurement is the value chain analysis
(Porter, 1985). In this analysis activities are analysed to determine their value added to products or
services and the costs that these activities bring along. Other methods that can be used for evaluating
2
projects in the first phase of the SDLC are strategic alignment, potential benefits, resource availability,
project size/duration and technical difficulty/risks. Strategic alignment is the extent to which the
project helps the organisation to reach is strategic objectives and long term goals. Potential benefits are
organisational benefits of the project like increasing profits, customer service and so on. Resource
availability is a method that determines the required type and amount of resources for a project and
their availability. The project size/duration determines the people that are needed and the time required
for completing the project. Finally the technical difficulty/risks are the limitations with respect to time
and resources for the project [HOF02].
How?
There are several ways to perform an organisational impact analysis of IS projects. Some of them like
the Critical Success Factor analysis (CSF), the Balanced Scorecard analysis, the assessment on project
feasibility and the Baseline Project Plan (BPP) are discussed in this section.
•The CSF analysis is a technique that is used for many purposes. One of aims is the linking of
candidate IS projects by means of critical success factors to objectives and therefore align the
projects with the business strategy.
•The Balanced Scorecard analysis is a method to measure performance from four related
perspectives: financial perspective, internal business perspective, customer perspective,
innovation and learning perspective. For each of the perspectives objectives can be set and
relevant measures to reach these objectives [WAR02].
•Another possibility of an organisational impact analysis is assessing project feasibility. In this
analysis the following different factors will be judged:
o Economic
o Technical
o Operational
o Schedule
o Legal and contractual
o Political
The result of the categories above determines whether a project is feasible or not.
•The BPP is the main result from the project initiation and planning phase. It contains the
project’s scope, benefits, costs, risks and the required resources for the project and this affects
the organisations as a whole.
•Some methods that can be used are already mentioned and explained above like the value
chain analysis, strategic alignment, potential benefits, resource availability, project
size/duration and technical difficulty/risks [HOF02].
After these analyses, the gathered information should be structured and studied by all participants of the analyses. When studied, this information should be converted into a list of advantages and disadvantages of the proposed project. This conversion could be done with brainstorming sessions (Osborn, 1963) or visual theme boards (Baxter, 1995). On the other hand can this information be used as input for writing possible scenarios about the outcome of the project and the impact of those outcomes for the organisation. This can be done with Scenario planning (Crawford, 1994).
Who should do an impact on the organisation analysis
On one hand there is the IS management team that could do the analysis. On the other hand there are the participants of the project team. Finally almost everyone can come up with advantages and disadvantages of the project plans for the organisation. Mainly it is important that everybody is heard and that all brought forward points are heard and used for the making the decision.
References
[HOF02] Hoffer, J.A., George, J.F., Valacich, J.S., Modern system analysis and design, 3rd
edition, Chapters 5 and 6, pp 134 – 191, Prentice Hall, 2002.
[Johnson] G. Johnson, K. Scholes (2002), Exploring Corporate Strategy sixth edition, Financial Times Prentice Hall Imprints.
[Porter1] M.E. Porter (1980), Competitive Advantage, Creating and sustaining Superior Performance, Addison-Wesley.
[Porter2] M.E. Porter (1980), Competitive Strategy± Techniques for Analyzing Industries and Competitors, New York: Free Press.
[Salmela] H. Salmela, T. Spil (2002), Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22, page 441-460.
Way 36. Contingency plan
Identifying possible near future changes, and the effects they can, or should have, on individual projects
By Thijs Munsterman
Preface
E-strategizing or information strategizing is an important part in an organization’s pro-active policy about ICT. Spil and Salmela proposed a “four cycle” information strategizing method that encompasses four different planning cycles: Agree, Align, Analyze and Authorize[SpS02]. To support these four cycles a total of 45 activities are given to enable better strategizing. This article will discuss one of the activities of the fourth and final cycle: the Authorization fase. The objective of this final cycle it to clear the way for the projects final proposal and acceptance. The activity discussed in this article is tool number 36: contingency plan. To generate this contingency plan an organization needs to do contingency planning. This article will discuss several aspects of this method by answering six basis questions about contingency planning: what, why, when, who and how?
What is contingency planning?
To generate a better understanding of contingency planning one first need to know its meaning. This way it can be placed in its proper context. Encyclopedia Britannica has the following entry on contingency[Bri05]:
1 : the quality or state of being contingent
2 : a contingent event or condition: as
a: an event (as an emergency) that may but is not certain to occur <trying to provide for every contingency>
b: something liable to happen as an adjunct to or result of something else
The part of interest for defining contingency planning is the second part. Contingency planning are all the things an organization does to limit the damage done by harmful events that it may not be able to avoid. Like for example making a plan to deal with a fire, the possible repercussions and ways to evacuate a building when an actual fire happens. By thinking ahead about potential problems a strategy for combating these events can be made. Important to notice is that this definition, in most cases and in this article, doesn’t include everything that is done to prevent the situation from happening. Most scientist define this as a security measure and it thus becomes a part of security planning. Contingency planning is about what to do when a situation occurs, not about preventing it[CPC92].
Why do contingency planning?
Contingency planning is about thinking ahead about events that may happen and that have some sort of negative impact on the organization. And because no organization wants to have its organization, resources or finances negatively effected it wants to do something about these effects. Contingency planning and the contingency plans are about identifying the possible risks and how the damage to the organization can be limited. When a company has plans for possible contingencies it is better prepared for the actual situation. By being prepared a company is able to minimize the negative impact of the situation.
When should contingency planning take place?
A good plan is only worth something when done in advance. Plans that are made up while a situation is developing never work as well as the plans made in advance. In an emergency it is difficult to think of all the possible implications and possibilities. By making a plan before the actual contingency happens an organization can think about possible effects, and have time to define and prepare the best solutions. This doesn’t mean a contingency plan should be made to far in advance. An effective contingency plan can only be made when (most) variables and effects are known. A contingency plan made without the right information is not very effective because it cant respond to a specific situation, because it wasn’t written with the specific situation in mind. A situation has to be known and understood in order to identify and prioritize risks. After that plans can be made to battle the effects of these contingencies.
Who is responsible for contingency planning?
The responsibility question can be divided into two separate responsibilities: the responsibility for writing and sustaining a contingency plan and the formal responsibility for executing and making sure there is a contingency plan. The actual contingency plans should be made by people with experience in risk assessment and access to information about the organization. The responsibility for this falls on the (IT)managers. The manager should be responsible for the contingency plan on a day-to-day basis and should evaluate the plan from time-to-time. The formal responsibility for the decision to write and execute a plan should be on top-management level. For example a CEO or board member should be given the responsibility over the contingency plan. In case of an emergency or problematic situation he or she can invoke the contingency plan and has the right hierarchical power to ensure the entire organization follows the plan. [Jor99]
How can a contingency plan be made?
A good contingency plan is made in advance and well thought through. Because of the complex nature of a good contingency plan it is best developed in a team. [Lyo96]
The organization alone is already very complex, making assumptions about possible risks and effects only makes it more complex. In a team certain problems areas, for example government issues, fire risks, electrical risk, can be divided to a more manageable size.
Another source of help can be found in checklists. The Association for Computer Machinery (ACM) is an important institute for advancing the knowledge and use of information systems in the world. Within the ACM there are several special interest groups. One of the is the Special Interest Group on Security, Audit and Control (SIGSAC). In 1976 they made a checklist for contingency and security planning. The checklist for contingency planning consist of 15 considerations about planning for future problems. With the help of this checklist an organization can verify its contingency plan [CPC92]
References
[Bri05] Encyclopedia Britannica, http://www.britannica.com, accessed 22/12/05
[CPC92] Checklist for security and contingency planning. SIGSAC Rev. 11, 1 (Jan. 1993), 3-16
[Jor99] Jordan, E. (1999) “IT contingency planning: management roles”, Information Management & Computer Security, 7/5(232-238)
[Lyo96] Lyons, A.L. (1996) “Contingency planning – Data processing” Computer Fraud & Security , Elsevier Science LTD, May 1996
[SpS02] Spil, T.A.M. & Salmela, H. (2002) “Dynamic and emergent information systems strategy formulation and implementation”, International Journal of Information Management, 22(441-460)
Way 37. Human resource plan
How affects the informated workplace an organization’s human resource management policy?
By Marijn van Schoote
Additions by Wouter Berends
Preface
This document will give a description of tool no. 37: The human resource plan. This will be done by the methodology of the ‘six honest men’, stated in the assignment.
What?
The tool human resource management plan can be used in the cycle identifying organizational implications. Its aim is to assign human resources to projects and defines an education plan associated with each. The fourth cycle concentrates on preparing proposals for actions. The objective of the fourth cycle is to ensure firm commitment of resources to implement the IS project and to acquire the IT resources and IS capabilities. [SPI2002]
Tool number 37 focuses on the human resource plan. According to John Bratton HRM is defined as follow:
“That part of the management process that specializes in the management of people in work organizations. HRM emphasizes that employees are the primary resource for gaining sustainable competitive advantage, that human resource activities need to be integrated with the corporate strategy, and that human resource specialist help organizational“[BRA1994]
The dedication of human resources should be in alignment with the corporate strategy.
Why?
IT can help people to do a better job, but only if they are willing to use the technology and if they become effective users. Unfortunately, many IT applications are misused, underutilized or abandoned. Even a good technical system may be sabotaged if it is perceived to interfere with an established social network. Thus, a good understanding of the intended end-users, their tasks, and the interdependencies between the two is a likely prerequisite for IS success.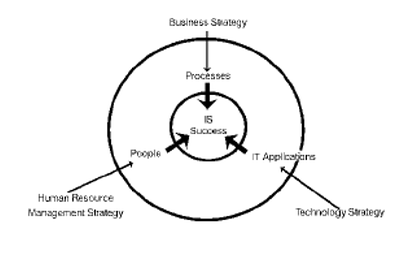
As depicted in the figure below an effective IS consists of the right IT application to help the right people perform the right process.
According to Hurst has the human resource element become the critical determinant of IS implementation success. [HUR1991]
When?
Muntslag states that the introduction of new IT in an organization and the organizational change often occur simultaneously. HR specialist should create awareness, having users participate in the process and providing staff training and re-development. Employee involvement in job redesign can raise motivation and lead to better performance [MUN2001]
How?
According to Martisons it is very difficult to overcome resistance to unwanted change simply through training or forced inducements. Instead, it is necessary to first establish the cultural and structural conditions which will be conducive to change. HR specialists can help to remove the threatening nature of a proposed IS and shape the expectations for the associated change. Lead users can be identified and asked to provide support during the implementation stage. Employees need to be told how the new IS will affect their jobs and, wherever possible, be given opportunities to gain experience without fearing mistakes. If HR specialists are reluctant to embrace a change, this will quickly be recognized by other staff. Resistance may then spread and quickly become entrenched. Once a favorable environment has been created, training can help to facilitate the change process.
According to Martisons HR specialists may assume one of the three following roles during the IS implementation/adoption process: reactive, supportive and proactive. These roles are depicted in the figure below.
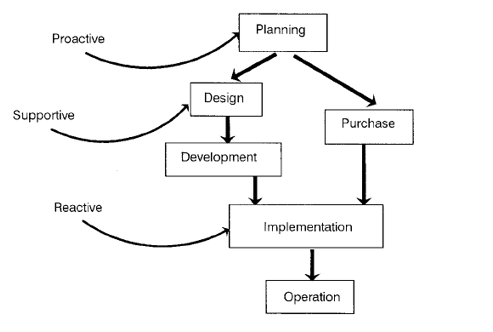
In the reactive role, the involvement of HR specialists is restricted to the actual implementation of the new IS system. In the supportive role, HR problems where anticipated and policies to either prevent or deal them can be developed. In the proactive role, HR specialist are involved form the IS planning process till the final implementation. They assist in designing new systems by considering HR issues and they assist in the final implementation project.
Dewulf (2002) states that resolving change problems is reached by creating a tension which should encourage employees to change. He has identified three levels of tension which should encourage employees to change:
•Creative tension, this exists when one realizes that there is a gap between the current vision and reality
•Task tension, this exists when one realizes that there is a gap between the current way of working and the future way of working.
•Learning tension, this exists when one realizes that there is a gap between the current competencies and the future competencies.
Dewulf(2002) attaches an organizational level to each of these tension. Creative tension plays a major role on executive level. Task tension plays a major role on managerial level and the learning tension on the individual employee level. But he also states that these kinds of tensions also exist on a personal level.
Beretta (2002) says that process-based performance measurement systems can help to make process performance relevant to individuals. The company has to translate their vision to the task of the different departments and individuals creating an organizational task tension. Financial incentives can be put on process-based performance measures to make these more personally important for individuals, matching the organizational task tension with the personal task tension. This way a process based measurement system can accommodate the adoption of a process view by creating personal learning tension in the direction of a process view.
Where?
Munslag states that introduction of IT in an organization involves top management and user participation. User participation can be obtained by involving the HR department.
Who?
Clegg and Kemp (1986) argue that HR specialists can significantly contribute in managing the introduction, context, and evaluation of IT applications. They may provide input on the relative appropriateness (in behavioral terms) of different technologies, the best approaches for introducing, integrating, and institutionalizing them, and the motivation and control measures that will encourage desired outcomes. However, HR specialists must recognize and understand the human factor issues associated with the IS adoption process before getting involved [CLEG1986].
HR specialist should define the training programs. Several types of training can be used to realize the business goals. These types can be split up in Type A and Type B.
Type A learning involves a straightforward method like “what buttons do I have to push”. Type B involves more the effective use of the system and ergonomic regulations.
2.1 Case MANCO
IST situation,
Manco had been conducting business for more than 17 years, and many of the procedures and functions in use had become outmoded. Since the early years of its establishment, some of the company’s major operations, such as production, sales, shipment, and inventory, had been supported by one application system written in a third-generation language. There were also a number of loosely coupled departmental and application-specific systems. Manco recognized the need to increase empowerment, accountability and ownership. Management realized that the key to combating its new organizational challenges would be to renew the current outdated IT infrastructure and migrate to a new, flexible application system that would empower its business operations and make them more responsive to customers’ needs.
ES and integration,
Manco decided to implement an appropriate IT package in conjunction with a BPR (Business Process Resesign) project. SAP R/3 was found to be the best ES package which could support Manco’s medium and longer-term requirements.
Gaps according to the case from a HRM viewpoint,
The implementation of SAP R/3 within the Manco group is overall considered as a failure. The persons that were conducting the implementation had a difficult time persuading lower echelons to be active in the change process, one reason for this was that charting the important processes within the implementation process and thus identifying the stakeholders within these processes, was hardly conducted. Management failed to give sufficient credence to its employees’ distress that was generated by massive change.
There was no formal communication strategy that identified effective mechanisms ensuring the distribution of the rationales and plans behind the change process.
2.2 Case Roll-Royce
IST situation,
Rolls-Royce made a couple of acquisitions which allowed the company to consolidate the market, this was one of the reasons that Rolls-Royce used over 1500 systems which were mostly developed internally. As a result these (legacy) systems were expensive to operate and difficult to maintain
ES and integration,
The implementation process of the Enterprise System was specifically strained, for it was conducted by a project team that consisted out of three companies (Rolls-Royce, EDS and SAP consultants) and resulted in cultural problems. The project had a high acceptance in the area where the old system fell short, however some functions and processes will not get the functionalities that the old application had and thus there will be more resistance in using the new system.
Gaps according to the case from a HRM viewpoint,
The implementation seemed a huge success, however there were problems during the implementation process which were:
•Cultural problems, The implementation project team expected a high acceptance of the system. However some functions and processes did not get the full appreciation the legacy systems once had, this was cause for extra concern within the project team.
•Business problems, SAP R/3 requires a fairly rigid business structure for it in order to work successfully. The user would have to change their working practices in order to be able to work with SAP.
3 How should the tool be used in the cases
When looking at the tool provided by Marijn van Schoote, it shows how a HRM specialist can engage the change process, this can be done in three approaches that was defined by Maritsons (1999): Proactive, Supportive and Reactive.
The HRM approach used in the (unsuccessful) MANCO case was barely Reactive. Project management believed that more communication should have taken place in order to persuade every one to participate, the underlying reason for not participating was largely due to lack of support from the human resources (HR) department. The MANCO case should (from a HRM viewpoint) have been supported in an proactive approach, using the Martisons model the HRM specialist would than have been active from the planning process, and thus for instance could have determined who were the important stakeholders with the important processes, these HRM managers could then put pressure on these persons, ensuring a better chance of success.
The approach used by the (successful) Rolls-Royce case was Supportive, the project team decided to resolve resistance by illustrating the improvements made to the company as a whole, thus breaking the traditional segregation of departments, they furthermore stepped up the original implementation plan in an attempt to address training and cultural changes.
References
[BRA1994] Bratton, J., Gold, J. (1994). Human resource management: theory and practice. London:Macmillan
[CLEG1986] CLEGG, C., & KEMP. N. Information technology: Personnel, where are you? Personnel Review, 1986, 15, 1, 8-15.
[HUR1991] HURST, B. F. Facilitating change : The key to success. CIO, 1991, 3(4), 39-46.
[MAR1999] Martinsons, M.G., Chong, P. K.C., The influence of human factors and specialist involvement on information systems success, Human relations, 1999, vol52 No 1, 123-152
[MUN2001] Muntslag, D.R. (2001). “The Art of implementation”. Inaugural lecture. Chair in ERP Implementation and Organizational Change at the University of Twente
[SPI2002] Salmela, H,& Spil, TAM (2002)"Dynamic and emergent information systems strategy formulation and implementation", International Journal of Information Management, 22, pp. 441-460
Al-Mashari, M. and Zairi. M. (2000), “Information and Business Process Equality: The Case of SAP R/3 Implementation”, The Electronic Journal on Information Systems in Developing Countries,”Bradford.
Beretta, S. (2002), “Unleashing the integration potential of ERP systems. The role of process-based performance systems”, Business Process Management Journal, Vol.8 No.3.
Dewulf, L. (2002), “Motiveren van medewerkers voor leren, werken en veranderen Opbouwen van spanning tussen visie en realiteit”, In Opleiding & Ontwikkeling, Vol. 3.
Maritsons, M.G., Chong, P.K.C., (1999) “the influence of human factors and specialist involvement on information systems success, Human relations, vol52 No 1, 123-152”
Yusuf Y., Gunasekaran A., Abthorpe. M. (2004), “Enterprise information systems project implementation: A case study of ERP in Rolls-Royce”, International Journal of production economics, Vol 87 Pag. 251-266.
Tool 38. First drafts of Project Proposals
By: Maria Karla Simental Vera
On basis of Sarah Schmidt
The Project Proposal is the initial document that converts an idea or policy into the details of a potential project, including the outcomes/benefits, outputs, major risks, costs, stakeholders and an estimate of the resourcing and time required [3].
Creating a draft for such a document should be done carefully since the information it contains will represent the basis for a preliminary evaluation on whether to continue to the next step or not. So in order to supply a good foundation for taking an informed decision, the data included in this DRAFT should be presented as clear, short and accurate as possible.
It is advised to make clearly visible how would the potential project deliver benefits to the business. This way, stakeholders would get confidence in investing on the potential project [1].
As result of an investigation on different worldwide recognized methodologies for project management [4], [5] and [6], and some literature research [1] and [2], the following template was formulated to facilitate the creation of a Project Proposal DRAFT.
Descriptive project name. | |
Summary of the situation that gave rise to the initiation of the project. | |
Explanation of the aims and objectives of the project. Objectives should be clear, concise and measurable. | |
A clear definition of the boundaries of the project. To avoid misunderstandings it is often useful to state what is not included within the scope. | |
List the critical factors (Examples: Report must be readable by non-technical staff or Infrastructure should be fully resilient, or Equipment should be limited to x supplier, etc.). | |
A list of the tangible results of the project (Examples: Technical design for x service, or Documentation of processes to be followed by support staff ). | |
Things which may limit or hinder the project and are outside the control of the project. | |
List all the potential events that could prevent the project meeting its objectives or timescales. If possible specify fallback plans or mitigating factors to overcome the risks. | |
Identify the Steering Committee or Project Board. Identify the key roles that need to be fulfilled to set up a project team (when applicable include reporting lines); each role should be described in terms of major responsibilities / accountabilities. | |
Enter project initiation date, milestone dates and project closure date. [2] | |
•Operational value investment: Cost of the Day-to-day running operations generated by this project (note it could be negative when the project delivers savings!). •Strategic value investment: If the project has a component that would enhance the performance of the business and help in long-term revenue generation (for example, the cost of a “supplier management system” might increase control over the goods or services delivered and therefore being seen as a strategic value investment). •Threshold investment: These investments may have at first glance negative return of investment but are needed for competitive survival. (for example, the cost of having a 0800 line for customer support). •Infrastructure investment: Typically this includes cost of internal networks, links to suppliers, applications development cost, etc. Note that not always all the type of investments apply, only use the ones that are relevant to the project [1] | |
The total amount of estimated effort to be spent only during the time that the project will run (operational run and maintain costs, should be excluded from this box and noted as an investment on the box above). Include the expenses you might generate by staff tariffs (include the unit used to do the calculation: hours, days, weeks, etc. and the tariff associated to it). Total budget required for common activities: traveling, external consultancy, training, etc. Plan for contingency budget and make clear that these figures are estimates and that they would become more definitive as the project progresses. | |
Provide an overview on how the following activities will be performed and informed to the Project Team and Steering Committee or Project Board. •Tracking progress •Comparing actual to predicted (costs, time and deliverables quality) •Analyzing impact of diversions. •Making adjustments (formalize, who needs to provide approvals for change scope, more budget, etc). [2] | |
Define how successful completion is to be confirmed/measured. |
The template is pretty straightforward and aims to be self-explanatory, however in the paragraphs below a short description of its structure and how it should be used is presented.
How is the template organized?
On the left column a title of the information that should be presented in that row is given (should remain as it is presented in the template). On the right column an explanation and in some cases examples on the kind of information that should be included are provided.
How to use the template?
When using the template, it is expected that the user will replace the text on the right column with the applicable information for the particular “potential project” (still on DRAFT Proposal) and submit it for approval to the relevant organizational parties.
Happy Project Management and success in delivering!
Sources:
[1] E-Business and E-Commerce Management
Dave Chaffey ISBN 0273 65188 9
Prentice Hall. England 2002.
Chapter 5: E-business strategy (Investment appraisal, page 206)
[2] Becoming a Master Manager A Competency Framework
Robert E. Quinn, Sue R. Faerman, Michael P. Thompson, Michael R. McGrath
ISBN 0-471-36178-X
John Wiley & Sons, Inc. USA 2003.
Chapter 5: The Coordinator Role (Competency 1: Managing Projects, page 138)
[3] Tasmanian Government Project Management Guidelines Project Management by Tasmanian State Government
March 2005, Tasmania State.
http://www.projectmanagement.tas.gov.au/pm_templates/pm001_projectproposal.htm
[4] Complete set of PRINCE2 Templates
PRINCE2, by the Office of Government Commerce.
June 2003, UK.
http://www.ogc.gov.uk/prince2/downloads/view.htm
[5] The Project Management Institute
http://www.pmi.org/pmief/media/presentation.swf
[6] Masters Certificate in Project Management
George Washington University School of Business & Public Management
http://www.esi-intl.com/public/ITprojectmanagement/index.asp
http://www.gwu.edu/~business/mspm/index.cfm?pg=programInfo/professionalAssociations.cfm
Way 39: A uniform set of selection criteria
By Jogchem de Groot, revised from Koen Voermans
When project proposals for different or alternative projects have been formulated it’s important that they are evaluated against the enterprise wide and strategic focus of the organisation in order to only execute the best alternatives. Defining a uniform set of selection criteria to compare projects of different types to each other makes up a necessary part of an IS/IT investment management process.
What is a uniform set of selection criteria?
The output of this step is a list of criteria to be used in selecting IS/IT projects, e.g. fit with the organisation’s strategic goals, objectives, mission and information needs, availability of resources (expertise, time and money) for execution, project costs and benefits (Spil, 2002). These criteria should be applied as uniformly as possible throughout the organisation to ensure that decision-making is consistent and processes become institutionalised.
Why is a uniform set of selection criteria needed?
Because of the rather low rate of successful IS/IT projects, project proposals should be evaluated and only the best alternatives should be selected. This evaluation can be supported by a uniform set of selection criteria. Without selection criteria, projects may be selected on the basis of isolated business needs, the type and availability of funds, or the receptivity of management to a specific project proposal.
When should a uniform set of selection criteria be developed?
The set of selection criteria should be created or updated during fourth cycle of the four-cycle method, the authorize cycle (Spil, 2002). The fourth cycle concentrates on preparing clear proposals for action. This tool is best used in the second sub phase of the fourth cycle: defining criteria for decision-making.
How can a uniform set of selection criteria be developed?
The IT Investment Management (ITIM) Framework developed by the Government Accountability Office (GAO, 2004) suggests that, in order to successfully develop and maintain IT portfolio selection criteria that support an organisation’s mission, organisational strategies and business priorities, two organisational commitments are required:
1.The organisation has documented policies and procedures that outline a systematic process for creating and modifying IT portfolio selection criteria. For larger organisations this may typically include:
oobjectives for the portfolio management process
oa link to the organisation’s strategic plans, budget processes and enterprise IT architecture
okey information required to create or modify the selection criteria
osuggested investment and proposal selection criteria
otriggers for initiating change in the selection criteria
oa list of people to whom the selection should be distributed
2.Responsibility is assigned to an individual or group for managing the development and modification of the IT portfolio selection criteria. This is critical because it creates a point of focus for the successful implementation of this critical process.
Additionally two prerequisites should be fulfilled:
1.Adequate resources, including people, funding and tools, have been committed for portfolio selection criteria activities.
2.A working group has been designated to be responsible for developing and modifying the IT portfolio selection criteria.
Now the set of selection criteria can be defined by this individual or working group. The selection criteria should be linked directly to the organisation’s broader mission, goals, strategies and priorities. ITIM defines four areas of focus:
•Cost, which may include life cycle costs broken apart into initial costs, ongoing development costs and indirect costs.
•Benefit, which may include tangible and intangible benefits estimated using a variety of techniques, e.g. cost/benefit analyses using net present value, return on investment, etc..
•Schedule, which may include the life cycle schedule and the schedule of benefits.
•Risk, which may include investment, organisational, funding and technical risks.
These criteria can be extended or supplemented by the criteria for project initiation and planning described in Hoffer (Hoffer, 2002):
•Technical, which may include identifying the organisation’s ability to construct the proposed project (hardware, software, system size, complexity and group’s experience with similar systems). This falls under the ITIM risk criteria.
•Operational, the degree to which a proposed system solves business problems or takes advantage of business opportunities. This falls under the ITIM benefit criteria.
•Legal and contractual, which may include potential legal and contractual ramifications due to the implementation of a project. This falls under the ITIM risk criteria.
•Political, which may include an evaluation of how key stakeholders within the organisation view the proposed project. This falls under the ITIM benefit and risk criteria.
If the investment decision making process is managed by a small group, and if the objectives for the organisation’s IT investments are stable, selection criteria can be developed once and modified incrementally year-to-year by the same small group. In large decentralized organisations with diverse and evolving objectives, it’s much more important to solicit input to the development of the selection criteria. It is important that when an organisation’s mission or business needs and strategies change, these criteria are re-examined.
When the set of selection criteria has been formulated three more important activities remain (GOA, 2004):
1.The set of selection criteria should be approved by the enterprise wide IT investment board.
2.Project management personnel and other stakeholders involved in the projects should be made aware of the selection criteria. This is especially important for the people writing the project proposals, so that they can be written with the selection criteria in mind.
3.The set of selection criteria should be regularly reviewed, using cumulative experience and event-driven data, and modified as appropriate.
References
(GAO, 2004) United States General Accounting Office, GAO-04-394G: “INFORMATION TECHNOLOGY INVESTMENT MANAGEMENT: A Framework for Assessing and Improving Process Maturity: Executive Guide”, March 2004, USA.
(Hoffer, 2002) Jeffrey A. Hoffer, Joey F. George, Joseph S. Valacich, “Modern Systems Analysis & Design”, Prentice Hall, New Jersey, 3rd edition, pp. 168-183, 2002
(Spil, 2002) Ton A. M. Spil, Hannu Salmela, “Dynamic and emergent information systems strategy formulation and implementation”, In International Journal of Information Management, 22, pp. 441-460, 2002
Way 40. Weighing of criteria
By Gerrit Jan van der Schoor
The four cycles method is a method to formulate and implement an dynamic and emergent information systems stragegy (Salmela & Spil, 2002). The method provides a basic schedule for organizing planning activities. The basis of this method are four cycles. Weighing of criteria is a method in the fourth cycle of the four cycles method. The fourth cycle ,wich is the last cycle, consists of authoring actions. It concentrates on preparing clear proposals for action. Defining criteria for decisions-making is an important task in the last cycle.
A uniform set of selection criteria can be defined, which are used in selecting Information System projects. The criteria can be for example: benefits, project costs, information needs, availability of time, expertise and money. It could be that level and importance of the criteria differs too much. In that case it is very difficult to make a decision. A weighing method of the criteria could provide a better basis for decision making.
Once criteria are chosen, the decision makers must place importance weights on each chosen element, but little help is given in the literature. The weighting of criteria is a critical step, since an improper selection of weights can radically alter the selected portfolio (Jiang & Klein, 1999).
The technique which we will use to analyse and weight IS projects is based on the Simple Multi-atrribute Rating Technique (SMART) (Goodwin & Wright, 1991). Because of the simplicity of both the responses required of the decision maker and the way in which these responses are analyzed, SMART has been widely applied. The analysis involved is transparent, so the method creates an enhanced understanding of the problem and be acceptable to the decision maker who is distrustful of a mathematical ‘black-box’ approach.
The cost of this simplicity is that the method may not capture all the detail and complexities of the real problem. Nevertheless, in practice, the approach has been found to be extremely robust.
The are different stages in analysis. We will start by stage 4 because the first three stages are about identifying the decicion maker, identifying alternative courses of action and identifying criteria which are relevant to the problem. This is considered to be done before actually weighing the criteria.
The following stages are discussed here:
Stage 4: For each attribute, assign values to measure the performance of the alternatives on that attribute.Stage 5: Determine a weight for each attribute. Stage 6: For each alternative, take a weighted average of the values assigned to that alternative.
Stage 4: Assign values
There are attributes such as benefits, durability which are difficult to be quantified. Because of this, there are two alternative approaches which can be used to measure the performance on these attributes: Direct rating and the use of value functions. By direct rating the decion maker gives a value between 0 and 100 is given to an attribute such as benefits. The space between the values gives his strength of preference for one project over another in terms of benefits. It should be noted that this is an interval scale.
Value functions are used when the information can be quantified such as time. The idea is to sort the projects first on the basis of a criteria.. Then add values to each to each attribute between 0 and 100. In this way a value function can be constructed with value on the vertical axis and the criteria on the horizontal axis.
Stage 5: Determine a weight for each attribute
After for each attribute values are assigned, one can define the weights for each criteria. Here we are using swing weights to attach the weights. These are derived by asking the decision maker to compare a change (or swing) form the least-preferred to the most-preferred values on one attribute to similar change in another attribute. The best method is to rank the criteria form the most important to the the less important criteria and then add values to each criteria. In the figure below an example of an office location problem illustrates this.
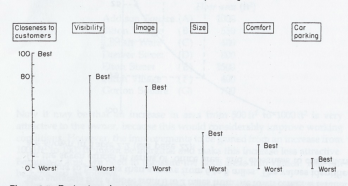
The problem is that the weights don’t add up to 100. This problem is solved by normalization: dividing each weight by the sum of the weights and multiplying by 100.
Stage 6: Aggregating the weighted attributes
We have now a measure of how well each project performs on each criteria and the weights which enables us to compare the values allocated to one attribute with the values allocate to the others. This means that we are now in a position to find out how well each project performs overall by combining the scores allocated to each project.
To calculate the scores of each project we will assume that the additive model is appropriate. This involves adding the weighted values scores (weights multiplied by the values) to obtain the overall score of each project. These aggregated scores on the project can be used in the decision process on selecting an IS/IT portfolio.
References
Goodwin, P., & Wright, G. (1991). Decision Analysis for Management Judgment, New York: Wiley.
Jiang, J.J., & Klein, G. (1999). Project selection criteria by strategic orientation. Information & Management, 36, 63-75.
Salmela, H., & Spil, T.A.M. (2002). Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management, 22, 441-460.
Introduction
This paper will give a description of tool no. 41: The concept of IS/IT portfolio. This will be done based on the application portfolio concept of Ward & Peppard. [WAR02]
What?
According to Ward & Peppard, the applications portfolio concept, can be seen as a means of bringing together existing, planned and potential information systems and assessing their business contribution.
They depict a composite 2 x 2 matrix (Figure 12), consisting of a number of matrices, produced to help management decision making with respect to IS/IT planning, utilization and resourcing. The matrices they have combined are the Sullivan matrix, the Information Assessment and Adoption (ITAA) matrix , two matrices developed by Ives, Learmonth and Galliers, and the e-business value matrix’ described by Hartman and Sifonis.
Figure 12: Composite matrix [WAR02]
Why?
Although precision should not be expected from the IS/IT portfolio concept, it can be seen as a relevant guidance to enlighten and support management decision making in an area which is often fraught with uncertainty and even conflict.
It is a valuable ‘framework’, which helps to link together and reconcile the complexities involved in managing the demand and supply components of the IS/IT strategy, in particular to achieve ownership by business managers of there IS/IT applications and the issues that have to be addressed in achieving success. [WAR02]
Describing the existing and future applications in a portfolio concept leads to the achievement of a consensus among executive management, line managers and the IT management on the content of the IS strategy.
Once the portfolio is understood and agreed, decisions on how best to manage each application, both existing and future, can be made, along with overall decisions on the use of resources across the portfolio and the selection of the most effective sources for supply – which aspects should be managed in-house and which can be outsourced. [WAR02]
When?
According to the four cycles method, the development of the IS/IT portfolio should be done during the last cycle, ‘authorizing actions’. This fourth cycle is divided in three sub phases, Identifying organizational implications, Defining criteria for decision making and finally Authorizing final decisions. This tool can be classified to the third phase.
How?
The process of classifying the applications is as important as the end result, since the discussion involved will enable different perspectives to be understood (and hopefully reconciled!) and the implications of the decisions made to be appreciated by all parties. [WAR02]
Each organization will have slightly different interpretations of the terms used for each segment. Hence, a decision-support tool that would fit every organization’s criteria for classification cannot be defined. [WAR02]
However, Ward & Peppard are proposing a simple starting point for the process, which contains a couple of questions and the interpretation of them, both mentioned below. But it should only be used to guide the assessment, not as a ‘rule book’.
Questions
If the development* succeeds, will it:
(a) | Result in a clear competitive advantage for the business? | Yes / No |
(b) | Enable the achievement of specific business objectives and/or critical success factor? | Yes / No |
(c) | Overcome known business disadvantages in relation to competitors? | Yes / No |
(d) | Avoid foreseeable business risks becoming major problems in the near future? | Yes / No |
(e) | Improve the productivity of the business and, hence, reduce long-term costs? | Yes / No |
(f) | Enable the organization to meet statutory requirements? | Yes / No |
(g) | Provide benefits not yet known, but may result in (a) or (b) above? | Yes / No |
* For existing applications the question is, is the application delivering benefits that…
Interpretation
The table below shows how the answers can be interpreted and the application classified, based on whether or not any Yes answers appear in a column.
If more questions produce a Yes answer in any one column (i.e. the application appears to be in more than one category), then it should be reassessed by splitting it into its major components and considering each of them in the same way (i.e. the application should be broken down into subprojects). If this is not done, the risks of failure will increase dramatically due to the mixed objectives and the confusion that it can cause once the project proceeds.
High potential | Strategic | Key operational | Support | |
(a) | Yes (i) | |||
(b) | Yes (i) | |||
(c) | Yes | |||
(d) | Yes | |||
(e) | Yes | |||
(f) | Yes (ii) | Yes (ii) | ||
(g) | Yes |
(i)If either applies, the supplementary question is then, ‘Is it clear what the business benefits are and how they can be obtained?’ if Yes it is Strategic, if No it is High Potential
(ii)To clarify which it is, the following question should be asked, ‘Will failure to comply lead to significant business risks (be specific about the risk)?’ If Yes it is Key operational, if No it is Support.
If agreement cannot be reached, it often means that the ‘system’ needs to be considered at a lower level, in terms of the main functions it performs.
Although many applications are often provided via large packages (e.g. ERP and CRM software), the purpose of the analysis is still to classify the business activities that the package covers (e.g. order processing, purchasing), rather than the package itself. [WAR02]
The main purpose in classifying applications is to ensure that they are managed successfully and that the expected contribution is delivered. Based on the issues relevant to each segment, appropriate implementation strategies can be adopted. [WAR02]
Where?
This tool can be useful for every organization that wants to have a good and common understanding of the existing, planned and potential information systems and their contribution to the business.
Who?
The development of the portfolio concept has to be done by the management. According to Salmela and Spil [SALM02] the IS/IT portfolio with the highest score provides a tentative choice that can be communicated to relevant stakeholders groups.
References
[SALM02] Salmela, H. & Spil, T.A.M. (2002). “Dynamic and emergent information systems strategy formulation and implementation”. International Journal of Information Management 22, 441-460
[WAR02] John Ward , Joe Peppard, Strategic Planning for Information Systems, John Wiley & Sons, Inc., New York, NY, 2002
Way 42. Stakeholder views on IS/IT portfolio
By Chris Brandhorst
On basis of Stefan Fountain
Introduction
In the process of creating a successful information systems strategy it is important to involve the stakeholders. The way different stakeholders feel about the IS/IT portfolio influences and
possibly can predict the success of the strategy. It is therefore necessary to get insight in the
(possibly conflicting) views of the different stakeholders by researching and documenting the
views expressed by all the groups that are affected by the chosen strategy or strategies. During a group (or bilateral) selection process we document the views of the stakeholders from which we summarise the commonly accepted choices of the IS strategy as well as the controversial issues that may exist [Sal02]. In this document we describe the outcome of this documentation as well as the process of reaching it. To describe it correctly we will answer the following questions:
1. Why are the stakeholders views important to the IS strategy?
2. Who are the stakeholders that we want to know the views of?
3. What information needs to be recorded, how is this information to be gathered and what
can be done with it?
4. When is this information to be gathered?
Each of the question will be addressed in the following paragraphs.
Importance to strategy
There is many literature available stating that the opinions of stakeholders are critical to the
success of the IS planning process or the IS itself. For instance, [Abr93] discusses a method to
predict the success or failure of an IS using the expectations of the stakeholders. Failure to
observe and manage these expectations, may very well lead to the failure of an IT project [Sch01]. Thus expectation management is a critical risk management strategy [Bac04].
The opinion of the stakeholders (and thus the success of the project) is influenced by a number of factors. First of all, people naturally resist change for reasons like self interest, lack of understanding and trust of the new situation, uncertainty and the fact that they have different assessments and goals [Daf00].
Secondly, studies indicate that the amount of involvement the stakeholders have in the IS process positively effects the outcome of the process. [New03] states that one of the strongest inhibitors to strategy implementation is the lack of user involvement during the implementation.
Finally, and perhaps most important, different stakeholders have different views of the same IS process [Teo01]. They perceive key IT management issues differently [Lee03], “parties involved in IS development bring different frames of reference to the situation” [Bostrom 1989, as quoted by [Ruo91]] and different stakeholders look for different outcomes of the process, because of different reasons for wanting an ISP study [Ruo91].
Often problems arise form these different views because they are contradictory, based on
individual preferences [Ruo91] or are based on different criteria for IS effectiveness [Sed98].
[Lee03] states that these conflicts between stakeholders negatively affect the IS planning process. To illustrate, [Lac95] presents a study in which was analysed what targets the three key IS stakeholder groups set for information systems. The groups are senior management, user management and IS management ([Ruo91] identified the same key groups, so did [Abr93], for the bigger part). The goal of the senior management with IS was to minimize costs. User management wanted service excellence. This caught the IS department in the middle, because these views implied that they were to “provide a Rolls Royce service at a Chevrolet cost” [Lac95].
This example shows the danger of not addressing the conflicting views problem: IS managers are placed in hostile environments were they most probably won’t meet all the conflicting demands, causing an improper alignment between business and IT [Lee03]. This may motivate IS mangers to manipulate the results of the IS process “to justify their performance to various stakeholders” [Lac95], which of course can cause the same misalignment.
In order to overcome this problem, the views of the different stakeholders must be analysed and, where possible, brought closer to each other. “Successful ISIP requires sound communication and the interpretation of these different views” [Ruo91]. Frequent communication with stakeholders creates a common frame of reference and communication between stakeholders may put groups close to each other and understand each others stakes [Lee03].
When not all conflicts can be resolved, the results of this tool can be used when making a risk
and value analysis. If a certain aspect of the IS strategy is too conflicting, it can be worth reevaluating this part before implementing. Finally, the views of the stakeholders may (according to [Abr93]) predict the outcome of the IS projects that are present within an organization.
Choosing stakeholders
It is important to identify all the stakeholders in the IS planning process, right from the top
management to the operational levels. “IS planning exercises are unique in that they require
intense collaboration of various stakeholders” [Teo01]. One of the risk factors that [Sch01]
identified was the “failure to identify all stakeholders”. In the four-cycle method set out in
[Sal02], choosing the right participants is the third step in the first cycle. However, participants are not the same as stakeholders. The first group is actively involved in the IS strategy planning process, but the latter may not be (like end-users). Although an IS strategy is, from an end-user point-of-view, a very high-level affair, the choices that are made can influence the way the user has to work a great deal.
Thus, besides the methods for selecting skilled people and define groups to be interviewed that are mentioned in [Sal02], research has to be done to identify all the groups in the organization that are influenced by the IS strategy in one way or the other.
Recording and alignment of views and predicting IS strategy outcome
According to [Ruo91] and as is clear from the above, “stakeholder groups should be observed at two levels. First, at stakeholder level […] and secondly at inter-group level”. Combining what was said above, the execution tool consists of three parts:
1. Recording of the views of the different stakeholders;
2. Creating a common perspective on the IS strategy as much as possible;
3. Observing all the exceptions of the common perspective.
Recording and aligning views
Which aspects of the stakeholder views need to be recorded are mentioned in various sources:
- Roles, responsibilities and expectations of each stakeholder. According to [Schi01] a
miscalculation of these factors is often reason for the failure of software projects. The
way the stakeholders see their own roles can be compared with the way the IS strategy
sees their roles and possible adjustments can be made. This information can also be used
to inform (or warn) stakeholders when they have the wrong expectations of their roles.
- Risk factors involved according to each stakeholder [Schi01]. Stakeholders may see
risks in projects which the IS strategy planning manager or team did not notice.
- Objectives of the IS/IT strategies according to each stakeholder [Sal02]. Once
again, for comparing these views to the IS strategy;
To begin with, the views of a random sample of the different stakeholders can be acquired by
various means, for instance interviewing or question forms. When a global impression of the
views is available, and thus also the discrepancies between the views, a group process or bilateral process can be started to create a common perspective as much as possible. When stakeholders are involved in the process, they will be more prepared to understand the stakes of the other groups, reach consensus in plan formulation and be more patient [Teo01].
To achieve this, whichever form the process may take, it “should allow ample opportunity for
debate and airing of different views” [Checkland, 1991, Galliers, 1987 as quoted by [Sal02]].
Furthermore, “[m]anagement education is needed to integrate the different views of managers
concerning the use of IT” [Ruo91].
The remaining contradictory views must be properly documented so that they can be taken into account in the remainder of the IS strategy planning process, for instance in a risk-value analysis of the IS/IT portfolio.
Predicting IS strategy outcome
According to [Abr93], the expectations that stakeholders have, the fact that they can be changed or not and the competences of the organisation may predict the success or failure of the IS implementation (success is defined as acceptance, use, satisfaction and value). Abreu’s and Conrath’s model (see Figure 1) focuses on expectations, specifically those of the three already mentioned key stakeholder groups. “The fundamental premise is that a precondition for IS implementation success is the existence of positive, realistic and compatible expectations held by each of the three stakeholder groups. These in turn are dependent upon the organization’s competence in designing an IS and competence in introducing it”. Expectations can be changed and when an organisation demonstrates competence in systems design or implementation, such a change can occur.
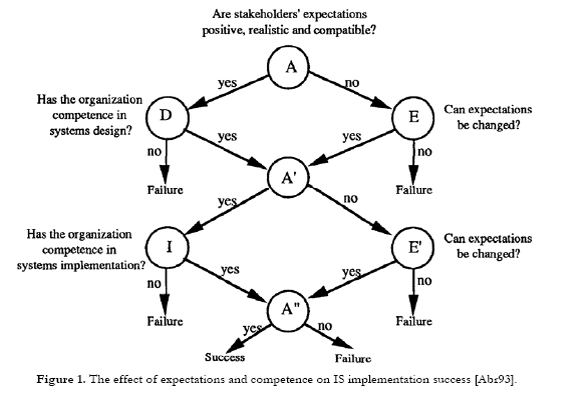
Figure 1. The effect of expectations and competence on IS implementation success [Abr93].
No one-time tool
As stated above, the opinions and expectations of stakeholders can be very important to the
success of the IS/IT portfolio coming forth from the IS strategy planning process. Therefore, it is advised not to make the documenting of the views of stakeholders a one-time, one-point
activity. In order to be able to respond rapidly to negative and conflicting opinions and unrealistic expectations, continuous monitoring of the views is necessary. This may take some more effort, but the activity will show its value when the views of stakeholders are out of line with the strategy.
References
[Abr93] Abreu, A.F., Conrath, D.W., The role of stakeholders’ expectations in predicting information systems implementation outcomes, Proceedings of the 1993 conference on Computer personnel research, StLouis, Missouri, United States, 1993, p. 408-415
[Bac04] Baccarini, D., Salm, G.S., Love, P.E.D., Management of risks in information technology projects, Industrial Management & Data Systems, Vol. 104, N. 4, 2004, p. 286-295
[Daf00] Daft, R.L., Management, 5th edition, Hartcourt College Publishers, Fort Worth, USA, 2000, p.371-377
[Lac95] Lacity, M.C., Hirschheim, R., Benchmarking as a strategy for managing conflicting stakeholder perceptions of information systems, Journal of Strategic Information Systems, Vol. 4, I. 2, June 1st 1995
[Lee03] Lee, G.G., Pai, J., Effects of organizational context and inter-group behaviour on the success of strategic information systems planning: an empirical study, Behaviour & Information Technology, Vol. 22, No. 4, July-August 2003, p. 263-280
[New03] Newkirk, H.E., Lederer, A.L., Sri, C., Strategic information systems planning: too little or too much?, Journal of Strategic Information Systems, Vol. 12, I. 3, October 2003, p. 201-228
[Ruo91] Ruohonen, M., Stakeholders of strategic information systems planning: Theoratical concepts and empirical examples, Journal of Strategic Information Systems, Vol. 1, No. 1, 1991, p. 15-28
[Sal02] Salmela H., Spil, A.A.M., Dynamic and emergent information systems strategy formulation and implementation, International Journal of Information management, Vol. 22, I. 6, 2002, p. 441-460
[Sch01] Schmidt, R., Lyttinen, K., Keil, M., Cule, P., Identifying Software Project Risks: An International Delphi Study, Journal of Management Information Systems, Vol. 17, No.4, Spring 2001, p. 5-36
[Sed98] Seddon, P.B., Staples, D.S., Patnayakuni, R., Bowtell, M.J., The University of Melbourne, Australia, The IS effectiveness matrix: the importance of stakeholder and system in measuring is success, Proceedings of the international conference on Information systems, Helsinki, Finland, 1998, p.165-176
[Teo01] Teo, T.S.H., Ang, J.S.K., An examination of major IS planning problems, International Journal of Information management, Vol. 21, I. 6, 2002, p. 457-470
Way 43: Risk And Value Analysis
By: Federico De Samaniego Steta
On basis of Joost Deetman
1. Introduction
Several years of analysis in the IS industry had proven that the development of IS projects can be challenging and time consuming task (as exposed by several analysis and surveys like the Standish's group “Chaos Report” in 1995, or the Robbins-Gioia survey in 2001), the relative lack of cohesion between the evolving nature of business plans and IS/IT strategy formulation has created a necessity for new methodologies that ensure strategic planning for IS/IT development and deployment inside an organization.
Furthermore, IS/IT project development represents a big investment inside an organization (in 1995, the Standish group reported that “The average cost of a development project for a large company is $2,322,000; for a medium company, it is $1,331,000; and for a small company, it is $434,000”), so an evaluation of the value and risks that this investment represents is compulsory (as with any other investments inside an organization). This risk/value analysis should be represented in financial and non-financial terms that can facilitate management decisions according IS/IT investments.
It is then necessary to utilize a framework that facilitates the development of successful IS/IT strategies: such as the four cycle method created by Salmela and Spil (International Journal of Information Management, 2002), which describes IS planning as an incremental and continuous process that is periodically adjusted to satisfy business needs. This represents a comprehensive methodology that considers the constant evolution of business plans and aligns them with IS/IT management.
This tool description attempts to integrate risk and value analysis inside the fourth cycle of the four cycle method (which is related to the authorization of IS/IT projects), and should be used only in this context. Risk management,assessment and analysis will be covered in the second chapter and value analysis in the third.
2. Risk management, assessment and analysis
Organizations are not new to the concept of risk management (described by B. D. Jenkins, as “The culture, processes and structures that are directed towards the effective management of potential opportunities and adverse effects”), nevertheless it is necessary to emphasize that IS/IT project planning and development process is generally “immature”comparing to other business-related activities and important attention should be paid to identification and evaluation of risks when pursuing a new IS/IT strategy inside an organization.
As explained by Gary Stoneburner et al. (Risk Management Guide for Information Technology Systems, 2002):”Minimizing negative impact on an organization and need for sound basis in decision making are the fundamental reasons organizations implement a risk management process”. A framework for such a risk management strategy is described by Stoneburner et al. (Risk Management Guide for Information Technology Systems, 2002), where two main components are described: risk assessment and risk mitigation. Risk assessment determines the potential threats and their impact on project development while risk mitigation “involves prioritizing, evaluating, and implementing the appropriate risk-reducing controls recommended from the risk assessment process” (Stoneburner et al, 2002). This tool will focus in the assessment phase of this risk management strategy, because it is clearly linked with the authorization cycle of the four cycle method.
Risk assessment can then be further described as the process of identifying and prioritizing risks inside an organization, Schmidt et al. (2001) elaborate this description and propose that this process consists of three steps: identification of risk factors, estimation of the like hood of each risk and evaluation of the total risk exposure (Schmidt et al, 2001).
In this model, an authoritative list of common risk factors in information system development was identified and prioritized in a 2x2 matrix according to two different metrics: perceived level of control of the risk inside the organization and perceived relative importance of the risk , as seen in figure 2.1 (Schmidt et al, 2001). In this matrix, the control axis is directly related to manager's ability to prevent the occurrence of a risk, and could be evaluated by interacting with management personnel in management workshops and brainstorming sessions; in the other hand, the risk importance axis can be seen as a hybrid metric comprised of risk frequency (that is, how likely it is that the risk will occur) and risk impact (effects that a particular risk create inside an organization) and can be evaluated with different risk analysis methodologies (that precisely are used for systematically use available information to determine how often specified risk-related events may occur and the magnitude of their consequences).
Although this risk categorization framework was aimed at particular set of risks identified by 41 senior management executives (Schmidt et al, 2001) it can be effectively used as a point of reference for expressing a high level view of the results derived from risk assessment and analysis (and even can be used as a tool for providing strategies to solve each of the“categories” of risks identified by the authors in the paper “A Framework to Identify Software Project Risks”) .
The idea is to utilize this framework as a tool for categorizing the risks found in the risk assessment process (where risks are identified and qualified in impact and frequency with the use of risk analysis methodologies), providing a point of reference for the development of strategies to attack them, and a high level representation scheme for management to analyze in the authorization process.
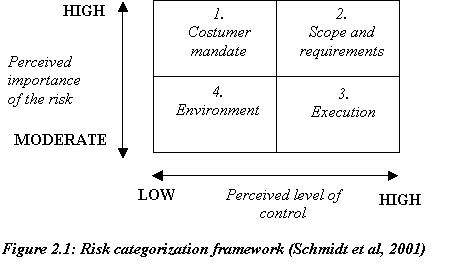
An alternate methodology, described by Stoneburner et al divides risk assessment in 9 steps, where only a few of them play a supportive role in the authorization phase. This is because this method is related to the identification of proper controls for reducing or eliminating risk during the risk mitigation process and therefore doesn't provide a proper framework for aiding the authorization cycle in the four cycle method (although it provides a good reference for some points like system characterization, impact analysis and threat identification).
However, risk analysis plays a vital role in this scheme, and could be conducted using several methodologies, such as: Failure Mode and Effect Analysis (FEMA), Fault Tree Analysis (FTA) or Benefit Cost Analysis (BCA, Gillen et al. 1999). This models can be effectively used as a reference to attack the risk analysis process, although it should be taken into account that some of them lack an emphasis on risks/threats where management fails to have direct control of the situation (which are treated as critical on the framework described above by Schmidt et al.).
Another probable strategy could consist of utilizing the concept of risk exposure analysis in the threats identified in the development of a IS project. This concept is comprised by the combination of two elements: probability of unsatisfactory outcome and consequences of such outcome (Fairley, 1994), making possible the utilization of a quantitative metric that considers the risk exposure as a multiplication of mathematical abstractions of this elements. Then, the probability of the unsatisfactory outcome can be calculated and multiplied by the estimated loss of the parties affected, resulting in the following formula (Padayechee, 2002):

![]()
It should be taken into account that risk exposure can be expressed in different magnitudes: as a risk can impact on different factors inside an organization (such as cost, performance, scheduling or quality). For example, personnel risks can be measured in man months and cost risks in monetary assets. This risk exposure analysis can aid in the process of prioritizing risks. Furthermore, the metric described by Padayachee can provide a simple quantitative evaluation of the importance factor of a particular risk inside the 2x2 risk categorization matrix (Schmid et al., 2002).
2. Value analysis
As said before, IS/IT project development is a big investment, which implies an inherent return value for the resources spent by the organization, such as monetary assets, time and personnel. However, the different value aspects derived from an IS/IT project are somewhat difficult to predict in monetary terms (such as performance, efficiency and saving estimations), which makes the identification and analysis of the desired value features critical for project authorization.
It should be noted that added value is not related to cost-reducing strategies, this is said because the only real value a organization can create is related with his performance against its competitors: either producing or having options to produce benefits with a greater profit; or producing or having options to produce higher or different benefits than the competition. The key to add value inside an IS project development is to align its development with any of this two contexts (Boehm and Sullivan, 2000).
In the case of non-profit organizations, where profit is something not related to the organization activities, the value is created when the organization achieves an equivalent social benefit with less resources (Porter and Kramer, 1999).
It is necessary then to determine the clear benefits that the investment will bring into the organization, the most direct approach to do this is describing the competitive advantage that the development of a particular project brings into an organization (aimed towards process optimization, quality or innovation). This makes a clear relation with the authorization phase: as the value analysis is directly directed toward creating business value (which is easily understandable by management personnel involved in the authorization process).
3. Authorization process
In the authorization cycle described in the four cycle method (Salmela and Spil, 2002), the system projects identified in the IS/IT portfolios are subjected to scrutinized analysis by senior management, in order to accept the investment necessary for the development of such projects.
The tools described in this pages are directed towards providing a basic risks/value analysis for the different projects in the portfolio identified in the first three cycles of the four cycle method. This analysis is aimed to support decision making in the authorization phase by the creation of a management report that describes the risks and benefits found for each project (the use of the categorization framework described by Schmidt et al is also recommended in order to classify in a high level view the risks found in all the project portfolios). The main idea of the report is to summarize the information accumulated during the risk assessment and value analysis processes into a format easily understandable by management personnel, avoiding to describe technicals details and concentrating on the correct display of the qualitative and quantitative information captured in the risk/value analysis (this can be done on a project to project basis or in a framework that involves the classification of the risks or benefits identified, such as some of the methodologies described before in this description).
4. Conclusion
Senior management should be able to utilize this tool's outcome to align the choices of IS/IT projects to be realized with the organization's current priorities for investment, this should be done trough the comparison of the different risks and benefits (added business value) detected in the different product portfolios. This decision-making task is basic for the success of any IS/IT project, as management approval is not only needed for the appropriate acquisition of resources, but also to provide feedback on the actual alignment of the identified project portfolios with the current state of business objectives and capabilities.
3. References
Boehm, B. W. Software Risk management: Principles and practices. IEEE Softw. 8,1, 32-41.
Fairley, R. 1994. Risk management for software projects. IEEE Softw. 11,3, 57-67.
Gillen, D., Li, J., Dahlgren, J., & Chang, E..1999. Assessing the Benefits and Costs of ITS Projects: Volume 1 Methodology. California PATH. University of California, Institute of Transportation Studies. Report No. UCB-ITS-PRR-99-9, 31-38.
Jenkins, B.D. 1998. Security Risk Analysis And Management. Countermeasures, Inc. 2-10.
Pedayachee, K. 2002. An interpretetive study of software risk management perspectives. In proceedings of the 2002 annual research conference of the South African institute of computer scientists and information technologists on Enablement trough technology. South African Institute For Computer Scientists and Information Technologists,118 -127
Porter, M.E. And Kramer, M.R. 1999. Philanthropy's new agenda: Creating value. Harvard Business Review 77,6,121-129.
Salmela H. and Spil T. A. M. 2002. Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22,6, 441-460.
Schmidt, R. C., Keil, M., Cule, P. E., and Lyytinen, K. 2001. Identifying software project risks: An international delphi study. Journal of Management Information Systems 17,4, 5-37.
Standish Group.1995. The Standish group reports: Chaos. Standish Group 1 – 5.
Stoneburner, G., Goguen, A., Feringa, A. 2002. Risk Management Guide for Information Technology Systems. National Institute of Standards and Technology. 800,30, 7-33.
Way 44. Final IS/IT Portfolio
By: J. Roos
Introduction
This paper will discuss one of the last tools as described in the ‘four cycles method’ [SS03]. The final IS/IT portfolio finds its place in the fourth planning cycle of the ‘four cycles method’,making it on of the last possible outcomes. The goal of this document is to provide the reader with a possible mechanism for assessing IS/IT results.
To use a clear systematic approach, Kipling’s method of the six honest serving-men will be used. This is also a practical choice because using this method will allow easy comparison to othermethods used in the E-Strategizing course at the University Twente.
Tool description
Salmela and Spil give the following description of the tool:
Final IS/IT Portfolio: Describes the IS/IT portfolio that has been formally approved by top management. [SS03]
What?
Portfolio management in this context, namely IS/IT, is a dynamic decision process, whereby a business’s list of active new (development) projects is constantly updated and revised. In this process, new projects are evaluated, selected and prioritized while existing projects can be accelerated, de-prioritized and even killed. The hard part of portfolio management is the uncertain nature of changing information. Opportunities, goals, strategic considerations and interdependence among project all have to be taken into account. The portfolio thus is a decision making tool within the business. The final IS/IT portfolio encompasses new, to be done projects, but also the projects that are already running, along with their implications on the business and management. [Dun83][Wp02]
Why?
The product portfolio supports decision-making and resource allocation. It tries to maximize return, in terms of economical or non-economical factors, to ensure the position of the company. The portfolio creates a link between business strategies and project selection. In a company, resources like funds, are usually finite, the portfolio helps in focusing to the right projects. Also, a right balance in short, long-term, main and supporting projects has to be found. Finally, the portfolio helps communicating objectives in the organization, both vertically and horizontally.
When?
The final IS/IT portfolio is near the end of the four cycles method.[SS03] Since this method actually is a cycle, the final portfolio will often be used in the authorization phase. Most tools will be more iterative in origin though, the final IS/IT portfolio is more of an end deliverable then a method to get to the end deliverable. The final portfolio will be made after a thorough value and risk analysis of the projects in the concept portfolio and hopefully before management coordinates its structure based on the projects.
How?
On writing the final portfolio, management will find that there are numerous parameters, dimensions and variables across which one might wish to seek a balance of projects. Valuation of projects has been done in a previous phase of the four cycle method, the difficulty lies in maximizing the value of the complete portfolio itself and creating balance. Also, different projects require different strategic planning strategies. [CEK01] In an attempt to combine most of the above named factors, a table has been constructed on strategic categories within a portfolio combined with certain management action. The primary table is a modification on Drucker’s eleven strategic categories model. [Dru64][Dru74]. The secondary table provides additional information on the strategic categories themselves.
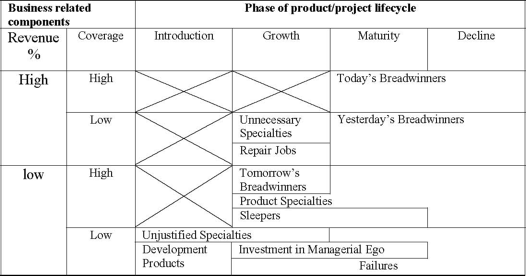
Table 1 - 11 strategic categories model
Classification | Management Action |
Today’s breadwinners | Slight modification or change now and then |
Tomorrow’s breadwinners | Press ahead with these |
Product specialties | Generally high margin business, limited competition, should absorb limited resources. Generally price insensitive market |
Development products | Make sure there are a good number of those around |
Failures | Withdraw |
Yesterday’s breadwinners | Milk the product |
Repair jobs | Make necessary change |
Unnecessary specialty / Unjustified specialty | If loss makers, withdraw. Watch contribution within company. |
Investments in management ego | Project should probably be withdrawn |
Sleepers | Be prepared to back this type of project. If you do not, competitors may. |
Table 2 - Strategic management actions
Misleading at first is the fact that the portfolio not only contains new to-be-done projects. It also covers the projects that are already running and summarizes their phases. Table 1 covers time, revenues and business coverage and is mainly focused on resulting products from projects. Supporting projects can also be applied in this matrix, linking the supporting project directly to the projects and processes it supports.
Each project type (strategic, high potential, key operational, support [WP02]) and phase has a particular way of managing it. Business processes need to be able to support these ways of management. This shows the importance of the final management IS/IT portfolio.
Where?
This chapter starts seemingly pointing to a geographical location. More important however is the ‘where’ in the company itself. The portfolio worked itself up the chain of command to the upper regions of senior management originating from lower- and middle-management. The portfolio however, as a means of communication, carries information again to the lower regions of the company.
Who?
IS/IT portfolio management is a critical senior management challenge. Not only that, but the topic is also related to the senior technology people. Combined they can find the right mixture of projects to maximize return, maintain competitiveness and efficiently allocate scarce resources. [SEK01]
Conclusion
In practice, financial methods seem to dominate portfolio management [SEK01]. Often heard methods here are NPV, ROI, EVA and payback period. Those valuation methods probably have been used in previous phases but are also to be included in the final portfolio. Apart from financial approaches, there are other methods of presenting a portfolio, based on a more strategic approach or so called portfolio maps or checklists. All the tools used individually will not give you a fitting portfolio in the end. Yet all the tools combined, or at least a few, will give you a better fitting portfolio on which management can act in the above described ways.
References
[Dru64] Drucker, P.F., Managing for Results, 1964 [Dru74] Drucker, P.F., Management: Tasks, Responsibilities, Practices, 1974 [CEK01] Cooper, R.G., Edgett, S.J., Kleinschmidt, E.J., Portfolio Management – fundamental to new product success, paper nr. 12, 2001 [Dun83] Dunst, K.H., Portfolio Management, Konzeption für die strategische Unternehmensplanung, 2003 [SS03] Salmela, H., Spil, T.A.M., Dynamic and emergent information systems strategy formulation and implementation, IT Management Select, volume 9, 3, 2003 [WP02] Ward, J., Peppard, J. Strategic Planning for Information Systems, 2002
Way 45 – IS management co-ordination
IS Management Coordination Structure.
By Rutger MacLean
When considering an IS Management Coordination Structure, it is imperative that all different aspects of managing IS are considered. Fortunately, when deciding on a structure that will facilitate the coordination of the different levels management of IS, there is little difference with other management areas.
What?
This tool is a help in creating a firm structure for controlling IS-projects. I designed this tool to be universally applicable in both newly started IS-projects as well as the more routine maintenance of existing IS. It maybe noted that there are some significant differences between these types of management challenges. However, this tool addresses them both, and both can be treated in the same way when using this tool.
Why?
Before deciding on which coordination structure is wanted, it is necessary to identify the need for such a structure. It is useless to define a coordination structure for a small project, which is hardly managed at all. Therefore a certain size is required, which brings around certain problems. The one strongest criterion is that there must be at least two managers responsible for the same project in one way or another. Otherwise there isn’t anything to be coordinated.
When?
The coordination structure must be decided, and made clear towards all levels of management, before the project starts. The structure is created in harmony with the planning and is directly related to the assessment of importance of the different sub-projects.
Who?
The people who will decide upon a certain IS Management Coordination Structure is essentially top-management, for they carry the ultimate responsibility and have the overview of the full project. However, it is desirable that top management decides upon this matter in close contact with the lower levels of management. Perhaps there are consultants involved, then they should be involved in the structure as well.
Where?
The structure is something that had to be decided within the company, but when there are several companies working on the same project it has to be decided among all these companies. That is somewhat more difficult, for decisions have to be made in harmony with all different stakeholders, whereas in one and the same company decisions can be pushed through top-down, if necessary.
How?
By using the framework described next. It is a simple decision making framework, which helps to bring some structure in IS Management Coordination.
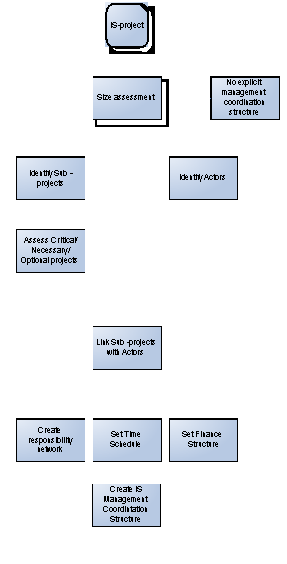
Decision and points of attention framework for IS Management Coordination Structure.
IS project:
Although it says IS-project as input, it does not always have to be a project. It might as well be a current situation concerning IS, which needs to be revised or updated.
Size Assessment:
When deciding upon the desirable coordination structure, the scale of the project is a important. A coordination structure consumes time and effort and is only profitable when at least two managers are concerned. Otherwise a more clan-like management style is desirable. If from a simple size assessment is derived that the project is too small to make a structure affordable, further implementation of this tool will not lead to better results.
Identify Actors:
For an efficient Management Coordination, first all relevant actors must be identified. In this case only managers are relevant actors. Still, first line workers are important and should not be forgotten. However, for determining a management coordination structure they have little influence. The actors to be selected are all managers with a certain interest in the project, starting with the top-manager and all the way down to operational management.
Identify Sub-projects:
Each IS-project has a lot of different, smaller sub-projects. These projects tend to address sub-needs of different types of end-users. All these projects have to be identified and reduced to that size where a manager can take full responsibility for such a project. If the whole project can be done by a single manager, the project is too small and should have been eliminated as not-feasible in the previous stage.
Assess Critical/Necessary/Optional projects:
All projects somehow interlink with each other. This creates the possibility to identify Critical sub-projects. These sub-projects are essential to the success of the entire project. For example, the creation of an IT-infrastructure, without that infrastructure an entire project would fail, even if all other sub-projects would be successful. Less important are the Necessary sub-projects. These sub-projects are important to complete, have a important functionality, but aren’t critical to the rest of the project. Without these functions, the project would lose much of its value. Finally, Optional projects have a certain added value, but the project will be fine without them.
Link Sub-projects with Actors.
All projects should have someone who is responsible for them. In general sub-projects should be linked with actors who have a specific interest in that project. If possible it is wise to assign critical projects to managers who meet their deadlines, necessary projects to managers who have a good idea of end-users’ wishes and optional projects to managers who meet their budgets.
Create responsibility network:
A responsibility network is a chart in which all managers are linked to higher or equal managers. They have to justify their actions always to their own superior, and if a project is vital to the well-being of another project, then they also have to justify their actions towards the manager who is responsible for that other project. This can be an equal, or even a lower manager.
Set Time Schedule:
As projects grow bigger, so is the need for a firm time-schedule. Since IS-projects tend to never meet the deadline, some powerful management and awareness about IS-reporting is needed. Certainly for the most essential sub-projects, which have other sub-projects waiting for their completion, this can be higly frustrating.
Set Finance Structure:
As all projects, IS-projects have to be financed, one way or the other. Often IS-projects not only finish late, but also take up far more resources than planned. Certainly for optional projects, which have little added value, this can be frustrating. When concerning Finance Structure and Time Schedule, keep this in mind as a rule of thumb.
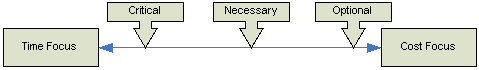
Create IS Management Coordination Structure
When all necessary information has been gathered, a schedule can be made in which the following aspects are considered.
-Due Date (When)
-Report from which manager, to which manager (Who)
-Project & Objective(What)
-Importance (Why)
-Cumulative Budget (How Much)
Here is an example of a possible IS Management Coordination Structure.
When (Date) | From (Actor) | To (Actor) | Project | Importance | Budget | Objective |
12-12-05 | Andrew | Greg | C | Critical | 20,000 | Team created |
15-12-05 | Andrew | Greg, Geoff | C | Critical | 40,000 | Schedule |
31-01-06 | Andrew | Greg, Geoff | C | Critical | 2,000,000 | Completion |
07-01-06 | Greg | Geoff | F | Optional | 20,000 | Funding |
14-02-06 | Geoff | Mr. MacLean | D | Necessary | 1,500,000 | Completion |
References:
Daft, R.L. Organization Theory and Design, 2001, Thompson Learning, pp. 240-266
Salmela, H & Spil, T.A.M. Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22, 441-460.
New way 46 –p187 - Evaluation
New way 47 -p188 - Political end Legal issues
New way 48 -p189 - Understanding resistance
New way 49 -p196 - Mapping IS Capability
New way 50 -p198 - Benchmarking
New way 51 -p200 - Financial analysis
New way 52 -p205- Scenario Planning
What is the evaluation tool?
The proposed new tool is an evaluation tool, for the four-cycle-method (Salmela and Spil, 2002). Managers who work with the four-cycle-method will set their goals in phase one of the method. Thanks to the evaluation tool IS managers will not make the same mistakes when planning new IS implementation processes. This tool evaluates the planning process and ensures deutero learning (Wijnhoven, 1999), so the organization will get on a higher level.
Why is this new tool important?
At this moment the four-cycle-method is a complete process which gives a manager many tools to use when forming and implementing an IS strategy. The work of Samela and Spil (2002) emphasizes a complete circle for e-strategizing, one extra tool which could be useful is the evaluation of the process itself. The four-cycle-method starts with evaluation of previous planning results, the tools which can be used according to the authors are:
1.Information year report
2.Information management control range
3.List of current and planned projects
These tools are good when evaluating the IS project but not to have a good look at the IS process. To ensure organizational learning it is important to evaluate the IS implementation process. To do this, clear goals have to be set in the first phase. This is already done thanks to step 2 in the first phase; setting planning scope and objectives. But the four-cycle-method does not look back and evaluates these scopes and objectives at the end. Thanks to this tool, deutero learning is ensured and the complete process will get on a higher level each time the four-cycle-method is performed.
When has this tool to be used?
As already explained in short in the previous part, this tool evaluates the process. So it’s obvious that the tool should be at the end of the four-cycle-method. There is only one problem: the last phase is the ‘the authorizing phase’ and according to the definition of this phase an evaluation tool would not fit here. That is why the evaluation tool has to be after the authorizing phase a sort of fifth phase; else the manager wouldn’t be able to evaluate the whole IS process, which is iterative in its essence. So, the tool could only be performed at the end of the complete cycle.
How should the tool be used?
Thanks to the objectives which are set during the first phase, IS managers should be able to look critically at the IS planning process. The manager has to evaluate and rethink the complete four-cycle-method to review the obstacles he encountered during the process. By doing so, the manager and the organization will learn from this (hopefully), so in future projects the same mistakes will not be made again.
Where has the tool to be performed?
The rethinking and evaluating of the IS process can best be done at the office of the IS manager, but location is no critical factor.
Who should be involved?
Most important is the IS manager, because the manager should use this tool to enrich future IS planning processes. But when evaluating the process the manager probably needs input from other persons who where involved during the process. An external advisor could be helpful as well, especially when the level of experience in evaluation is low (so in any case in the first few years of using the four-cycle method). This advisor can assist in determining weaknesses in the strategising process and in pinpointing opportunities.
References
•Salmela, H,& Spil, TAM (2002), Dynamic and emergent information systems strategy formulation and implementation, International Journal of Information Management, 22, pp441-460.
•Wijnhoven, A.B.J.M., (1999), Managing Dynamic Organizational Memories, instruments for Knowledge Management, Enschede: Twente University Press
New Way 47. Political and legal information sources
By van der Linden, van den Berg, Voermans & Driezen.
Introduction
In this paper a tool that is missing in the four method cycle of Spil and Salema will be described using the six honest men of Rudyard Kipling. In our opinion a tool is lacking in the ‘Reviewing existing plans, documents and information sources’ part of the second planning cycle (alignment).
What?
In the ‘Reviewing existing plans, documents and information sources’ part of the second planning cycle internal and external information sources play an important role. In the external information sources tool (nr. 15) no attention is paid to legal and political restrictions and developments. The economic, industrial and competitive climate is mentioned though. When considering the PESTEL framework as a starting point for analyzing the macro-environment of the organization. The Economic and Technological factors are mentioned in the four cycle method. Environmental factors are not extremely important in ICT and the Socio-cultural factors will, in our opinion, be reflected in other tools (for instance tool 18). But legal and political factors are not mentioned. We think a tool 15B should be added: analysis of the existing and future legal and political situation.
In this tool, existing and possible future laws and relevant political developments are analyzed and their effects upon the E-strategy are listed. For example, laws concerning privacy of users of information systems (a hot issue at the moment) should be taken into account.
Why?
With the growing importance of IT and IS in organizations, it is important that IT and IS respond to existing legislation. When formulating E-strategy, possible future legislation concerning ICT should also be taken into account. Not only can a company get a monetary penalty when its systems are not fully legal, this is also not good for a company’s image. In Europe, legislation concerning data-exchange between companies and countries and privacy of IT-users (for example on the Internet) is developing very rapidly. Therefore, before formulating an E-strategy, a company should monitor these developments and their implications.
Where?
The monitoring of legal and political developments can be done within an organization. This is mostly important for large organizations with lots of users of different information systems and for large or small organizations who have lots of users of systems outside the company (for example via the Internet, with E-commerce or something alike).
An analysis of developments can be done within an organization (internal analysis of external developments).
When?
This monitoring should be done continually, because laws can change at any moment and new laws are introduced continuously. Recent changes and expected laws should be recorded and then be used within the second cycle (or directly when new laws are affecting existing systems).
Who?
The monitoring can be done by an internal juridical employee who tracks changes and developments. He/she should have a juridical background and be familiar with political ‘games’ and legal language, because otherwise it will be very difficult to understand exactly what is being stated. After ‘translating’ laws IS management and top management can be involved to interpret the laws and think about possible effects on the E-strategy.
How?
The juridical employee has to stay informed about developments. He can do this by reading magazines, checking websites about the subject and talking to colleagues about the subject (most probably the employee himself/herself knows best how to do this).
Introduction
As part of the course E-Strategizing at the University of Twente students have to come up with a new tool that could be used within the Four Cycle Method (FCM) as defined by Salmela and Spil in their paper (Salmela & Spil, 2002). The Four Cycle Method uses many different tools (also known as methods) to define an e-strategy for corporate businesses.
This document will outline a new tool that could be used to create a better understanding of resistance towards changes introduced by an e-strategy.
The next chapter will outline the questions which form the rationale for this document in more detail.
Problem description
In general changes are bound to be resisted by humans. This is also the case in respect to an e-strategy for any given corporation. Resistance to a plan means the implementation of this plan can fail or be delayed. In respect to this there are several questions one could ask himself. As an introduction to the subject this chapter outlines the questions which form the rationale for this document.
Following chapters will formulate answers to these questions as much as possible.
First of all the main problem description is:
How should a change project with possible resistance be managed?
Following questions have been derived from this problem description:
Q0 Is it possible to categorize resistance?
Q1 What are the reasons to resist?
Q2 Is it possible to predict the outcome of the change process knowing the amount resistance?
Q3 Is there a way to plan the change project with resistance?
Q4 How to eliminate or reduce the resistance?
Resistance
Resistance towards changes is a common obstacle in changing the organization. Resistance will always be conducted by one or more people in the organization. Before changing the organization it is important to identify this possible resistance and more important the reasons why the people resist. This chapter will discuss the possible categories of members and the reasons why people resist to changes in general.
Categories
This paragraph describes two possible categories of people. It is important to identify the type of people which will be influenced by the change. Both categories have some similarities, but also change from each other. These two categories will help to identify the possible expected resistance.
According to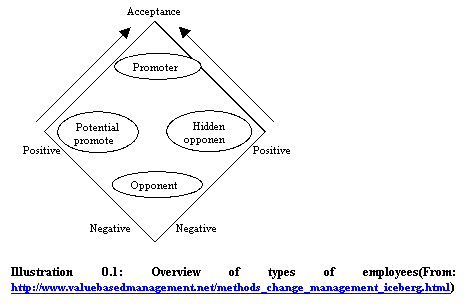 Krüger (Krüger, www) members or parts of an organization embody different attitudes towards changes. Krüger supplies four groups and describes shortly how each category of people can best be handled. Error! Reference source not found. gives an overview of each of the categories. The categories that are shown are:
Krüger (Krüger, www) members or parts of an organization embody different attitudes towards changes. Krüger supplies four groups and describes shortly how each category of people can best be handled. Error! Reference source not found. gives an overview of each of the categories. The categories that are shown are:
•Opponents: Have both a negative general attitude towards change AND a negative behavior towards this particular personal change;
•Hidden opponents: Have a negative generic attitude towards change although they seem to be supporting the change on a superficial level ("Opportunists");
•Potential promoters: Have a generic positive attitude towards change, however for certain reasons they are not convinced (yet) about this particular change;
•Promoters: Have both a positive generic attitude towards change AND are positive about this particular change for them personally.
Another possible categorization is the one provided by Rogers (Rogers, www). Rogers identifies five categories of people. These can be described as:
•Innovators: These are brave people which will pull the change.
•Early adopters: These are respectable people, opinion leaders that try out new ideas but only in a careful way.
•Early majority: These are thoughtful and careful people, but accept change more quickly than most average people.
•Late majority: These are skeptic people who will only use new ideas or products when the majority of the people are using it.
•Laggards: These are traditional people, caring for the "old ways". They are critical towards new ideas and will only accept them if the new idea has become mainstream or even tradition.
As show in both categorizations there are people who will accept changes, but also people who will resist them. It should be clear that a change effecting only promoters or innovators can be implemented more easily because there will be little or no resistance. A change affecting opponents or laggards will most likely be heavily resisted.
Knowing the kind of people that will be affected by a change could give management an indication about the expected resistance. This could be used for an evaluation of the proposed change. When evaluation indicates heavy resistance a difficult and long change project should be expected and the chance for success will probably be small.
Reasons
In the previous paragraph categories of people where discussed. As read before it is important to know what resistance a change is facing. But knowing the type of resistance perhaps is not nearly as important ad to know the reasons for resistance by people.
According to Trice and Beyer (Trice & Beyer, www) resistance can be executed on two levels. These levels are an organizational or an individual level. On every level there are different reasons why a change could be resisted. In this document we give some common reasons for people to resist to a change. Note this overview is meant as an indication and there might be much more reasons for a given change to be resisted.
Organizational level
When Groups, departments, or other parts of an organization are affected by a change they most likely will resist. As was stated before when a change is resisted it will be difficult to implement the change.
From an organizational point of view there are different reasons to resist changes. Some of these reasons are:
•Threats to power and influence;
•Lack of trust;
•Different perceptions and goals;
•Social disruption;
•Resource limitations;
•Fixed investments;
•Inter-organizational agreements.
Individual level
From an individual point of view there are also several reasons to resist to changes. Although the impact of this resistance will be much lower than on the organizational level it is also much more difficult to diminish this type of resistance. Some reasons for individuals to resist changes are:
•Fear of the unknown
•Self-interest;
•Habits;
•Selective attention and retention;
•Dependence;
•Need for security.
As was pointed out already these are nowhere near complete lists. There can be many reasons for individuals or groups to resist changes. The reasons given above however are a useful categorization that managers can use to minimize some of the resistance to proposed changes.
Change management
The process concerned with changing corporate environments is often referred to as change management. This chapter describes how such process could be shaped so a proper implementation of changes can be guaranteed based on a more sound manner.
Preparation
Before implementing a change or planning it, it is useful to analyze if the change could succeed. Beckhard and Harris (Beckhard & Harris, 1987) introduced a resistance theory. This theory provides a simple yet powerful formula which gives a quick impression of the possibilities and conditions to change an organization. gives an overview of this formula.![]()
Illustration 0.1: Change theory equation.
As illustrated in the disadvantage times the desirability times the practicality times needs to exceed the resistance before the change can possibly be a success. So if for instance a group or individual whose commitment is needed is not:
•Sufficiently dissatisfied with the present state of affairs;
•Eager to achieve the proposed end state;
•Convinced of the feasibility of the change;
The “costs” for the change will most likely outweigh the change attitude and the change will probably be hard to implement.
One of the problems however is the quantification of the given literals. One solution is to draw up questionnaires and hand these out to key persons in a planned change process. By multiplying the results of these questionnaires it is possible to see if the outcome is more or less then the expected resistance. The resistance can be defined as the average of the entire set of people which is being questioned. So for example in a change process with ten key persons the result of the equation could be:
4 x 3 x 8 > 5 x 5 x 5 → 96 > 125
Which means changes will probably be hard to implement since the equation is not balanced properly.
Implementation
To ensure a proper implementation of changes we intend to work according the method drawn up by Deming (Deming, www). The Deming cycle allows for adopting changes into a corporate environment in an orderly manner. The Deming cycle or PDSA cycle consists of the following steps:
•PLAN: Plan ahead for change. Analyze and predict the results.
•DO: Execute the plan, taking small steps in controlled circumstances.
•STUDY: Study (or check) the results.
•ACT: Take action to standardize or improve the process.
Error! Reference source not found. gives a clear overview of the relation between the steps which form the Deming cycle.
Illustration 0.2: Overview of the Deming cycle
(from: 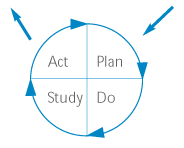 http://www.modern.nhs.uk/improvementguides/process/2.htm).
http://www.modern.nhs.uk/improvementguides/process/2.htm).
When working incrementally it might be possible to minimize resistance to changes before they are implemented. This could best be done during the planning phase.
Some possibilities of what could go wrong during changing corporate environments are provided by John Kotter (Kotter, 1990). He concludes that there are eight reasons why many change processes fail. Below an overview is given:
•Allowing to much complexity;
•Failing to build a substantial coalition;
•Understanding the need for a clear vision;
•Failing to clearly communicate the vision;
•Permitting roadblocks against the vision;
•Not planning and getting short-term wins;
•Declaring victory too soon;
•Not anchoring changes in corporate culture.
(from: http://www.valuebasedmanagement.net/methods_kotter_change.html)
Kotter and Schlesinger (Kotter & Schlessinger, www) have set out the following six change approaches to deal with resistance to changes in a corporation:
•Education and Communication: Where there is a lack of information or inaccurate information and analysis. One of the best ways to overcome resistance to change is to educate people about the change effort beforehand. Up-front communication and education helps employees see the logic in the change effort. this reduces unfounded and incorrect rumors concerning the effects of change in the organization.
•Participation and Involvement: Where the initiators do not have all the information they need to design the change and where others have considerable power to resist. When employees are involved in the change effort they are more likely to buy into change rather than resist it. This approach is likely to lower resistance and those who merely acquiesce to change.
•Facilitation and Support: Where people are resisting change due to adjustment problems. Managers can head-off potential resistance by being supportive of employees during difficult times. Managerial support helps employees deal with fear and anxiety during a transition period. The basis of resistance towards change is likely to be the perception that there some form of detrimental effect occasioned by the change in the organization. This approach is concerned with provision of special training, counseling, time off work.
•Negotiation and Agreement: Where someone or some group may lose out in a change and where that individual or group has considerable power to resist. Managers can combat resistance by offering incentives to employees not to resist change. This can be done by allowing change resistors to veto elements of change that are threatening, or change resistors can be offered incentives to leave the company through early buyouts or retirements in order to avoid having to experience the change effort. This approach will be appropriate where those resisting change are in a position of power.
•Manipulation and Co-option: Where other tactics will not work or are too expensive. Kotter and Schlesinger suggest that an effective manipulation technique is to co-opt with resisters. Co-option involves the patronizing gesture in bringing a person into a change management-planning group for the sake of appearances rather than their substantive contribution. This often involves selecting leaders of the resisters to participate in the change effort. These leaders can be given a symbolic role in decision making without threatening the change effort. Still, if these leaders feel they are being tricked they are likely to push resistance even further than if they were never included in the change effort leadership.
•Explicit and Implicit Coercion: Where speed is essential and to be used only as last resort. Managers can explicitly or implicitly force employees into accepting change by making clear that resisting changes can lead to losing jobs, firing, transferring or not promoting employees.
By using the techniques given above managers can ensure proper implementation of changes in an early stage. If for example the change equation outlined in the previous chapter indicates a certain change is likely to be resisted managers could conduct a survey to find out what causes this resistance and adapt their plans accordingly.
Integration
Integrating the proposed method into the Four Cycle Method (FCM) can be done in several ways. One way is to align the steps given by the Deming cycle with those of the FCM. Another option is to perform multiple iterations of the Deming cycle in each of the cycles from the FCM. Depending on the amount of changes required the latter is probably the best solution. Managers of a corporation could decide themselves which way of integration is best suitable for their corporate environment.
Conclusions
This chapter summarizes the different concepts outlined in the previous chapters.
As was pointed out in the first chapter of this paper people can be divided into several categories from a resistance point of view. This can be used to create a better understanding about what drives people to resist changes. Resistance can be viewed from either an organizational or an individual perspective. With help of these categorizations it is possible to create quantification for the resistance theory. This theory enables a manager to determine the possible resistance towards a change.
The resistance theory provides a method to predict the amount of resistance towards changes. This method can be used in combination with a traditional structuring of the change management process. The opted method for this is the Deming cycle which recognizes four individual stages for a change implementation. These are: plan, do, act and study. The resistance theory can be used in the planning phase of the Deming cycle to determine the possible amount of resistance towards changes. By adapting plans it could be possible to reduce and minimize the resistance of the employees.
Several techniques for improving the corporate and individual resistance towards change have been outlined as well. By improving for instance the communication and decreasing the complexity of planned changes it is possible that employees will be more positively biased against planned changes. The outlined techniques can be applied in an early stage of the change management to create a more positively biased corporate environment towards changes.
Literature
Salmela, H. & Spil, T.A.M. (2002). Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22, 441-460.
Beckhard & Harris (1987), Organizational Transitions: Managing Complex Change, p. 98-99, Addison Wesley Publishing Company, ISBN: 0201108879
Kotter (1990), A force for Change: How Leadership Differs from Management, Free Press, ISBN: 0029184657
Internet
Kotter & Schlesinger (www), http://www.valuebasedmanagement.net/methods_kotter_change_approaches.html
Rogers (www), http://www.valuebasedmanagement.net/methods_rogers_innovation_adoption_curve.html
Krüger (www), http://www.valuebasedmanagement.net/methods_change_management_iceberg.html
Trice & Beyer (www), http://www.valuebasedmanagement.net/methods_trice_beyer_changing_organizational_cultures.html
Deming (www), http://www.valuebasedmanagement.net/methods_demingcycle.html
New Way 49 - Mapping of IS capability
Niels Höfte, Wilco Leenslag, Wilco Menge, Erik Nijkamp and Marijn van Schoote
Introduction
This report describes a new outcome for the Four Cycle Method by Salmela & Spil [SPI-02]. It is an addition to the 45 outcomes already mentioned in the paper. The new founded outcome is based on the paper from Peppard [PEP-04] “Beyond strategic information systems: towards an IS capability”. In this paper a new fourth era is proposed where organization’s performance will be significantly dependent on it’s IS capability. Because this is an upcoming era, IS capability is not explicitly mentioned in the Four Cycle Method. Mapping of IS capability best fits in the “Planning the IS/IT infrastructure” phase between outcome 23 and 24.
In this report the theory of the six honest men is used to describe the new outcome “Mapping of IS capability” [KIP-42], answers 6 questions; What, Why, When, How, Where and Who.
What is IS capability?
Capability or organizational capability is the set of competences an organization needs to accomplish certain organizational goals. IS capabilities are the set of competences an organization needs to successfully implement and use information systems, according the strategic goals associated with these information systems. Is capability is only visible at the level of the overall organization.
When information systems grow more complex (like ERP systems), the success factors often more depend on the IS capabilities than of the quality of the actual information system itself. The organization needs to be able to implement and manage the organizational changes.
The current IS capabilities can be an enabler or a ‘brake’ when implementing and using an information systems. Only when the ambition level is matched with the capability level the capabilities will act as an enabler. When the ambition level is too high, the capabilities fall short and will act as a ‘brake’. (Also, when the ambition level is too low, the ambition level itself can be considered a ‘brake’.)
Why is IS capability necessary?
Creating an overall IS strategy becomes increasingly more difficult because of the impact of complex information systems and the importance of aligning IS/IT with business strategies. The IS capability of an organisation determines whit what competencies they have to do this. Mapping of IS capability is done to identify the current IS capability and if disappointing to improve it.
When is mapping of IS capability done?
Mapping of the IS capability of an organisation is done in the beginning of the third phase (Analyzing IS resources and technology infrastructure) of the Four Cycle Method because the results can have impact on “Planning the IS organisation” and the fourth cycle.
How can mapping of IS capability be done?
The most difficult part of achieving IS capability is how to do it. Mapping the IS capability requires competencies with characteristics that enable an organization to conceive, choose and implement strategies. The organization could identify an advantage by conceiving an innovative strategy that depends on IT, but successfully implementing such a strategy will be dependent on:
§Organization’s ability to successfully deploy appropriate resources
§Fusing IS knowledge and business knowledge.
§A flexible and re-usable IT infrastructure.
§An effective use process to link IS/IT assets with (business) value realization.
IS capability is not as dependent on the technology and software applications as much as it depends on the organization’s ability to implement and manage change. Implementation of a new information system (Enterprise System) normally involves, removing current problems and constraints to progress through more integrated processes and systems. This will cause many existing IS competencies to be re-assessed and improved to enable the organization to be operated and managed as an integrated whole, using information and systems in new and quite different ways. If successful, the organization will have an improved business and IS capability, which can raise new strategic opportunities.
Where in an organization should mapping IS capability be done?
To quote Peppard [PEP-04] page 182: “although having an IS capability is a business imperative today, different organizations may choose to resource it in different ways, but almost all will rely on a combination of internal and external resources”. Today companies are outsourcing more and more also due to the complexity of IS/IT. Therefore the IS capability is distributed. So mapping should be done internally and also externally at the outsourcer to determine the overall IS capability.
Who should map the IS capability?
Peppard highlighted in his research that the resource elements i.e. the knowledge and skills, underpinning these IS competencies are not located solely in the IS function. Consequently, IS competencies do not exist in any one functional area: this point is crucial and presents management with the challenge of establishing, developing and nurturing these competencies within the existing ‘functional’ structure. However, it is worth noting that the significant resource elements of the competencies within the ‘supply’ domain often reside within the IS function.
Conclusion
Due to the new proposed fourth era by Peppard [PEP-04], IS capability there is a need to add a new outcome to the Four Cycle Method by Salmela & Spil [SPI-02] which covers the IS capability. IS capabilities are the set of competences an organization needs to successfully implement and use information systems, according the strategic goals associated with these information systems. Mapping of IS capability is responsible for identifying the current IS capability and if disappointing to improve it. Mapping of the IS capability of an organisation is done in the beginning of the third phase (Analyzing IS resources and technology infrastructure) of the Four Cycle Method because the results can have impact on “Planning the IS organisation” and the fourth cycle.
Today companies are outsourcing more and more also due to the complexity of IS/IT. Therefore the IS capability is distributed. So mapping should be done internally and also externally at the outsourcer to determine the overall IS capability.
Peppard highlighted in his research that the resource elements i.e. the knowledge and skills, underpinning these IS competencies are not located solely in the IS function. Consequently, IS competencies do not exist in any one functional area: this point is crucial and presents management with the challenge of establishing, developing and nurturing these competencies within the existing ‘functional’ structure.
The most difficult part of achieving IS capability is how to do it. Mapping the IS capability requires competencies with characteristics that enable an organization to conceive, choose and implement strategies. If implemented successful, the organization will have an improved business and IS capability, which can raise new strategic opportunities.
References
[KIP-42] Kipling R., The Elephant's child, Garden City, N.Y, 1942
[SPI-02] Salmela H, Spil T A M, Dynamic and emergent information systems strategy formulation and implementation, International journal of information management, ISSN 0268-4012, vol. 22 (2002), afl. 6, pag. 441, 2002
[PEP-04] Peppard, J. et al. Beyond strategic information systems: towards an IS capability. Journal of Strategic Information Systems 13, pp167-194, 2004
New way 50 Benchmarking
Group 5
Our proposal for the missing tool is “benchmarking”. The four-cycle method includes the analysis of previous projects and the comparison of previous with planned projects for the e-strategy, but analysis and comparison just take internal projects into account. The four-cycle method includes no tool for evaluating projects or other objects of different companies or in particular competitors. But as we think, this could help a lot in formulating an e-strategy.
First of all, what is benchmarking? “Benchmarking is an approach used for evaluating and improving the company performances, by comparing them with the best performing companies. Benchmarking first studies the process to be improved, finds a best practice process in order to try to match two parts of the processes which have analogies, and then tries to change or modify the interconnections, structures or behaviour of the part to be improved using the analogy with the best transformation process.” (M Lucertini, F Nicolo, D Telmon, Business Administration and Organisation Theory, vol. 38, issue 1, March 19, 1995)
By benchmarking you can find best practises or examples of projects that failed. Analysing benchmarks and their results, respectively, enable you to figure out critical factors that are important for the success of a project. Though the quoted definition above is mainly about processes, it’s not only about processes or projects of competitors that can be analysed to get useful information. Of course you can also analyse, for instance, the IT-budget of your competitors to get a clue how to make it right. Helpful for us is that the same procedure mentioned above should be applicable for information system planning.
In the following the “six honest men” questions and answers are discussed.
How:
There exists a common process model which we want to describe here. It consists of four phases:
1.Planning
a.Agree on the benchmarking object, define it and select criteria
b.Search for partners / competitors
2.Execution
a.Collection and gathering of data
b.Checking the data for consistency
3.Evaluation
a.Analysis of the collected data
b.Figure out improvement actions
4.Realization
a.Implementation of the improvement proposals
What:
The benchmarking object can be chosen during the planning phase of the four-cycle model. Benchmarked objects can be for example the frequently used information system in the industry, the finance (IT-budget), business processes or simply projects.
Why:
Benchmarking can be helpful in figuring out critical success factors and to find best practices that can give you a kind of guideline for your own company. If you don't know what the standard is, you cannot compare yourself against it. Another point is that you also have to know where your competitors stand.
Though it is most appropriate to benchmark within your own field of interest (see ‘Who’ question), one should be aware that widening your horizon beyond the own field of interest sometimes helps to find new (maybe innovative) “best practises” from totally different fields, but whose “best practises” just fit to the own one.
Who:
For benchmarking you need to find partners. Most appropriate are your competitors. But in any case the partners need to be companies from the same branch of trade. The more similar the companies are concerning number of employees, the service they offer or product they sell the easier is it to compare the companies. All partners of the benchmarking can profit from it, because the best companies can improve their reputation and the others can learn from it.
Where:
The collection of the data needs to be done in the companies, but the analysis of the data can be done together with partners during a meeting.
When:
The benchmarking should be done during the first cycle, the planning cycle. It helps to gather some crucial information that you can be used to formulate a successful e-strategy.
IT benchmarking, in particular, is important because it can justify investments in infrastructure, provide a window to user satisfaction, improve the redesign of IT-enabled business processes, and enhance user learning or knowledge management. (W.J. Doll et al. / Information & Management 41, 2003, 199–212)
Like the four-cycle method, benchmarking approach should also be viewed as a complementary rather than a one-off job.
We think that the aspect of benchmarking is missing in the four-cycle method. It is a further option that is useful in finding the optimal e-strategy for your company.
References:
William J. Dolla,*, Xiaodong Dengb, Joseph A. Scazzeroc:
A process for post-implementation IT benchmarking, 2003
New way 51 – Financial analysis and return on investment
Stefan Fountain, Ingmar Eeftink, Wesley Oosting, Sebastiaan Hoogeveen, Bart Vrijkorte
Introduction
In this paper we identify a missing tool in the four cycles method for IS planning. We suggest an additional tool derived from the IS planning literature and explain why this tool can be easily used to fill the detected gap.
Four cycles method
The four cycles method attempts to combine the strengths of both the comprehensive and the incremental planning to be able to recognise emerging trends. The method provides a basic schedule for organising planning activities. The four cycles method sees IS planning as a continuous process [SA2002]. The four cycles method divides a chosen period of time into four different planning cycles: agreeing on planning objectives, aligning business objectives, analysing IS resources and IT infrastructure, and authorising actions. Each planning cycle has its own set of tools.
Missing tool
After using the four cycles method during the working conferences for three weeks now, we all agree that this method is a continuous IS planning approach that combines the best of comprehensive planning and incremental planning. The suggested tools in the cycles form a complete overview to gather the necessary information needed to obtain a justified IS/IT portfolio in the end. All these tools generate a lot of information making it hard for stakeholders to make decisions upon them. Therefore we would like to suggest an additional tool that reduces the information overload and gives a total overview of the gathered information in the different cycles. We think that tool is the score card method.
Score card method
The score card method is a technique for ranking projects on certain categories. Projects with a higher ranking are more likely to get resources from the organisation for implementation. The categories on the score card represent benefits and risks. Benefits get a positive score, risks a negative. Projects can obtain a score from 1-5. Parker et al. have identified the following categories [OI1993]:
•Return on investment: return on investment is the relative yield on the invested capital in a project. This return can derive from increased efficiency or benefits like value linking (increased profit at lower cost), value acceleration (profits sooner available), or value restructuring (increasing labour productivity);
•Strategic match: strategic match indicates whether a project is aligned with the organisational goals;
•Competitive advantage: competitive advantage is the degree which a project contributes to the organisations’ strategy;
•Management information: this category indicates in which degree information is generated of registered about the organisations’ core activities;
•Competitive response: competitive response describes whether project failure will lead to competitive arrears;
•Strategic IS architecture: strategic IS architecture indicates whether a future system is aligned with the corporate IS strategy;
•Project/organisational risk: this category indicates whether the organisation is able to change;
•Definitional uncertainty: definitional uncertainty describes in which degree the definition of the future system is clear;
•Technical uncertainty: to which extend technological factors can be fulfilled to make sure the project succeeds;
•Infrastructure risk: infrastructure risk describes whether organisational restrictions have to be introduced for implementing the project.
Not all the mentioned categories have to be in an organisations’ score card. Categories are only scored if they are of importance for an organisation. Besides each category has its own weighted value to emphasize its relative importance. Categories are viewed from ‘business domain’ and ‘technology domain [OI1993]. Categories in the business domain represent the relation between the project and the strategy and the primary activities of the organisation. The technology domain categories describe the project requirements concerning the knowledge and infrastructure of the organisation and the definition of the project itself. A total score card would look like table 1.
ROI + | SM + | CA + | CR + | MI + | POR - | SA + | DU - | TU - | IR - | |
Business Domain | ||||||||||
Technology Domain | ||||||||||
Weighted Value |
Table 1: Score card according Parker et al.
Oirsouw et al. have a different view on project score cards [OI1993]. They see score cards as a tool to prioritise projects and not as an absolute criterion. Their score card prioritises projects on four (aggregated) categories and not on one total score. These categories are initial investment, return on investment, total benefit, and risk index. Total benefit is the sum of the benefit categories of Porter et al. multiplied with their corresponding weighted value. The risk index can be retrieved by summating the different risk categories. This results in the following score card.
Project # | Profit | Total benefit | Risk index | |||
Initial investment | ROI | |||||
1. | ||||||
2. | ||||||
3. | ||||||
Table 2: Score card according Oirsouw et al.
For both score card methods count that most categories, if not all can be derived by use of the four cycle method tools. We see that determining the appropriate categories is the responsibility of top management. Filling in these categories with indicators is the role of functional- and IS management. Finally top management makes decisions upon a completed score card.
Conclusion
We think the four cycles method with its underlying tools is a complete method to gather information for IS planning. What we miss in this method is a tool that aggregates and presents the gathered information in a clear way to make planning decisions upon it. In this paper we suggested the score card method to overcome this lack. We have described the score card method according Parker et al. and score card method of Oirsouw et al. Organisations should decide for themselves which method to adopt.
References
[OI1993] Oirsouw, R., Spaanderman, J. & Vries, de H. (1993). Informatie economie: investeringsstrategie voor de informatievoorziening. Schoonhoven: Academic Service.
[SA2002] Salmela, H. & Spil, T.A.M. (2002). Dynamic and emergent information systems strategy formulation and implementation. International Journal of Information Management 22, 441-460.
Introduction
In the process of creating a successful Information Strategy it is important to analyse the attainability of the IS/IT Portfolio. We must therefore understand the financial consequences of the chosen strategy or strategies. To describe it correctly we will answer the following questions:
1.Why is a financial assessment important to IS strategy?
2.What does the financial assessment entail?
3.How is financial attainability measured for the IS/IT portfolio?
4.Who is involved in creating the assessment and where is the information gathered?
5.When in the four-cycle method set out in [Salmela, Spil 2002] could the assessment take place?
Why is a financial assessment important to IS strategy?
During a series of analyses we create a financial assessment report that indicates the expected achievable results. These results can indicate failure or success in attaining the expected ROI. Obviously this information is very valuable to financial management in determining changes to the IS/IT portfolio [Gibbs 1994]. Often correction of the strategy is necessary due to budget constraints, in this process the better the information regarding expected results the more aligned the decisions become to reality. Expected results are more accurate when based on preceding situations and studies. The bottom line being strategy becomes more realistic and the chance of projects succeeding within time and budget increase. [Risk 7 - Funding, p16, Schmidt 2002]
What does the financial assessment entail?
A financial assessment consists of a report on the expected future costs and gains of future projects. In this report estimations are made of the overall costs such as development and labour costs, software licenses and hardware purchases, organizational restructuring and all other costs related to the proposed IT/IS portfolio.
The tangible gains are aspects such as higher productivity, lower communication costs and reduced labour costs. Estimations of these aspects provide the information for the yield report. It is difficult to get an accurate projection of future gains, this must be done by looking at past results and speaking with experts and managers who have the correct experience to make realistic claims. Intangible gains and yield such as stakeholder satisfaction, are not measured here as these will likely lead to ambiguous value assessment. However it does not mean they are not important, on the contrary: often success is measured by the satisfaction of its stakeholders. [Bedeian 1991]
How is financial attainability measured for the IS/IT portfolio?
There are a number of tools that can be used. First of all it is important to get an overview of expected yields and results over a given period or over a number of periods. These reports form the basis of further analysis such as the NPV, which can be a valuable indicator in decision-making about current and new projects.
The NPV indicator calculates the sum of all cash flows caused by a project and discounts these cash flows for the cost of capital. With this information it can be determined if the project is eventually profitable. [Drury 2001] To calculate the NPV (see formula 1) we need the expected cash flow (CF) for a certain number of years (t).
Usually the cash flow for an investment is negative at the start and becomes positive in later periods. This means that if the exact lifespan for a proposed information system project is unknown, it is wiser to make a conservative estimation in order to prevent overestimation of a project’s value. The results of the NPV analysis can be compared and thus an assessment can be delivered for each project in the portfolio.
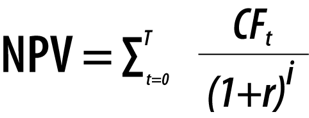
Formula 1 - NPV calculation over T periods t with interest rate r
Our recommendation is to prepare a table with all the expected cash flows and to make an NPV analysis. Such a table would look similar to the following table:
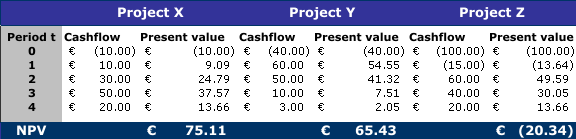
Table 6 - NPV analysis example (r = 10%) in thousands of Euro’s
Inaccuracy is a concern since the further we go into the future the more inaccurate the projection of our expected results will become. However inaccuracy may pose a problem for earlier periods as well since it is difficult to analyse the financial consequences of a project on the basis of a high-level project plan. This might introduce uncertainty about the results. The main purpose of the assessment however is not to accurately predict the required budgets and other resource allocations but to provide an indication of the attainability and future benefits of a project.
Who is involved in creating the assessment and where is the information gathered?
As mentioned before we need a number of players to create an accurate financial assessment. The following list is not exhaustive since every organization will have a different allocation of responsibilities; the list is merely an indication of possible information sources:
•IS Experts – To assess future and current costs
•Functional management – to determine how much has been saved and can be saved across the divisions through automation
•External sources – Research firms can indicate certain industry trends that can lead to cost increase or cost reduction
One could argue that Financial Management should be in the list and people in financial management could definitely provide valuable information, however we choose to leave them out since their view is on a different level. After all the purpose of the assessment is to determine which projects are useful, it is not the goal to convince financial management that certain projects are a good idea or that a larger budget is required. These things might come in a later phase.
When in the four-cycle method set out in [Salmela, Spil 2002] could the assessment take place?
The goal of the financial assessment tool is to take financial considerations into account so that project plans become more realistic. Therefore we believe that this tool belongs primarily in the third cycle since “The third cycle adds realism to planning by bringing in resource capacities and constraints under which the IS function operates." [Salmela, Spil 2002] This is exactly the goal of the financial assessment from the view of actual and future costs.
It is important to realise financial implications of proposed projects early on as this can prevent that a lot of time is spend on unprofitable projects. With the results of a financial assessment the organization can focus on projects that it can really benefit from.
The third cycle is the earliest possible opportunity for this analysis since the financial consequences of projects cannot be measured if there are no project plans which are created in this phase.
References
[Schmidt 2001] Schmidt R., Lyytinnen K. et al., Identifying Software Project Risks: An International Delphi Study, Journal of Management Information Systems / Spring 2001, Vol. 17, No. 4, pp. 5–36, 2001
[Gibbs 1994] Gibbs, W.W., Software’s chronic crisis. Scientific American, 271, 3 (September 1994), 86–95.
[Bedeian 1991] Bedeian A, Zammuto R., Organizations: Theory and design, Dryden Press (Chicago), 1991
[Salmela, Spil 2002] Salmela H, Spil, T., Dynamic and emergent information systems strategy formulation and implementation, International Journal of Information Management 22 (2002) 441–460
[Drury 2001] Drury, Management & cost accounting, 5th ed. Business Press
New Way 52. Scenario Planning
By Rob Draaijer
Within the set of tools a manager can use for strategic (information systems) planning, scenario planning stands out for its ability to capture a whole range of possibilities in rich detail. (Schoemaker 1995) Scenario analysis can be used as a starting point for formulating a preliminary IS /IT project portfolio (Salmela & Spil 2003) . Scenario planning is a powerful tool for bridging the gap between ICT professionals and managers, because it links both managerial and technical perspectives. (Erasmus 1999).
Firstly, I will provide a short introduction on what scenario planning and how scenarios should look like. Finally, I will provide an overview of a model for building scenarios and some tips for implementing scenario planning in your organization.
What is scenario planning?
Scenario planning has been defined in many different ways. Porter (1985) describes scenarios as “an internally consistent view of what the future might turn out to be - not a forecast, but one possible future outcome”. Schwartz (1991) defines scenarios as: “a tool for ordering one’s perceptions of alternative future environments in which one’s decisions might be played out”. Another definition provided by Schoemaker (1995) describes scenario planning as: “a disciplined method for imagining possible futures that companies have applied to a great range of issues”. Although these definitions are quite vague and abstract, it is important to note that scenarios are not concerned with getting the future “right”. Instead, scenarios are designed for challenging the prevailing mindset. Scenario planning tries to encourage decision makers to evaluate and consider changes that they would probably not have foreseen otherwise. Scenario planning tries to compensate for two common mistakes: overconfidence and tunnel vision (Schoemaker 1995)
According to Salmela & Spil (2003) scenario planning can be used during the third planning cycle of the four cycle method, for formulation a a preliminary IS/IT project portfolio. I agree that it can be used as a starting point for formulating a preliminary IS/IT project portfolio, but I think it could also be argued that scenario planning would fit in the second planning cycle. Firstly, scenario planning nicely fits the the objective of the second cycle: “promoting strategic thinking, creativity and innovation in the planning process” (Salmela & Spil 2003). Secondly, scenario analysis can be tightly integrated with way 18 and 19 (Leenslag 2005, Oosting 2005) of the second planning cycle. Properties of scenarios In today’s uncertain and fast paced environment there is no single deterministic future; instead today’s organizations perceive thousands possible futures. Developing scenarios is the process of shifting,
sorting and combing these possibilities into a few story lines, called scenarios. These scenarios should exhibit the following properties: (Erasmus1999, Schoemaker 1995)
1.Relevant The scenarios must significantly impact tothe future of the organization
2.Plausible The scenarios must describe futures that could reasonably occur.
3.Consistent The scenarios must be consistent withthe chosen time frame and the identified trends and uncertainties should fit together
4.Surprising The scenarios must challenge the prevailing mindset.
5.Archetypal The scenarios must describe generally different futures
6.Equilibrium The scenarios must describe a state in which the system will stay for some length of time
A good set of scenarios should consist of approximately two to four scenarios, that all fulfill these criteria to about the same degree. It is important that the scenarios must focus on the organization’s context, i.e. the organization should not be able to influence the developments outlined in the scenarios by much.
Developing scenarios
Now I will give brief overview of the 10-step model from Schoemaker (1995) for developing scenario. This methodology can be used to develop scenarios, but many more methodologies exist. The interested reader can consult Chermack, Lynham & Ruona (2001) for a good overview of different scenario planning methods.
1.Define the scope
When constructing scenarios, the first step is to delimit the time frame and the scope of the analysis. Because the developments of IS/IT are fast paced, it is very difficult to look far ahead. For example, who would have predicted ten years ago, that large telecom companies currently abandon their regular telephone systems in favor of Internet telephony (VOIP)? After you have established the time frame, it is essential to ask yourself what issues will have the greatest impact on the organization that far ahead. This can be done by looking at the past developments and asking yourself which developments, that you know about now, you wish have had known in the past.
2.Identify the major stakeholders
Now think about who will have an interest in and whom the major issues will affect. Clearly, customers, suppliers, competitors, employees, shareholders and so forth are stakeholders. You can use the strategic framework from Ward & Peppard (2002) to make an analysis of the stakeholders. Identify the role, interests and power positions of the major stakeholders.
3.Identify basic trends
Which industry trends will certainly affect the issues identified in step 1. The methodology described in way 18 and 19 (Leenslag 2005, Oosting 2005) can be used to identify these trends. After each trend is briefly described, it can be useful to classify the impact of every trend on your current strategy as positive, negative or uncertain in an uncertainty chart. An example of a basic trend is the globalization, i.e. the increasing integration of economies around the world.
4.Identify key uncertainties
Think about which events will significantly affect the issues from step 1, but whose outcomes are uncertain. Identify for each uncertainty the possible outcomes. Again, the outcomes from way 18 and 19 (Leenslag 2005, Oosting 2005) can be used as input for this step. You may also wish to identify the correlation between the uncertainties using a correlation matrix.
5.Construct initial scenario themes
Now it is possible to construct the initial themes of the different scenarios. A simple method to identify the scenarios is to identify extreme scenarios by placing all positive outcomes (relative to your current strategy) in one scenario and the negative outcomes in another one. Alternatively you can heuristically select the two uncertainties with the greatest impact, e.g. by voting, and place them in a matrix to get a starting point for four different themes.
6.Check for consistency and plausibility
Are the selected outcome combinations and trends, selected in step 5, consistent? Check whether the combinations trends and outcomes are compatible with the time frame and if they go together. Finally, check if the major stakeholders are placed in positions, they do not like and can influence. If so, the scenario will probably evolve into another stable state. Describe
that state instead.
7.Develop learning scenarios
The goal of this step is to develop strategically relevant themes by constructing simple scenarios and place the possible outcomes and trends around them. These scenarios provide boundaries, but they can be implausible, inconsistent or irrelevant. It is very important to give
the scenarios a good descriptive name.
8.Identify research needs
Now that you have constructed the major scenarios, it is possible that you need to do some additional research to increase the understanding of certain trends and uncertainties. This knowledge can be used find things you have overlooked, or increase the understanding of key
uncertainties, trends or stakeholders.
9.Develop quantitative models
At this point you assess whether certain interactions in your scenarios can be formalized in a quantitative model. Because issues surrounding information technology are often very fuzzy, it will frequently not be possible to quantify the interactions.
10.Evolve toward decision scenarios
At this stage, you will have developed scenarios that enable you to test your strategies and generate new ideas. Ask yourself the question if these are the scenarios that you want to give to others in your organization? If the answer is yes then you are finished, if not go
back to step 1 and repeat all the steps until you can successfully answer this question. You can assess the quality of the scenarios by testing them against the criteria from the “Properties of scenarios” section.
Implementing scenario planning
In order to start the scenario planning process in your organization, it may be wise to plan a one or two day session, that focuses on the developments in the environment
of organization and neglects the internal issues and strategies. In this session, the various participants in can think freely about the trends and uncertainties in the external environment. De Bono (1992) presents 13 tools for creative thinking that might be useful during these sessions. It is important to involve a diverse group of people in the scenario planning process. The more different kind of people (in terms of culture, age, sex, position and so forth) that are involved, the better the scenarios will be. (Erasmus 1999) Because scenarios describe certain possible futures, but do not directly deal with your strategy, it is advisable to also involve people form outside your organization. For example, it makes sense to invite major stakeholders, like key suppliers and customers, researchers, regulators, consultants
and so on. (Schoemaker 1995) Traditionally organizations mostly involved strategic
planners in the scenario building process. But by using the Internet and Extranets, virtual teams can be established to engage in the scenario planning process. Scenario planning is not even restricted to organizations,it can also be used for inter-organizational scenario building as well. When using these virtual teams, you will probably want to combine occasional
face-to-face interaction (to build trust) with continuous virtual interaction (to build knowledge). (Erasmus 1999)
References
Chermack, T. J., Lynham, S. A. & Ruona, W. E. A. (2001), ‘A review of scenario planning literature’, Futures Research Quarterly 17 (2), pp.7–31.
De Bono, E. (1992), Serious Creativity, Harper- Collins Publishing, New York, NY, USA.
Erasmus, D. (1999), A common language for strategy, in ‘Mastering Information Management’, Financial Times Publishing.
Leenslag, W. (2005), Way 18. list of new future acts or events, in ‘Syllabus of E-strategizing’, Not in press.
Oosting, W. (2005), Way 19. classification of certainty of future acts and events, in ‘Syllabus of E-strategizing’, Not in press.
Porter, M. E. (1985), Competitive Advantage – Creating and Sustaining Superior Performance, Free Press, New York, NY, USA.
Salmela, H. & Spil, T. A. M. (2003), ‘Dynamic and emergent information systems strategy formulation and implementation’, IT Management Select 9 (3), pp 22–37.
Schoemaker, P. J. H. (1995), ‘Scenario planning: A tool for strategic thinking’, Sloan Management Review 36 (2), pp. 25–40.
Schwartz, P. (1991), The Art of The Long View: Planning for The Future in An Uncertain World, Doubleday, New York, NY, USA.
Ward, J. & Peppard, J. (2002), Strategic Planning for Information Systems, John Wiley & Sons, Inc., New York, NY, USA.
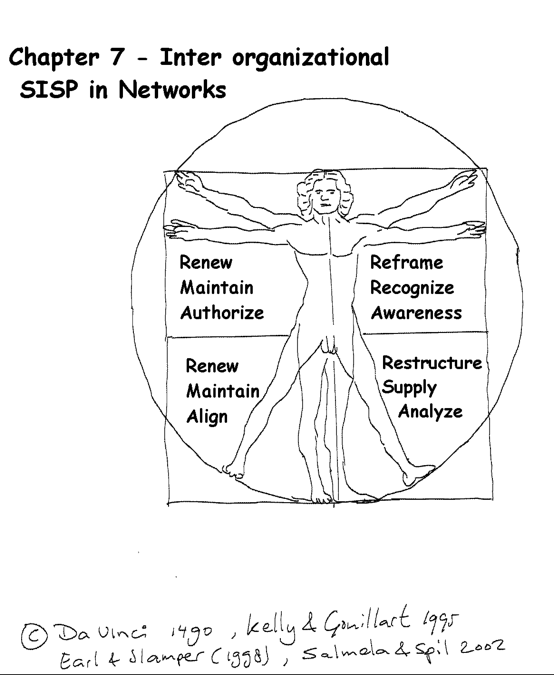
This chapter contains two recent papers accepted at major conferences in Europe. They can be referred to as:
Salmela, HTT & Spil, TAM (2006)” Strategic Information Systems Planning in Inter-organizational Networks: Adapting SISP approaches to network context”, ECMGL conference, Paris.
Spil, TAM & Salmela HTT (2006)”Strategic IS Planning for Dynamic Networks”, IRIS 2006 conference, Helsingor.
Strategic Information Systems Planning in Inter-Organizational Networks: Adapting SISP approaches to network context
Hannu Salmela, Turku School of Economics and Business Administration, Rehtorinpellonkatu 3, 20500 Turku, Finland
Ton A.M. Spil, University of Twente, PO BOX 217, 7500 AE Enschede, The Netherlands
hannu.salmela@tukkk.fi
a.a.m.spil@utwente.nl
Abstract: For over two decades, the network economy is taking shape, forcing organizations to co-operate intensively. The use of technology to support the exchange of information is essential in these networks. Still, existing methods for strategic IS planning are based on an assumption that planning takes place inside a single organization. This research asks, how these methods need to be adapted, if they were to be applied in a network context. The paper draws from several background disciplines in order to identify approaches to network governance. The review identified similarities to managerial styles within single organisations, such as reliance on personal relationships and/or hierarchic authority to enforce implementation of plan. In networks, however, strategic IS planning should also employ contractual mechanisms to cope with conflicting interests between different parties. Hence, the political approach to SISP, which is often considered as less desirable within a single organization, can constitute a far more significant approach in a network context. This paper identifies SISP dimensions that characterise political/contractual planning. In a network context, the SISP process should pay more attention to analysing the costs and benefits for different network parties in order to formulate contracts that ensure commitment to the implementation of plans. These new dimensions are illustrated through an analysis of IS planning process within five insurance companies that recently merged.
Keywords: Strategic IS planning, Inter-organizational networks, Inter-organizational systems
Introduction
During the past two decades, industrial restructuring, large-scale downsizing, vertical disaggregation, outsourcing, and elimination of layers of management have guttered the mighty multidimensional organizations of the 20th century. Replacing them are leaner, more flexible firms focused on a core technology and process, laced in a network of strategic alliances and partnerships with suppliers, distributors, and competitors (Achrol 1997). Information technology has been a central enabler for this process. The complexity of the alliances, of subcontracting agreements, and of decentralized decision-making for would have been simply impossible to manage without the development of computer networks (Castells 1996).
Despite the shift in economy towards inter-organizational networks, and the critical role of computers for such networks, very little is known about IS planning in a network context. The strategic information systems planning (SISP) is predominantly seen as a process that takes place within a single organization (Brown 2005), and only few attempts have been made to address such planning in a network context (Finnegan, Galliers and Powell 2003). Acceptance and adoption of inter-organizational information systems (IOIS) are frequently far below the sponsors’ expectations and their stabilization in a dynamic business environment is a big management challenge (Klein, Poulymenakou, Riemer, Papakiriakopoulos, Gogolin and Nikas 2004). While the literature on information partnerships and inter-organizational systems has widely discussed governance issues (Konsynski and McFarlan 1990; Kumar and Dissel 1996), the use of planning and plans to coordinate and control the use of IT in networks is not directly addressed. Few empirical studies have examined the external environment of organizations in relation to SISP (Brown 2005). Salmela and Spil (Salmela and Spil 2002) conclude that future research should aim at more dynamics and on inter-organizational aspects of SISP.
The governance of networks differs from one network to another. While some networks are based on formal contracts, others rely more on informal relations and trust between key managers. Network governance may also be based on a single powerful hub that largely determines strategic choices at the network level. The key proposition in this paper is that SISP efforts on the network level should be adapted to overall network governance style. The paper first reviews general network literature to identify basic network governance styles and then continues to discuss the assumptions behind different SISP approaches. In essence, it is suggested that rather than starting from scratch, research on network level SISP planning could build upon the results from three decades of research on traditional SISP.
The need to govern IT in networks
IT has been seen as a key enabler in the trend towards networked organizations. It constitutes a means to support coordination and control of decisions and actions by different network partners. The use of IT does, however, also constitute a governance problem of its own. A network level decision to share information and knowledge, or integrate information systems, causes several questions:
1.What are the strategic objectives of using IS on the network level?
2.What information systems applications and business process changes need to be implemented to achieve these objectives?
3.How are IS decision rights allocated e.g. which IS/IT related decisions are outsourced to network level, which remain within individual companies?
4.What network level standards should be implemented to harmonize data structures and to foster agility and reliability of the IT infrastructure?
5.How does the network organize reciprocal IT skills to implement the required applications and information management procedures?
Because of the difficulties associated with making network level agreements, all networks are likely to attempts to reduce the need for them. For instance, existence of de facto standards makes it easier to exchange information, without network specific agreements on IT. Still, knowledge sharing, information partnerships and inter-organizational systems can not be implemented simply by using standard applications and procedures. As the ambitions in the exchange of information grow, more often than not, partners end up making agreements on the use of IT.
In inter-organizational information systems co-operation typically requires detailed plans, policies, procedures and relationship specific IT investments (Kumar and Dissel 1996). In information partnerships, the divergences of interest between different parties can be overcome only if top executives share an understanding of benefits and have a “stubborn vision” of collaboration (Konsynski and McFarlan 1990). On the other hand, socio-political issues such as quest for dominance, clash of executive personalities, or incompatibility of organizational culture and values can underlie the demise of such alliances (Kumar and Dissel 1996). In knowledge exchange, cooperation and control is needed in low levels of the organization. Finnegan et al. distinguish between two approaches to IOS planning: monarchist and club. While the monarchist category is a discrete, formulated process, club is seen more as a cooperative learning activity (Finnegan et al. 2003). The IOS topology (pooled, sequential or reciprocal) is seen as affecting the choice of coordination mechanism (Kumar and Dissel 1996).
All these observations suggest that some form of planning is required. Prior research suggests that the approach used resembles the Organizational Approach: IT decisions are made as part of wider business themes (Earl 1993). The decisions are made informally and incrementally. Prior research is, however, very limited. It would be premature to say that comprehensive and formal planning approaches can not work. To strengthen the theoretical background, we shall first review general network literature to identify how networks, in general, seek for coordination and control.
Different approaches to network governance
Perhaps the most fundamental difference between a network and an organization is lack of a single authority to ensure coordination of actions. Absence of a single authority has led networks to employ a wide array of mechanisms. These mechanisms have intrigued researchers in many fields, such as economics (Williamson 1985), strategic management (Thorelli 1986), organization science, (Ouchi 1979) marketing (Wilkinson 2001), sociology (Leblebici, Salancik, Copay and King 1991), and information systems (Malone, Yates and Benjamin 1987).
In order to present these mechanisms, we distinguish three ideal types of networks:
(1)Relational networks where coordination is based on social bonds and personal contacts.
(2)Hierarchic networks that rely on the authority of one strong network partner for coordination.
(3)Contractual networks where coordination is achieved through negotiation and enforcement of contracts.
The distinction is based on Ouchi’s (1979) seminal work on organizational control mechanisms. The interplay between these basic governance mechanisms has, however, characterized the discussions about networks in many different disciplines. Adler (Adler 2001) has later described these three ideal types as a triangle (Figure 1). In essence, it suggests that we ask of networks “whether the content of their constituent ties is market exchange, hierarchical authority, or community trust” (Adler 2001, p. 219).
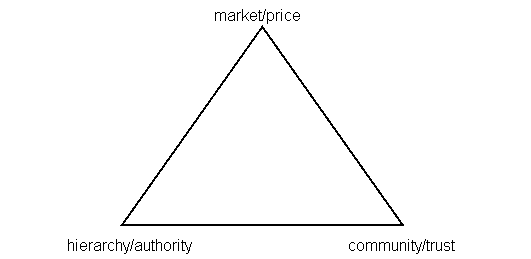
Figure 1: Network Coordination Mechanisms (Adapted from Adler 2003 and Ouchi 1980)
In the following, the three ideal types and their associated coordination mechanisms are discussed in more detail.
Relational networks
In relational networks, managers engage in behaviours that promote creation of close personal and social relationships over a long period of time. They start with minor transactions in which little trust is required because little risk is involved (Johanson and Mattsson 1987). To prove trustworthiness, managers show compliance to social norms of the network. While each network creates its own norms, typical social norms that underlie relational governance are solidarity, mutuality, flexibility, role integrity, harmonization of conflict, and restraint of power (Achrol 1997). They also socialize new members and use rituals and ceremonies to ensure that the objectives, attitudes and values of individuals substantially overlap with those of the network (Ouchi 1979).
Decisions in these networks are based on shared values and common beliefs about what behaviors, goals and policies are important or unimportant, appropriate or inappropriate, and right or wrong (Morgan and Hunt 1994). Hence, the managers use non-coercive strategies, e.g. discussions on effective ways of doing business, rather than coercive ones (Frazier and Rody, 1991). Managers in these networks have to use their social capital to influence the decision making (Nahapiet and Ghoshal 1998; Håkansson and Ford 2002). They can also eliminate many complex forms of auditing (Ouchi 1979).
Relational mechanisms are not, however, without disadvantages. Noncoercive strategies can take considerable time to implement effectively (Frazier and Rody 1991). Furthermore, an organization that is member in several networks can find it difficult to use relational mechanisms with all its networks (Frazier and Rody 1991). Paradoxically, in a relational network the party that is least committed to a relationship is likely to control negatively by restricting its development (Håkansson and Ford 2002). These limitations leave room to the use of other mechanisms that are faster, but also more vulnerable to opportunistic behavior.
Hierarchic networks
In hierarchic networks, the responsibility for cooperation and coordination is devoted to a single powerful organization, a network hub. Typical examples of network hubs are integrators that coordinate all upstream supplier firms and downstream distributor firms (e.g. Casio, Nike and Dell). Theoretically, the hub should be the one that is best positioned to monitor and cope with the critical contingencies faced by the network participants in a particular market (Achrol 1997).
The managers in the network hub can use behaviors that are quite similar to those that they have got accustomed to within a hierarchic organization. They can do strategic analysis in order to write strategic plans to compete with rival networks (Thorelli 1986). They can also define lower level plans, policies, standards and rules to facilitate cooperation within the network. The mere existence of power is often sufficient to condition others (Thorelli 1986; Håkansson and Ford 2002). Hence, other members rely on the assumption that the authority of the hub is sufficient to make all parties to implement plans. The control resembles bureaucratic control, where managers suspend judgment about orders from their superiors, e.g. a network hub, and simply follow orders (Ouchi 1979). The strength of hierarchic network is based on the simplicity and flexibility that power, hierarchy and bureaucratic control create.
Turning networks into hierarchies has, however, it problems. A business network is seldom the result of one designer. Rather, it is the outcome of the deliberations, aims and actins of a number of participants (Håkansson and Ford 2002). Coercive use of power can easily lead to loss of creativity and problem solving capacity (Frazier and Rody 1991; Achrol 1997).
Contractual networks
In contractual networks, managers take the conflicting business interests as a starting point for negotiations about future actions. The primary task of managers is to negotiate contracts that are used to govern a long-term network relationship (Williamson 1975). Rather than delegating decision making to some central party, each member in the network bases its decisions on its own economic and institutional interests. Hence, each manager is required to seek for acceptance and approval of contracts inside their own organizations, in order to ensure that they adhere to the internal rules and norms of their own organizations (Ouchi 1979; Leblebici et al. 1991).
Because all members are allowed to act opportunistically, planning in these networks resembles political decision-making and non-zero-sum games where decisions are taken in the face of some opponent. Hence, managers try to predict partner’s future actions or moves on the basis of the logic of the “game” (e.g. collective and individual outcomes with different moves) and on the context of different players (e.g. financial and institutional interests of other parties). The planning is essentially negotiation or bargaining between organizational interests, where communication can be a means of co-ordination, but also a medium of threat, bluff and deception (Bennett and Cropper 1990).
The control is based on contracts (Ring and Van de Ven 1992). Only if a proposal to adapt the contract is made, managers will bargain over the disposition of any incremental gains. Although they all have a long-term interest in effecting adaptations of a joint profit maximizing kind, each also has an interest in appropriating as much of the gain as he can (Williamson 1981). Hence, rather than resorting immediately to strict reliance on litigation – with its transaction-rupturing features – they may rely, for instance, on third party assistance (arbitration) in resolving disputes. As a pure model, market is a very efficient mechanism of coordination and control (Ouchi 1979).
As is well described in the transaction-cost theory, market mechanisms often turn out to be insufficient when partners need to make substantial long-term investments. In addition to contracts, managers tend to rely on hierarchic (e.g. through joint ventures, mergers or acquisitions) or relational (building of trust and commitment) mechanisms to govern the investments.
Adapting SISP profiles to different networks
Prior SISP research has identified several generic IS planning approaches (McLean and Soden 1977; Pyburn 1983; Earl 1993; Segars and Grover 1999). These approaches are based on a number of variables related to the SISP process. One of the underlying themes is that the SISP approach is likely to reflect the overall business planning style and governance structure of the organization. In this paper it is suggested that the same may apply to networks: strategies about the use of IT are coordinated and controlled in a similar manner as the overall network strategies. Hence, an internal SISP approach that is compatible with the network coordination mechanism might provide the best starting point for crafting a network SISP for that context.
Table 1 lists managerial behaviours that are typically used in each of the three ideal network types. It also links the SISP approaches to different types of networks. The placement of approaches to the columns is based on the similarities of coordination and control mechanisms between the three ideal network types and the descriptions of SISP approach or profile as described in the original articles (Earl 1993; Segars and Grover 1999).
Hierarchic networks provide a context with most similarities to planning within a single organization. Hence, the managers in the network hub can choose from three different approaches, depending on whether the strategist is a senior manager (design school), an analyst (planning school) or a consultant (positioning school). In IOS planning, the monarchist approach reflects planning in a situation where one dominant organisation has most power: “Planning here is traditional in that the strong organisation can set the objectives and design the process that others must meet (Finnegan et al. 2003, p. 189).
Relational networks also provide a relatively familiar context for SISP, as personal and social relations often play a crucial role in the management of organizations. Good personal relationships between IS and senior business managers are also of critical importance for the success in SISP. The Learning School/Organizational Approach for SISP that appears to have most similarity with the principles of relational governance. In IOS planning, the description of the club approach adopts similar principles: “the planning process is more participative as those involved must attempt to accommodate each other’s needs and expectations. This is a more learning environment where strategies tend to evolve” Finnegan et al. 2003, p. 189).
In contractual networks, the planning context is probably the most difficult one for SISP, because of the open conflict of interests that exists between different parties. It is still interesting to note, that the description of SISP philosophy that is based on “political school” resembles the governance of contractual networks (Segars and Grover 1999). The strategy making is bargaining and negotiation, the role of the planner is negotiator or broker, and the process is driven by parochial, rather than common, interest. The administrative approach was reported to provoke conflicts, drama and game playing (Earl 1993). Such planning was considered as less effective. In the Segars and Grover study, the political approach received lowest scores in all four planning effectiveness measures. In contractual networks, however, this approach to planning might be far more effective.
Table 1: Linking network ideal types and planning approaches
Network Ideal type | Hierarchic network | Relational network | Contractual network |
Co-ordination mechanism | Hierarchy/Authority | Community/trust | Market/price |
Decision making behaviour | Centralized design of network strategies, plans, policies, rules, and standards by a network hub. Informing other parties about plans, policies and rules | Promotion of shared network values. Creation of social norms for the network, adherence to norms. Future actions agreed informally and accepted by all parties | Negotiation and bargaining (gaming) to define each parties interests. Formulation of contracts. Approval of contracts within each unit |
Control behaviour | Monitoring: The network hub controls implementation of plans, policies, rules and standards Sanctions: Exclusion from the network – loss of business value | Monitoring: informal and non-visible, trust replaces the need for formal control Sanctions: social sanctions, loss of influence and social capital within the network | Monitoring: formal monitoring of contracts, use of third parties in conflict resolution Sanctions: defined by the norms of the marketplace |
SISP approach | Design School / Business led approach Planning School / Technological approach Positioning/ Method driven approach | Learning School/ Organizational approach | Political School Administrative Approach |
IOS planning approach | Monarchist | Club | --- |
In the following we use an illustrative case study to illustrate the theory and to give guidance to future research. The objective of the case study is to position the IOSISP process within the IOSISP triangle of figure 1. To do so we first position the IOSISP Process in the planning dimensions of Segars and Grover (Segars, 1999 #5). Then we use three additional dimensions to position the planning approach in the triangle presented in Figure 1.
Case Insurance Organizations
The insurance organization studied has merged recently with three other insurance companies and since then are “living apart together”. In IS literature this is called co-existence (Wijnhoven, Spil, Stegwee and Fa 2006). Recently another insurance company took over the whole organization making it one of the biggest insurance organizations in the country with five separate locations. In this complex network an IOSISP was created.
All people involved in the planning process were asked to position the IOSISP on the six scales from Segars and Grover (1999). An overview is given in figure 2. Most participants thought the IOSISP process was comprehensive fitting the culture of the organization where everything needs to be done in a thorough and precise manner. When the respondents were asked to compare the IOSISP process with other processes in the organization, their answers regarding the level of formalization differed. Some did report that it was a rather formal process but there were also those who stated that it was relatively informal.
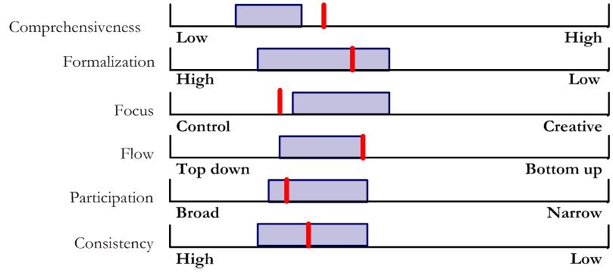
Figure 2: Interviewees’ evaluations on SISP profile with comparison to the positioning school (bars).
The focus determinant did not have such a broad range and although the method used did have some creative thinking processes most of the focus was considered more control like. The organizational structure of the insurance organizations is rather hierarchical and in the flow dimension the participants recognized a more top down approach. A broad group of people from the insurance locations participated in the planning process but still some of the participants had a feeling that it could have been broader. Within the organization there is history of creating strategic IS plans periodically. Since this was the first IOSISP, the participants did not all score this dimension (consistency) very high.
If we compare the results to the profiles of Segars and Grover we find a close match to the method driven approach or the positioning school, as illustrated in figure 2. After the acquisition, there was a clear hierarchic relationship and the use of authority in the new organizational network was natural. Hierarchy and authority are perhaps the most effective means to achieve fast results. Hence, the selection of a method driven approach to SISP was a natural choice. Choosing an organizational approach to build personal relationships and shared values is not needed, if the implementation of plans can be achieved even without them.
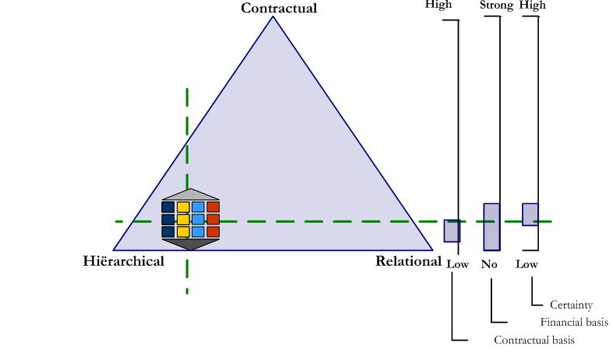
Figure 3: Positioning the SISP profile on the three-dimensional scale
As discussed above, planning process had characteristics that are more typical to hierarchical/authoritative coordination than to relational. Hence, on the horizontal axis the planning is closer to hierarchical end.
Vertically, there is no valid framework that we can use to position the IOSISP process within the triangle of figure 1. Based on the literature about contractual networks (section 3.3. above) in general, and the work by Ring and Van de Ven (1992) in particular, we added the following three new dimensions to the analysis of IOSISP process:
1.Contractual basis: the degree to which decisions were formulated as contracts between different stakeholder groups
2.Financial basis: the degree to which the planning process produced calculations for each party about costs and benefits
3.Certainty: the degree to which the resulting plan/contract ensures certainty about implementation of plans in different environmental settings
In this case we found none of these activities. Again, coordination that is based on hierarchy/authority is far more effective way to implement plans. Formulating plans as contracts to show benefits to all parties was not deemed as necessary. In the old situation, with relatively independent insurance companies, the selection of coordination mechanisms might have been different. Figure 3 illustrates the positioning of the insurance case IOSISP in the triangle. Future research is, however, needed to validate vertical dimensions and to make a reliable positioning of the approach possible.
Contributions
The objective in this paper was to review literature on network governance in general, and the governance of information systems in particular, with an objective to adapt strategic IS planning. Perhaps most importantly, the paper identifies three network types that can be used in the analysis of SISP processes in networks. It also provides several observations about how SISP needs to be adapted if it is to be used in an inter-organizational context.
The first observation is related to SISP as a process that needs to be adapted to network context. It was suggested that networks use a combination of relational, hierarchic and contractual mechanisms. It was also stated that the governance mechanisms in relational and hierarchic networks are not totally different from those used within single organizations. Hence, these networks could start from existing SISP profiles.
The second observation is related to SISP as a political process. Because conflicting interests and power struggles do emerge inside a single organization, management of conflicting interests has been addressed in prior writings of SISP. It is, however, only a marginal issue in traditional SISP. The political school fits poorly to the existing SISP research paradigm. It appears to be very ineffective if measured with traditional criteria. If SISP is to be carried out on a network level, the ability to manage conflict between different actors in the network needs to be a natural part of the SISP process. It may also mean that in particular in the market networks, the objectives of SISP need to be adjusted to the realities of the planning context.
The insurance company case illustrates the choice of coordination mechanisms. After the acquisition of several companies, also the SISP approach relied largely on the use of hierarchy and authority to ensure plan implementation. The case does, however, illustrate also other possibilities that could have been used: in principle, the new owner could have tried to build personal relationships and/or shared values with the other companies.
Suggestions for future research
The paper predicts that the planning approaches will vary, depending on the network governance style. It seems also likely that some approaches (typically practiced in a certain context) will be more successful than others. Both field studies and surveys can be used to further elaborate or to test these predictions. Survey research in background disciplines provides instruments for measuring governance styles (relational, hierarchic, contractual), whereas the measures used in prior SISP research provide a starting point for measuring SISP approaches (e.g. comprehensiveness) and planning effectiveness (awareness, alignment, coalition, learning).
Process theories are, however, needed for understanding the dynamic nature of networks, i.e. how networks change from one equilibrium state to another and how strategic IS planning can contribute to this. For instance, it is quite likely that all networks make some use of all three coordination mechanisms and that their relative importance may change over time. This calls for a longitudinal research approach. Because the use of SISP in networks is far from being an established practice, action research could also be feasible.
Summary
Strategic Information Systems Planning is often placed on a scale from comprehensive practices (relying on hierarchic mechanisms) to incremental practices (relying on relational mechanisms). When SISP is practiced on a network level, this scale will no longer be sufficient as such. We have to add a third dimension, contractual mechanisms. Lack of a single network authority means, that the decisions will always include a political dimension. The need for further studies and empirical cases that illustrate the political dimension of (IO)SISP, and the use of contracts to manage this dimension, is apparent.
Acknowledgements
This research was supported by the Dutch Research Council (NWO).
References
Achrol, R. S. (1997). "Changes in the theory of interorganizational relations in marketing: Toward a network paradigm," Journal of the Academy of Marketing Science, Vol.25, No.1, pp. 56-71.
Adler, P. S. (2001). "Market, Hierarchy, and Trust:The Knowledge Economy and the Future of Capitalism," Organization Science, Vol.12, No.2, pp. 215-135.
Bennett, P. and S. Cropper. (1990). "Uncertainty and Conflict: Combining Conflict Analysis and Strategic Choice," Journal of Behavioral Decision Making, Vol.3, pp. 29-45.
Brown, I. T. (2005). Espoused theory versus theory in use: The case of Strategic Information Systems Planning. Department of Information Systems. Capetown, University of capetown: 427.
Castells, M. (1996). The rise of the network society. Malden, Massachusetts, Blackwell Publishers Inc.
Earl, M. J. (1993). "Experiences in strategic information systems planning," MIS Quarterly, Vol.17, No.1, pp. 1-25.
Finnegan, P., R. D. Galliers and P. Powell. (2003). "Systems Planning in Business-to-Business Electronic
Commerce Environments," Information Technology and Management, Vol.4, pp. 183-198.
Frazier, G. L. and R. C. Rody. (1991). "The Use of Influence Strategies in Interfirm Relationships in Industrial Product Channels," Journal of Marketing, Vol.55, No.1, pp. 52-69.
Håkansson, H. and D. Ford. (2002). "How should companies interact in business networks," Journal of Business Research, Vol.55, No.2, pp. 133-139.
Johanson, J. and L.-G. Mattsson. (1987). "Interorganizational Relations in Industrial Systems: A Network Approach Compared with the Transaction-Cost Approach," International Studies of Management and Organization, Vol.17, No.1, pp. 34-48.
Klein, S., A. Poulymenakou, K. Riemer, D. Papakiriakopoulos, M. Gogolin and A. Nikas (2004). IOIS and Interfirm Networks – Interdependencies and Managerial Challenges. Munster, University of Munster: 57.
Konsynski, B. R. and W. E. McFarlan. (1990). "Information partnerships - Shared data, shared scale.," Harvard Business Review, pp. 114-120.
Kumar, K. and H. G. v. Dissel. (1996). "Sustainable collaboration: Managing
conflict and cooperation in interorganizational systems.," MIS Quarterly, Vol.20, No.3, pp. 279-300.
Leblebici, H., G. R. Salancik, A. Copay and T. King. (1991). "Institutional Change and the Transformation of Interorganizational Fields: An Organizational History of the U.S. Radio Broadcasting Industry," Administrative Science Quarterly, Vol.36, No.3, pp. 333-363.
Malone, T. W., J. Yates and R. I. Benjamin. (1987). "Electronic Markets and Electronic Hierarchies: Effects of Information Technology on Market Structure and Corporate Strategies," Communications of the ACM, Vol.30, No.6, pp. 484-497.
McLean, E. R. and J. V. Soden. (1977). Strategic Planning for MIS. New York, John Wiley.
Morgan, R.-M. and S.-D. Hunt. (1994). "The commitment-trust theory of relationship marketing," Journal-of-Marketing, Vol.58, No.3, pp. 20-38.
Nahapiet, J. and S. Ghoshal. (1998). "Social Capital, Intellectual Capital, and the Organizational Advantage," Academy of Management Review, Vol.23, No.2, pp. 242-266.
Ouchi, W. G. (1979). "A conceptual framework for the design of organizational control mechanisms," Management Science, Vol.25, No.9, pp. 833-848.
Pyburn, P. (1983). "Linking the MIS plan with corporate strategy: An exploratory study," MIS Quarterly, Vol.7, No.2, pp. 1-14.
Ring, P. S. and A. H. Van de Ven. (1992). "Structuring cooperative relationships between organizations," Strategic Management Journal, Vol.13, pp. 483-498.
Salmela, H. and T. A. Spil. (2002). "Dynamic and emergent information systems strategy formulation and implementation," International Journal of Information Management, Vol.22, No.6, pp. 441-460.
Segars, A. H. and V. Grover. (1999). "Profiles of strategic information systems planning," Information Systems Research, Vol.10, No.3, pp. 199-232.
Thorelli, H. B. (1986). "Networks: between markets and hierarchies," Strategic Management Journal, Vol.7, pp. 37-51.
Wijnhoven, F., T. Spil, R. Stegwee and R. T. A. Fa. (2006). "Post-merger IT integration strategies: An IT alignment perspective," Journal of Strategic Information Systems, Vol.15, No.1, pp. 5-28.
Wilkinson, I. (2001). "A History of Network and Channels Thinking in Marketing in the 20th Century," Australasian Marketing Journal, Vol.9, No.2, pp. 23-52.
Williamson, O. E. (1975). Markets and Hierarchies: Analysis and Anti-Trust Implications. New York., The Free Press.
Williamson, O. E. (1981). "The Economics of Organization: The Transaction Cost Approach," American Journal of Sociology, Vol.87, No.3, pp. 548-577.
Williamson, O. E. (1985). The Economic Institutions of Capitalism. Firms, Markets, Relational Contsructing., The Free Press.
Maintaining a new equilibrium with a dynamic political approach for SISP in organizational networks
Ton AM Spil
Hannu TT Salmela
University of Twente, The Netherlands
Turku School of Economics and Business Administration, Finland
This research was supported by the Dutch Research Council (NWO)
Abstract.
Strategic alliances, partnerships, coalitions, franchises, consortia, mergers, acquisitions and many other network forms are common practice these days. Although many researchers showed the problems involved, especially in non-hierarchical networks, the networking society is growing rapidly. Existing methods for Strategic Information Systems Planning (SISP) are based on the assumption that planning takes place inside a single organization. This research asks, how the planning processes need to be adapted, if they were to be applied in a network context. The paper draws from corporate strategy, business transformation and information strategy background disciplines in order to identify differences between a single organisation and a network. Based on this review it is argued that on a network level, strategic IS planning should rely on a dynamic planning process, to deal with the inherently evolutionary nature of strategy formation in networks. Secondly, the study shows that contractual governance needs to be attended in Inter-Organizational SISP especially in combination with the authorization or maintaining process. By lack of hierarchy it is far more difficult to implement the contribution of the planning process. Our advice is to use a dynamic political approach.
1. Introduction
Grover & Segars(2005) state that the SISP process and SISP learning are underemphasized in IS research. The strategic information systems planning is predominantly seen as a process that takes place within a single organization (Brown 2005) despite the shift in economy towards inter-organizational networks and the critical role of information systems for such networks. Only few attempts have been made to address such planning in a network context (Finnegan et al. 2003). Acceptance and adoption of interorganizational information systems (IOIS) are frequently far below the sponsors’ expectations and their stabilization in a dynamic business environment is a big management challenge (Klein et al. 2004). Salmela & Spil (2002) conclude that future research should aim at more dynamics and on inter-organizational aspects of SISP. While the literature on information partnerships and inter-organizational systems (Konsynski et al. 1990; Kumar et al. 1996) has widely discussed governance issues, the use of planning and plans to coordinate and control the use of IT in networks is not directly addressed.
Few empirical studies have examined the external environment of organizations in relation to SISP (Brown 2005). The objective of this paper is to develop a dynamic method for SISP that managers in inter-organizational networks could use that also can be used to form a basis for empirical research in the future. The paper first reviews typical dimensions of SISP effectiveness (Segars et al. 1999) to different network contexts. It is acknowledged, however, that the lack of a formal, unequivocal authority in organizational networks (Homburg 1999) and the evolutionary nature of network strategies calls for a dynamic SISP process. The dynamic SISP method is a further development of continuous and interactive methods presented in prior literature. The political school of SISP will be emphasized in the contribution section since there is a best fit with the market orientation (Salmela et al. 2006). The participation is based on agreements, which can be formalized into contracts (Wassenaar 1995). In essence, the method attempts to provide both adaptability to different network governance styles and sufficient flexibility and continuity for a dynamic network environment.
2. The IT governance challenge in networks
Ring & Van de Ven (1992) argue why organizations start repeating contract-based transactions although they should use hierarchic arrangements (Williamson 1975). Companies have used varying approaches to control and coordinate. An organization interested in preserving and advancing their interests have to persuade others of their legitimacy (Brown 1998). The contract based governance include strategic alliances, coalitions and other kinds of network organizations (Ring et al. 1992).
New resources may be created and put under the jurisdiction of organizations that have not previously been claimants in particular areas (Markus 1983). Existing power structures are challenged which may trigger political behaviour (Fehse et al. 2002). Buchanan and Badham (1999) distinguish four categories: Conflict avoidance, Manipulation, Forming alliances and Scapegoating.
Political behaviour can be defined as the practical domain of power in action, worked out through the use of concrete political actions and broader tactics (Pettigrew 1977). Exactly those aspects appear in the political school of thoughts (Segars & Grover, 1999). The main theme is “bargain and negotiate” and the core belief strategic planning as a power process. “The primary role of the planner is negotiator or broker between organizational interests”.
The challenge for IT Governance therefore is to externalize these political thoughts which are close to the administrative approach as described by Earl (1993) where strategic plans emerge, consistent with dynamic and emergent thoughts (Salmela & Spil, 2002). To study these thoughts we introduce the transactional dimension in figure 1.
3. A dynamic view of network governance
The dynamic view of networks introduces a new variable, time, to the analysis of network governance. A longitudinal analysis of most networks reveals, that rather than being governed, inter-organizational relationships are constantly being established, maintained, developed, and broken (Johanson et al. 1987). Also the mechanisms used for governing these relationships evolve through time between relational, hierarchic, and contractual ones.
The concepts for analyzing the networking behaviour of individual companies over time are fairly well established. In industrial economics, individual firm’s actions are explained as cumulative processes where the firm develops the relationships that secure its access to important resources or capabilities (Johanson et al. 1987). To manage their relationships, companies balance the benefits and costs of exploitation versus exploration, i.e. they trade off the gains from working more closely with existing partners against the potential gains from developing new relations (Håkansson et al. 2002; March 1991; Wilkinson et al. 2002). Ability to integrate internal and external competences is critical for addressing rapidly changing environments(Teese et al. 1997).
The concepts for analyzing dynamic change on the network level are still limited (Wilkinson 2001). At this level the outcomes are far more complex and may not easily, or even in principle, be traced to the actions of individual network members (Håkansson et al. 2002; March 1996; Wilkinson 2001).
The identification of stages in the network growth has been one way to conceptualize the evolution at the network level. For instance, Ford (1980) discusses how a network can evolve through pre-relationship and early stages to development stage, the long-term stage and the final stage. It is acknowledged, however, that there is no inevitability for such development. Rather, the formation of a network is an emergent process that is contingent upon many variables (Ford 1980).
Another stream of research is based on the longitudinal analysis of change in industry networks, e.g. (Leblebici et al. 1991). These stories bring into surface also the interaction between the network and its context. While powerful organizations can and do influence their immediate relational networks, they also make attempts to influence the more general environment. For instance, those linked to the state can attempt to build their goals and procedures directly into society as institutional rules. The organizations within networks can also promote establishment of common standards, rules and norms within the industry. After becoming established conventions, they need not be supported by coercive or normative processes (Leblebici et al. 1991).
Descriptions of industry level change view technology as a primary cause for industry level change: a new technology offers new possibilities to solve problems (Leblebici et al. 1991). As some innovative organizations take advantage of these technologies, they also put pressures for other’s to change. Once the innovation gains legitimacy, others imitate the practice and accept its validity and value, sometimes even uncritically (Barley et al. 1997).
The idea that the new technology drives change in industry networks is not new for the information systems literature. For instance, Venkatraman suggests that the highest risks and returns from IT are achieved when IT is used to redefine industry structures (Venkatraman 1994). The stories of the competitive use of IT are also often stories of IT induced changes in the industry networks (Grover et al. 1999).
Hence, the starting point SISP in a network context may more often than not be a situation where the network is only emerging. The situation is far more complex than simply aligning the use of IT to the business objectives within an existing network, which already possesses established mechanisms for its governance. In such a situation it is very difficult to imagine a comprehensive strategic IS plan to be a viable solution. Rather, if planning is to be used, the process needs to be continuous and iterative. To study the dynamics of IOSISP we can use the process dimensions of Segars & Grover (1999) and the differences between comprehensive and iterative planning as laid down by many researchers (Ciborra 1994; King 1978; Salmela et al. 2002; Vitale et al. 1986).
Together with the transactional dimension from section 3, figure 1 shows the research model in which an IOSISP should be executed. The contractual, hierarchic and relational quadrants are well known in literature (Adler 2001; Ouchi 1979). We choose incremental as the fourth quadrant and try to show in section 4 how with cyclic processes value can be added to several organizations.
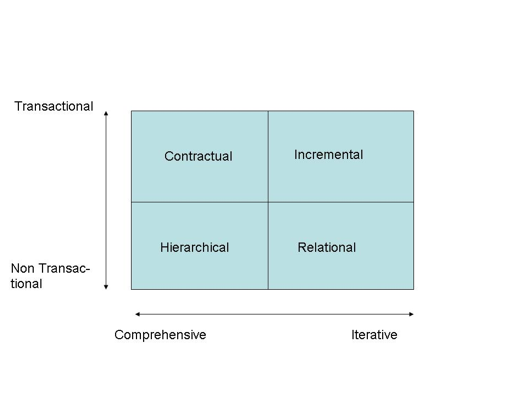
Figure 1 – Context of (Inter) Organizational Strategic IS Planning
4. A dynamic process view of SISP in interorganizational networks
As argued above, networks are likely to require a more dynamic strategic IS Planning process than the ones typically used in individual organisations. The introduction learned that not many empirical studies address the problem of inter-organizational planning (Brown 2005). One of the reasons for this is that a dynamic external process model is missing. In this section we build a blueprint of a dynamic strategic IS planning process for networks. This blueprint is derived from the transformation notion of Gouillart and Kelly (Gouillart et al. 1995), applied by Earl and Sampler (Earl et al. 1998) to information technology specifically. These ideas can be mapped to the effectiveness themes of Segars & Grover with special attention to the political school. In addition, it incorporates dynamic elements from the four cycles model (Salmela et al. 2002), the process model (Mentzas 1997), and from prior descriptions of iterative SISP processes (Salmela et al. 2002; Venkatraman et al. 1993).
In essence, the process comprises four cycles that are repeated annually. The first cycle asks different network parties to critically evaluate how strategic IS planning is practiced in companies and on the level of the whole network. The second cycle concentrates on the analysis of the network level potential inherent in IT – can the network use IT competitively. The third cycle focuses on practical constraints e.g. differences in business practices and information architectures that need to be solved. Finally, the fourth cycle formulates and seeks approval for carefully argued strategic proposals.
What makes the process dynamic is that the repeating of similar cycles enables the network to start small and evolve incrementally over years. Also the time that managers devote to planning can vary from one planning session a year to monthly meetings, depending on the significance and strategic potential of IT for the network. The adaptation to network governance styles can be done by altering the emphasis between cycles. Nevertheless, it is the authorization cycle that is both critical and significant in all network contexts. The themes of the four cycles are illustrated in figure 2 and the content and objectives in each cycle will be further elaborated below.
Create Strategic Awareness
The first cycle aims to raise awareness on the issue of strategic formulation (Mentzas 1997). Reframing network direction is the shifting of the partnering companies' conception of what the network is and what it can achieve (Gouillart et al. 1995). It addresses the corporate mind. Corporations often get stuck in certain way of thinking, and lose the ability to develop fresh mental models of what they are and what they could become. Reframing opens the corporate mind and infuses it with new visions and new resolve. The main focus in the first process is to evaluate and create a new planning approach (Mentzas 1997; Salmela et al. 2002). Earl and Sampler (Earl et al. 1998) call this process “recognizing the disequilibrium”. They question the value of IT and the IT-function which they call supply and assess the demand discontinuities.
The inter-organizational SISP starts with the awareness that information systems go beyond the scope and the range of the organization itself. This can be a strategic choice or a necessity. The turbulence and orientation phases of van der Poel (Poel 1995) also describes the dynamic environment within an organization, externally this will only be worse. Participation is the most common success factor in SISP literature and for an internal SISP process difficult to maintain. A certain level of cooperation is needed to reduce the potential conflicts(Henderson 1990). The IS planners must ensure that the “bases of power” are supportive of the planning process (Segars & Grover 1999). For inter-organizational SISP it will be a tremendous effort to remain top management participation throughout the process. There will be many stakeholders with many interests (Ciborra et al. 1994; Galliers et al. 1991) but the main question is the same: What is the value of IT for the network but…… Value for one organization can mean investment for the other. A “pre-contract” might be the result of this cycle in which the interests of all parties are stated.
Analyze Information Supply
In this cycle the network seeks radical performance improvements (Earl et al. 1998). Restructuring is the domain where payoffs are fastest and cultural difficulties are greatest, often making layoffs and the anxieties associated with them an unavoidable side effect (Gouillart et al. 1995). Mentzas (Mentzas 1997) regards information as a strategic resource in this phase and wants to analyze the IT use. According to Spil and Salmela (Salmela et al. 2002) this process adds realism to the planning. They describe it as the third process but they also indicate that the order and iteration of the phases must be seen as dynamic. A certain degree of analysis is realized for the processes, procedures and technologies for better understanding the organization (Segars & Grover, 1999). It is not difficult to argue that with more organizations involved the latter will be much more difficult.


![]()
![]()

Figure 2 – a dynamic process model of strategic information systems planning derived from Gouillart and Kelly (1995), Earl and Sampler(1998), Segars & Grover (1999) and (Spil et al. 1999).
Inter organizational information supply will mean many suppliers on a higher level leading to multiple opportunities. That, together with complex infrastructures will allow little analysis and much opportunity generation. Strategic information resources are often internally dedicated to planned and running projects. This will lever the chance of conflicts. All participating organizations in the made their own choices for information systems so there is likely to be a non fit between inter organizational systems and a need for standardization. In this cycle there is need for transaction governance like in the electronic marketplaces(Bakos 1991; Benjamin et al. 1995; Malone et al. 1987; Wassenaar 2002). Since this cycle is on supply most of this governance will be devoted to analyzing costs or investments for each partner both in money, time and capacity.
Align Business and Information Domain
The linkage between Business Strategy and IS Strategy is already mentioned by King (King 1978) but really came alive in the early 1990s by researchers from the MIT-school (Venkatraman et al. 1993). In the third cycle, Earl and Sampler (1998) focus on future value by emphasizing the demand management. Revitalization the enterprise is about igniting growth by linking the corporate body to the environment (Gouillart et al. 1995). All organizations want to grow, but the sources of growth often are elusive, making the process of achieving growth more challenging and protracted than the previous process. Strategy conception identifies opportunities and scenario’s (Mentzas 1997). These opportunities need to be clarified and formally expressed. This process has to create a shared vision between senior managers in the organization(Salmela et al. 2002).
The top managers in a network have to have a shared vision and values as argued in the relational networks. They have to do this before they are able to create an information strategy. The political dimension gets more important in this phase as we get closer to decision making and have a better idea about costs and profits involved. The future Value of IT is often over estimated and might trouble the relational network at this point. It will be very difficult to formalize this process and we see that tools like strategic option generators (Ward et al. 2002) are used in this process which is also confirmed by (Wassenaar 2002). Interorganizational transactional alignment will show all benefits for all stakeholders.
Authorize and Maintain new equilibrium
Renewing the organization deals with the social side of the transformation, and with the spirit of the company (Gouillart et al. 1995). It is about creating capacity, thus allowing the company to regenerate itself. It involves the cultivation of a reflex of adaptation to environmental changes. The primary objective is to reduce potential for conflict that might jeopardize the implementation of the plan (Segars et al. 1998). The most important task in this process is for both business and IT function to recognize that information management needs continuous improvement (Earl et al. 1998). Salmela and Spil (Salmela et al. 2002) emphasize defining criteria on which authorization can be based. It also requires the definition of concrete actions (Mentzas 1997).
Strategic resources are a main issue in this process and on inter-organizational level it is even more important. In this phase we can expect a question like: who is going to pay for that? A risk analysis would be necessary but in a network situation it is not clear who is risking what which makes the situation not easy to control. Another point of concern is the project organizations that have to be staffed by several organizations. There will be a tendency to appoint a group to one organization to keep the locus of control.
The decision making itself will be more subjective than for internal SISP since there are no clear criteria on higher level to decide on. It seems to have less details and seems to be less formal (Finnegan et al. 2003). In this way it will be difficult to remain a balance between demand and supply of information with a near impossibility to freeze the situation. Nonetheless, a final contract should be delivered with clear agreements about the full programme.
5.Case Healthcare Organizations
There is little empirical evidence that describe inter-organizational SISP processes. In this section we describe the processes of fifteen healthcare partners and four knowledge institutes to create a new information strategy for the whole region over a period of six years. This case is derived from a careful document analysis and longitudinal observations of one of the authors. The objective is to get a better view on IOSISP and to derive a research model for further empirical study both in Finland and the Netherlands. Table 1 summarises the questions derived from the case observations.
Creating Strategic Awareness
The project started out in 1999 and called itself ICT connection of the region. The partners had different sizes and different interests. In strategic group sessions every participant introduced themselves in a presentation and many ideas were generated. Every partner was sure of the necessity of the collaboration. After four rather broad sessions, a small group continued to prepare a funding proposal for the ministry. The major control mechanism at this stage was relational. The meetings were very informal and participation was voluntary and participation varied. After the funding proposal was declined there was a difficult time in holding the partners together but big involvement of top management of two large partners kept the connection going.
Analyze Information Supply
In the second process an e-health architecture was build on a global level. A radical performance improvement is proposed in a next generation scenario. The participation in this process was mainly from CIO’s and not from CEO’s. The final outcome was a rather futuristic architecture laid down in a funding proposal. As a result of the authorization cycle a new analysis cycle was started with two project plans that covered infrastructure and application service providing.
Align Business and Information Domain
Creating a shared vision was one of the most important results of this strategy process. At first all parties involved presented themselves and many ideas were generated. In a later stadium the main actors did a strategic session at a consultancy firm. The main objectives and the overall roadmap was derived from this session. From that point the alignment was more directed to stating objectives for the seven projects generated whit little attention to the overall goals.
Authorize and Maintain new equilibrium
After staying a long time in the previous three processes without getting funding and without plans for funding ICT themselves there was new initiative called innovation care in the region that set up a sort of programme management. The regional ministry donated money to create seven project plans and so the strategy process came into a contractual control situations where explicit business models were build.
Case Results
The IOSISP process of the fifteen healthcare organizations changed a lot over time but it was not a linear learning process as shown in recent literature (Grover et al. 2005). The picture would show more ups and downs. In general there was too much reliance on relational coordination mechanisms in the first period. Also the funding problems caused hick ups in the continuity of the process.
A critical appraisal of costs and benefits from the start could have made the process much clearer but it is doubtful if such clear statements could be made in the first period since there was no shared vision at that point in time. The alignment cycle seemed to be more dynamic than the other cycles. In that way many ideas could be generated but little attention was given to implementing those ideas. Analysis did happen but more in an organizational context than in an interorganizational context. Interoperability and communication were main overall issues but difficult to address.
Both authorization and contractual coordination were a problem in the IOSISP process, especially in the first period until 2004. The Project Initiation Documents in the later stage can be seen as a form of contractual behaviour but no real obligations were made.
Context\Process | Make Aware | Analyze | Align | Authorize |
Loss of creativity? Interorganizational disequilibrium? Scope? | Strategic analysis for competitive advantage? Detailed plans? New standards? | Formal methods? Interorganizational vision? | Single powerful organization? Bureaucratic control? Risks? | |
Personal relationships? Participation? | Social norms? Reducement of conflicts? | Shared values? Future value? | Time to implement? Commitment? Social side of transformation? Continuous improvements? Tasks? | |
Business interests as a starting point? How to build a pre-contract? | Communication is co-ordination or threat? Infrastructural aspects difficult to sell? | Own interests? Political decision making? Growth? | Acceptance and approval own organization? Third party assistance? Long term investments? Who is paying what? | |
Continuity? Changing stakeholders? | Ability to change infrastructure? | More cycles needed? Changing objectives? | Learning? Power shift? |
Table 1 – Coordination mechanisms versus SISP processes (The grey questions refer to areas that are of particular interest in networks and hence need most attention in further research).
Contributions for research
The objective in this paper was to review literature on network governance in general, and the governance of information systems in particular, with an objective to discuss the role of strategic IS planning. The paper provides several observations about how SISP needs to be adapted if it is to be used in an inter-organizational context.
The main observation is related to the dynamic and iterative nature of SISP. The requirement for SISP to enable changes in both the strategy process and content of plans is not new. In a network setting, however, the fact that no one actor is in charge means that the network strategy process is highly interactive, evolutionary and responsive. SISP process must be able maintain continuity despite the fact that the participants in the network may change, the governance structures may mature as the relationship evolves, external regulations and standards can radically influence what is possible, etc. Hence, we suggest that continuous and iterative models of SISP provide a better starting point for inter-organizational SISP than models that make a clear distinction between strategy formulation as a separate study and strategy implementation.
The dynamic process view of SISP in interorganizational networks is a first attempt to incorporate these observations into a method. While having similarities to prior SISP methods, it also identifies issues that require special attention particularly in a network context, such as the significance of the authorization processes (See table 1). Next to theoretical answers, the paper contributes many empirical questions. Future research will try to answer these questions by building an interview model from the framework given by table 1. The case study turned out to be more dynamic than we thought it would be. The question is whether this was by necessity or by choice?
Suggestions for future research
Perhaps most importantly, this paper calls for rigorous empirical studies that investigate the ways, how organizations within networks coordinate their use of information systems. This paper lays ground for the development of both variance and process theories (Markus et al. 1988) about the role of strategic IS planning in networks.
The paper predicts that the planning approaches will vary, depending on the network governance style. It seems also likely that some approaches (typically practiced in a certain context) will be more successful than others. Both field studies and surveys can be used to further elaborate or to test these predictions. Survey research in background disciplines provides instruments for measuring governance styles (relational, hierarchic, contractual), whereas the measures used in prior SISP research provide a starting point for measuring SISP approaches (Segars et al.) and planning effectiveness (awareness, alignment, coalition, learning). Qualitative research in organizational networks should provide a basis for further study in (IO)+SISP.
Summary
This paper started out with the question how existing SISP methods should be changed to adapt to a network context. Therefore we combined a contextual way of thinking with a process view to arrive at the following conclusions. Strategic Information Systems Planning is often placed on a scale from comprehensive practices (relying on hierarchic mechanisms) to incremental practices (relying on relational mechanisms). When SISP is practiced on a network level, this scale will no longer be sufficient as such. We have to add a third dimension, contractual mechanisms. Secondly, the context of SISP within a network is likely to change continuously. Therefore SISP should incorporate a dynamic planning method that is flexible but still able to maintain the changes incurred. In addition, new mechanisms are needed to allow real strategic information systems thinking. Finally we notice more questions in the authorization process of SISP than in the other processes. Lack of a single authority in the network means that the final decisions will be political or contractual ones. The need for further studies and empirical cases that illustrate the political dimension of (IO)SISP is apparent.
References
Adler, P.S. "Market, Hierarchie and Trust: The Knowledge Economy and the future of Capitalism," Organization Science (12:2) 2001, pp 215-235.
Bakos, J.Y. "Electronic Marketplaces," MIS Quarterly:September) 1991, pp 295-310.
Barley, S.R., and Tolbert, P.S. "Institutionalization and Structuration: Studying the Links between Action and Institution," Organization Studies (18:1) 1997, pp 93-117.
Benjamin, R.I., and Wigand, R.I. "Electronic Markets and virtual Value Chains on the information Super Highway," Sloan Management Review (36) 1995, pp 62-72.
Brown, A.D. "Narrative, politics and legitimacy in an IT implementation," Journal of Management Studies (35:1) 1998, pp 35-58.
Brown, I.T. "Espoused theory versus theory in use: The case of Strategic Information Systems Planning," in: Department of Information Systems, University of capetown, Capetown, 2005, p. 427.
Buchanan, D., and Badham, R. Power, Politics and Organizational Change. Winning the Turf Game Sage, London, 1999.
Ciborra, C. "The Grassroots of IT and Strategy," in: Strategic Information Systems, C. Ciborra and T. Jelassi (eds.), John Wiley & Sons, Chichester, 1994, pp. 3-24.
Ciborra, C.U., and Lanzara, G.F. "Formative Contexts and Information Technology: Understanding the Dynamics of Innovation in Organizations," Accounting, Management and Information Technologies (4:2 ) 1994.
Earl, M.J., and Sampler, J.L. "Market management to transform the IT organization," Sloan Management Review), Summer 1998, pp 9-17.
Fehse, K., Krabbendam, K., and Boer, H. "The role of politics in the implementation of information systems: a hospital case," International Journal of Healthcare Technology and Management (4:3/4) 2002, pp 205-219.
Finnegan, P., Galliers, R.D., and Powell, P. "Systems Planning in Business-to-Business Electronic
Commerce Environments," Information Technology and Management (4) 2003, pp 183-198.
Ford, D. "The development of Buyer-Seller Relationships in Industrial Markets," European Journal of Marketing (15:5/6) 1980, pp 339-354.
Galliers, R.D., and Sutherland, A.R. "Information Systems Management and Strategy Formulation: The "Stages of Growth Model" Revisited," Journal of Information Systems (1:1), March 1991.
Gouillart, F.J., and Kelly, J.N. Transforming the organization McGraw-Hill inc, New York, 1995.
Grover, V., and Ramanlal, P. "Six myths of information and markets: Information technology networks, electronic commerce, and the battle for consumer surplus," MIS Quarterly (23:4), Dec. 1999, pp 465-495.
Grover, V., and Segars, A.H. "An empirical evaluation of stages of SISP: patterns of process design and effectiveness," Information & Management (42) 2005, pp 761-779.
Håkansson, H., and Ford, D. "How should companies interact in business networks," Journal of Business Research (55:2) 2002, pp 133-139.
Henderson, J.C. "Plugging into strategic partnerships:The critical IS connection," Sloan Management Review (31) 1990, pp 7-18.
Homburg, V.M.F. "The political economy of information management," in: Bedrijfskunde, University of Groningen, Groningen, 1999, p. 248.
Johanson, J., and Mattsson, L.-G. "Interorganizational Relations in Industrial Systems: A Network Approach Compared with the Transaction-Cost Approach," International Studies of Management and Organization (17:1) 1987, pp 34-48.
King, W.R. "Strategic Planning for management information systems," MIS Quarterly:2) 1978, pp 27-37.
Klein, S., Poulymenakou, A., Riemer, K., Papakiriakopoulos, D., Gogolin, M., and Nikas, A. "IOIS and Interfirm Networks –Interdependencies and Managerial Challenges," University of Munster, Munster, p. 57.
Konsynski, B.R., and McFarlan, W.E. "Information partnerships - Shared data, shared scale.," Harvard Business Review), september-october 1990, pp 114-120.
Kumar, K., and Dissel, H.G.v. "Sustainable collaboration: Managing conflict and cooperation in interorganizational systems.," MIS Quarterly (20:3) 1996, pp 279-300.
Leblebici, H., Salancik, G.R., Copay, A., and King, T. "Institutional Change and the Transformation of Interorganizational Fields: An Organizational History of the U.S. Radio Broadcasting Industry," Administrative Science Quarterly (36:3) 1991, pp 333-363.
Malone, T.W., Yates, J., and Benjamin, R.I. "Electronic Markets and Electronic Hierarchies: Effects of Information Technology on Market Structure and Corporate Strategies," Communications of the ACM (30:6) 1987, pp 484-497.
March, J.G. "Exploration and Exploitation in Organizational Learning," Organization Science (2:1) 1991, pp 71-87.
March, J.G. "Continuity and Change in Organizational Action," Administrative Science Quarterly (41) 1996, pp 278-287.
Markus, M.L. "Power, Politics and MIS Implementation," Communications of the ACM (26:6) 1983, pp 430-444.
Markus, M.L., and Robey, D. "Information technology and organizational change: causal structure in theory and research," Management Science (34:5) 1988, pp 583 - 598.
Mentzas, G. "Implementing an IS Strategy - a team approach," Long Range Planning (30:1) 1997, pp 84-95.
Ouchi, W.G. "A conceptual framework for the design of organizational control mechanisms," Management Science (25:9) 1979, pp 833-848.
Pettigrew, A.M. "Strategy formulation as a political process," International Studies of Management and Organisation (7:2) 1977, pp 78-87.
Poel, K.G.v.d. "Theory and practice of information strategy," in: Information Systems, University of Brabant, Tilburg, 1995.
Ring, P., and Ven, A.H.V.d. "Structuring Cooperative Relationships Between Organizations," Strategic Management Journal (13) 1992, pp 483-498.
Salmela, H., and Spil, T. "SISP in Inter-organizational Networks: Adapting SISP approaches to network context," ECMLG, Paris, 2006.
Salmela, H., and Spil, T.A. "Dynamic and emergent information systems strategy formulation and implementation," International Journal of Information Management (22:6) 2002, pp 441-460.
Segars, A.H., and Grover, V. "Strategic Information Systems Planning Success: An Investigation of the Construct and its Measurement," MIS Quarterly (22:2 (June)) 1998, pp 139-163.
Segars, A.H., and Grover, V. "Profiles of strategic information systems planning," Information Systems Research (10:3) 1999, pp 199-232.
Spil, T., and Salmela, H. "The fall of Strategic Information Systems Planning and the rise of a dynamic IS Strategy," IRIS, Keuruu, 1999, pp. 237-249.
Teese, D.J., Pisano, G., and Shuen, A. "Dynamic Capabilities andStrategic Management," Strategic Management Journal (18:7) 1997, pp 509-533.
Venkatraman, N. "IT-enabled business transformation: from automation to business scope redefinition," Sloan Management Review (35:2) 1994, pp 73-87.
Venkatraman, N., Henderson, J.C., and Oldach, S. "Continuous Strategic Alignment: Exploiting Information Technology Capabilities for Competitive Success," European Management Journal (11:2) 1993, pp 139-149.
Vitale, M.R., Ives, B., and Beath, C.M. "Linking Information Technology and corporate strategy: An Organizational View," International Conference on Information Systems, San Diego, 1986, pp. 265-276.
Ward, J., and Peppard, J. Strategic Planning for Information Systems John Wiley & Sons LTD, Cranfield, 2002.
Wassenaar, D.A. "Informatieplanning in transactioneel perspectief," in: Information Management, University of Twente, Amsterdam, 1995, p. 320.
Wassenaar, D.A. "Towards an eclectic approach to strategic inter-organisational systems (IOS) management-or how to act strategically in a turbulent E-business environment-," International Conference on Electronic Commerce, Hongkong, 2002.
Wilkinson, I. "A History of Network and Channels Thinking in Marketing in the 20th Century," Australasian Marketing Journal (9:2) 2001, pp 23-52.
Wilkinson, I., and Young, L. "On cooperating: firms, relations and networks," Journal of Business Research (55:2) 2002, pp 123-132.
Williamson, O.E. Markets and Hierarchies: Analysis and Anti-Trust Implications. The Free Press, New York., 1975.
Part 1 - Year report 2003 Information Management University
This chapter looks back at the most important issues of last year. More extensive information can be found in the company plan of the Information Management (IM) department.
Development activities have been stopped since the 20th of November, due to the fire in the computer building. In the first quarter of 2003, still much attention was paid to get the production environments operational again. This included data restoring actions.
Information policy
The ‘Policy Information services & Automation’ has been established by the board of managers (BoM); The conclusions of the policy give direction to the activities in the next years on behalf of the automated information service and it makes the UNIVERSITY organisation policy operational on this aspect.
The BoM recorded that the ICT related costs of organisational systems have to be paid for integral and central. The IM DEPARTMENT has been asked to calculate, in a budget neutral way, the financial support of this.
ICT in education
The merge of the Library, the Educational centre and the ICT department especially benefited a closer cooperation in the field of ICT in education. The lines are shorter and the decision-making is more direct.
The UNIVERSITY migrated from TeleTOP 4 to 5. The management of this version of TT is placed in the TeleTOP BV in founding. IM department will maintain UNIVERSITY specific functionality.
In the portal project MyCampus, the Oracle Portal is definitely chosen for the realisation of the student and employee portal. This will be established in 2004. The use of WebHare as content management resource for @Campus (former UTIS) has taken a considerable flight. Many units, services and faculties, work with WebHare.
For the Digital University, the Digital Portfolio (DPF) version 2 is produced. A number of educations on the UNIVERSITY will also start using DPF.
Besides the DPF project for the DU, different other projects were conducted in DU association. Examples are the use of formulas on the web and the application of testing programmes.
The SURF association made a start with project DARE (Digital Academic Repositories). This project promises interesting developments in the coming years, in which the UNIVERSITY will gladly fulfil a pulling role.
Digitalising Company processes
To digitalise the financial function (DFF) and the arrangement of the accounting house, the workflow application is fully used. At the end of 2003, the Financial Economic Department will start using workflow applications for handing in domestic travel declarations and the processing of purchase invoices. In 2004, the remaining declarations will be handled, as will be the internal recharging.
Together with the Personnel Department, further developments of workflow applications for the processing of hour notes of stand-ins were made. Unfortunately, not much progress was made here.
In 2003, the digitalisation of all decentralised personnel files was concluded. More and more educational bureaus also started digitalizing (or let digitalize) their student files. Furthermore, since student year 2003/2004 they received direct access into the digital filing cabinet of the Central Student Administration (CSA). They are now able to consult diplomas and identification cards. In the field of the business archive, little progress was made. From the conversation with the head of DUB (Services Academic Board) it appeared no direct need to digitalize the board post exists. Yet in some units (e.g. IM DEPARTMENT and Technical Nature Sciences) a business archive was arranged in DocuWare.
The IM DEPARTMENT decided to stop providing services in the area of workplace automation (e.g. advising the use of MS-Office). It was discovered that faculties and services cannot or will not reserve the financial means.
Administrative Automation
Cluster Steering
Because changes in the responsible persons within the DUB and the project group IR, the project did not make much progress. At the moment the workgroup IR is working on the development of the new plan. The partial project Education: Pre-registration/registration will be concluded in 2003.
Cluster Research
In the final quarter of 2003 the new release of Metis (research information system) will be taken into production. In connection with the reorganisation, Metis is converted to the new arrangement of faculties in the summer of 2003. The Business Object universe of Metis has been realised.
Cluster Education/Students
The web application ISIS (students administration)It enables students to e.g. pass on address mutations and check whether their reenrolment has been processed yet. This relieves work of the CSA.
For the new release of ZAP (room request system), specifications have been defined and the development of the release can be started. For the research in replacing ZBS (room management system) Planon (Facility Management Information System) a work planning is made.
An extensive preliminary investigation in internship administration has been carried out. This resulted in the advice to develop a central registration system for both internships and graduation places.
The new School site and TeleTOP VO (a study environment for VWO-students) is implemented, both connected to ORCA.
Cluster Personnel
The implementation of Oracle HR is in full motion. No salary components will be entered yet because the new salary system selection procedure is still ongoing. On January first 2004 the transition of GPI the new personnel information system will take place. All person, job and illness data of all active employees will be converted.
The choice model ‘conditions of employment’ is adjusted to the new @campus layout and self-made calculation module is added.
Cluster Financial
In the first half of 2003, a large effort was made for processing the consequences of the turning and reorganisation of the UNIVERSITY. Some examples are the overall use of the institute code and the adjustment of reports.
In 2003, the project/hour registration system TAS (Time Accounting System) has been taken into use. An unexpected large interest in this system has risen.
An advice report about e-procurement was produced. Within PROFIT, the decision was made to execute further implementation of the e-procurement after reorganisation the purchase function. It is preferred to use the e-procurement module of Oracle Applications.
Further activities around e-procurement will be taken up as part of the later to be established Workgroup Purchase under responsibility of the IM
Cluster Facility Department
The module ‘message and work orders’ of Planon have been in use by the IM since January first 2003. The Planon reservation module, the replacement of CAAS (reservation system) has been taken into use by the Bureau Reservations, a new service of the Facility Department. Research is being conducted to investigate whether Planon can also take over the function of ZBS (room management system). The module ‘space management’ of Planon, to replace Insite View (space management system), has not been purchased yet. This project will be shifted to 2004.
Other Activities
The use of Business Objects as report resource has taken a flight. More and more units discovered the possibilities of BO. In December a UNIVERSITY-wide information afternoon for and by BO-users will be held.
End 2003 the new release of RUN (management system for basic ICT facilities like e-mail accounts and workplaces) will be taken in use. With this new release, the decentralized workplace supporters get web access to for them relevant parts of RUN.
The Oracle client/server (c/s) applications (like FASIT (administrative system) and RUN) on the UNIVERSITY run under version 6i for FORMS and REPORTS. Oracle announced that maintenance and support for this version stops in 2005. At the moment Oracle is supplying version 9I. An important point of attention is that from 9I, the c/s principle will no longer be supported and applications can only be run by means of a browser. To transfer c/s applications; Oracle delivers a tool, which to expectations will be not be officially Oracle supported before 2004 (at the moment it concerns a beta-release). Based on a conducted pilot the conclusion was drawn to convert a number of c/s applications to the web in 2004. Based on these experiences a decision can be made to convert the remaining applications.
Policy frame
The University profiles herself as an innovative university with a society focussed position, e.g. intensive use of ICT in education. ICT is being used in education in a renewing way to create a rich and effective learning environment. ICT is being applied in the supporting company processes of the UT to make them run more efficient and effective, by which space for the primary tasks of the UT: education and research originates.
The UT strives for integrated and transparent access to applications and information for students and employees. Transparency means that information systems will be connected in an insightful and user-friendly manner, e.g. an electronic learning environment connected to information systems for student administration, study progress management and a digital portfolio. The use of workflow, digital documents and files, web access, improved management information and self-service, leads to a productive work environment for the execution of the primary tasks of the UT (education and research).
The service ITBE develops and maintains the UT-wide useful standard ICT facilities; the decentralised units (faculties, institutes) develop and maintain the specific education and/or research connected ICT facilities. The ITBE has core capacity available for central development, which can, if necessary, be temporary replenished with external capacity. The last in preference by employing students (promoting student activism).
This plan proposes policy choices, made within the sketched policy frame.
Level of ambition
There are multiple developments in ICT and they occur extremely fast. The UT can’t be leading in all areas, but has to make choices.
Policy choice: In the information supply the UT chooses a position:
•as ‘innovator’ for ICT in education and wireless applications;
•as ‘early adaptor’ for data warehousing in institutional research, electronic file administration, workflow management, e-business, communication and presentation via the web and the component technology;
•as ‘follower’ for applications for management of traditional administration for education, research, students, personnel and finance.
The cost reductions with which the UT is confronted at the moment, have as consequence that we have to make choices. The ambition levels mentioned before will remain guiding.
Directing principles
The way to direct has all to do with the kind of organisation and the time spirit. Momentarily, partly because the necessary reductions within the UT, a refinement on the decentralised autonomy of the past years is noticeable. Besides the reductions, arguments as delicate integration and unnecessary complexity are present. Where possible and essential, a tendency towards more centralised steering is noticed
Policy choice: We shouldn’t go back to the centralized steering, like in the seventies. But the UT has to come to more agreements on the institutional level. Standardisation of procedures and technology are necessary to guarantee that the priorities of the UT as a whole come to their rights. Formulating and maintaining these central agreements require managerial commitment on the highest management level (Board of Management/ University Management Team).
Flexible and strong ICT-organisation
Because of the increasing importance of ICT services, the UT requires an organisation which has to identify herself with words like: flexible, dynamic, effective and efficient. In these areas the UT makes a difference between common and research/ education bound ICT services.
Policy choice: The UT wants a strong organisation for ICT services. The current fragmentation of ICT support by independent decentralised teams will have to be decreased to the necessary minimum. ITBE develops and maintains common ICT services. Faculties and institutes develop and maintain the research/ education bound ICT services.
Directing ICT services
The UT has a good position concerning her information policy and the execution of it. The current information domains, institution systems, system keepers, financing and the Advising institute Management Information policy Twente (AMIT) and the Advising Committee Information Technology (ACIT) as conference and advice institutions, form a construction which has proven its value over the past years.
In the frame of the reorganisation of the UT; the Board of Management has established two new councils for the directing of ICT services: the IT-council (infrastructural ICT services) and the I-council (institution systems).
Policy choice: ITBE prepares in consultation with the IT-council and I-council proposals for decision making by the Board of Management/ University Management Team. Further ITBE involves these councils in the operational elaboration of these decisions.
Institution systems: directing and financing
In March 2003 the Board of Management decided to come to an unambiguous direction and financing of the UT institution systems. The institution systems have to be integrally (development, maintenance and production) financed from central resources. The current available resources will be allocated if necessary, so central financing can be filled in budgetary neutral. ITBE draws up the financial model for the financing of the institution systems in 2003 in close cooperation with the I-council.
The University Management Team/ Board of Management sets mainlines and frames for the institution systems. The precise content and realization is formed in a yearly planning & control cycle by the service ITBE, in close cooperation with the I-council.
Policy choice: the institution systems are integrally (development, maintenance and production) financed from central resources. A yet to be formed Council for Institution systems will guard the yearly planning & control cycle, executed by the service ITBE.
From process to customer focus
Until now, information systems were mainly focussed to the process and an efficient registration. New systems will have to take the needs of the customer into account. The skilled ICT-user of today wants to deliver data in an easy way and be able to request tailored oversights. The real customers have to be involved in this process. These ‘real’ customers are the end-users of systems and information. We are for example talking about the students and directors of the education/ management.
Policy choice: In buying and developing applications and procedures we have to think more from the customers point of view: one service window, single log on, user friendly and integrated access of de various systems. Hereby the real end-users have to be involved. The e-business application is important in filling in these policy choices. This requires more alignment between system holders and possibly leaves them with less separate autonomy.
National cooperation
In the SURF more-year plan 2003>6 a remarkable shift is visible. Attention is paid to shared supporting systems for the starting point ‘cooperation in systems and competition in education and research’. The goal hereby is: common database systems for basic administration.
Policy choice: The UT advocates cooperation in higher education on the area of supporting information systems. Where possible the UT will participate in institution transcending purchase or development tracks.
C@mpus+
The UT wants to be ahead in ICT in education. Over the past years, CIV and DINKEL have built a good cooperation to fulfil this UT ambition (introduction TeleTOP). Here fore DINKEL supplied the educational input and CIV the ICT facilitation. The new service ITBE, formed by the fusion of CIV and DINKEL, will execute projects under the umbrella of C@mpus+ for the coming years. The student portal and employee portal will be key concepts. Web communication forms an integral part, this means that the Bureau Communication (BC) will also be and stay closely connected to these developments.
Policy choice: ITBE and BC work optimal and alert together to realise C@mpus+. This has to lead to better accessibility of information and systems for the different target groups on the UT (internal and external).
Institutional Research
Managers desire digits and performance indicators of the UT, as a whole and parts of it. These Institutional Research (IR) is proceeding less well as expected. Causes are:
1.the data is not always deductible from the available databases;
2.those whom have to deliver the data, are not enough realising the importance of it;
3.the complex UT organisation is hard to catch in the model of the asked digits.
To achieve a better grip the ITBE-I&A is mapping the UT-information architecture and will improve this were necessary.
Policy choice: Institutional research is and stays important. The further developments are taken step by step, to begin with the information cluster Education (MISUT OW – Management Information concept UT Education).
Availability and security
Our dependency of ICT is increasing and with it our demands concerning availability and security. We actually want to be able to use one browser and one log-on to access everything from anywhere in the world at any time of the day. Preferably this information has to be available 7 x 24 hour a week. In specific for tele-education this is a hard demand.
Policy choice: New investments are necessary for extra security to reach optimal availability. For authentication and authorisation we have to come to more powerful (and yet customer friendly) mechanisms.
E-business
The term e-business has been overvalued the last period. After the hype now comes the time of handling. We can integrate information systems stepwise and communicate worldwide via the web. This creates new possibilities, i.e. user friendly interface, customer and supplier get direct access to UT administration, users can perform mutations themselves, run times improves and the UT wins in quick-wittedness and competitive strength.
Policy choice: The UT continuously checks for her own management where the philosophy of e-business can be applied.
Paper poor office
Especially at the UT, e-mail is substituting post traffic by paper at a high velocity. Individually we process and archive our texts already digitally. For complicated administrative flows systems are needed for electronic file maintenance and workflow management. ITBE cooperates with her customers to redesign and streamline work processes.
Policy choice: ITBE conducts projects in cooperation with her customers to try out electronic file maintenance and workflow management as an ‘early adapter’ and via a controllable path, implement these for the UT in a standardised manner.
Technical architecture and ICT-tools
ICT-tools and resources come in great diversity with each their specific advantages and disadvantages. We have too little manpower to support all these tools. For continuity and controllability the UT has to make clear choices.
Policy choices:
•Technical architecture: J2EE (Java 2 Enterprise Edition)
•For database systems of considerable size: Oracle
•For custom reports: Business Objects
•Use of XML for the exchange of data and the separation of data and cosmetics
•For web-enabled systems with underlying Oracle-database: Jdeveloper
•For course management in the education: TeleTOP, extended with functionality for testing and digital portfolio
•For workflow management: Staffware
•For authentication en authorisation: LDAP
•Uniform content management for web communication (starting with the use of WebHare)
•For some resources passive knowledge is sufficient and expertise is hired if needed. Criteria for this are: functional support and continuity have to be guaranteed
Part 3 - Architecture
The theme of working conference 3 is Analyse – Integration of student IS. The university has divided their central information systems into five domains: research, services, personal, finance and education. According to the theme, the scope of this document is the education domain. Developments and undesired situations in this domain are being described and can be used as input for the next discussion.
Student records
Student’s personal records are filed in ISIS. Records of their study results are filed in FASIT. These are the most important records for the education domain and therefore ISIS and FASIT are the most important systems. These systems are connected to many other systems inside and outside the domain. Most of these connected systems receive data; some of them send data and a few have both properties.
FASIT needs data from ISIS to operate. Every night FASIT receives a batch with the latest mutations. Therefore FASIT works with information that should not be older than twenty-four hours. Almost al the other systems “look” into the database of ISIS or FASIT to get the data they want, we call this the view. These systems are so-called satellite systems. If the core system fails, the satellites can get trouble with operating. So there are two ways in which data transaction is performed: view and batch.
At other universities it’s quite common that student records and study records are registered in one central information system, unlike at our university. ISIS is capable of registering study results, but the university chose a separate system. FASIT was already up and running before ISIS. The users of FASIT wanted to keep it. But looking at the other universities and at the age of the systems, it’s quite possible ISIS and FASIT will both be replaced by one central student information system (CSIS). This CSIS can also perform some actions which are now in little satellite systems, like registering for tests (TAST) and showing test results (TOST). The advantage of creating CSIS is that there will be fewer connections with other systems. The disadvantage is that almost the complete student administration will depend on one system. There is a nationwide development to standardise student records. The purpose is to make it easier to exchange student information between universities. This can stimulate the replacement of ISIS. If ISIS is not replaced, then the university needs to create a translation system to convert the ISIS records to the standardized student record.
Portal
Study related information is registered at many different places. I.e. educational announcements: students can find these at VIST, a publication board near BOZ and very often also on TeleTOP. The Student Union introduced a portal: one place from where different information sources can be accessed. They combine this with Single Sign On (SSO) to make it even more user-friendly. The university has taken over the concept and introduced the MyCampus Student Portal (MCSP).
The MCSP has been built from scratch. The Student Union Portal (SUP) was connected to the systems through a connection which we called view. Therefore it completely depended on these systems. Failure of one those systems meant less functionality of the SUP. MCSP should be less dependent. Therefore some vital information was copied into a local database.
Persons and their roles
fig 1. Sets of students and employees |
People in the university systems are divided in three different roles: student, employee or employee not university (ENU). Some systems have the possibility to add more roles, like third parties. This is only done when people temporarily need access to those systems, like an external consultant. Students are registered in ISIS and the rest in Oracle HR (which stands for Human Resource). An id-number is assigned to all people; the system in which the person is registered assigns this number. When a person is a student as well as an employee, this person is registered in two systems and gets two id-numbers. The result is a double administration of one person. Looking at figure 1 the intersection of the set students and the set employees is empty: S Ç E = Æ. This is unrealistic and unwanted.
When a person logs in on a system, his username and password are being checked. This data is created and registered in a system called RUN (Registration University Network users). The identification of users has recently been passed on to the LDAP system. LDAP was already running for a few years and used to contain only contact information. Its functionality has been extended with user authentication. LDAP contains information of all users and is also capable in distinguishing different roles of users. Students who are also employee are being displayed only as student.
The university examines the way students who are also employee are treated. An option is to make a sort of a virtual flexible workers organisation (like a virtual Randstad or Vedior). The latest developments are that a student will not be working for faculties anymore, but for the personal department of the university. But they still will be registered in ISIS as well as in Oracle HR. The student will not be aware of his Oracle HR record. Nothing really changes in the systems, but this might have been a good opportunity to deal with the double administration of persons.
Identification keys
The university uses id-number to identify students, courses, employees, et cetera. These numbers are called keys. The keys are declared in the systems where the object is first registered. The keys are used in all the systems of the university. Hence, local keys are publicly known and used.
Table : The interaction of university systems on education | |||
Flow | I/A | Description and key | |
1 | ISIS à RATS | View | Address data. Ñ: studentnumber |
2 | ISIS à PICA-LBS | View | Person data Ñ: studentnumber |
3 | ISIS à SKI | View | Student data. Ñ: student number |
4 | ISIS ßà IBG | Batch | Student data Ñ: student number |
5 | PTT à ISIS | Batch | Postcodebestand |
6 | ISIS à CBS | Batch | Student data for december count Ñ student number |
7 | ISIS à Student Union | View | Student data. Ñ: student number |
8 | ISIS à MCSP | Batch | Student data. Ñ: student number |
9 | ISIS à IBBS | View | Student data en adresses Ñ: student number |
10 | ISIS ßà FASIT | Batch & view | à Student data Ñ: student number |
ß: Scholarship data Ñ: student number | |||
11 | ISIS à SST | View | Student data Ñ: student number |
12 | ISIS à ORCA | View | Pre inscriptors-, students-, alumni data. Ñ: student number |
13 | ORCA à Schoolsite | View | High school student data Ñ: ORCA-ID |
14 | MCSP à Student Union | View | Person data and adresses. Ñ: student number |
15 | @Campus à MCSP | View | Newsitems Ñ: no (RSS feed) |
16 | VIST à IBBS | View | Course information. Ñ: course number |
17 | FASIT à VIST | View | Course number en naam Ñ: course number |
18 | FASIT à SST | View | Studieresultaten. Ñ: student number |
19 | FASIT à ORCA | View | Student data, examination date and date of leave Ñ: student number |
20 | FASIT à PEFASIT | Batch | Curriculum data, studyresults. Ñ: student number |
21 | FASIT à TOST | View | Studyresults. key: student number |
22 | FASIT ßà MAST | View, batch | a. à: student data, minordata. Ñ: student number |
b. ß: new student population. Ñ: minor | |||
23 | RUN à TeleTOP | View | Student data Ñ: student number |
24 | VIST à TeleTOP | View | Course information. Ñ: course number |
25 | ZBS à VIST | View | Lecture data Ñ course number |
26 | TAST à VIST | View | Examination roster Ñ: course number |
27 | FASIT ßà TAST | View | a. à: course data. Ñ: course number |
b. ß: Studyresults Ñ: student number | |||
28 | ZBS à TAST | View | Examination data. Ñ: course number |
29 | FASIT à RUN | View | Student data Ñ: student number |
30 | FASIT à SMS-Tost | Batch | Student number, studieresultaten. Ñ: student number |
![]()
Introduction
This document is based on the e-learning survey of Namah [NAM02]. E-learning is a kind of distance learning. In some definitions, it is even the same. E-learning has been growing exponentially the last years; this is triggered by the growth of the Internet. More and more people are connected to the Internet, bandwidth broadens, multi-media possibilities improve, et cetera.
History
Since the invention of the computer in the 60’s, people saw possibilities to educate through the computer. However, with the Internet the possibilities expanded. The advantages of the Internet are the use of common standards and the separation of content and control. It also contributes to the “anytime, anywhere” principle. Looking at the business environment, the expectations are that the information systems will be more and more integrated. Knowledge will be more widely accessible.
Definition
What is e-learning really? Different people made different definitions. Broad definitions are for example:
•E-learning is the exchange of knowledge supported by any kind of electronic device (e.g. CDROM, cassette tape, internet). 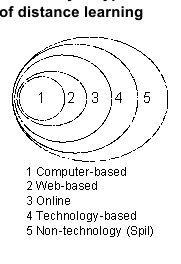
•E-learning provides the potential to provide the right information to the right person at the right times and places using the right medium.
More narrow views state that the Internet or an intranet must be involved. To make a distinction in these different definitions, e-learning is divided in four categories. I.e. “online learning”, “web-based training”, “technology-based training“ and “computer-based training or instruction”. Spil added a fifth layer: “non-technology”. The distinction in broadness of the definition is shown in the figure on the right. Technology-based training contains any kind of technology, which supports the training. Computer-bases training means “presenting courses on the computer”. Information on other sources can often not be accessed; therefore, the computer is a stand-alone.
E-learning versus instructor led
The most common form of teaching is that of the instructor. For example: a teacher in a class, or a driving instructor. The main problem is that the instructor and the student must be at the same place, at the same time, to be able to exchange knowledge. To accomplish this, people often need to leave their working area’s to go to the teaching areas. Besides the fact that they will not be able to work, they also need to travel there. When people learn through e-learning, they will not need to leave their working area, traveling will not be necessary, but they still will not be able to do their normal work. But there are more disadvantages of pure e-learning. Students will not be able to socially interact; they only interact with the interface of the system. Sometimes discussion boards or chat rooms can be used, but it is still not the real deal. This can also be reflected on the feedback aspect. In a classroom, a teacher can be asked questions any minute. Using e-learning could take more time to get a reaction. Another problem is that not everything can be taught electronically, e.g. psychology, driving lessons.
The advantages and disadvantages, which are just mentioned can also be related to money. Why do organizations educate their people? When people have better knowledge about their activities, they will be able to work more efficient. However, training people costs money. The costs of the education should be in perspective of the cost savings. The advantages that people will not need to travel to get to a classroom and that they do not need a face-to-face instructor seems to save money. But if cost saving is the only motivation for e-learning, the results might be rather poor.
Instructor-led teaching can be supported by e-learning. An instructor can use the benefits of e-learning. Things, which do not necessarily need face-to-face contact, can be taught this way. E.g. making tests and exercises. A combination of the benefits of both can result in an efficient program. Some advantages are: study programs can be individualized, students can work on their own speed, cost saving because of less travel and out of office time, greater flexibility in methods.
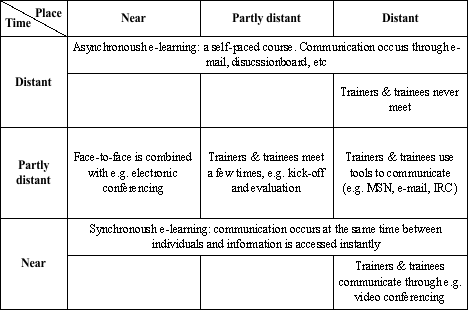
Table 1: various types of e-learning
Knowledge management
The gap between the knowledge of the employees and the information, which they need to know, is growing. Because internet is also growing, there are possibilities to provide these employees with digital courses. But information is overwhelming us. More and more information is available through more and more channels and locating necessary information gets harder.
The context of e-learning is creating knowledge. Knowledge management is a common type of management in organizations. E-learning is an available method of learning management. There could be more alignment between these two types of management because they both categorize and store knowledge and knowledge is spread through organizations through its employees’ minds and a variety of knowledge artifacts.
Aligning of learning and knowledge management has one big problem: they focus on different aspects of the organization. Knowledge management focuses on strategic and tactical aspects and learning management focuses on operational, and on tactical aspects. So there is an overlap in focus. However, there are developments in more common systems and methodologies. Even content management might be aligned in the future. The combination of the three types of management and their systems can be combined in an Intellectual Capital System (ICS).
Vendors
Many organizations are working on making standards for specifications for e-learning. Others are making programs and other products for e-learning. These e-learning products can be divided into three categories according to the interaction with the instructor: little or no interaction (free learning), free learning supported by an instructor (coached learning) and interactive learning (classroom learning). Gartner distinguishes six types of vendors for e-learning solutions, varying from standard software packages to custom built applications based on a organization’s needs. Any kind of e-learning an organization wants to adopt must first be fully supported by the management. The management needs to see the benefits of e-learning and how they can obtain a strategic advantage.
References
[NAM02] Namahn, E-learning, A research note by Namahn, March 2002, http://www.namahn.com/resources/notes.htm
IS Strategy process
To achieve insight in the information systems (IS) strategies in an organisation, the Facility Department of the University of Twente was studied. In this study the realization of the automation plan for the Facility Department is examined. As a guideline for this study the article: Dynamic and emergent information systems strategy formulation and implementation by H. Salmela and T.A.M. Spil was used.
Introduction
The Facility Department (FB) is a service department of the University of Twente (UT). The FB offers a wide range of products and services which facilitate working and studying at the UT as much as possible. The mission of the FB is: ‘To create the optimal workplace, working conditions and facilities for students and employees of the University of Twente.’
For this case description the automation plan of the FB was used. During the process of writing this plan, all department heads of the different services offered by the FB were interviewed. All the information gathered from these interviews was consolidated into the automation plan of the FB.
The FB is aware of the necessity of development of the Information Technology (IT) services, at the moment further professionalizing of the organisation and the provision of services is taking place. In the automation plan the focus is on how the information provision and automation develops within the FB. What is currently well functioning, on which parts in the process information provision and automation can make an important contribution, where the bottlenecks are and what improvements are possible. The solutions to the problems were translated into a number of projects, which were prioritised.
Agreements
The UT has made policy choices in the information services; she chose to position herself as:
●Innovator for Information Communication Technology (ICT) in education and wireless applications;
●Early adaptor for data warehousing in institutional research, electronic file administration, workflow management, e-business, communication and presentation via the web and the component technology;
●Follower for applications for management of traditional administration for education, research, students, personnel and finance.
For the FB the above mentioned policy of the UT combined with the strategy plan of the FB points out ten FB-areas were (the management of) the information services and automation can deliver an important contribution:
1.A further implementation and embedding of the Facility Management Information System ‘Planon’ in the organisation of the FB. This way the FB will achieve more efficient workflows and better control of her resources. Also better and more efficient quality control and manageability of these workflows and resources are enabled. Quality control is crucial in further professionalizing the organisation of the provision of services;
2.Optimising the entrance systems of the campus and the buildings by good control of entrance and barrier passes, maintenance of the systems, etc. This enables strict control on entrance authorisations and spreads the technical responsibility over more than one person;
3.Improvement of IT-knowledge throughout the FB. An example is the advanced use of Excel and Business Objects, when more knowledge is present in the organisation, the knowledge of the “Informatietechnologie, Bibliotheek & Educatie (ITBE)” can be used more structured and efficient;
4.Further implementation and expansion of a central UT-wide e-commerce system, to achieve more efficient and decentralised purchasing facilities, which will be more efficient to administrate;
5.An improvement of the support for making the timetables for the different spaces on the UT by better viewing functions and central all over timetables;
6.Further digitalising specific post categories for archiving and distribution of this post, to decrease the amount and loss of internal post;
7.Good maintenance and archiving of building, installation and ground plans. This is necessary for facility management, especially with the coming restructuring and maintenance of the buildings;
8.Further automation of internal and external invoice entry;
9.An equal work division of ICT support. To guarantee the continuity of the systems, enough capacity has to be available and preventive steps against overload have to be taken;
10.Standard work procedures have to be formulated, communicated and maintained considering: standard applications versions on all workplaces and standard procedures on archiving in the different departments.
During the process of writing the automation plan for the next five years, research was necessary. First an inventory was made of all systems currently being used by the department. To make this inventory all department heads were interviewed. During these interviews a number of questions were asked. These questions focussed on the systems currently in use, but also on wishes for the future, developments, shortcomings etc. All information was gathered in a system inventory, including wishes and problems per system. These wishes and problems were aggregated over all departments and shaped into possible projects. All projects were prioritised. These aggregated projects were discussed in a board meeting of the FB; this resulted in a new grouping and priority setting of the projects. A decision was made to form a new project organisation (see figure 1).
The principal is the director of the FB. The steering committee will exist of members of the FB and ITBE; to achieve broader decision-making and a wider basis. The main tasks of the steering committee are: overall policy and its decisions, to guard the common progress of the project, to provide means for financing the projects. The principal project group will exist of one member of the FB and one member of the ITBE. The goal of this group is to structure communication of the different project groups to the steering committee. A project group will be formed per project and can contain several work groups. ![]()
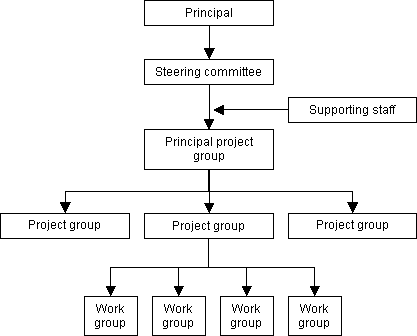
In the choice of which tools to use in the projects, it was decided to make a project plan per project. This project plan must at least contain the following:
●Who does what and when, and how many hours will it cost (per activity);
●What amount of external costs will be made (per activity);
●How many internal FB hours are necessary (per activity) and whom from the FB has to be involved in the project.
These tools are global tools; the specific tools have to be decided upon per project. This enables flexibility towards the project environment and the persons involved in the project.
When looking at the evaluation of previous planning results, it can be seen that a list of current and planned projects was made. In setting the scope of planning and selecting objectives two information sources were used: “De Nota Informatiebeleid UT” (The overview of the information policy of the UT) and the “Strategieplan Facilitair Bedrijf” (Strategy plan FB). The automation plan of the FB contains a list of targeted planning outcomes. Also a scope is defined in the form of priorities given to the projects. In selecting participants and adjusting the planning approach, a new project organisation was established. The main employees to be involved are known. Also a planning horizon for the next five years was established. The outcomes of the first planning cycle are roughly:
•list of current and planned projects;
•list of targeted planning outcomes;
•an informal network of people to be involved.
Alignment
At the start of the project a corporate strategy was available; the “Strategieplan Facilitair Bedrijf” (Strategy plan FB). In this plan the mission; place in the hierarchical relations with the university; services; structure; strategic personnel plan and budget are outlined. Top management participated in the process; results were discussed and decisions were made by the management team. As a result of the automation plan, it was decided to form a new project organisation.
Information is essential to perform the services of the FB, for this reason information can be considered to have a strategic role. Information is used to outline and determine the future path and activities of the FB. On the other hand, information also has an operational role in the activities of the FB; e.g. for planning of maintenance.
In the second planning cycle, internal and external information sources have been indexed for use in the process. Guided by the strategy plan of the FB, some implications for IS objectives were revealed. Also a list of new future acts was made. In the automation plan a list of all new project ideas of interviewed members of the FB were included. These ideas were aggregated and remoulded into projects, which were prioritized by the management team. This way an IS plan with project priorities was established. Senior management participation is integrated into the process by the new project organisation. A summary of the outcomes of the second planning cycle is:
•internal information sources;
•external information sources;
•implications of corporate strategy for IS objectives;
•list of new future acts or events;
•list of new project ideas with priorities;
•senior management participation.
Analyse
The investigation of all existing systems in the FB was a time intensive process. Because the different departments all had their own specific applications; it was chosen to investigate by means of interviews. This meant interviews had to be held with all department heads; this is a time consuming but information intense approach. After all interviews it became clear this within the FB 34 different systems were used. Some of these were used by several departments, others only by one. In conducting the interviews a structured format was used. Different attention areas were formulated and these were investigated by set questions. This format was chosen to gather structured, comparable information over all departments. All participants were gladly involved in the process; because they were aware of the importance for the future and saw opportunities to be heard and stress their own interests.
As a result of the interviews an overview of all used systems was created. This overview was combined with knowledge of what each system was used for and by whom. Also the shortcomings and wishes per system were gathered. This resulted in a list of needs and wishes for the future IS infrastructure. The outcomes of the third planning cycle are:
•IS needs;
•Technology assimilation plan (general).
Authorise
The automation plan was reviewed by the management team and approved by the director. The director appointed employees for the leading roles in the new project organisation. At this point the automation plan is to be used as a guideline for further research and detailed planning of the projects. It contains first drafts of project proposals, which now have to be defined in detail.
The outcomes of the fourth planning cycle are at this moment:
•impact on organisation;
•first drafts of project proposals.
Wrapping up
The IS planning process was a flexible process. During the investigation interviews were conducted, from these interviews the information needed to write the automation plan was retrieved. For the present the automation plan was the end product of the research and global planning phase. This plan will be the guideline for following phases; to continue the process. Because of the flexibility in the process by working with projects and activities; conducted by project teams; the process can be seen as creative and adjustable to each situation. Although for a structured management of the different projects, it is essential to maintain a formalistic process.
Comprehensive or incremental IS Planning process
An organisation can choose to use a comprehensive or more incremental IS planning process. To determine whether the IS Planning process use by the FB was more comprehensive of more incremental five planning characteristics can be compared. The first characteristic is ‘Plan comprehensiveness’; looking at the FB it can be seen that first a strategy was formed, on which the rest of the planning process was based. In the comprehensive process, the plans are complicated and highly integrated with the strategy; in the incremental process, plans are simple and loosely integrated. On this scale the FB will move slightly towards the comprehensive practice. The second characteristic is ‘Approach to analysis’; at the FB all department heads were interviewed to derive experiences and opinions to forms projects. These interviews were held with use of a predetermined interview model, this formal process is part of the comprehensive process. The use of personal experiences and judgement are signs of an incremental process. On this characteristic the FB has parts of both processes. The third characteristic is the ‘Planning organisation’; planning at the FB was done by the board meeting of the FB and a few members of the ITBE. This shifts towards the comprehensive practise. The fourth characteristic ‘Basis for Decisions’; implies that the FB used a formal decision process, executed by the board. This is also a feature of the comprehensive process. The last characteristic ‘Plan control’; concerns the fact whether plans are periodically (comprehensive) or continuously (incremental) reviewed and adapted to changing circumstances. The different projects at the FB have to be formed and adjusted continuously to adapt to the changing circumstances; this is more an incremental process trait. Concluding it can be said that viewing all characteristics the IS Planning process used by the FB is a comprehensive process with several incremental traits.